As the threats from advanced tracking and state-sponsored surveillance continue to grow, some privacy enthusiasts are looking for more protection in the form of multi-hop VPNs. If you consider the resources being spent by surveillance agencies to de-anonymize users, choosing a VPN service that offers a higher level of anonymity is indeed a valid consideration.
A multi-hop VPN simply encrypts your connection across two or more servers (multiple hops) before exiting on to the regular internet. Routing your traffic through two or more servers in separate jurisdictions gives you a higher level of privacy and security – even if one server were to be compromised.
In this guide we will explain why people are using multi-hop VPNs and how they can help you achieve higher levels of privacy and security. The key factor when considering whether you need a multi-hop VPN is your threat model. How much privacy do you need and want for your unique situation?
However, for those interested in achieving higher levels of privacy and security, there are multi-hop VPNs.
The best multi-hop and double VPN services in
Below we are going to go into more detail on this topic, showing you exactly what we mean with multi-hop and double VPN in the context of VPN services. But firs, for those in a hurry, these are the best VPN services that offer multi-hop and double VPN features:
Double-hop VPN services (fixed locations, not self-configurable)
- NordVPN – $3.09 per month (with this 69% off coupon); based in Panama; 31 double VPN configurations (see the NordVPN review)
- Surfshark – $3.09 per month; based in The Netherlands; 15 double-VPN server configurations (see the Surfshark VPN review)
- ProtonVPN – $8.00 per month; based in Switzerland; 48 double VPN servers (see the ProtonVPN review)
- VPN.ac – $3.75 per month; based in Romania; 22 double VPN configurations (see the VPN.ac review)
Self-configurable VPN services:
- Perfect Privacy – Up to four servers, plus the NeuroRouting feature; $8.95 per month; based in Switzerland (Perfect Privacy review)
- OVPN – Up to two servers; $7.00 per month (but the multi-hop feature is a paid add-on for $5.00/month); based in Sweden
- IVPN – Up to two servers; $8.33 per month; based in Gibraltar
Now let’s dive into the details and specifically answer why you need a multi-hop or double VPN.
Surveillance and advanced online anonymity
A multi-hop VPN is a good privacy tool against targeted monitoring and other theoretical attack vectors we will discuss below. It may also be useful for those in dangerous situations, such as journalists or political dissidents living in oppressive countries.
One key question is whether you can trust the data center where the VPN server is located.
VPN services will rent, lease, or colocate servers in data centers all over the world for their network. These servers will be fully encrypted, secured, and under control of the VPN provider, thereby preventing third-party access to sensitive user data and traffic.
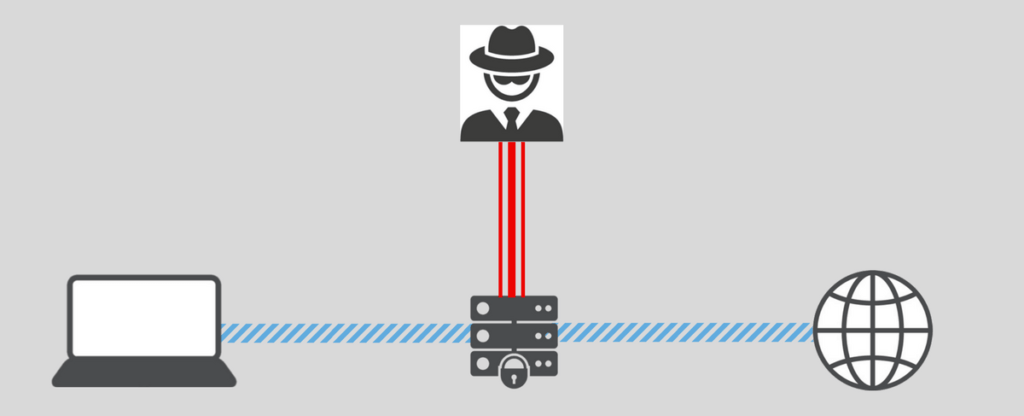
What can the data center see with an encrypted VPN server?
Even with strong encryption of the VPN server, the data center (host) – or perhaps an external state surveillance agency – could potentially monitor incoming and outgoing traffic on the server.
While this may seem alarming, it would still be very difficult for the data center (or third party) to gather useful information because:
- The traffic remains securely encrypted on the VPN tunnel, which right now is considered to be unbreakable (AES-256 encryption with the OpenVPN protocol, for example).
- Correlating outgoing traffic with incoming traffic is extremely difficult. Theoretically, traffic correlation for some users may be possible through advanced statistical analysis and studying traffic patterns. However, this remains difficult, especially on a large scale, even for powerful adversaries.
- Most VPNs utilize shared IPs, with many users on a given server (and IP address) at the same time, with all traffic being mixed. (Note: this is also why you should not “roll your own VPN” that only you will be using).
Even though a standard, single-hop VPN configuration will be adequate for the vast most users, incoming/outgoing traffic correlation may still be possible – at least in theory.
Are data centers really being targeted for traffic correlation attacks?
We have no way to know for sure. In many cases when authorities wanted customer data, they simply went to the data center and physically seized the server:
- Perfect Privacy servers were seized in the Netherlands (no customer data was affected)
- ExpressVPN servers were seized in Turkey (no customer data was affected) – as pointed out in my guide on no logs VPN services
In other cases, some VPNs have cooperated with authorities and handed over user information after being pressured by law enforcement agencies. These cases related to criminal investigations being conducted by US authorities. See for example the IPVanish logs case and also the PureVPN logging example.
Multi-hop VPN cascade
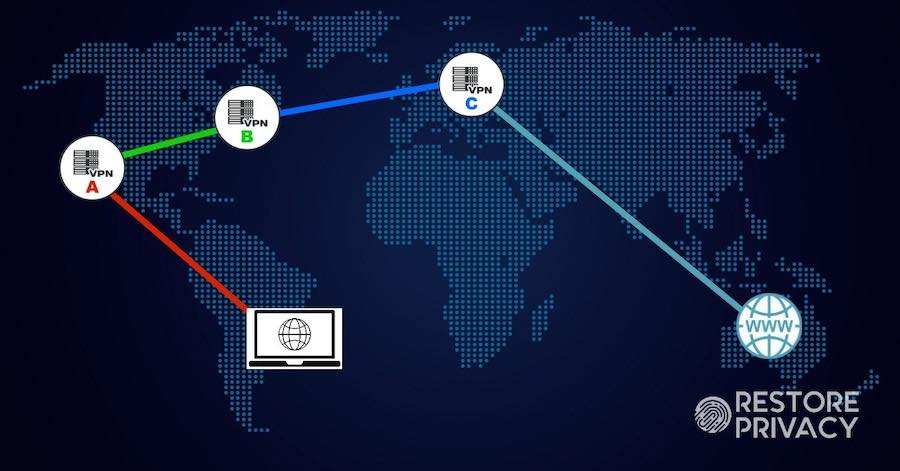
The first example of a multi-hop VPN we will examine is a “cascade” – where traffic is encrypted across two or more of the VPN’s servers.
One provider offering the ability to create custom VPN cascades with up to four servers is Perfect Privacy. Here is a basic visual explanation of how that would work using a four-hop VPN cascade:
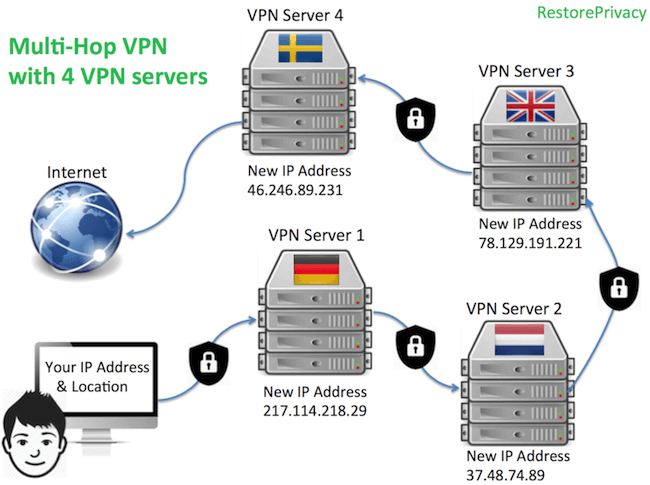
In the picture above, the user’s identity is changed at every hop and re-encrypted using OpenVPN 256-bit AES encryption (for example), before the traffic exits the VPN cascade on to the regular internet. With every hop, the new VPN server only gets the previous VPN server’s IP address/location – further obscuring and protecting the user’s true identity.
Perfect Privacy also makes some interesting points in this article:
With a cascaded connection this [traffic correlation] attack becomes much more difficult because while the ISP/eavesdroper still knows the VPN entry node of the user, it does not know on which server the traffic exits. He would need to monitor all VPN servers and take a guess at which exit node the user is using. This makes it next to impossible to successfully identify users by traffic correlation.
Also it is theoretically possible that an attacker has physical access to the VPN server in the data center. In that case he can possibly execute a de-anonymization attack on the VPN user. A cascaded connection protects against this attack vector: Since the user’s traffic is encapsulated with an additional layer of encryption for each hop in the cascade, no traffic can be read or correlated with incoming traffic.
The attacker would still see outgoing encrypted traffic to another VPN server but he cannot determine whether this is a middle or exit node. To successfully intercept and decrpyt the traffic, the attacker would need to have physical access to all hops in the cascade simultaneously. This is practically impossible if the hops are in different countries.
Using a multi-hop setup with strong encryption and other privacy tools provides you with a high level of online anonymity and security.
Double VPN services
Double VPN servers are a unique feature with some services.
With a double-VPN configuration, the first server could see your originating IP address, and the second server could see your outgoing traffic, but neither server would have both your IP address and your outgoing traffic.
This setup should still offer decent performance and it will also offer a higher level of security and privacy over a single-hop setup.
There are a few VPNs offering double-hop configurations that I have tested and found to work well:
- NordVPN – $3.09 per month (with this 69% off coupon); based in Panama; 31 double VPN configurations (see the NordVPN review)
- Surfshark – $3.09 per month; based in The Netherlands; 15 double-VPN server configurations (see the Surfshark VPN review)
- ProtonVPN – $8.00 per month; based in Switzerland; 48 double VPN servers (see the ProtonVPN review)
- VPN.ac – $3.75 per month; based in Romania; 22 double VPN configurations (see the VPN.ac review)
If you want the most features with your double-VPN, then either NordVPN or Surfshark would be a good decision.
Can you still get fast speeds with double VPN?
Are double VPN servers fast?
In my own tests, I have found that you can still get excellent speeds with some double VPNs (but not all).
The fastest double-VPN we have tested was with NordVPN on a USA-Canada server configuration at 614 Mbps download speeds, as you can see with the speed test result below.
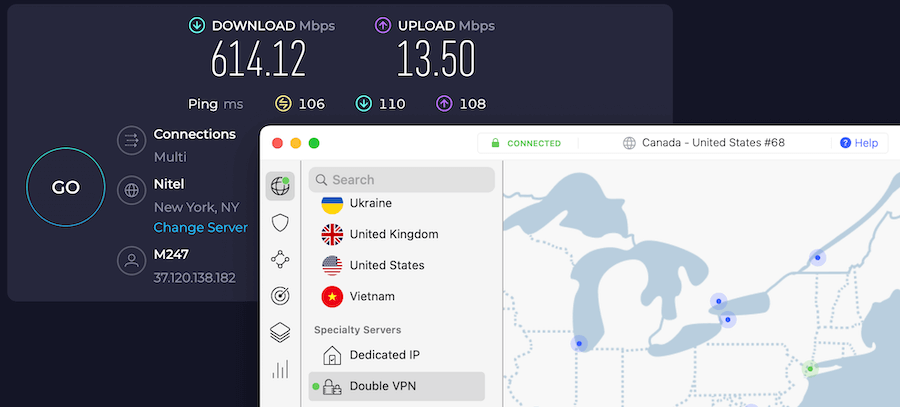
You can see server options and prices on the NordVPN website here.
On the opposite end of the spectrum is ProtonVPN, which delivers sluggish speeds in most performance tests. You can see examples of this in the ProtonVPN vs NordVPN comparison.
One drawback with the double-hop VPNs mentioned above is that they only offer static configurations. This means that you cannot configure your own unique multi-hop VPN using any server in the network.
Additionally, you can also create double-hop connections with VPNs that offer self-configurable server selection, which we’ll examine more below.
- Perfect Privacy – Up to four servers (plus the NeuroRouting feature)
- OVPN – Up to two servers (but the multi-hop feature is a paid add-on, as we covered in the OVPN review)
- IVPN – Up to two servers
Ok, so double VPN servers are great — but what if you want even more hops? Or perhaps you want to select custom locations for your multi-hop VPN connection.
Self-configurable multi-hop VPNs
A self-configurable multi-hop VPN allows you to individually select the servers in the VPN cascade. Here are a few VPN services offering this feature.
1. Perfect Privacy – Multi-hop VPN with up to 4 servers
Perfect Privacy allows you to create self-configurable VPN cascades with up to four hops directly in the VPN client. I tested this feature out for the Perfect Privacy review with both the Windows and Mac OS clients and found everything to work well.
Here is a four-hop VPN server cascade: Frankfurt >> Copenhagen >> Calais >> Malmo
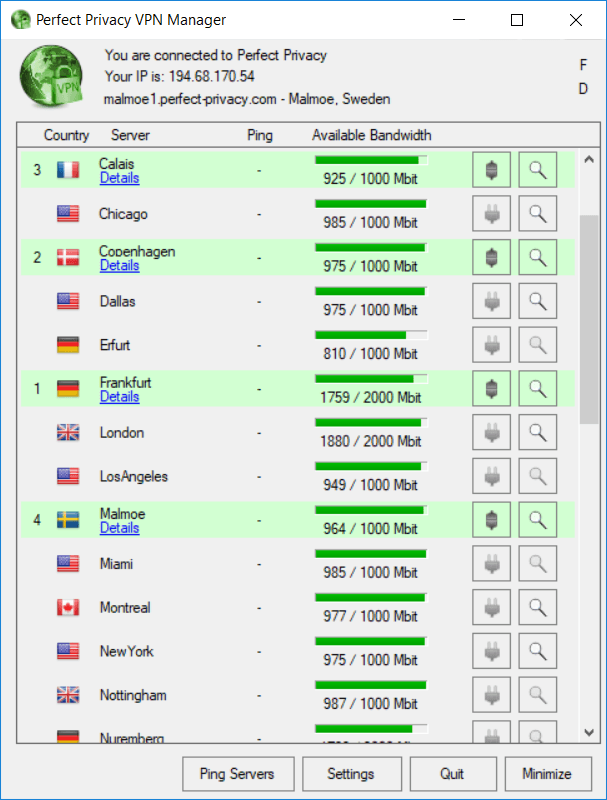
With this configuration, your true identity and IP address will be protected behind four different encrypted VPN servers.
Every website you visit will only see the server details of the last hop in the VPN cascade. You can simply enable the multi-hop configuration setting, and then dynamically add or remove VPN servers in the VPN client. The last server in the cascade will reflect your publicly-visible IPv4, IPv6, and DNS resolvers.
Note: One of the drawbacks of Perfect Privacy is the price, at about $8.95 per month. If you want a cheap VPN with multi-hop support, however, NordVPN would probably be a better fit.
Perfect Privacy is also one of the few VPNs with IPv6 support.
See our Perfect Privacy review for more information.
2. OVPN (two hops)
OVPN is a Swedish VPN service that offers multi-hop configurations through an add-on feature. This feature is $5 per month in addition to your regular VPN subscription. This is similar to ProtonVPN and the Secure Core option, which is more expensive than the basic subscription tier.
You can route traffic over two hops with OVPN. OVPN also supports IPV6.
3. IVPN (two hops)
IVPN is a VPN service based in Gibraltar. It offers users the ability to route traffic over two hops, but does not support IPv6. However, IVPN does support WireGuard VPN protocol.
Like some of the others we’ve covered, IVPN prices are above-average, but it is also a fully-featured VPN with clients for all major operating systems and devices.
Dynamic multi-hop VPN configurations (NeuroRouting)
Another interesting development in multi-hop connections and advanced security is NeuroRouting.
This is a unique feature was officially launched in October 2017 by Perfect Privacy.
NeuroRouting is a dynamic, multi-hop configuration that allows you to simultaneously route your traffic across numerous unique/different server configurations in the network. Here is an overview of this feature:
- Dynamic – Your internet traffic is dynamically routed across multiple hops in the VPN server network to take the most secure route. The routing path is based on TensorFlow, an open source software for machine learning, and data remains in the network as long as possible. Being based on TensorFlow, the network continually learns the best and most secure route for a given website/server.
- Simultaneous – Each website/server you access will take a unique route. Accessing multiple different websites will give you numerous, unique multi-hop configurations and IP addresses at the same time, corresponding to the location of the website server and the last VPN server in the cascade.
- Server-side – This feature is activated server-side, meaning every time you access the VPN network, NeuroRouting will be active (unless you disable it from the member dashboard). This also means it will work on any device – from routers to Mac OS and Android. Finally, NeuroRouting works with OpenVPN (any configuration) as well as IPSec/IKEv2, which can be used natively on most operating systems.
The image above shows NeuroRouting in action, with the user connected to a VPN server in Iceland, while accessing four different websites located in different parts of the world.
You can learn more about NeuroRouting here.
Multi-hop VPN chains with different VPN providers
Ok, what if you want to add different VPN providers to the mix?
Another option is to create chains using more than one VPN provider at the same time. This is sometimes referred to as a “VPN within a VPN” or a “nested chain” of VPNs.
This is a good option for protecting users against a VPN that may be compromised, as well as a VPN server that may be compromised.
Here are a few different ways to do this:
VPN 1 on router > VPN 2 on computer/device
This is an easy setup with a VPN on a router and then using a different VPN service on your computer or device, which is connected through your VPN router. Choosing nearby servers will help minimize the performance hit with this setup.
VPN 1 on computer (host) > VPN 2 on virtual machine (VM)
This is another setup that can be run without much hassle. Simple install VirtualBox (free), install and setup the operating system within the VM, such as Linux (free), and then install and run a VPN from within the VM. This setup can also help protect you against browser fingerprinting by spoofing a different operating system from your host computer.
You can also add a router to the mix, using three different VPN services:
VPN 1 on router > VPN 2 on computer (host) > VPN 2 on virtual machine (VM)
Lastly, you could also create virtual machines within virtual machines, or daisy-chain virtual machines. (If you are new to virtual machines, there are many videos available online that explain setup and use.)
Virtual machines are a great privacy and security tool, since they allow you to create isolated environments for different purposes – also known as compartmentalization. Within VirtualBox, you can create numerous different VMs using various operating systems, such as Linux, which you can install for free. This also allows you to easily create new browser fingerprints with each additional VM, while also concealing your host machine’s fingerprint.
Use Linux – When setting up VMs, I’d recommend running a Linux OS, for the following reasons:
- Free
- Open source
- More private and secure than Windows or Mac OS
Ubuntu is user-friendly and easy to get going in minutes.
Note: Be sure to disable WebGL in Firefox with all your VMs (see the instructions in the Firefox privacy guide using about:config settings). This will prevent graphics fingerprinting since all the VMs will be using the same graphics driver.
We will be covering the topic of nested VPN chains more in the Advanced Privacy Guides series.
Mirimir has also written some guides on setting up nested VPN chains:
- How to create dynamic nested VPN chains.
- A series of guides about using nested VPN chains and Tor.
When should you not use multi-hop VPN chains?
If your top priority is speed and performance, I would recommend using a single-hop VPN. So when would you want to prioritize speeds? Here are a few situations:
- If you are using a VPN for streaming, especially if you are streaming in high definition (HD)
- When using a VPN for torrenting and P2P downloads
- Watching a Netflix with a VPN (or using any other streaming service)
- Using a VPN for gaming where you will need fast ping / low latency
Conclusion on multi-hop VPNs in 2024
A multi-hop VPN configuration is an excellent way to achieve a higher level of privacy and security while also distributing trust across data centers and adding extra layers of encryption.
However, you should also understand that even when routing traffic over numerous hops, you are still placing all your trust in a single VPN service. Therefore this won’t protect you if the VPN itself is compromised. To get around this issue and further distribute trust, you can use nested VPN chains, with we will discuss more in future advanced privacy guides.
One of the simplest methods for using a multi-hop VPN on all devices would be to utilize the NeuroRouting feature from Perfect Privacy. Simply activate NeuroRouting from the member dashboard, and it will automatically be applied to all devices that connect to the VPN, with any protocol, any app, and any device. Because it is a server-side feature, rather than controlled within the client, it will simply work with everything that connects to the VPN.
Here is a recap of the multi-hop VPNs we’ve covered in this guide.
Double-hop VPN services (fixed locations, not self-configurable)
- NordVPN – $3.09 per month (with this 69% off coupon); based in Panama; 31 double VPN configurations (see the NordVPN review)
- Surfshark – $3.09 per month; based in The Netherlands; 15 double-VPN server configurations (see the Surfshark VPN review)
- ProtonVPN – $8.00 per month; based in Switzerland; 48 double VPN servers (see the ProtonVPN review)
- VPN.ac – $3.75 per month; based in Romania; 22 double VPN configurations (see the VPN.ac review)
Self-configurable VPN services:
- Perfect Privacy – Up to four servers, plus the NeuroRouting feature; $8.95 per month; based in Switzerland (Perfect Privacy review)
- OVPN – Up to two servers; $7.00 per month (but the multi-hop feature is a paid add-on for $5.00/month); based in Sweden
- IVPN – Up to two servers; $8.33 per month; based in Gibraltar
This multi-hop / double VPN guide was last updated on January 18, 2024.

Hi Sven,
i really appreciate your efforts writing such great articles. I could learn a lot from them, i dont stop reading them.
Thank you so much for your dedicated efforts.
to my mind Perfect Privacy is the best and if they’d add tor to the windowsApp it would be greatest great
I have the recent version of cloudflare WARP program/app installed on my laptop and smartphone. I am tethering my laptop to my smartphone via USB cable connecting to internet using cellular network. Is my input to internet encrypted once ( laptop or smartphone ) or twice ( laptop and smartphone )?
Hello Ken:
1. Cloudflare == google == direct feed to the 14 eyes agencies & XKeyScore.
2. Dump CloudFlare.
3. Your actual question is irrelevant in light of this.
4. Due diligence: Seek other options.
I`m kinda missing hide.me in this article. This VPN Provider, based in Malaysia has a perfect double-hop feature where you even can set your entry- and exit-note all for yourself from all of their servers.
For example, I set up a double-hop connection for privacy friendly countries, Switzerland -> Iceland or Sweden -> Iceland and the speeds are quiet good. With a 1 Gigabit connection I`m still getting about 200-300 Mbit/s Download in Speed-Tests.
This VPN, specially with this dynamic double-hop feature is definitely worth trying in my opinion!
Sven, I’m a baby in all this info pertaining to security etc. My question is what do you install first than second etc. i hate confusion and mistakes as important as this is. Is there some guide to how to install all needed downloads for max. security? My Desktop and my iphone is were i need to be wanting to have the security you mentioned I need to get a new email and other mistakes I’ve made! My E-MAIL: [redacted for privacy]. I’m reading all of your articles and want to be able to in future be able to comment with some knowledge like some of your guys.
LeRoy, I’d recommend first just getting a VPN set up on your primary computer. This is straightforward. Simply sign up for a good VPN, download the app for your computer, connect to a VPN server, and you’ll be good to go.
If you sign up with NordVPN, they can walk you through the installation process. And as mentioned above in this article, you can easily connect to their Double VPN servers to encrypt traffic over two hops.
You can get a discounted price on NordVPN here.
Awesome article! One minor correction: Surfshark now allows you to configure a multi hop connection with whichever 2 servers (from all their servers, as far as I noticed) you prefer.
Thanks for the article, Sven. Maybe a good idea to also run TOR: first start the VPN, then run TOR. That way, the VPN can’t see what the user is doing. Is that correct?
That isn’t necessary. If you don’t want the VPN to see what sites you visit, you just need to:
1) Start the VPN app on your desktop.
2) Open the Tor browser (or Brave with Tor window) and use the internet as normal.
The VPN sees your IP, and all browsing activity goes through Tor, making it invisible to the VPN.
Apologies to the admin but a small error. The article states Surfshark is based in the British Virgin Islands. However, they are located in The Netherlands as of today. Regards, Wolfgang Zwingli
Hi Wolfgang, thanks for noting that, it’s now fixed.