One of the best ways to protect your privacy is to encrypt important information on your computer. Whether you need to send personal information to someone, or simply want to make sure that no one who gets access to your computer can see stuff you would rather keep private, encryption is the way to go.
Happily, as a user of Windows 10, you have numerous options for encrypting information. In this guide we will show you ways to encrypt individual files, file folders (and all the files within them), even entire disk drives. Each approach has its own benefits and drawbacks, so we’ll cover those too. That way, you’ll have a better sense of which type of encryption you will need for various situations. Before we go further, here are a couple of points to keep in mind:
- With Windows 7 officially unsupported now, and Windows 8 best forgotten as fast as possible, this guide deals only with the Windows 10 operating system.
- If you are encrypting a file to share with someone else and need to give them the password, you should not send them that password using the same method that you send them the file. For example, if you plan to email them the file, it would be a big security risk to also email them the password. Ideally give them the password over the telephone, a secure messaging app like Signal or Wickr Me. At the very least send it via a different email service than the one you will use for the file.
Now let’s talk about when to use the three types of encryption that you can use:
- Individual file encryption
- Folder encryption
- Hard drive / Disk encryption
Individual file encryption
As the name implies, individual file encryption refers to encrypting one file at a time. Each file has its own password or key.
Individual file encryption is great for files you plan to share or store in the cloud. Windows 10 users can encrypt individual files using a tool like 7-zip. You can also encrypt individual Microsoft Office files from within their apps, although this is better suited to casual person use than protection against serious adversaries.
Folder encryption
Next up is folder level encryption. This approach involves encrypting everything that is stored in a folder. Passwords or keys are assigned to the folder, not individual files.
Folder encryption is a great organizational tool. For example, you could create a different encrypted folder for each member of your family. Give Sally only the password for her folder, and Jimmy only the password for his, and each can have their own private space on the same device.
Note that storing a file in an encrypted folder doesn’t prevent you from also encrypting files individually.
Hard drive / Disk encryption
Hard drive or disk encryption protects the entire drive at once. To use a device with an encrypted hard drive you would need to enter the password or key when you logged on, or nothing on the disk would be accessible.
This kind of encryption is a good first line of defense in case of theft. If someone stole your laptop, or ripped the drives out of one of your servers, they would need to defeat the hard drive encryption to get any data at all.
You can still apply folder level encryption and individual file encryption to an encrypted disk.
Password management and file encryption
Before we dive into the details of file encryption, we need to make an important note on passwords. You need to be using a good password manager, along with good password hygiene.
Why is that?
Well, if you lose or forget the password for accessing your encrypted files, then they’ll probably be gone for good. A good password manager is critical. We’ve reviewed many options, including 1Password, LastPass, and many more.
See our guide on the best password managers for the top recommendations and step-by-step information for good password management.
Now that we’ve hit the basics, it is time for some specifics. Let’s start with…
How to encrypt files and folders on Windows 10
Your options for encrypting files and folders on Windows 10 devices depend on which version of Windows 10 you have. Windows 10 Pro and Enterprise users have a built-in encryption tool called the Encrypting File System (EFS). Any Windows 10 user, including those with the Home edition, can also use third-party apps such as 7-zip for file and folder encryption.
Beyond these options, Microsoft Office apps have a basic file locking / encryption feature built in, as does Adobe Acrobat. While we will be looking at all these options, you’ll really want to take a look at a new addition to the Windows 10 files and folders encryption scene: NordLocker.
We’ll round out our coverage of Windows 10 encryption by taking a look at this new, flexible, easy-to-use file and folder encryption system.
How to encrypt files and folders with the Encrypting File System (EFS)
The Encrypting File System (EFS) is built into the Professional and Enterprise versions of Windows 10. It is treated as an Advanced feature of the Windows File Explorer. This makes a lot of sense, since used carelessly, EFS can leave you with files you can never access again.
EFS does all its encryption work in the background, including automatically creating a File Encryption Key (FEK), and encrypting that key so only the account that encrypted the file can decrypt it. All this happens automatically and transparently.
Aside from a lock symbol that appears in the File Explorer next to a file or folder that is encrypted, there is no easy way to tell that a file or folder is encrypted with EFS.
Unfortunately, EFS has some quirks that make it a less than ideal choice for many uses. Knowing what these are will help you decide whether EFS is the answer to your Windows 10 file encryption needs:
- EFS only works on drives formatted with NTFS.
- If you move an EFS-encrypted file to a disk formatted with FAT32 or exFAT, it becomes decrypted.
- If you move an EFS-encrypted file across a network, or send it with an email message, it becomes decrypted.
If these quirks haven’t scared you away, here’s how to encrypt files and folders with EFS:
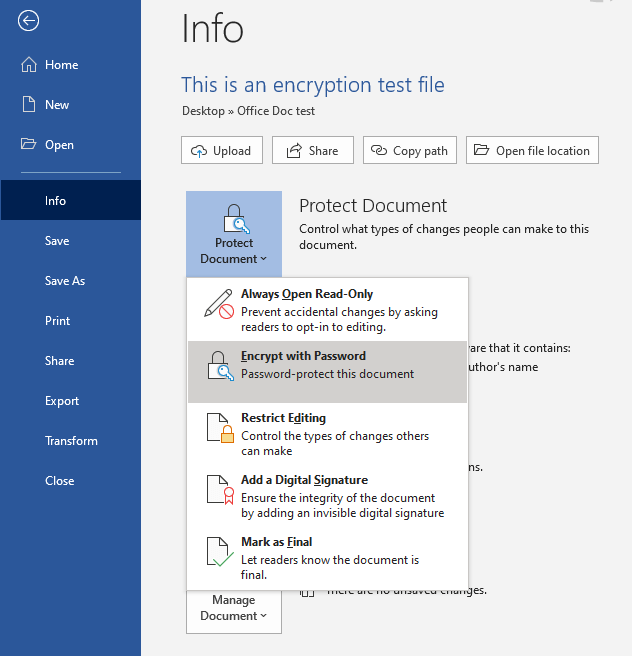
- Launch Windows File Explorer and navigate to the file or folder you want to encrypt using EFS.
- Right-click the file or folder you want to encrypt.
- In the menu that appears, select Properties.
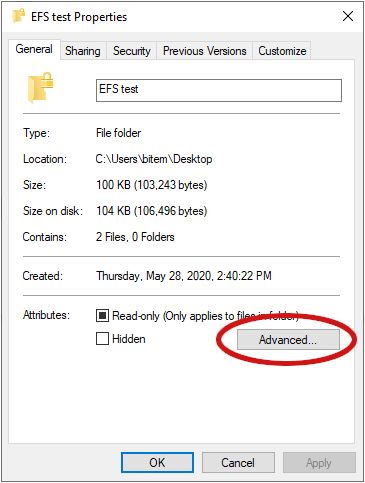
- In the General tab of Properties, find and click the Advanced button (it is circled in red in the following image).
- In the Advanced Attributes dialog box that appears, set the Encrypt contents to secure data checkbox.
- Click OK until you return to the document window.
That is all you need to do, from now on, the encrypted file or folder will appear encrypted to anyone other than the user account that encrypted the item in the first place.
How to encrypt files and folders with 7-zip
7-zip is a freeware file compression program that can also encrypt files and folders using AES-256 encryption, which is the industry standard for most encrypted systems.
If you plan to use 7-zip to encrypt files or folders you should know that the process creates an encrypted copy of the file or folder. The original, unencrypted file or folder is unchanged.
If you are creating the encrypted item because you plan to send it somewhere, or store it in the cloud or something like that, this is fine. But if your goal is to protect the files and folders on your own device, this isn’t ideal.
In the rest of this section, we’ll first look at how to encrypt files and folders with 7-zip. After that we’ll talk about what else you need to do if your goal is to protect the files and folders on your own device.
The following instructions assume you already have 7-zip installed on your system. If not, you can download it here.
How to encrypt Windows 10 files and folders using 7-zip
- Right-click the file or folder you want to encrypt.
- In the shortcut menu that appears, select 7-Zip, then Add to archive…. This opens the Add to Archive window.
- In the Archive field, enter the name for the archive you will create.
- In the Archive format list, select zip.
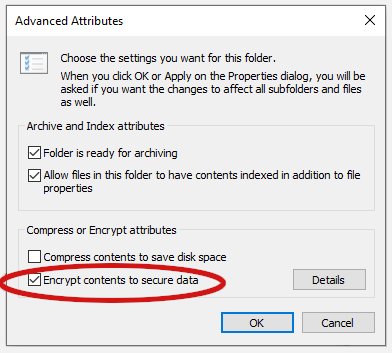
- In the Encryption section of the window, enter a strong password in the Enter password field, and again in the Reenter password field.
- In the Encryption Method list, select AES-256.
- Select OK. This creates the encrypted archive file, which appears in the same folder as the file or folder you encrypted.
What to do after you encrypt something with 7-zip
The result of encrypting something with 7-zip the way we did here is a zipped archive that is AES-256 encrypted. This archive appears in the same folder as the file or folder that you encrypted, alongside the original file or folder. What this means to you depends on what you plan to do with the encrypted file or folder.
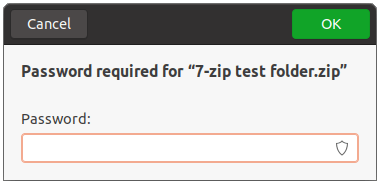
If you created the archive to share copies of the file or folder, this is fine. Just send the archive to the recipient. Assuming they have 7-zip or a similar program on their system (and you securely conveyed the password to them somehow), they will be able to unzip the archive, then double-click the file to enter the password in a dialog box like this one:
Once they do that, the operating system should open the file in whatever app is appropriate, and the recipient can view it, or save it, or do whatever is necessary with it. Note that they will still have the encrypted files on their system as well.
If you created the archive to protect the files or folders on your system, you should skip down to the section titled, “Eliminate any possible unencrypted copies of the file” once you are done encrypting files and follow the instructions there to make sure no unencrypted copies of things are lying around where some snoop can find them.
How to encrypt Microsoft Office files on Windows 10
Some applications now have options to encrypt the types of files they themselves use. For example, Microsoft Word can encrypt Word files, and Adobe Acrobat can encrypt PDF files. We’ll demonstrate this below.
How to encrypt files using Microsoft Office on Windows
Let’s use Microsoft Word to show how it is done by encrypting a simple Word document.
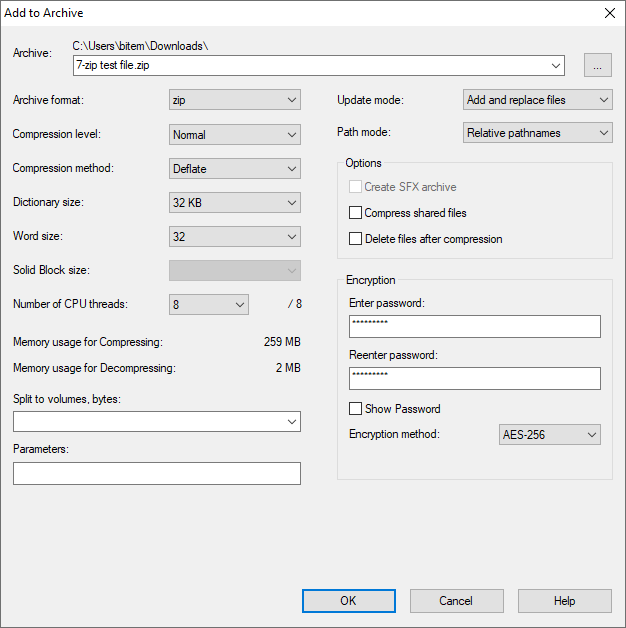
- With the document you want to encrypt open in Word, select File, then Info.
- In the Info window, select Protect Document.
- In the menu that appears, select Encrypt with Password.
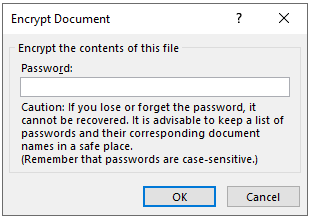
- In the dialog box that appears, enter the password you want to use for this document.
From now on, the only way to view this document will be by entering the password when prompted from within a Microsoft Office application that supports the unencrypted file type. But please see the next section to eliminate any possible unencrypted copies of the file on your computer.
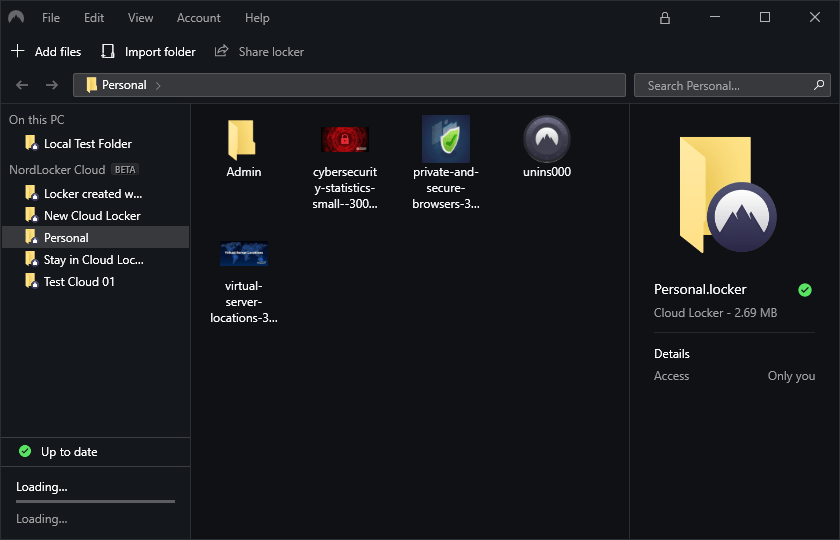
How to encrypt files and folders with NordLocker
NordLocker is a young sibling of NordVPN, one of the top VPN services in the world. NordLocker is a file and folder encryption system for Windows and Mac OS that includes cloud storage capabilities. Since the focus of this article is encryption on Windows 10 systems, we’ll focus on the encryption side of the product. For a complete review of the product, including its cloud storage capabilities, read our full NordLocker review.
As its name implies, NordLocker stores encrypted files or folders in lockers. Anything stored in a locker is securely protected with an array of potent cryptography: AES-256, ECC (with XChaCha20, EdDSA, and Poly1305), and Argon2. What this means to us is that anything in a locker is completely illegible to anyone, unless they are using NordLocker, and know your master password.
On the other hand, when you log into NordLocker on your computer, all the lockers open up for you. You can work with files and folders through the NordLocker interface as if they were totally unprotected. Your apps can read and write them, you can move them, delete them, treat them like normal files. Because NordLocker encrypts individual files and folders with the lockers, it is fast and efficient. You don’t have to sit and wait whenever you open, close, or move a file within its locker.
Encrypting files is super easy too. It is literally a drag-and-drop process. Let’s look at an example.
How to create a locker and encrypt a file with NordLocker
For this example, we’ll assume you already have NordLocker installed on your PC. If you don’t, and you would like to follow along with the example, follow this link to download the free version of NordLocker for Windows.
- Log in to NordLocker. You’ll see the default lockers created by NordLocker, as well as any other lockers you might already have created.
- Hover the cursor to the right of NordLocker Cloud (BETA) and a circle with a cross will appear.
- Click that to create a new locker. Since our goal in this procedure is to encrypt files and folders on your Windows 10 computer, be sure to create a locker that resides only on your PC.
- Drag any files or folders you want encrypted into the locker, or use the Add files or the Import folder menu options at the top of the window to select files/folders to add to the locker. The first time you add something to the locker, NordLocker will give you the option to move that file to the locker or copy that file to the locker while leaving the unencrypted file on the disk drive. Having an unencrypted copy of a file or folder on the computer defeats the purpose of creating and storing an encrypted copy.
Note: When you move an item to a locker, NordLocker deletes it, but doesn’t do anything to make the item unrecoverable on the disk. If your threat model includes protecting your computer against enemies who can recover deleted files from your disk drive, think carefully about whether NordLocker is the right choice to protect your data.
As long as your NordLocker is unlocked, you and your apps can work with the files and folders normally. When NordLocker is locked (you can do it manually by closing NordLocker, or set it to lock itself after a delay) no one can access them, even if they have physical access to your computer.
Eliminate any possible unencrypted copies of the file
In this section we are assuming that after you encrypt a file you want to eliminate all unencrypted copies from your system. If you use 7-zip or Microsoft Office to encrypt files, it is likely that Windows 10 still has one or more temporary copies of the unencrypted files stashed on the disk. To be safe, you will want to delete any unencrypted originals and all temporary files once you are done encrypting things.
How to delete any possible unencrypted copies of the file
- First, with 7-zip or NordLocker, make sure to delete the unencrypted original of the file.
- Click Start, then type temporary into the search box. In the menu that appears, select Delete temporary files. This opens the Storage settings window.
- Windows 10 scans your system and displays a list of file types that are stored on the various disk drives of your system. Select Temporary files to see a list of the file types that are available to delete.
- In that list, set the Temporary files and Recycle Bin checkboxes, then click the Remove Files button at the top of the list to obliterate any unencrypted copies of the file that might still be floating around on your system.
How to encrypt hard drives on Windows 10
When it comes to disk encryption on Windows 10, BitLocker Device Encryption is the tool that Microsoft provides. Built into Windows 10 Pro and Enterprise, BitLocker Device Encryption does exactly what it sounds like – it encrypts all the storage devices in your system.
This sounds ideal, but there are some drawbacks to using BitLocker.
- If BitLocker Device Encryption wasn’t preinstalled and configured on your computer, it can be a real headache to install and configure. Check out this Overview of BitLocker Device Encryption posted on Microsoft.com.
- BitLocker has different capabilities depending on what hardware your computer has built onto its motherboard.
- As mentioned earlier, BitLocker only works on Windows 10 Professional and Enterprise systems.
Happily for us, there is a great alternative available. Called VeraCrypt, it addresses all of the drawbacks we just saw:
- VerCrypt is significantly easier to install than BitLocker.
- VeraCrypt is not dependent on special hardware built into your computer.
- VeraCrypt works on every version of Windows 10, not just Pro and Enterprise.
VeraCrypt is Free, Open Source Software (FOSS), which we really like. Without getting into the OpenSource vs Proprietary software argument that plagues the computer world, from our perspective, FOSS software is generally considered more secure, and of course is free to use. Once VeraCrypt is installed, all you need to do is enter your VeraCrypt password whenever you start the computer.
Given all that, you know where we’re going with this. In the following section we’ll walk you through installing VeraCrypt on one of our lab machines.
Ready?
How to install VeraCrypt for Windows 10 hard drive / disk encryption
While installing VeraCrypt is much simpler than the alternative, there is more to it than just launching an installer and pressing Okay a few times. And if you mess up, there is a chance you will lose files or even access to the entire disk drive.
We suggest you read through the instructions that follow before starting the process. If you are not confident you can complete the steps shown, or if you have a bad habit of losing important passwords, it is better to skip this type of encryption.
Installing VeraCrypt
Here are the steps to install VeraCrypt on Windows 10:
- You will need a standard USB drive for the VeraCrypt Rescue Disk you will create later. Find yourself a USB drive you can dedicate to this, and format it as FAT or FAT32 so it is ready when we need it.
- You will also need a program that can unzip files. We recommend 7-zip, the free and open source zip program we have discussed elsewhere in this guide. You can download 7-zip here.
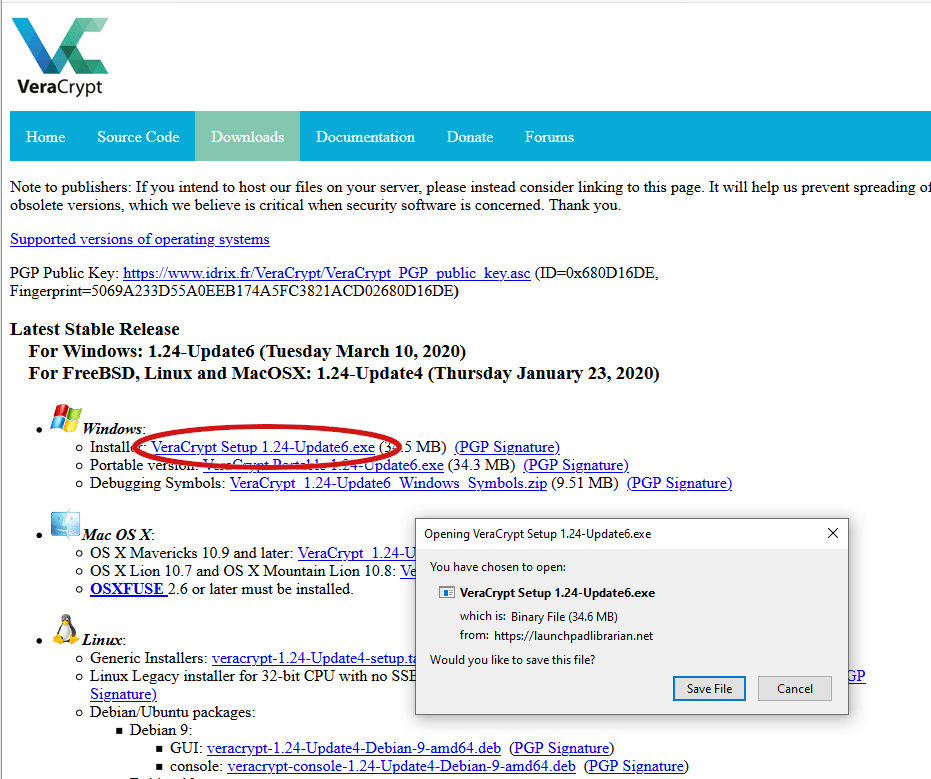
- Go to the VeraCrypt download page and look for the Windows Installer setup link (circled in red in the following image). Click the link. In the dialog box that appears, click Save File to download the installer.
- Launch the VeraCrypt setup program and accept all the default options displayed in the Setup Wizard.
- After a moment, VeraCrypt should display a message stating that “VeraCrypt has been successfully installed.”
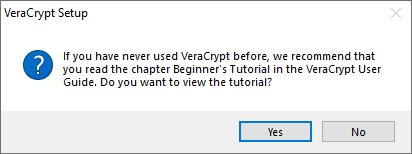
- Click OK to close the Wizard, then Finish to complete the installation process. VeraCrypt will display the message shown below.
- If you are new to VeraCrypt, it is worthwhile to follow the advice given here and view the tutorial. Click Yes to view the tutorial, or No to skip it. Either way you go is fine since we will walk you through the rest of the steps right here.
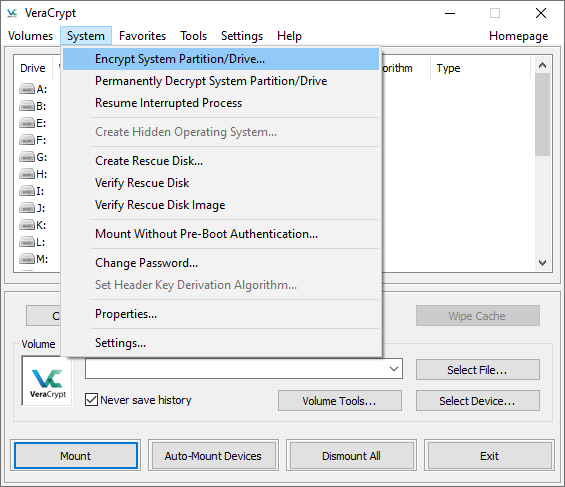
- Launch VeraCrypt. Select the System menu, then Encrypt System Partition/Drive.
- The VeraCrypt Volume Creation Wizard appears. The Wizard asks what type of system encryption you want: normal, or hidden. Normal simply encrypts the system partition and is what we want, so select Normal, then click the Next button to continue.
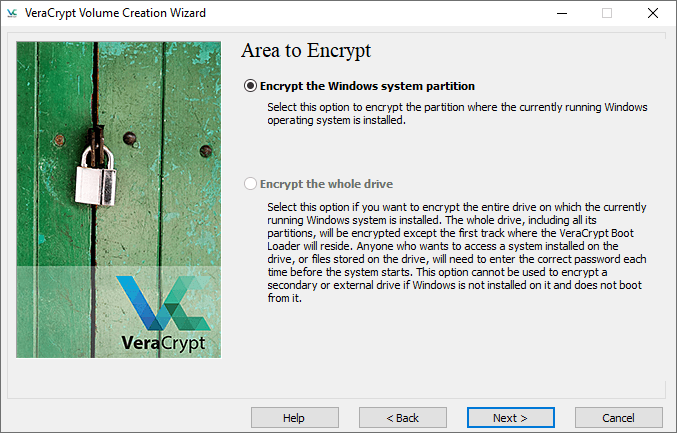
- Next the wizard will ask you whether to encrypt just the Windows system partition, or the entire drive. If you have multiple partitions with important data, you can encrypt the whole drive. If you only have one partition on the drive (as we do on this computer), VeraCrypt will only let you select the Encrypt the Windows system partition option. Make your choice and click Next when ready.
- The Wizard displays the Number of Operating Systems window. Is your system dual-boot or multi-boot (you can start the system in various operating systems)? If so, select Multi-boot. Otherwise, select Single-boot. Click the Next button to continue.
- The Wizard displays the Encryption Options window. We recommend you choose AES for the Encryption Algorithm, and SHA-256 for the Hash Algorithm. Both are widely-used algorithms that will serve you well. Click the Next button to continue.
- The Wizard displays the Password window. It is important to choose strong passwords if you want your system to be secure. Many password manager programs (such as our top pick, Bitwarden) include password generators that can help you create a strong one. Note: VeraCrypt will hassle you about it if you choose a password less than 20 characters long. Click the Next button to continue.
- The Wizard displays the Collecting Random Data window. You will be required to move your mouse around randomly within the window. This additional randomness increases the strength of your encryption keys. Once the randomness meter at the bottom of the window is full you can click the Next button to continue.
- The Wizard displays the Keys Generated window. There is nothing you need to do here except click the Next button to continue.
- The Wizard now forces you to create a VeraCrypt Rescue Disk (VRD). The explanation for this appears in the following image. If you want to live dangerously you can set the Skip Rescue Disk verification checkbox to avoid being forced to create a physical rescue disk. Make note of where VeraCrypt says it will store the ZIP image, then click Next to continue.
- Unless you selected the Skip Rescue Disk verification option in the last step you are now going to be forced to create a physical rescue disk and allow VeraCrypt to inspect it to see if you did it right. VeraCrypt doesn’t tell you how to do this or assist in any way, but we can. Remember finding a spare USB drive a little while ago? It is time to insert that USB drive into your system. Now navigate to the location where VeraCrypt stored its Rescue Disk in the previous step. Use 7-zip (or another ZIP program) to extract the files in the VeraCrypt Rescue Disk.zip file directly to the root of the USB drive. Once that is done, click Next so VeraCrypt can check your work.
- Assuming all went well, you should now see the Wizard’s Rescue Disk Verified window. Remove the USB drive from the computer and click Next.
- The Wizard displays the Wipe Mode window. For any normal uses, you don’t need to worry about this. Make sure the Wipe Mode is set to None (fastest) and click Next to continue.
- We are getting there. The Wizard now displays the System Encryption Pretest window. This is where VeraCrypt checks to make sure that the encryption process will actually work, rather than assuming it will work and trashing your system if it doesn’t. The image below explains what will happen in detail. Click Test to see how it goes. Note that VeraCrypt will probably ask you to print some more warnings and emergency procedures and the like before it actually does the test, so be ready for that.
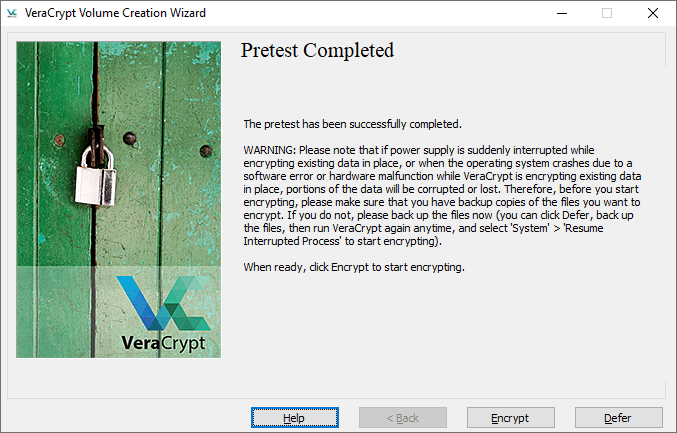
- Assuming everything went well, you should see the following window once you have successfully restarted your computer and passed the system encryption pretest.
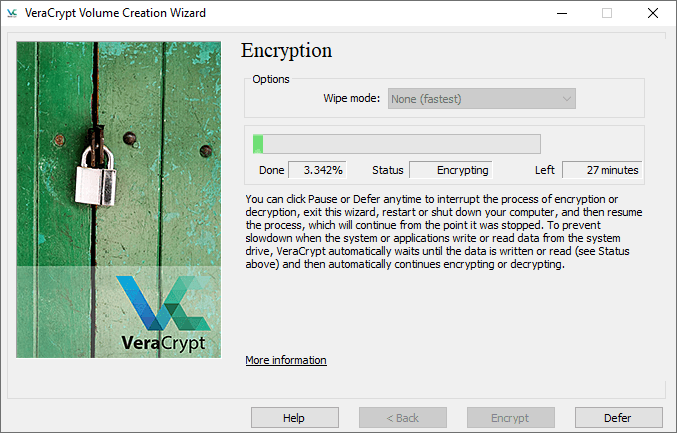
- VeraCrypt recommends you to make backup copies of all your important files before you encrypt your system. This will allow you to recover if something drastic like a power failure or system crash occurs in the middle of the encryption process. Once you are done with that, take a deep breath and click Encrypt. VeraCrypt will display more documentation it wants you to print if possible, covering when to use the VeraCrypt Rescue Disk after the encryption process is complete, then will finally begin the actual encryption process. You’ll be able to monitor the progress of the encryption, which is a nice touch.
- Once the encryption is done, you will need to enter your VeraCrypt password every time you start the computer.
How to encrypt files conclusion
Encrypting important information is one of the best things you can do to protect yourself from everyone who is trying so hard to get their hands on your personal information.
In this guide we covered techniques that Windows 10 users can use to encrypt individual files, folders, and entire drives on their Windows systems. While no one can guarantee that your data will be 100% safe against any and all attacks, the simple act of encrypting your most important data can make a big difference.
Let us know which encryption techniques you decide to apply in the comments below.
And if you need a solution for storage, check out our best cloud storage guide.

I use File Protect System-SE ( https://www.microsoft.com/store/apps/9P5SXJ8BL4GM ).
A professional solution with a lot of functionality. Very easy to use. Intuitive interface behind which hides a powerful post-quantum encryption system.
What impressed me the most was the file package handling capabilities. This is a unique solution.
In addition, there are built-in modules for steganography, management of the crypto primitives used, output of control reports, etc.
This is an app made by professionals for professionals.
I think this little-known application guarantees the comprehensive protection I need in my daily activities.
first I wanted to say thank you for taking the time to write this article. I had several questions regarding Veracrypt as a not-so tech savvy person:
1. I cannot encrypt the whole disk, only the system drive (the other options is greyed out). I did some research online and found out that it had something to do with GPT/MBR or whatever it is called? I followed a youtube video and converted my disk to mbr with a program called diskpart, but I could not boot Windows after that. After following several videos, I reinstalled Windows but am unable to convert my drive to MBR. It states that it is MBR before installing Windows but as soon as the installation is completed, the drive is still GPT? Can you help and explain how I can convert GPT to MBR (and if that is actually necessary — like what is the ACTUAL difference between “whole drive” and “system drive only” encryption and is my data safe anyway?
2. Can you also explain some of the more advanced settings found under the “performance/driver configuration” option in Veracrypt ? I read in another article that RAM encryption is not enabled by default? Should I enable it ( I thought that whole system encryption would also encrypt RAM and why is that not the place? Like is data written on RAM unencrypted by default?).
3. Could you also make a guide to show how we can delete data safely on SSD? Cuz I — what a shocker — read online that this was not possible on an SSD ? I use a program called “Ascomp secure eraser” and have recently switched to a new program called “bleachbit” but do not know if there is any difference ? (Maybe you coukld review both programs). What I noticesd is that Bleachbit does not give the user the option to have data deleted several times (e.g. peter Gutmann method and how the rest of them are called). Also note that I do not want to erase my whole C drive, just some folder/file on my PC (i only have one ssd) so that it cannot be recovered anymore ?
Again tanks for your help in showing us how to stay private cheers
Hello,
I also had a problem with shredding files and free disk space sanitization on the SSD.
As I wrote, I have been using File Protect System-SE, which has built-in modules for shredding and cleaning digital media. This is a professional solution and I have personally tested the results, using specialized means.
The reason for this is that, unlike other similar solutions, FPS-I uses hybrid cleaning. It is a combination of encryption and erasure. In this case, even if an attempt is made to restore the SSD using specialized hardware, the result will be unusable information.
It is very easy to use. The interface is intuitive and easy to understand.
You can test FDM II spe ( https://www.microsoft.com/store/apps/9MZ58Q8WW5KP ), which is a specialized application only for data destruction, but one of my colleagues also uses it for protection, because it has Crypto File Manager inside.