
There is a lot of misinformation being promoted in various privacy circles about Tor. This article will examine some facts about Tor and assess whether it is the infallible privacy tool it’s made out to be by some.
There is a growing chorus of people who blindly recommend Tor to anyone looking for online anonymity. This recommendation often ignores mountains of evidence suggesting that Tor is not the “privacy tool” it’s made out to be.
No privacy tool is above criticism or scrutiny, and each has pros and cons. Unfortunately, Tor has garnered a cult-like following in recent years among people who pretend it’s infallible. Honest criticism of Tor is often met with accusations of “FUD” and ad-hominem attacks, so as not to disrupt the collective Groupthink.
Never mind the fact that the Tor network is a popular hangout for pedophiles and drug dealers – along with the law enforcement these types attract. Today, Tor is being marketed as some kind of grass-roots privacy tool that will protect you against government surveillance and various bad actors.
According to Roger Dingledine (Tor co-founder) and other key Tor developers, getting people (outside the US government) to widely adopt Tor is very important for the US government’s ability to use Tor for its own purposes. In this goal, they have largely succeeded with Tor being widely promoted in various privacy circles by people who don’t know any better.
But is Tor really a secure and trustworthy privacy tool?
Here are the facts.
1. Tor is compromised (and not anonymous)
That governments can de-anonymize Tor users is another well-known point that’s been acknowledged for years.
In 2013 the Washington Post broke an article citing reports that US government agencies had figured out how to de-anonymize Tor users on a “wide scale”. From the Washington Post:
Since 2006, according to a 49-page research paper titled simply “Tor,” the agency has worked on several methods that, if successful, would allow the NSA to uncloak anonymous traffic on a “wide scale” — effectively by watching communications as they enter and exit the Tor system, rather than trying to follow them inside. One type of attack, for example, would identify users by minute differences in the clock times on their computers.
There are also reports of government agencies cooperating with researchers to “break” or somehow exploit Tor to de-anonymize users:
Then in July, a much anticipated talk at the Black Hat hacking conference was abruptly canceled. Alexander Volynkin and Michael McCord, academics from Carnegie Mellon University (CMU), promised to reveal how a $3,000 piece of kit could unmask the IP addresses of Tor hidden services as well as their users.
Its description bore a startling resemblance to the attack the Tor Project had documented earlier that month. Volynkin and McCord’s method would deanonymize Tor users through the use of recently disclosed vulnerabilities and a “handful of powerful servers.” On top of this, the pair claimed they had tested attacks in the wild.
For $3,000 worth of hardware, this team from Carnegie Mellon could effectively “unmask” Tor users. And this was in 2015.
In 2016, a court case brought more information to light about how the US federal government hired software engineers to effectively crack Tor and de-anonymize users.

ARS Technica also discussed this case in February 2016 where they noted:
A federal judge in Washington has now confirmed what has been strongly suspected: that Carnegie Mellon University (CMU) researchers at its Software Engineering Institute were hired by the federal government to do research into breaking Tor in 2014.
The following year, in 2017, more evidence came forward showing how the FBI can see what you’re up to on Tor.
There are also researchers who devised attacks allowing them to de-anonymize 81% of Tor users in the wild. This article came out in 2014, before the Carnegie Mellon research was carried out.
And there’s more…
2017 court case proves FBI can de-anonymize Tor users
The means by which the FBI is able to de-anonymize Tor users and discover their real IP address remains classified information. In a 2017 court case, the FBI refused to divulge how it was able to do this, which ultimately led to child abusers on the Tor network going free. From the Tech Times:
In this case, the FBI managed to breach the anonymity Tor promises and the means used to collect the evidence from the dark web make up a sensitive matter. The technique is valuable to the FBI, so the government would rather compromise this case rather than release the source code it used.
“The government must now choose between disclosure of classified information and dismissal of its indictment,” federal prosecutor Annette Hayes said in a court filing on Friday.
The cat is out of the bag. The FBI (and presumably other government agencies) has proven to be fully capable of de-anonymizing Tor users. Most Tor promoters simply ignore these different cases and the obvious implications.
2. Tor developers are cooperating with US government agencies
Some Tor users may be surprised to know the extent to which Tor developers are working directly with US government agencies. After all, Tor is often promoted as a grass-roots privacy effort to help you stay “anonymous” against Big Brother.
One journalist was able to clarify this cooperation through FOIA requests, which revealed many interesting exchanges.
Here is one email correspondence in which Roger Dingledine discusses cooperation with the DOJ (Department of Justice) and FBI (Federal Bureau of Investigation), while also referencing “backdoors” being installed.
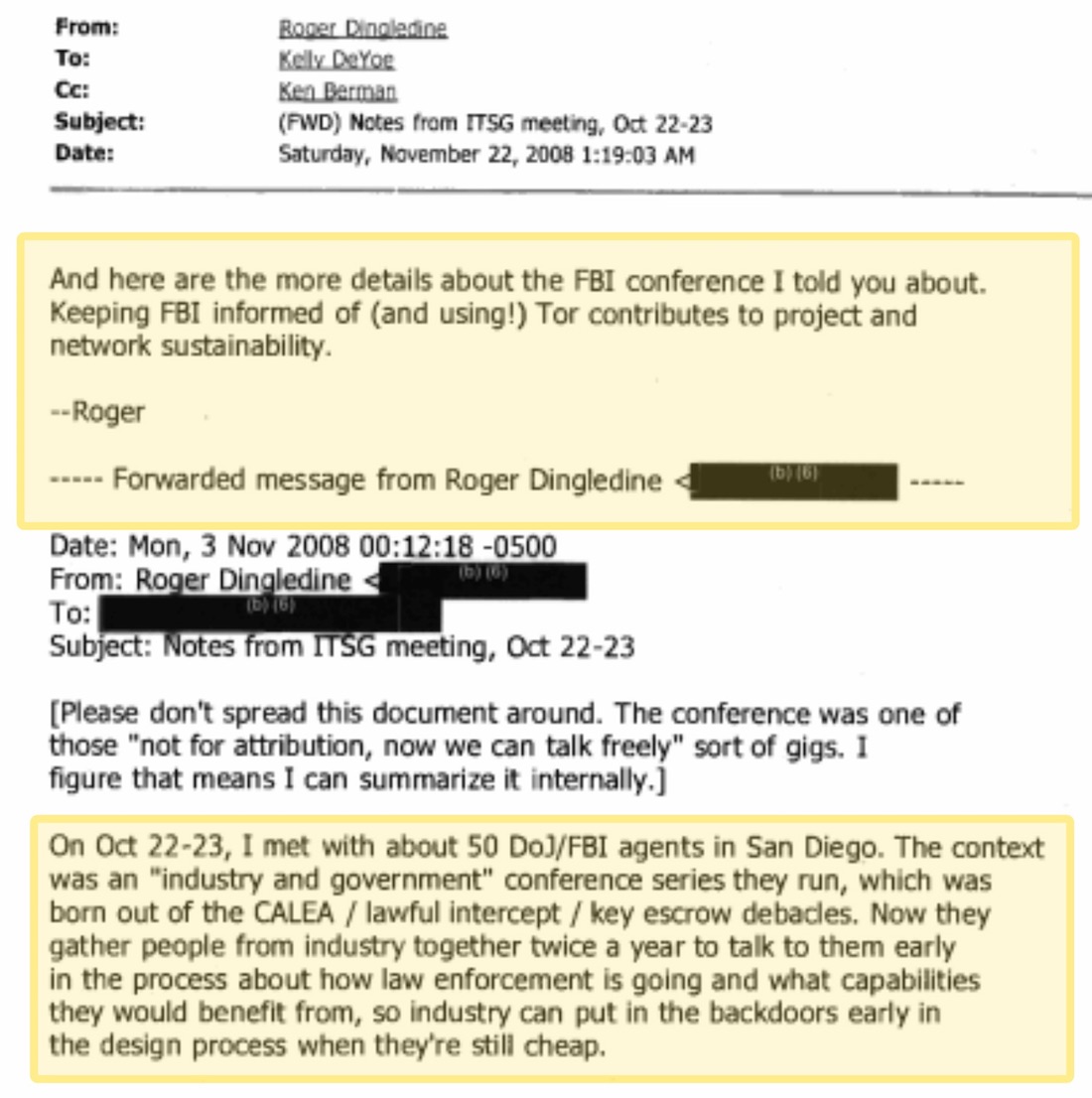
You can see more details from this correspondence here.
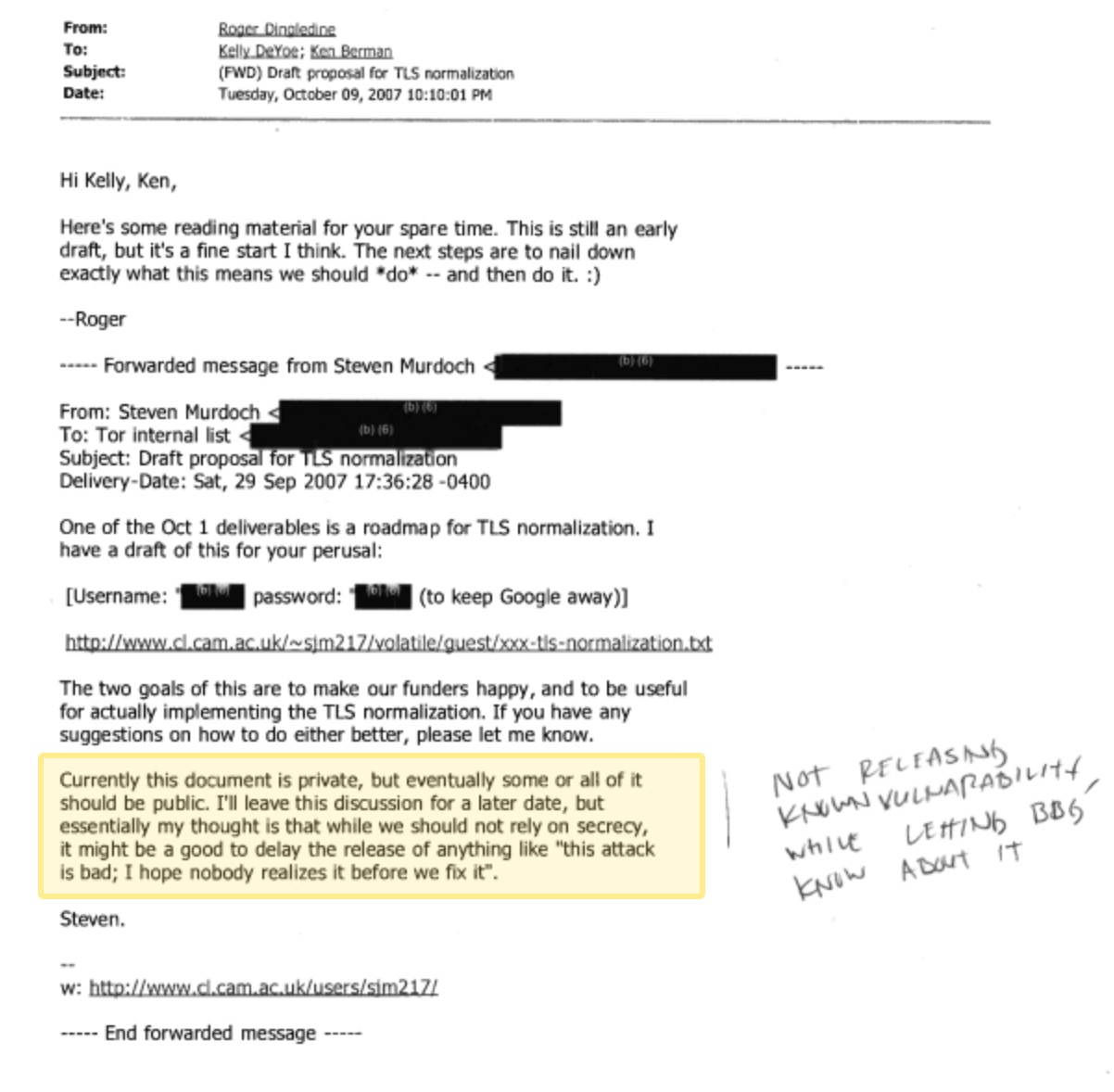
In another exchange below, Tor developer Steven Murdoch discovered a vulnerability with the way Tor was handling TLS encryption. This vulnerability made it easier to de-anonymize Tor users, and as such, it would be valuable to government agencies. Knowing the problems this could cause, Steven suggested keeping the document internal,
…it might be a good to delay the release of anything like ‘this attack is bad; I hope nobody realizes it before we fix it’.
Eight days later, based on the emails below, Roger Dingledine alerted two government agents about this vulnerability:
While there is disagreement as to the seriousness of these issues, one thing remains clear.
Tor developers are closely working with the US government.
The journalist who collected the FOIA documents also suggests that, “Tor privately tips off the federal government to security vulnerabilities before alerting the public.”
Whether or not you agree with the ultimate conclusion of this researcher, the facts remain for anyone who wants to acknowledge them. The big issue is the close cooperation between Tor developers and US government agencies.
You can see numerous exchanges between Tor developers and US government agencies here. (Backup copy of documents.)
And if you really want to dive in, check out the full FOIA cache here.
3. When you use Tor, you stand out like a glow stick
Meet Eldo Kim. He was the Harvard student who assumed Tor would make him “anonymous” when sending bomb threats.
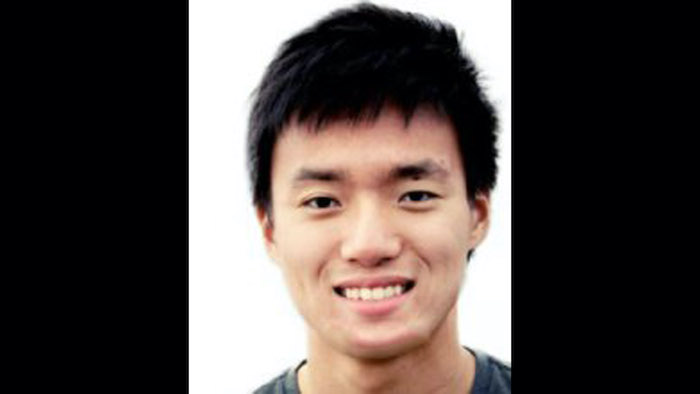
Kim didn’t realize that when he connected to Tor on the university network, he would stand out like a f***ing glow stick.
The FBI and the network admins at Harvard were able to easily pinpoint Kim because he was using Tor around the time the bomb threat email was sent through the Tor network. From the criminal complaint:
Harvard University was able to determine that, in the several hours leading up to the receipt of the e-mail messages described above, ELDO KIM accessed TOR using Harvard’s wireless network.
Eldo Kim is just one of many, many examples of people who have bought into the lie that Tor provides blanket online anonymity – and later paid the price.
Had Kim used a bridge or VPN before accessing the Tor network, he probably would have gotten away with it (we’ll discuss this more below).
4. Anybody can operate Tor nodes and collect your data and IP address
Many proponents of Tor argue that its decentralized nature is a benefit. While there are indeed advantages to decentralization, there are also some major risks. Namely, that anybody can operate the Tor nodes through which your traffic is being routed.
There have been numerous examples of people setting up Tor nodes to collect data from gullible Tor users who thought they would be safe and secure.
Take for example Dan Egerstad, a 22-year-old Swedish hacker. Egerstad set up a few Tor nodes around the world and collected vast amounts of private data in just a few months:
In time, Egerstad gained access to 1000 high-value email accounts. He would later post 100 sets of sensitive email logins and passwords on the internet for criminals, spies or just curious teenagers to use to snoop on inter-governmental, NGO and high-value corporate email.
The question on everybody’s lips was: how did he do it? The answer came more than a week later and was somewhat anti-climactic. The 22-year-old Swedish security consultant had merely installed free, open-source software – called Tor – on five computers in data centres around the globe and monitored it. Ironically, Tor is designed to prevent intelligence agencies, corporations and computer hackers from determining the virtual – and physical – location of the people who use it.
People think they’re protected just because they use Tor. Not only do they think it’s encrypted, but they also think ‘no one can find me’.
To not assume government agencies are doing this right now would be extremely naive.
Commenting on this case, security consultant Sam Stover emphasized the risks of someone snooping traffic through Tor nodes:
Domestic, or international . . . if you want to do intelligence gathering, there’s definitely data to be had there. (When using Tor) you have no idea if some guy in China is watching all your traffic, or some guy in Germany, or a guy in Illinois. You don’t know.
In fact, that is exactly how Wikileaks got started. The founders simply setup Tor nodes to siphon off more than a million private documents. According to Wired:
WikiLeaks, the controversial whistleblowing site that exposes secrets of governments and corporations, bootstrapped itself with a cache of documents obtained through an internet eavesdropping operation by one of its activists, according to a new profile of the organization’s founder.
The activist siphoned more than a million documents as they traveled across the internet through Tor, also known as “The Onion Router,” a sophisticated privacy tool that lets users navigate and send documents through the internet anonymously.
Are governments running Tor nodes for bulk data collection?
Egerstad also suggests Tor nodes may be controlled by powerful agencies (governments) with vast resources:
In addition to hackers using Tor to hide their origins, it’s plausible that intelligence services had set up rogue exit nodes to sniff data from the Tor network.
“If you actually look in to where these Tor nodes are hosted and how big they are, some of these nodes cost thousands of dollars each month just to host because they’re using lots of bandwidth, they’re heavy-duty servers and so on,” Egerstad says. “Who would pay for this and be anonymous?“
Back in 2014, government agencies seized a number of different Tor relays in what is known as “Operation Onymous”. From the Tor Project blog:
Over the last few days, we received and read reports saying that several Tor relays were seized by government officials. We do not know why the systems were seized, nor do we know anything about the methods of investigation which were used. Specifically, there are reports that three systems of Torservers.net disappeared and there is another report by an independent relay operator.
Commenting on this case, ARS Technica noted in 2014:
On July 4, the Tor Project identified a group of Tor relays that were actively trying to break the anonymity of users by making changes to the Tor protocol headers associated with their traffic over the network.
The rogue relays were set up on January 30, 2014—just two weeks after Blake Benthall allegedly announced he had taken control of Silk Road 2.0 and shortly after the Homeland Security undercover officer who infiltrated Silk Road 2.0 began getting paid to be a site administrator. The relays not only could have de-anonymized some users, but they also “probably tried to learn who published hidden service descriptors, which would allow the attackers to learn the location of that hidden service,” Tor project leader Roger Dingledine wrote in a July 30 blog post.
This issue continues to gain attention. In this Gizmodo article from 2021, we find the same problems. Bad actors can and do operate Tor nodes.
Additional reading: A mysterious threat actor is running hundreds of malicious Tor relays
No quality control!
The fundamental issue here is there is no real quality control mechanism for vetting Tor relay operators. Not only is there no authentication mechanism for setting up relays, but the operators themselves can also remain anonymous.
Assuming that some Tor nodes are data collection tools, it would also be safe to assume that many different governments are involved in data collection, such as the Chinese, Russian, and US governments.
See also: Tor network exit nodes found to be sniffing passing traffic
5. Malicious Tor nodes do exist
If government-controlled Tor nodes weren’t bad enough, you also have to consider malicious Tor nodes.
In 2016 a group of researchers presented a paper titled “HOnions: Towards Detection and Identification of Misbehaving Tor HSDirs“, which described how they identified 110 malicious Tor relays:
Over the last decade privacy infrastructures such as Tor proved to be very successful and widely used. However, Tor remains a practical system with a variety of limitations and open to abuse. Tor’s security and anonymity is based on the assumption that the large majority of the its relays are honest and do not misbehave. Particularly the privacy of the hidden services is dependent on the honest operation of Hidden Services Directories (HSDirs). In this work we introduce, the concept of honey onions (HOnions), a framework to detect and identify misbehaving and snooping HSDirs. After the deployment of our system and based on our experimental results during the period of 72 days, we detect and identify at least 110 such snooping relays. Furthermore, we reveal that more than half of them were hosted on cloud infrastructure and delayed the use of the learned information to prevent easy traceback.
When conspiracy “theory” becomes conspiracy fact.
The malicious HSDirs identified by the team were mostly located in the United States, Germany, France, United Kingdom and the Netherlands.
Just a few months after the HSDir issue broke, a different researcher identified a malicious Tor node injecting malware into file downloads.
According to ITProPortal:
Authorities are advising all users of the Tor network to check their computers for malware after it emerged that a Russian hacker has been using the network to spread a powerful virus. The malware is spread by a compromised node in the Tor network.
…It has emerged that one of these exit nodes had been modified to alter any program downloaded over the network. This allowed the attacker to put his own executable code in such programs, and potentially take control of victims’ computers.
Due to the altered node, any Windows executable downloaded over the network was wrapped in malware, and worryingly even files downloaded over Windows Update were affected.
Use at your own risk.
See also:
OnionDuke APT Malware Distributed Via Malicious Tor Exit Node
6. No warrant necessary to spy on Tor users
Another interesting case highlighting the flaws of Tor comes form 2016 when the FBI was able to infiltrate Tor to bust another pedophile group.

According to Tech Times:
The U.S. Federal Bureau of Investigation (FBI) can still spy on users who use the Tor browser to remain anonymous on the web.
Senior U.S. District Court Judge Henry Coke Morgan, Jr. has ruled that the FBI does not need a warrant to hack into a U.S. citizen’s computer system. The ruling by the district judge relates to FBI sting called Operation Pacifier, which targeted a child pornography site called PlayPen on the Dark web.
The accused used Tor to access these websites. The federal agency, with the help of hacking tools on computers in Greece, Denmark, Chile and the U.S., was able to catch 1,500 pedophiles during the operation.
While it’s great to see these types of criminals getting shut down, this case also highlights the severe vulnerabilities of Tor as a privacy tool that can be trusted by journalists, political dissidents, whistleblowers, etc.
The judge in this case officially ruled that Tor users lack “a reasonable expectation of privacy” in hiding their IP address and identity. This essentially opens the door to any US government agency being able to spy on Tor users without obtaining a warrant or going through any legal channels.
This, of course, is a serious concern when you consider that journalists, activists, and whistleblowers are encouraged to use Tor to hide from government agencies and mass surveillance.
Now let’s put this all into context by looking at the history of Tor and it’s funding.
7. Tor was created by the US government (and not for your “right to privacy”)
If you think Tor was created for “privacy rights” or some other noble-sounding cause, then you would be mistaken. The quote below, from the co-founder of Tor, speaks volumes.
I forgot to mention earlier, probably something that will make you look at me in a new light. I contract for the United States Government to build anonymity technology for them and deploy it. They don’t think of it as anonymity technology, though we use that term. They think of it as security technology. They need these technologies so that they can research people they’re interested in, so that they can have anonymous tip lines, so that they can buy things from people without other countries figuring out what they are buying, how much they are buying and where it is going, that sort of thing.
— Roger Dingledine, co-founder of Tor, 2004 speech
This quote alone should convince any rational person to never use the Tor network, unless of course you want to be rubbing shoulders with government spooks on the Dark Web.
The history of Tor goes back to the 1990s when the Office of Naval Research and DARPA were working to create an online anonymity network in Washington, DC. This network was called “onion routing” and bounced traffic across different nodes before exiting to the final destination.
In 2002, the Alpha version of Tor was developed and released by Paul Syverson (Office of Naval Research), as well as Roger Dingledine and Nick Mathewson, who were both on contract with DARPA. This three-person team, working for the US government, developed Tor into what it is today.
The quote above was taken from a 2004 speech by Roger Dingledine, which you can also listen to here.
After Tor was developed and released for public use, it was eventually spun off as its own non-profit organization, with guidance coming from the Electronic Frontier Foundation (EFF):
At the very end of 2004, with Tor technology finally ready for deployment, the US Navy cut most of its Tor funding, released it under an open source license and, oddly, the project was handed over to the Electronic Frontier Foundation.
The Electronic Frontier Foundation (EFF) remains one of the biggest promoters of Tor today, which is not surprising given EFF’s deep ties to the project.
8. Tor is funded by the US government
It’s no secret that Tor is funded by various US government agencies.
The key question is whether US government funding negatively affects Tor’s independence and trustworthiness as a privacy tool.
Some journalists have closely examined the financial relationship between Tor and the US government:
Tor had always maintained that it was funded by a “variety of sources” and was not beholden to any one interest group. But I crunched the numbers and found that the exact opposite was true: In any given year, Tor drew between 90 to 100 percent of its budget via contracts and grants coming from three military-intel branches of the federal government: the Pentagon, the State Department and an old school CIA spinoff organization called the BBG.
Put simply: the financial data showed that Tor wasn’t the indie-grassroots anti-state org that it claimed to be. It was a military contractor. It even had its own official military contractor reference number from the government.
Here are some of the different government funding sources for the Tor Project over the years:
Broadcasting Board of Governors:
“Broadcasting Board of Governors (BBG) [now called U.S. Agency for Global Media], a federal agency that was spun off from the CIA and today oversees America’s foreign broadcasting operations, funded Tor to the tune of $6.1 million in the years from 2007 through 2015.” (source)
State Department:
“The State Department funded Tor to the tune of $3.3 million, mostly through its regime change arm — State Dept’s “Democracy, Human Rights and Labor” division.” (source)
The Pentagon:
“From 2011 through 2013, the Pentagon funded Tor to the tune of $2.2 million, through a U.S. Department of Defense / Navy contract — passed through a defense contractor called SRI International.” (source)
The grant is called: “Basic and Applied Research and Development in Areas Relating to the Navy Command, Control, Communications, Computers, Intelligence, Surveillance, and Reconnaissance.”
We can also see what the Tor project has to say about the matter.
When soliciting funds in 2005, Tor claimed that donors would be able to “influence” the direction of the project:
We are now actively looking for new contracts and funding. Sponsors of Tor get personal attention, better support, publicity (if they want it), and get to influence the direction of our research and development!
There you have it. Tor claims donors influence the direction of research and development – a fact that the Tor team even admits.
Do you really think the US government would invest millions of dollars into a tool that stifled its power?
9. When you use Tor, you help the US government do spooky stuff
The United States government can’t simply run an anonymity system for everybody and then use it themselves only. Because then every time a connection came from it people would say, “Oh, it’s another CIA agent looking at my website,” if those are the only people using the network. So you need to have other people using the network so they blend together.
—Roger Dingledine, co-founder of the Tor Network, 2004 speech
The implications of this statement are quite serious.
When you use Tor, you are literally helping the US government. Your traffic helps to conceal CIA agents who are also using Tor, as Dingledine and journalists are pointing out.
Tor is fundamentally a tool for the US government, and it remains so today:
Tor’s original — and current — purpose is to cloak the online identity of government agents and informants while they are in the field: gathering intelligence, setting up sting operations, giving human intelligence assets a way to report back to their handlers — that kind of thing. This information is out there, but it’s not very well known, and it’s certainly not emphasized by those who promote it.
You will never hear Tor promoters discuss how important it is for the US government to get others on the the Tor network. This remains a taboo topic that Tor advocates simply avoid.
The Tor Project’s website also discusses how Tor is actively used by government agencies for different purposes:
A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.
Michael Reed, another early developer of Tor, explained how it has always been a tool for US government military and intelligence operations:
The original *QUESTION* posed that led to the invention of Onion Routing was, “Can we build a system that allows for bi-directional communications over the Internet where the source and destination cannot be determined by a mid-point?” The *PURPOSE* was for DoD / Intelligence usage (open source intelligence gathering, covering of forward deployed assets, whatever). Not helping dissidents in repressive countries. Not assisting criminals in covering their electronic tracks. Not helping bit-torrent users avoid MPAA/RIAA prosecution. Not giving a 10 year old a way to bypass an anti-porn filter. Of course, we knew those would be other unavoidable uses for the technology, but that was immaterial to the problem at hand we were trying to solve (and if those uses were going to give us more cover traffic to better hide what we wanted to use the network for, all the better…I once told a flag officer that much to his chagrin).
Here’s another early Tor developer who spilled the beans. Tor was never meant for “dissidents in repressive countries” or helping various privacy activists fighting for human rights, which is how Tor is promoted today.
Just as Roger Dingledine asserted in the opening quote to this section, Paul Syverson (Tor co-founder) also emphasized the importance of getting other people to use Tor, thereby helping government agents perform their work and not stand out as the only Tor users:
If you have a system that’s only a Navy system, anything popping out of it is obviously from the Navy. You need to have a network that carries traffic for other people as well.
Tor is branded by many different individuals and groups as a grassroots project to protect people from government surveillance. In reality, however, it is a tool for government agents who are literally using it for military and intelligence operations (including spying on those who think they are “anonymous” on Tor).
Tor’s utility for the military-surveillance apparatus is explained well in the following quote:
Tor was created not to protect the public from government surveillance, but rather, to cloak the online identity of intelligence agents as they snooped on areas of interest. But in order to do that, Tor had to be released to the public and used by as diverse a group of people as possible: activists, dissidents, journalists, paranoiacs, kiddie porn scum, criminals and even would-be terrorists — the bigger and weirder the crowd, the easier it would be for agents to mix in and hide in plain sight.
According to these Tor developers and co-founders, when you use Tor you are helping US government agents in doing whatever they do on the Tor network. Why would anyone who advocates for privacy and human rights want to do that?
10. IP address leaks when using Tor
Another recurring problem with Tor is IP address leaks – a serious issue that will de-anonymize Tor users, even if the leak is brief.
In November 2017 a flaw was discovered that exposed the real IP address of Tor users if they clicked on a local file-based address, such as file://., rather than http:// or https://.
This issue illustrates a larger problem with Tor: it only encrypts traffic through the Tor browser, thereby leaving all other (non-Tor browser) traffic exposed.
Unlike a VPN that encrypts all traffic on your operating system, the Tor network only works through a browser configured for Tor. (See the ‘what is a VPN‘ guide for an overview.)
This design leaves Tor users vulnerable to leaks which will expose their identity in many different situations:
- Tor offers no protection when torrenting and will leak the user’s IP address with torrent clients.
- Tor may leak IP addresses when accessing files, such as PDFs or other documents, which will likely bypass proxy settings.
- Windows users are also vulnerable to different types of leaks that will expose the user’s real IP address.
It’s important to note, however, that oftentimes de-anonymization is due to user error or misconfiguration. Therefore blame does not lie with Tor itself, but rather with people not using Tor correctly.
Dan Eggerstad emphasized this issue as well when he stated:
People think they’re protected just because they use Tor. Not only do they think it’s encrypted, but they also think ‘no one can find me’. But if you’ve configured your computer wrong, which probably more than 50 per cent of the people using Tor have, you can still find the person (on) the other side.
Once again, non-technical users would be better off using a good VPN service that provides system-wide traffic encryption and an effective kill switch to block all traffic if the VPN connection drops.
11. Using Tor can make you a target
As we saw above with the bomb threat hoax, Eldo Kim was targeted because he was on the Tor network when the bomb threat was sent.
Other security experts also warn about Tor users being targeted merely for using Tor.
In addition, most really repressive places actually look for Tor and target those people. VPNs are used to watch Netflix and Hulu, but Tor has only one use case – to evade the authorities. There is no cover. (This is assuming it is being used to evade even in a country incapable of breaking Tor anonymity.)
In many ways Tor can be riskier than a VPN:
- VPNs are (typically) not actively malicious
- VPNs provide good cover that Tor simply cannot – “I was using it to watch Hulu videos” is much better than – “I was just trying to buy illegal drugs online”
As we’ve pointed out here before, VPNs are more widely used than Tor – and for various (legitimate) reasons, such as streaming Netflix with a VPN.
So maybe you still need (or want?) to use Tor. How can you do so with more safety?
How hide your IP address when using Tor
Given that Tor is compromised and bad actors can see the real IP address of Tor users, it would be wise to take extra precautions. This includes hiding your real IP address before accessing the Tor network.
To hide your IP address when accessing Tor, simply connect to a VPN server (through a VPN client on your computer) and then access Tor as normal (such as through the Tor browser). This will add a layer of encryption between your computer and the Tor network, with the VPN server’s IP address replacing your real IP address.
Note: There are different ways to combine VPNs and Tor. I am only recommending the following setup: You > VPN > Tor > Internet (also called “Tor over VPN” or “Onion over VPN”).
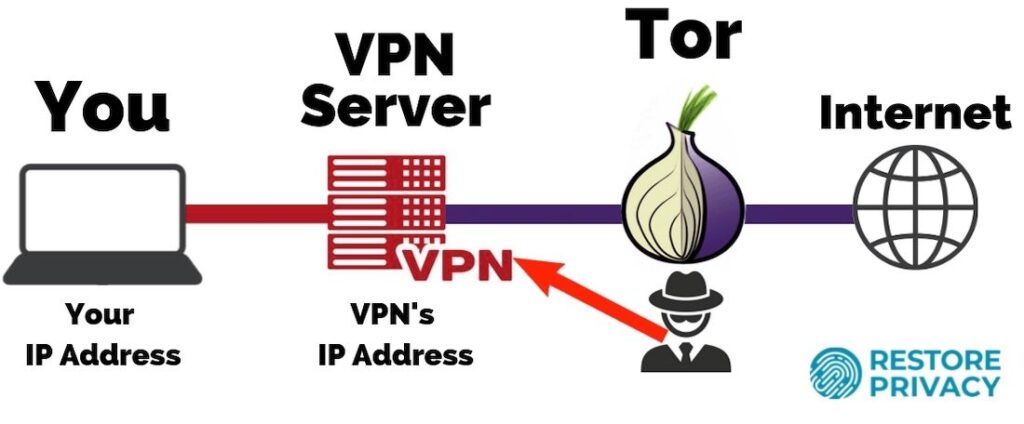
With this setup, even if a malicious actor was running a Tor server and logging all connecting IP addresses, your real IP address would remain hidden behind the VPN server (assuming you are using a good VPN with no leaks).
Here are the benefits of routing your traffic through a secure VPN before the Tor network:
- Your real IP address remains hidden from the Tor network (Tor cannot see who you are)
- Your internet provider (ISP) or network admin will not be able to see you are using Tor (because your traffic is being encrypted through a VPN server).
- You won’t stand out as much from other users because VPNs are more popular than Tor.
- You are distributing trust between Tor and a VPN. The VPN could see your IP address and Tor could see your traffic (sites you visit), but neither would have both your IP address and browsing activities.
For anyone distrustful of VPNs, there are a handful of verified no logs VPN services that have been proven to be truly “no logs”.
You can sign up for a VPN with a secure anonymous email account (not connected to your identity). For the truly paranoid, you can also pay with Bitcoin or any other anonymous payment method. Most VPNs do not require any name for registration, only a valid email address for account credentials. Using a VPN in a safe offshore jurisdiction (outside the 14 Eyes) may also be good, depending on your threat model.
For those seeking the highest levels of anonymity, you can chain multiple VPNs through Linux virtual machines (using Virtualbox, which is FOSS). You could also use VPN1 on your router, VPN2 on your computer, and then access the regular internet (or the Tor network) through two layers of encryption via two separate VPN services. This allows you to distribute trust across different VPN services and ensure neither VPN could have both your incoming IP address and traffic. This is discussed more in my guide on multi-hop VPN services.
Note: The claim that “VPN is fully, 100%, a single point/entity that you must trust” is false. This claim comes from this Tor promoter who coincidently works for the US government’s Naval Research Lab.
When you chain VPNs, you can distribute trust across different VPN services and different jurisdictions around the world, all paid for anonymously and not linked to your identity. With Tor alone, you put all your trust in The Onion Router…
Tor Project agrees on the benefits of adding VPN
The Tor Project also agrees on the benefits of correctly using a VPN with Tor, as I recommend above. Here are a few quotes from the Tor Project about the benefits of using a VPN before Tor (archived):
- “might prevent your ISP etc from seeing that you’re using Tor”
- Routing Tor through a VPN “can be a fine idea assuming your VPN provider’s network is in fact sufficiently safer than your own network.” [A verified no logs VPN is a lot safer than an internet provider that has your name, date of birth, payment details, and is collecting your data and sharing it with surveillance agencies, such as the case with US internet providers.]
- “Another advantage here is that it prevents Tor from seeing who you are behind the VPN. So if somebody does manage to break Tor and learn the IP address your traffic is coming from, … then you’ll be better off.”
While I generally agree with the points above, unfortunately, the Tor Project also stated some incorrect information in the beginning of their article as follows, “Most VPN/SSH provider log, there is a money trail, if you can’t pay really anonymously.”
These points are incorrect.
- “Most VPN/SSH provider log” – This is simply not true. There are many no logs VPN services and also a small number of VPNs that are verified to be no logs, having undergone third-party audits, server seizures, or court subpoenas for user data.
- “there is a money trail” – This is a huge misconception that is promoted by people who don’t know what they’re talking about. A “money trail” has no bearing on the effectiveness or encryption of a VPN. VPNs are not illegal and are becoming mainstream privacy tools. If an adversary knows you have a subscription with a specific VPN service, this has zero bearing on the effectiveness of your VPN. Even if the adversary has your username and password, this still has no bearing on the effectiveness or encryption of the VPN (it just means your adversary can use the VPN for free). VPN encryption is dynamic and negotiated new with each connection. And if you are worried about “money trails” then pay anonymously.
- “can’t pay really anonymously” – This is again false, perhaps blatant lying to scare people away from VPNs. Most VPNs offer anonymous payment options, such as gift cards or Bitcoin, with no name required. You only need a valid email, and you can easily setup an anonymous/burner email for this purpose that’s not connected to your identity. Done.
Note: While there have been various cases proving the FBI can easily de-anonymize Tor users, there has never been any court cases (that I’ve seen) proving the FBI (or any government agency) can de-anonymize VPN users, assuming there’s good encryption with no leaks. Instead, we have seen a few isolated cases where the FBI pressured VPNs to log user data and provide this to authorities to identify a specific user, such as with the IPVanish logging case in the US.
Tor vulnerabilities and VPNs
There are other attacks that the Tor Project admits will de-anonymize Tor users (archived):
As mentioned above, it is possible for an observer who can view both you and either the destination website or your Tor exit node to correlate timings of your traffic as it enters the Tor network and also as it exits. Tor does not defend against such a threat model.
Once again, a VPN can help to mitigate the risk of de-anonymization by hiding your source IP address before accessing the guard node in the Tor circuit.
Can exit nodes eavesdrop on communications? From the Tor Project:
Yes, the guy running the exit node can read the bytes that come in and out there. Tor anonymizes the origin of your traffic, and it makes sure to encrypt everything inside the Tor network, but it does not magically encrypt all traffic throughout the Internet.
However, a VPN can not do anything about a bad Tor exit node eavesdropping on your traffic, although it will help hide who you are (but your traffic can also give you away).
I discuss these points more in my VPN vs Tor comparison.
Conclusion
No privacy tool is above criticism.
Just like with Tor, I have also pointed out numerous problems with VPNs, including VPNs that were caught lying about logs, VPN scams, and dangerous free VPN services. All privacy tools come with pros and cons. Selecting the best tool for the job all boils down to your threat model and unique needs.
Unfortunately, for many in the privacy community, Tor is now considered to be an infallible tool for blanket anonymity, and to question this dogma means you are “spreading FUD”. This is pathetic.
In closing, for regular users seeking more security and online anonymity, I’d simply avoid Tor altogether. A VPN will offer system-wide encryption, much faster speeds, and user-friendly clients for various devices and operating systems. This will also prevent your ISP from seeing what you’re up to online.
Additionally, VPNs are more mainstream and there are many legitimate (and legal!) reasons for using them. Compared to Tor, you definitely won’t stand out as much with a VPN.
For those who still want to access the Tor network, doing so through a reliable VPN service will add an extra layer of protection while hiding your real IP address.
Further Reading:
Tor and its Discontents: Problems with Tor Usage as Panacea
Users Get Routed: Traffic Correlation on Tor by Realistic Adversaries
Tor network exit nodes found to be sniffing passing traffic
On the Effectiveness of Traffic Analysis Against Anonymity Networks Using Flow Records
Judge confirms what many suspected: Feds hired CMU to break Tor

Leave a Reply