
This in-depth guide examines the best encrypted email services to keep your emails, inbox, and attachments secure.
Despite being one of our oldest methods of online communication, email is still one of the most popular. Untold billions of email messages fly around the world every day, carrying personal and business information that we depend on. This makes email services a prime target for hackers and spies.
Unfortunately, experience shows that most large email providers do not respect user privacy. For example:
- Gmail was caught giving third parties full access to user emails and also tracking all of your purchases. (See our guide on the best Gmail alternatives.)
- Advertisers are allowed to scan Yahoo and AOL accounts to “identify and segment potential customers by picking up on contextual buying signals, and past purchases.”
- Yahoo was also caught scanning emails in real-time for US surveillance agencies.
And the problem runs deeper than the policies of your email provider.
Top encrypted email services
- Proton Mail – Best Swiss encrypted email service
- StartMail – Server-side email encryption
- Mailfence – User-friendly email encryption
- Tuta – Private email service with unique encryption
- Mailbox.org – Email encryption with suite of features
- Posteo – Affordable service with layered encryption
- Runbox – Reputable and affordable email
- CounterMail – Premium Swedish encrypted email service
- Kolab Now – Solid email encryption aimed at businesses
- Soverin – Encrypted email service from the Netherlands
Why do you need email encryption?
Once you see the scope of the problem, we think you’ll agree that you need to encrypt at least some of your emails.
Data breaches
Breaches of the databases at companies large and small expose hundreds of millions, if not billions of records per year. A part of those records are email messages, stored on mail servers around the world. Bad guys of all stripes target email messages because they can contain valuable information that can be sold or used for fraudulent activities. This includes financial data, vacation plans, corporate strategies, and personal data.
Pervasive surveillance
Years ago, Snowden and others revealed the vast scope of surveillance programs that are being run around the world. Many of them are marginally legal. Since then, the problem has only grown, with governments around the world sucking up every bit of email data they can get their hands on. Private companies are in on it too, as they can profit from collecting and selling your email content.
Because most email services store your data on their servers in unencrypted form, you have no real privacy. Hoping that big free email providers like Gmail won’t read your messages and use what they find for their own purposes, is largely naive.
For example, we know that Gmail reads through every message you send or receive looking for information like airline reservations to add to your calendar. Then there is Smart Reply, an optional feature that reads messages so it can suggest short replies that might be relevant to the content of that message. While features like these can be useful, they can only work if Gmail can read and, at least partially, understand your email messages.
Location is important
Where your email service is located can have a huge impact on your email privacy. While jurisdictions like Switzerland have laws that protect your online privacy, others (including the United States and its Five Eyes friends) have laws in place to erode it.
Leaving aside all the folks who can legally stick their nose into your email communications, there are also the illegal peeping Toms. While email services take steps to protect your messages from outsiders (aside from themselves), these steps are not foolproof.
Data breaches do result in hackers getting their hands on the email account passwords, which can result in identity theft, fraud, and other crimes. Unfortunately, hackers often manage to easily get access to people’s inboxes. Once inside, there is nothing to stop them from reading your email and stealing sensitive personal information.
The fact is, email security is a big issue, even today. There are a lot of ways in which your email privacy can be compromised. In this guide, we’ll talk about various scenarios in more detail, and I’ll show you how to encrypt your email to protect against at least some of these problems.
What are the best encrypted email services?
As noted above, we think the best solution is to actually switch to an email provider that supports end-to-end encryption. Luckily, there are many encrypted email services that use one of three different methods:
- PGP, which stands for Pretty Good Privacy, is one of the most popular encryption protocols. It is supported by most secure email providers.
- Some email services rely on a unique encryption protocols. For example, Tuta uses a combination of AES and RSA encryption.
- Many email services also allow you to send a link to an encrypted message that can be accessed with a shared password rather than private key.
If you are open to switching to a secure email service with built-in encryption, we’d encourage you to explore our guide on secure and private email services.
Best Encrypted Email Services in 2024
Now that we know what to look for, it is time to do an overview of 10 best encrypted email services.
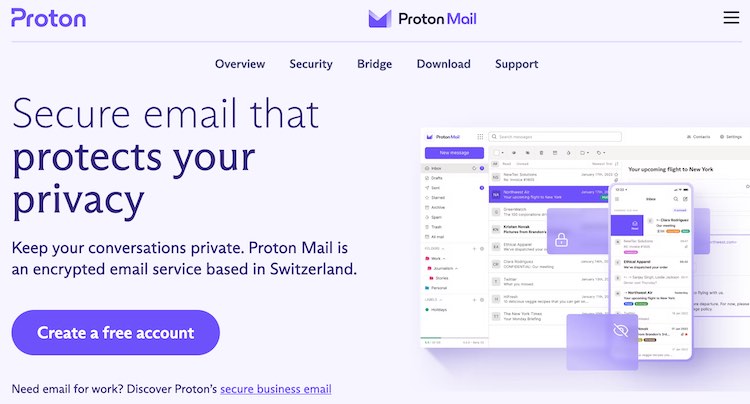
1. Proton Mail – Best Swiss encrypted email service
| Based in | Switzerland |
| Storage | 15-500 GB |
| Price | $3.49/mo. |
| Free Tier | Up to 1 GB |
| Website | Proton.me |
Proton Mail is one of the most popular email services around, and that isn’t just a fluke. This encrypted email provider is located in Switzerland, one of the best jurisdictions when it comes to user privacy. Proton Mail was developed by MIT and CERN academics, which is a clear indication that this is an ambitious project.
The end results is an intuitive, private, and encrypted email service with 70+ million users. Proton Mail utilizes end-to-end PGP encryption to protect your contacts, calendar, and emails (including their attachments). It has recently added Tracking Links Protection feature which removes tracking pixels from all messages. All of your data is saved on the encrypted Swiss servers located in an underground bunker.
However, since Proton Mail uses PGP, email address and subject line of each message is unencrypted.
Switching to Proton Mail from other services, like Gmail, is very straightforward. After subscribing, you’ll be able to access Import-Export app which lets you quickly transfer all sensitive messages and contacts.
Proton Mail extra features
Proton Mail also has some additional tools that you may expect from a paid service.
- Proton Mail Bridge – allows Proton Mail to connect to other email services.
- Proton Calendar – easily manage your meetings and personal appointments.
- Proton Drive – store and share your important files via secure links.
- Proton VPN – a solid VPN is available by subscribing to Proton Unlimited plan. If you are intrigued, you may want to take a look at our ProtonVPN review.
- iOS and Android apps
See all Proton Mail features here >>
All in all, Proton Mail is a top encrypted email service with plenty of additional tools. If you are satisfied with PGP encryption and need extra features that are present in apps like Gmail, Proton Mail is well worth your money.
For more information, take a look at our Proton Mail review.
+ Pros
- End-to-end (E2E) and zero-access encryption for Email, Calendar, and Contact information
- Operates under Swiss jurisdiction
- All data stored on servers in Switzerland
- Apps for Android and iOS mobile devices
- Web client, encryption algorithms, Android and iOS code are all open source
- Support for custom domains
- Strips IP address from emails
- Can be used with third-party email clients through the Proton Mail Bridge feature
- Can import contacts and emails
– Cons
- Subject lines not encrypted
- May require personal information for verification of new accounts
Proton Mail Coupon:
Get 33% Off Proton Mail with two-year plans using the coupon below:
(Coupon is applied automatically.)
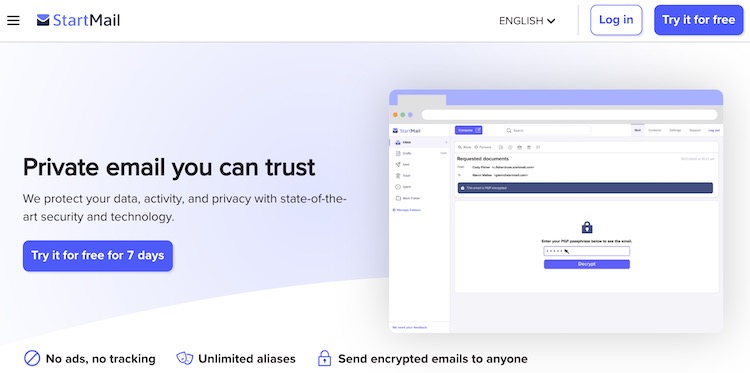
2. StartMail – Server-side email encryption
| Based in | The Netherlands |
| Storage | 10-20 GB |
| Price | $3.00/mo. |
| Free Tier | 7 day trial |
| Website | StartMail.com |
StartMail is a reliable email provider based in the Netherlands. It was made by the same team that developed a private search engine called StartPage. This initially made us a bit skeptical because Startpage was acquired by System1, which is not a good look from a privacy standpoint. However, we’ve learned that StartMail operates as a separate entity and follows the Personal Data Protection Act.
The Netherlands is one of the safer privacy jurisdictions in Europe. After reading through StartMail’s privacy policy, it seems that this service will only collect a minimum amount of user data that is required for it to operate smoothly.
Email migration is convenient, since StartMail has SMTP and IMAP support. This means that you can use it with third-party email services and quickly import your contacts and messages.
StartMail also lets you create a custom domain and includes 20 GB of storage space.
Disposable aliases and unique encryption
StartMail allows you to create disposable email addresses by using Email Aliases feature. This is useful when you’re required to provide an email to a service you don’t want to subscribe to. Alternatively, you can use the same feature to organize your emails, by using different alias for work and private messages.
What differs StartMail from similar services is that it encrypts your email directly on the server, instead of your browser. There seem to be many benefits to this, which are presented in companies white paper. The arguments are sound, but the jury is still out if this is a better way to protect your data.
All in all, StartMail is a solid encrypted email service, but it does have a few downsides. We recommend using their 30-day free trial to explore the service and see if it is the right choice for you.
+ Pros
- Create unlimited email aliases
- PGP end-to-end encryption
- Easy contacts and email migration
- Organize your inbox with filters
- Minimalistic design
- No ads. No tracking. No spam.
- Flexible spam filter
- Unlimited burner aliases
- Anonymous cryptocurrency payments
- Use custom domain
- Compliant with GDPR
– Cons
- Short trial period
- Free version unavailable
- Lacks Calendar, Notes, and File storage
To go more in-depth, take a look at our StartMail review.
StartMail Exclusive Coupon:
Get 50% Off any subscription plan with the coupon below, no activation code required:
(Coupon is applied automatically.)
3. Mailfence – User-friendly email encryption
| Based in | Belgium |
| Storage | 5-50 GB |
| Price | €3.50/mo. |
| Free Tier | Up to 500 MB |
| Website | Mailfence.com |
If you are looking for encrypted email that has a bit more features, Mailfence might be the right choice for you. Along with email, it also offers file storage, groups, and calendar. Mailfence is located in Belgium, which is a solid privacy jurisdiction.
This email supports OpenPGP encryption, so it is compatible with many third party email services. Still, email addresses and subject lines in each message are unencrypted, meaning that somebody can still read them.
Mailfence has a user-friendly and attractive interface with some advanced features.
If you are experiencing problems, you can always contact their support team that’s available via phone or email. Mailfence lets you pay with cryptocurrency for your subscription, letting you remain completely private.
Importing contacts and messages is easy, since Mailfence supports SMTP, POP, IMAP, and Exchange ActiveSync. This email service can be accessed via browser, but there is also a progressive web app that works on iOS and Android devices.
Note: Recently, Mailfence has dropped POP/IMAP support for Gmail servers due to strict financial requirements.
In short, Mailfence seems like a reliable service that provides both email encryption and suite of productivity tools. It’s highly secure, although there are some areas that could be improved.
Learn more about this encrypted email service by reading our Mailfence review.
Website: https://mailfence.com/
4. Tuta – Private email service with unique encryption
| Based in | Germany |
| Storage | 1 – 1,000 GB |
| Price | €3.00/mo. |
| Free Tier | Up to 1 GB |
| Website | Tuta.com |

Tuta (formerly Tutanota) is an encrypted email service from Germany that is also open source. This is a private company without outside investors, so they are not pressured to compromise user privacy in exchange for money. Tuta’s goal is to provide their users with a premium level of security while also remaining user-friendly service.
Tuta Mail doesn’t rely on PGP and instead combines AES and RSA encryption. By doing this, they are able to encrypt both – the email address and the subject line that comprise message headers. Furthermore, Tuta Mail is in the process of updating its encryption protocol to add post-quantum cryptography and removes IP address from messages.
So, you get a full end-to-end encryption of your contacts, the calendar, and inbox. This data is encrypted at rest in Germany, where the company’s servers are located. All in all, Tuta gives you two options for sending emails:
- By sending messages to Tuta user, its system will encrypt and decrypt messages as needed. The process the super straightforward, making it perfect for casual users.
- If you email user that doesn’t use Tuta, you’ll have the option to send the message without encryption or provide an email with a link to your message. For this to work, you will have to send a password key separately to your recipient, so that they are able to open the email. We recommend that you send this through another channel, like encrypted messaging app. What is particularly neat about the Tuta implementation is that recipients of the encrypted messages can see the entire thread of messages.
Lack of PGP support
One of Tutanota’s biggest strengths can also be seen as weakness. Since it doesn’t have the support for PGP or open PGP, you will be unable to send encrypted messages to users that rely on alternative email services. According to Tutanota cofounder Matthias Pfau, this is a compromise that the company won’t take. To find out more, we recommend reading his article Let PGP Die: Why We Need a New Standard for Email Encryption.
Another drawback is that Tutanota doesn’t allow you to import emails from other providers as there is no SMTP, IMAP, or POP support. Granted, the company said that they’re thinking about implementing this, but it has been a few years without any resolution about the matter.
To combat all of this, Tutanota has created a solid support for multiple platforms. It is available on Windows, Mac OS, Linux, Android, and iOS. There is even a that app, which makes things more convenient.
All in all, Tutanota is one of the safest encrypted email services around. However, this comes at a price – lack of compatibility. If that doesn’t bother you, we highly recommend that you give it a try.
Take a look at our in-depth Tutanota review for more info.
Website: https://tutanota.com/
5. Mailbox.org – Email encryption with suite of features
| Based in | Germany |
| Storage | 2 – 100 GB |
| Price | €1.00/mo. |
| Free Tier | None |
| Website | Mailbox.org |
Mailbox.org is one of the most affordable encrypted email services. Despite its low pricing, we are talking about a premium secure messaging app. Along with it, you will also get many productivity tools, like Calendar, Drive, Address Book, Portal, etc. It’s goal is to be a jack-of-all-trades, but lets see how good it is at keeping your data secure.
Mailbox.org is based in Germany, which is very good from privacy standpoint. Its servers that encrypt all your data at rest are also located there. This service supports PGP encryption, so you can easily migrate your contacts from other service. This also lets you use third-party apps for Mailbox.org, which is crucial as there is no native client for mobile devices.
Mailbox subscription start at €1/month, but you can try it basically for free thanks to its 30-day refund policy. Pricier plans include more storage space and additional features useful for business and private users.
See our Mailbox.org review for more test results and more information.
Website: https://mailbox.org/
6. Posteo – Affordable service with layered encryption
| Based in | Germany |
| Storage | 2 – 20 GB |
| Price | €1.00/mo. |
| Free Tier | None |
| Website | Posteo.de |
Posteo continues the trend of affordable yet highly secure German email services. It was founded in 2009, so this service has a lot of experience under its belt. Posteo is very similar to Mailbox.org, although it lacks custom domains and trial mode.
Along with encrypted email, you will also get notes, calendar, and contacts feature. Posteo also has email aliases and solid spam filter, so you can effectively eliminate unwanted messages. Email migration is also straightforward, and you can copy messages and contacts from up to three email accounts.
Posteo uses a layered encryption that is a combination of OpenPGP and S/MIME encryption, both of which are intuitively implemented. It uses no-logs policy and strips the IP address from all of the messages. On top of that, this service uses two-factor authentication and advanced security protocol DANE, which stands for DNS-Based Authentication of Named Entities.
Although you can’t pay with cryptocurrency, Posteo lets you make anonymous payment by sending the cash via mail. If you decide to pay with PayPal or credit card, it won’t tie in your payment details with your account. This way, you will leave a minimal digital trail.
Unfortunately, Posteo doesn’t have their native mobile and desktop app, but you can easily combine it with third party email services.
You can find even more details in our Posteo review.
Website: https://posteo.de/
7. Runbox – Reputable and affordable email
| Based in | Norway |
| Storage | 2 – 50 GB |
| Price | $1.66/mo. |
| Free Tier | 30 day trial |
| Website | Runbox.com |

Runbox is a Norwegian encrypted email service that’s been on the market for 20+ years. A part of their success can be tied to its jurisdiction, as Norway takes user privacy very seriously. Plus, all of Runbox servers are run from Norwegian data centers. All in all, this service has a spotless track record.
From a physical standpoint, its security is excellent. However, we ain’t sure that it’s enough, since Runbox doesn’t provide end-to-end encryption. This means that your emails aren’t encrypted on Runbox servers, so technically their staff can access all of your sensitive data. Granted, it is possible to use PGP with Runbox, although this feature isn’t completely integrated. In the end, some users will have to decide if they trust Runbox enough for storing their personal data.
Runbox is currently a bare-bones service and its interface looks a bit outdated. This will change when Runbox 7 goes live, as it will add tasks and calendar section. However, we don’t know when that will happen as this project has been in beta for quite a while. For now, lets focus on their full service.
Convenient migration
Runbox supports SMTP, IMAP, and POP protocols, so you can quickly copy all of your contacts and emails when switching. Depending on plan you choose, you’ll be able to make up to 100 aliases that you can use to stop spam and organize your messages. Storage space also varies, and you can get up to 250 GB for emails and 25 GB for storing files.
Runbox is currently only browser-based, so you will have to use third-party apps if you want to effectively use it on mobile devices.
We advise that you test Runbox out before committing, as there is a free trial available. If you suddenly change your mind, you can get a refund within the first 60 days.
We also did a complete Runbox review that give you a full picture of the service.
Website: https://runbox.com/
8. CounterMail – Premium Swedish encrypted email service
| Based in | Sweden |
| Storage | 4 GB+ |
| Price | $4.83/mo. |
| Free Tier | 7 day free trial |
| Website | CounterMail.com |

Note: CounterMail is currently an invite-only service and you won’t be able to access it without an invite.
CounterMail is a minimalistic email service with end-to-end encryption. It is fully based in Sweden, which is another excellent jurisdiction.
CounterMail has OpenPGP encryption and follows a no-logs policy by only using RAM mode servers that can’t store user data. Both of these features can also be found in premium VPN services like NordVPN. There’s also another layer of encryption (RSA and AES-CBC) that will protect you from Man-In-The-Middle attacks and identity theft.
By default, CounterMail will remove your IP address from the message headers. Every email and its attachments are stored encrypted at rest on Swedish servers, so even CounterMail won’t be able to access your private data. When it comes to security, this encrypted email service has a really high standard.
However, CounterMail also has some drawbacks. With it, you won’t get any additional features like notes or calendar. CounterMail also has an outdated user interface, which you will surely deter some users. But, if everything you’re looking for is a secure encrypted email and the ability to quickly migrate your messages and contacts, CounterMail is a really good option.
Website: https://countermail.com/
9. Kolab Now – Solid email encryption aimed at businesses
| Based in | Switzerland |
| Storage | 5 GB+ |
| Price | $5.47/mo. |
| Free Tier | 30 day trial |
| Website | KolabNow.com |
Kolab Now is a secure service from Switzerland that offers a full suite of features. Aside from encrypted email, you will also get a calendar, notes, file storage (5GB), and many other features that make it a solid option for businesses.
This service uses an E2E encryption Perfect Forward Secrecy. You will be able to import all of your messages, as Kolab Now has SMTP, IMAP, and POP support. All of your sensitive info is stored encrypted at rest on servers in Switzerland.
Kolab Now is a bit more expensive, but that is to be expected considering all of the features that you get. If you are also looking for a productivity tool, it is well worth considering.
Website: https://kolabnow.com/
10. Soverin – Encrypted email service from the Netherlands
| Based in | The Netherlands |
| Storage | 25 GB |
| Price | €3.25/mo. |
| Free Tier | No |
| Website | Soverin.net |
Soverin is a budget encrypted email service based in the Netherlands, an excellent privacy jurisdiction. This is a bare-bones service, so you will only get file storage in addition, though it is pretty sizeable (25 GB).
Soverin stores user data on servers in Germany, however, it is not encrypted at rest. So, its employees can technically sift through your emails if they want to. Soverin offers SSL/TLS encryption and also strips IP addresses from email headers.
Old emails can be easily imported, as this service is compatible with most third-party email apps. Soverin also strictly adheres to European privacy laws, which are generally set in users favor. All in all, this is a decent service that still needs to work on its email encryption in order to become a serious contender.
Website: https://soverin.net/
Honorable mention: Skiff Mail – US encrypted email service

Skiff Mail is a promising new encrypted email service located in California. It caught my eye since it uses PKI end-to-end encryption instead of PGP. Since PKI doesn’t rely on public and private keys or passphrases to access emails, it is more convenient to casual users.
By subscribing to Skiff Mail, you will also get 15GB of space for your email and other important files. Transferring your messages and contacts is also straightforward, as you can import both by copying .EML file.
This is a fairly affordable service, with subscription plans that start from $3/month. With it, you’ll get access to disposable aliases, along with Pages, Calendar, and Drive sections. Since Skiff Mail lets you create a custom domain, you can also use it professionally.
All of this looks fine on paper, but you’ve got to remember that Skiff Mail is based in the US. This immediately makes us skeptical since this jurisdiction doesn’t have the greatest reputation. Luckily, you can test Skiff Mail for free and see for yourself if it is secure enough for your purpose.
Website: https://skiff.com/
Concerns with US-based encrypted email services
There’s a good reason why we didn’t include many US services, and it concerns privacy and data security. There are a lot of examples of US tech companies being forced to hand over private data to authorities without notifying its users. This is particularly prevalent with email services. Here are some known examples:
- Lavabit – Lavabit was a privacy-focused email based in the US that was forced to shut down when the owner refused to give up the encryption keys to government agents.
- Riseup – Another US email service catering to privacy-minded users, Riseup was hit with data requests and was forced to comply.
Here’s a quote describing the Riseup situation, which could affect any US-based email service:
After exhausting our legal options, Riseup recently chose to comply with two sealed warrants from the FBI, rather than facing contempt of court (which would have resulted in jail time for Riseup birds and/or termination of the Riseup organization).
There was a “gag order” that prevented us from disclosing even the existence of these warrants until now. This was also the reason why we could not update our “Canary” [warrant canary that warns users about these events].
This is why it is crucial to choose an encrypted email service based in a good privacy jurisdiction. If you don’t, your data could quickly become compromised
Encrypted email alternatives
One of the fundamental problems with email is metadata.
Email is structured in such a way that metadata is very difficult to conceal from third parties. Email headers can reveal a lot of private data. What’s worse, PGP, the most widely-used encryption protocol, does not encrypt subject lines. This exposes further data to third parties and potential adversaries.
Another problem is that most people simply do not want to use an encrypted email service and/or encrypt messages. This isn’t an easy problem to get around — unless you use an alternative to email.
Best alternative: encrypted messaging service
We’d recommend using a good encrypted messaging service if you are really concerned about privacy and data security. Most of them do a very good job encrypting data, collect little (or no) metadata, and offer stronger encryption than many email services.
Some of our favorite options are Signal, Session, and WickrMe. There are many more alternatives, which you can check out in our best secure messaging services article.
Conclusion on encrypting email
In this world where the assaults on our privacy grow by the day, it is important to take whatever steps we can to defend ourselves. One place you should protect is in your email inbox. Unless you want a vast number of entities (from Google AIs to foreign spies) reading your email messages and doing who knows what with the information they find there, you need to encrypt your email.
Remember: If you aren’t up for rolling your own end-to-end encryption system, you can move your most important email connections to one of the private email services.
ProtonMail, for example, has a free version that handles E2EE for you and uses a system much like Gmail’s Confidential mode to send private messages to people who don’t use ProtonMail. And if your encrypted messaging needs aren’t too intense, you can get by just fine with the free version of ProtonMail or another one of our recommended encrypted email providers.
Best encrypted email services FAQ
What is the best email encryption service?
While this will mostly depend on your needs, we found Proton Mail to be one of the safest encrypted email services.
Can encrypted emails be hacked?
Encryption doesn’t stop hackers from intercepting your messages. However, if they don’t have a private key, all they would get is scrambled data that is totally unreadable.
Is Proton Mail safer than Gmail?
Proton Mail is safer alternative as it has powerful encryption and is based in one of the safest jurisdictions in the world – Switzerland.
This guide on encrypted email was last updated on March 11, 2024.

Leave a Reply