What are VPN protocols? Why do people get so excited about the differences?
With most VPN providers offering a variety of VPN protocols to choose from, it is good to know the pros and cons of these different options so you can select the best fit for your unique needs.
In this guide, we will compare the most popular VPN protocols, including OpenVPN, IPSec, L2TP/IPSec, IKEv2/IPSec, WireGuard, PPTP, and SSTP. This is meant to give you a brief overview of the pros and cons of each VPN protocol.
So let’s dive in.
What are the different VPN protocols?
What is a VPN protocol?
In the context of this article, a protocol is a set of instructions for formatting and processing data. A VPN protocol is a set of instructions to establish a secure and encrypted connection between your device and a VPN server for the transmission of data.
Most commercial VPN services offer a variety of different VPN protocols that you can use within the VPN client. For example, the screenshot below comes from the ExpressVPN review and shows the different protocols available to ExpressVPN users.
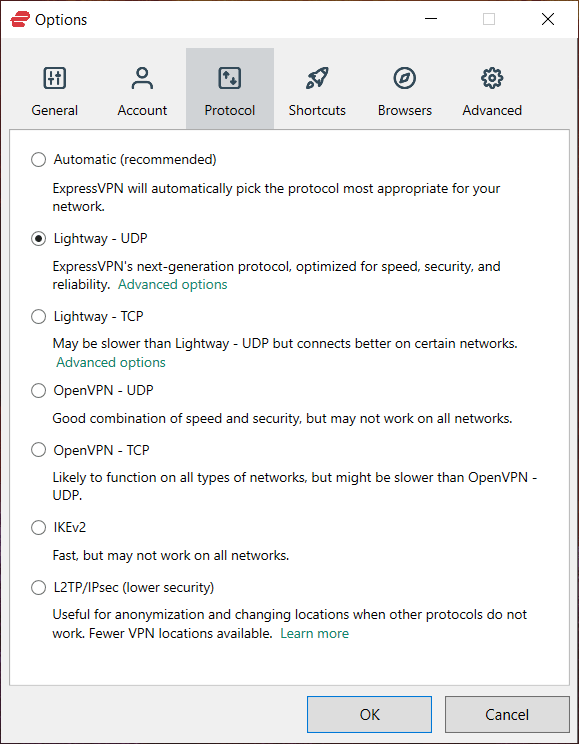
Note: You can see above that one of the VPN protocols listed is the Lightway VPN protocol. Developed by ExpressVPN, this open source protocol is used by ExpressVPN to increase data transmission speed and security when compared to ExpressVPN’s implementation of OpenVPN. Lightway is similar to WireGuard.
Now we will take a closer look at various VPN protocols.
OpenVPN – The current industry standard
OpenVPN is a versatile, open source VPN protocol developed by OpenVPN Technologies. It is a very secure protocol and has passed many third-party security audits. While WireGuard is growing in popularity, OpenVPN is still the most popular VPN protocol at this time.
OpenVPN is generally considered to be the industry standard when it is properly implemented and uses SSL/TLS for key exchange. It provides full confidentiality, authentication, and integrity and is also very flexible with various use cases.

Setup: OpenVPN requires special client software to use, rather than being built into different operating systems. Most VPN services provide custom OpenVPN apps, which can be used on different operating systems and devices. Installation is usually fast and simple. OpenVPN can be used on all major platforms through third-party clients: Windows, macOS, Linux, Apple iOS, Android, and various routers (check the firmware for compatibility).
Encryption: OpenVPN uses the OpenSSL library and TLS protocols to provide encryption. OpenSSL supports a number of different algorithms and ciphers, including AES, Blowfish, Camellia, and ChaCha20.
Security: So long as OpenVPN is properly implemented, it is considered to be a very secure protocol. It does not have any known major vulnerabilities.
Performance: OpenVPN offers good performance, especially if run over UDP (User Datagram Protocol), rather than TCP (Transmission Control Protocol). OpenVPN is also stable and reliable whether used over wireless or cellular networks. If you are having connection problems you can use OpenVPN with TCP, which will confirm all packets sent, but it will be slower.
Ports: OpenVPN can be used on any port using UDP or TCP.
Verdict: Recommended
WireGuard – A newer VPN protocol with great performance
WireGuard is a newer VPN protocol. It seeks to provide better performance and more security than existing protocols. It was officially released from beta in 2020 and continues to gain popularity due to better performance and security than even the best VPN protocols that came before it.

As we covered in the main WireGuard VPN guide, the protocol has some great benefits, mainly with better performance, a smaller code base, and upgraded security.
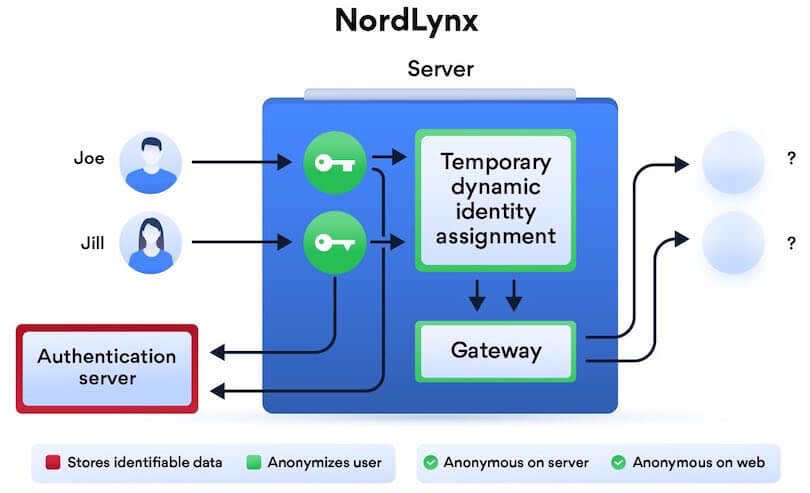
There are also a few drawbacks to WireGuard. By default, WireGuard stores user IP addresses on the server and does not assign IP addresses dynamically. However, many VPNs have found good solutions to these problems that ensure WireGuard does not undermine privacy.
For example, NordVPN implements a double-NAT system to ensure user IP addresses are never stored on the VPN server. This effectively solves the inherent privacy issues with WireGuard. And as we covered in the NordVPN review, NordLynx is the name of their implementation of the WireGuard VPN protocol.
Setup: WireGuard is included in the kernel of Linux. , Mac OS, and perhaps with some mobile operating systems. A limited number of VPNs support WireGuard – check with the provider for setup instructions.
Encryption: WireGuard utilizes Curve25519 for key exchange, ChaCha20, and Poly1305 for data authentication, and BLAKE2s for hashing.
Security: WireGuard has officially been released from beta and has passed security audits. It offers updated encryption standards and can be considered very secure.
Performance: Generally speaking, WireGuard offers excellent performance in terms of speed, reliability, and also battery consumption. It is ideal for mobile users because it allows you to seamlessly switch between network interfaces without losing the connection. Re-connecting is also supposed to happen much faster than with OpenVPN and IPSec.
The biggest performance advantage of WireGuard is fast download speeds. In our OpenVPN vs WireGuard comparison, we found that WireGuard outperformed OpenVPN with all server locations by about 57%. Some of the top VPNs that support WireGuard can get speeds from 300 Mbps to 445 Mbps on a 500 Mbps internet connection, as you can see in the Surfshark vs NordVPN report.
Ports: WireGuard uses UDP and can be configured on any port. Unfortunately, there is no support for TCP, which makes it easier to block.
Verdict: Recommended with select VPN services
IPSec – Internet Protocol Security
What is IPSec? IPSec is a secure network protocol suite that authenticates and encrypts data packets sent over an IP network.
IPSec stands for Internet Protocol Security. IPSec was developed by the Internet Engineering Task Force. Unlike SSL, which works on the application level, IPSec operates on the network level and can be used natively with many operating systems. Because most operating systems support IPSec natively, it can be used without third-party apps (unlike OpenVPN).
IPSec has become a very popular protocol to use with VPNs when paired with L2TP or IKEv2, which we will discuss more below.
IPSec encrypts the entire IP packet using:
- Authentication Header (AH), which places a digital signature on each packet; and
- Encapsulating Security Protocol (ESP), which provides confidentiality, integrity, and authentication of the packet in transmission.
Leaked NSA presentation – A discussion of IPSec would not be complete without referencing a leaked NSA presentation that discusses the NSA compromising IPSec protocols (L2TP and IKE). It’s difficult to come to any concrete conclusions based on vague references in this dated presentation.
Nonetheless, if your threat model includes targeted surveillance from sophisticated state-level actors, you may want to consider a more secure protocol, such as OpenVPN. On a positive note, IPSec protocols are still widely considered to be secure if they are implemented properly.
Now we will examine how IPSec is used with VPNs when paired with L2TP and IKEv2.
IKEv2/IPSec
What is IKEv2/IPSec?
IKEv2 is a tunneling protocol that is standardized in RFC 7296 and it stands for Internet Key Exchange version 2. It was developed as a joint project between Cisco and Microsoft. To be used with VPNs for maximum security, IKEv2 is paired with IPSec.
The first version of IKE (Internet Key Exchange) came out in 1998, with version 2 being released seven years later in December 2005. In comparison to other VPN protocols, IKEv2 offers advantages in terms of speed, security, stability, CPU usage, and the ability to re-establish a connection. This makes it a decent choice for mobile users if WireGuard and OpenVPN are not suitable.
Setup: Setup is generally quick and easy, requiring you to import the configuration files for the servers you want to use from your VPN provider. (See this setup example with Perfect Privacy.) IKEv2 is natively supported on Windows 7+, macOS 10.11+, Blackberry, and iOS (iPhone and iPad), and some Android devices. Some operating systems also support an “always on” function (a.k.a. a kill switch), which forces all internet traffic through the VPN tunnel, therefore ensuring no data leaks.
Encryption: IKEv2 uses a large selection of cryptographic algorithms, including AES, Blowfish, Camellia, and 3DES.
Security: One drawback with IKEv2/IPSec is that it is closed source and was developed by Cisco and Microsoft (but open source versions do exist). On a positive note, IKEv2 is widely considered to be among the fastest and most secure protocols available, making it a popular choice with VPN users.
Performance: In many cases, IKEv2 is faster than OpenVPN since it is less CPU-intensive. There are, however, numerous variables that affect speed, so this may not apply in all use cases. From a performance standpoint with mobile users, IKEv2 may be the best option because it does well establishing a reconnection.
Ports: IKEv2 uses the following ports: UDP 500 for the initial key exchange and UDP 4500 for NAT traversal.
Verdict: Recommended
L2TP/IPSec
Layer 2 Tunneling Protocol (L2TP) paired with IPSec is also a popular VPN protocol that is natively supported by many operating systems. L2TP/IPSec is standardized in RFC 3193 and provides confidentiality, authentication, and integrity.
Setup: Setting up L2TP/IPSec is generally fast and easy. It is natively supported on many operating systems, including Windows 2000/XP+, macOS 10.3+, as well as most Android operating systems. Just like with IKEv2/IPSec, you simply need to import the configuration files from your VPN provider.
Encryption: L2TP/IPSec encapsulates data twice with encryption coming via the standard IPSec protocol.
Security: L2TP/IPSec is generally considered secure and does not have any major known issues. Just like with IKEv2/IPSec, however, L2TP/IPSec was also developed by Cisco and Microsoft, which raises questions about trust.
Performance: In terms of performance L2TP/IPSec can really vary. On the one hand, encryption/decryption occurs in the kernel and the protocol also supports multi-threading, which should improve speeds. But on the other hand, the fact that this VPN protocol double-encapsulates data can slow it down significantly.
Ports: L2TP/IPSEC uses UDP 500 for the initial key exchange as well as UDP 1701 for the initial L2TP configuration and UDP 4500 for NAT traversal. Because of this reliance on fixed protocols and ports, L2TP/IPSEC is easier to block than OpenVPN.
Verdict: L2TP/IPSec is not a bad choice, but you may want to opt for IKEv2/IPSec, OpenVPN, or WireGuard if available.
PPTP – An outdated and insecure protocol
PPTP stands for Point-to-Point Tunneling Protocol and is one of the oldest VPN protocols still in use today. It runs on TCP port 1723 and was initially developed by Microsoft.
PPTP is now essentially obsolete due to serious security vulnerabilities. We won’t spend too much time discussing PPTP because most people are not even using it anymore.
PPTP is supported natively on all versions of Windows and most operating systems. While it is relatively fast, PPTP is not as reliable and does not recover as quickly from dropped connections as OpenVPN.
Overall, PPTP should not be used in any situation where security and privacy are important. If you are just using a VPN to unblock content, PPTP may not be a bad choice, but there are more secure options worth considering.
Verdict: Not recommended
Lightway – A new VPN protocol from ExpressVPN
While many VPN providers have been working to integrate WireGuard, ExpressVPN has taken a different route. This VPN provider instead developed its own protocol with Lightway.
In many respects, the Lightway VPN protocol is similar to WireGuard. It is based on the latest cryptography and also offers reliability improvements. And while Lightway is faster than OpenVPN, it is not quite as fast as WireGuard in real-world tests. See for example thespeed tests section of this ExpressVPN vs NordVPN comparison.
Using the Lightway protocol with the ExpressVPN app is simple. All you need to do is open up the Settings area, select Protocol, and then click on the version of the Lightway protocol you want to use.
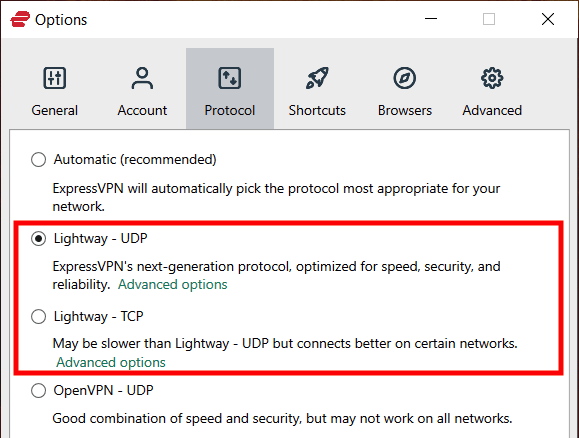
At this time, only ExpressVPN is using Lightway. While Lightway is open source and has passed security audits, it still remains less popular than WireGuard.
SSTP – A VPN protocol for Windows, but not very commonly used
Like PPTP, SSTP is not widely used in the VPN industry, but unlike PPTP, it does not have major known security issues.
SSTP stands for Secure Socket Tunneling Protocol and is a Microsoft product that is available for Windows only. The fact that it is a closed source product from Microsoft is an obvious drawback, especially with massive security vulnerabilities discovered in other Microsoft products recently.
SSTP transports traffic through the SSL (Secure Socket Layer) protocol over TCP port 443. This makes it a useful protocol to use in restricted network situations, such as if you need a VPN for China. There is also support for other operating systems, aside from Windows, but it is not widely used.
Because SSTP is closed source and remains entirely under the ownership and maintenance of Microsoft, you may want to consider other options. Of course, SSTP may still be the best option if all other protocols are getting blocked on your network.
In terms of performance, SSTP does well and is fast, stable, and secure. Unfortunately, very few VPN providers support SSTP. For many years ExpressVPN supported SSTP in the Windows client, but it is no longer supported today.
Verdict: SSTP may be useful if other VPN protocols are getting blocked, but OpenVPN or WireGuard would be a better choice (if available). Most VPNs do not offer any support for SSTP.
Which version of OpenVPN should you use: OpenVPN UDP vs OpenVPN TCP
With OpenVPN being the most popular VPN protocol, you can usually select between two varieties: OpenVPN UDP or OpenVPN TCP. So which to choose?
The screenshot below is from the NordVPN review, where I am choosing between OpenVPN TCP and UDP protocols.
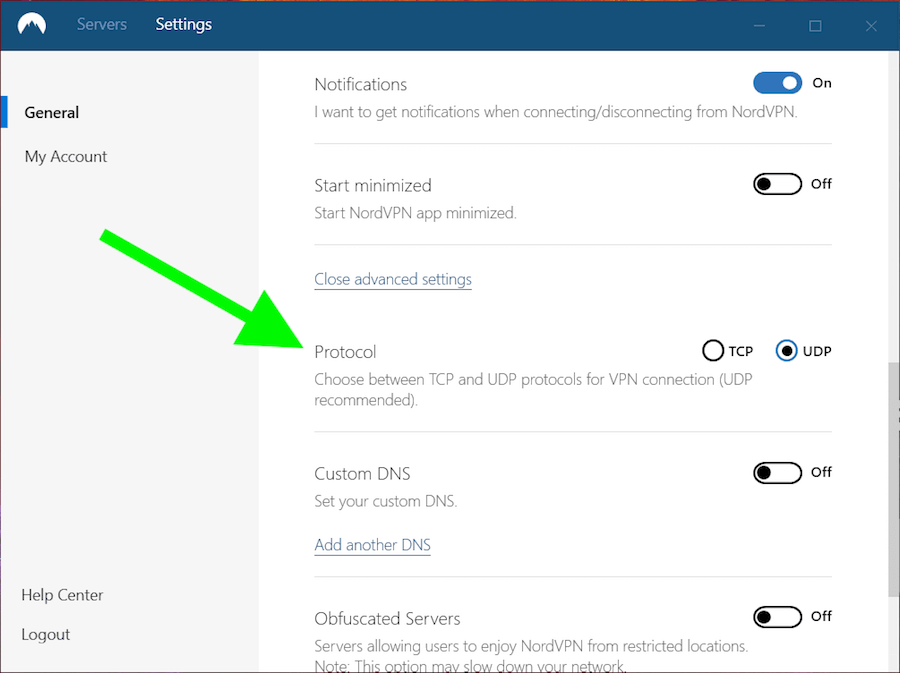
Here’s a brief overview of both protocols:
- TCP (Transmission Control Protocol): TCP is the more reliable option of the two, but it comes with some performance drawbacks. With TCP, packets are sent only after the last packet is confirmed to have arrived, therefore slowing things down. If confirmation is not received, a packet will simply be resent – what is known as error correction.
- UDP (User Datagram Protocol): UDP is the fastest of the two options. Packets are sent without any confirmation, which improves speed but also may not be as reliable.
By default, OpenVPN UDP would be the better choice because it offers superior performance over OpenVPN TCP. If you are having connection problems, however, switch to TCP for more reliability.
TCP is often used for obfuscating VPN traffic to look like regular HTTPS traffic. This can be done by using OpenVPN TCP on port 443, with the traffic routed in TLS encryption. Many VPN providers offer various forms of obfuscation to defeat VPN blocks, and most utilize OpenVPN TCP.
Note: to see how WireGuard outperforms OpenVPN in real-world tests, just check out our IPVanish vs NordVPN report. Here we have speed tests with NordVPN using WireGuard against IPVanish using OpenVPN. And the difference was huge.
What is the best VPN protocol for your use case?
As noted in my overview of the best VPN services, there is no one-size-fits-all solution for every person. This applies to choosing a VPN service and also selecting a VPN protocol. The best protocol for your situation will depend on a few different factors:
- The device you are using – different devices support different protocols.
- Your network – if you are in a restricted network situation, such as in China or with school and work networks, some protocols may not get through. Some VPN providers offer designated VPN protocols for these situations – see the VPN for China guide for more of a discussion on this topic.
- Performance – Some protocols offer big advantages in terms of performance, especially on mobile devices that go in and out of connectivity.
- Threat model – Some protocols are weaker and less secure than others. Choose the best VPN protocol for your security and privacy needs, given your threat model.
As a general rule of thumb, however, OpenVPN and WireGuard are my top recommendations for VPN protocols. They are secure, fast, trustworthy, open source, and audited.
In terms of performance, all of the fastest VPNs we have tested were using the WireGuard VPN protocol. While you can still get better than average speeds with OpenVPN, the WireGuard VPN protocol remains the top performer by a long shot.
Conclusion on VPN protocols in 2022
This best VPN protocol guide is meant to serve as a basic overview of the main VPN protocols in use today: OpenVPN, WireGuard, L2TP/IPSec, IKEv2/IPSec, PPTP, and SSTP.
For more in-depth information on each protocol, you can examine references from the respective developers.
We will continue to update this guide as development continues with these different VPN protocols.
This guide was last updated on January 27, 2023.

While most countries need ID verification to buy a SIM card, the US does not.
NSA Protocol, contact Bluffdale and ask for a cookie.
I too am outside of the US and it has recently became clear to me the U.S. is not the land of the digitally free…
WireGuard is built into many operating systems—such as Linux, Android, OpenBSD and FreeBSD.