
Proton VPN is a VPN service that is based in Switzerland. It is backed by some serious brainpower and brands itself as a secure, premium VPN for users who are serious about protecting their online privacy. It was officially launched in 2017 by the makers of Proton Mail, a secure email provider.
In today’s updated Proton VPN review, I set out to see how this VPN performs relative to other VPN services in terms of privacy, security, and performance.
The answers (and test results) may surprise you. Before we get into the details, here is a table highlighting some key facts about Proton VPN:
| Website | ProtonVPN.com |
| Based in | Switzerland |
| Logs | No logs |
| Price | $4.99/mo. |
| Support | Email + Chat |
| Refund | 30 days |
| Coupon | 50% Off Proton VPN |
Below are some of the questions that I will answer in this Proton VPN review:
- How fast is Proton VPN with servers throughout the network?
- What security and privacy features does Proton VPN offer, and do all features work correctly?
- Does Proton VPN have any problems with IP address leaks or DNS leaks?
- How responsive is the Proton VPN support staff?
- Does Proton VPN unblock Netflix and other streaming services?
- How does Proton VPN compare to other top-rated VPNs and is it worth it?
Overall, Proton VPN has made some good improvements in the last year or so, but it still lags behind other leading VPNs in a few key areas.
Proton VPN overview
Here is a brief overview of my test results and research findings for this review of Proton VPN:
+ Pros
- Useful privacy features (no leaks)
- Secure server network (secure core)
- Good privacy jurisdiction and data protection policies
- WireGuard VPN support (but not on Linux)
- Transparent company with a good track record
– Cons
- Average speeds
- Above-average prices
- Limited support for streaming
Additional research findings:
- Customer support
- Pricing, payment options, and refund policy
- Proton VPN FAQ
Pros of Proton VPN
Here are the Pros that I found for this review.
User-friendly VPN applications
Proton VPN has a nice lineup of apps that are user-friendly and full of features.
The layout and design are great, and I also like the dark-mode theme. Below is the compact view of the Windows VPN app that I tested for this review:
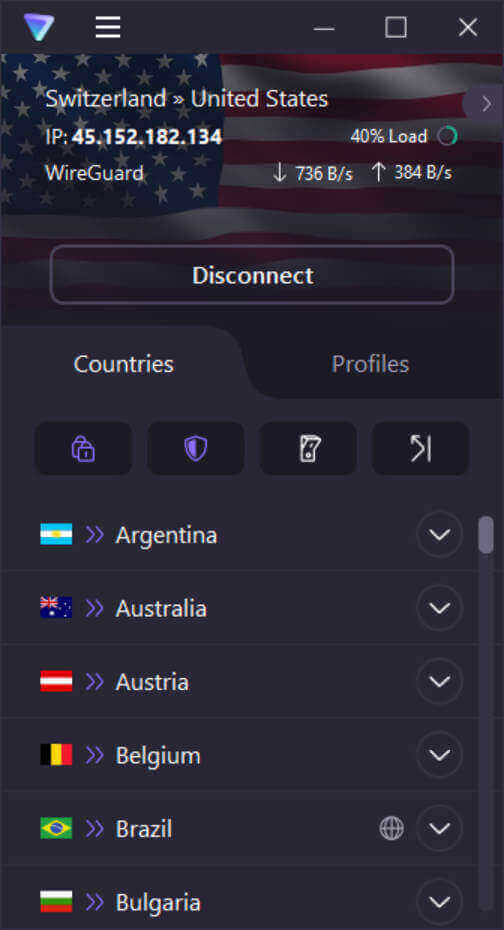
In order to give you quick access to the major features, the designers came up with the tabbed interface you can see here.
- The Countries tab lets you select a country and if desired a specific server in that country. This is also where you can turn on and off the four major features: Secure Core, NetShield, Kill Switch, and Port Forwarding.
- The Profiles tab is where you create, manage, and choose the specific profile you want to use.
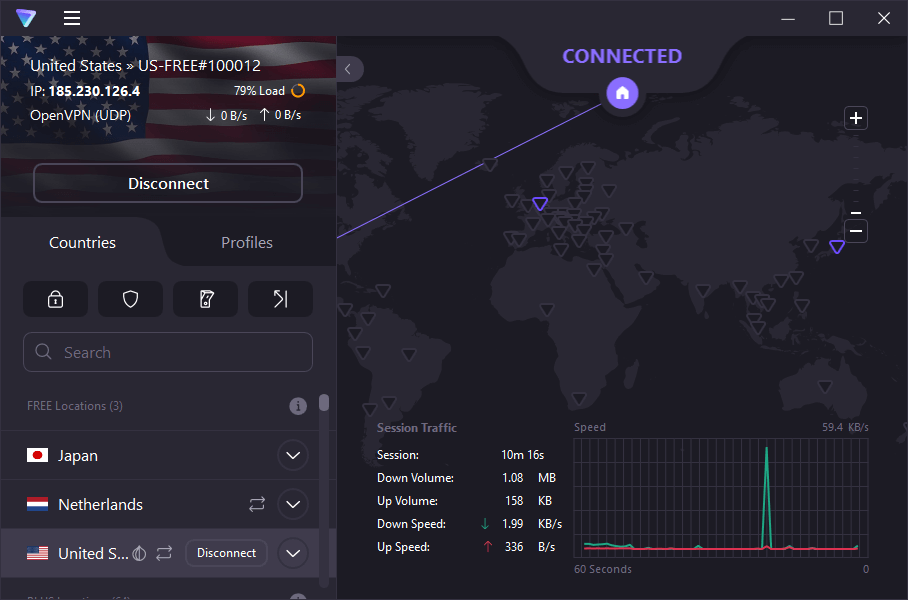
The expanded view of the Proton VPN app gives you access to all the features and controls of the compact view, plus scrolling session statistics and a world map showing your current connection. You can also select one of the triangles on the map, each of which represents a server location. Doing so causes Proton VPN to connect to a server in that location.
Proton VPN offers dedicated clients (apps) for all major devices and operating systems, including Windows, macOS, Linux, iOS, Android, Android TV, and Chromebook. They have recently added browser extensions for Firefox and Chrome.
Note: For macOS, you can use the native IKEv2 protocol or WireGuard with the Proton VPN macOS client. The fastest macOS VPN services we have tested use WireGuard.
The most recent addition to Proton VPN’s operating system support is a set of dedicated apps for major versions of Linux. This is a level of operating system support most VPN services can’t match. Linux support also appeared recently for Surfshark, as described in our Surfshark VPN review.
Below you can see what the Proton VPN Linux apps that we tested for this review looked like. It still lacks some of the features that the Windows app offers (no Port Forwarding or Profiles are shown) but it worked well for me during my testing.
Note: If you are primarily a Linux user, you might want to check out our review of the best VPNs for Linux for other options.
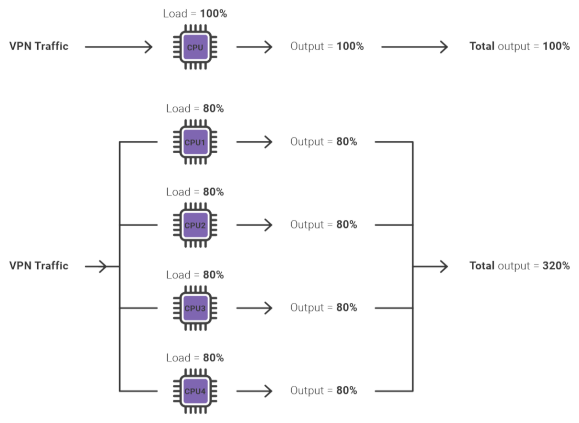
Proton VPN also offers a “VPN Accelerator” feature, which should improve speeds under some circumstances.
VPN Accelerator tries to improve speed through techniques like rewriting the code of various protocols to support multi-threading and using special TCP algorithms designed to recover faster from packet loss.
In general, connections were pretty quick to establish and there weren’t any major issues. While Proton VPN is not the best VPN for PC, the desktop clients still worked well in our tests.
Useful privacy and security features
Proton VPN has several useful features that can boost your security and privacy. Here’s a partial list:
- 3-state kill switch
- Protection against DNS leaks
- Split tunneling
- Custom and predefined profiles
- NetShield to block ads and malware
- Port forwarding
- Tor over VPN
- Worldwide streaming
- P2P/BitTorrent
3-state kill switch
A typical VPN kill switch can be either on or off. When on, it protects your privacy by blocking your traffic if the internet connection fails. This prevents your IP address from being exposed. But a typical kill switch only protects you when you are using the VPN.
Proton VPN has taken things one step further with a 3-state kill switch. Whereas the typical kill switch has two states (on or off), they added a third state: Permanent Kill Switch. The Permanent Kill Switch protects you even when you are not using the VPN. In other words, if you turn on the Permanent Kill Switch, your device can only connect to the internet through the VPN, even if the VPN is turned off.
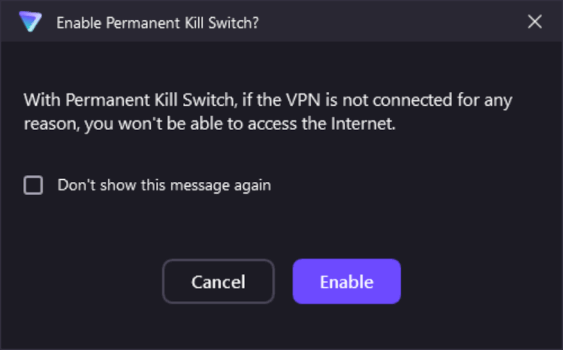
The Proton VPN kill switch worked properly during our testing.
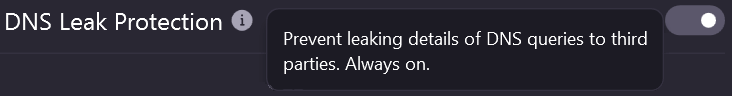
Protection against DNS leaks
You and I know this website by the human-readable name RestorePrivacy.com. But the computers on the internet identify it by a 32-bit IP address. To convert from the name we use to the IP address the computers use, your web browser makes a query to a DNS service that does the translation for it.
Entities that want to spy on your online activities (including your Internet Service Provider, or ISP) can try to read your DNS queries to learn what sites you visit. The top VPNs encrypt your browser’s DNS queries and sent them to a private DNS system that snoops can’t get access to. We include a DNS leak test in our testing regime to make sure that your DNS queries are not exposed when using a VPN.
Proton VPN passed this test with no problems. Note that Proton VPN’s DNS leak protection is always active, the switch on the Advanced Settings tab assigned to it is permanently set to On.
Split tunneling
The Windows and Android apps also offer a Split Tunneling VPN feature, just like we saw in the ExpressVPN review. This allows you to route traffic for certain applications outside of the VPN tunnel. Split tunneling is popular with gamers who want the minimum latency and greatest speed of their internet connection.
Split tunneling can also make connecting to bank websites easier. Banks have their own security that may block VPNs, forcing you to disconnect the VPN to visit the bank. Split tunneling lets you avoid this. But using the Split Tunneling feature forces you to make a choice.
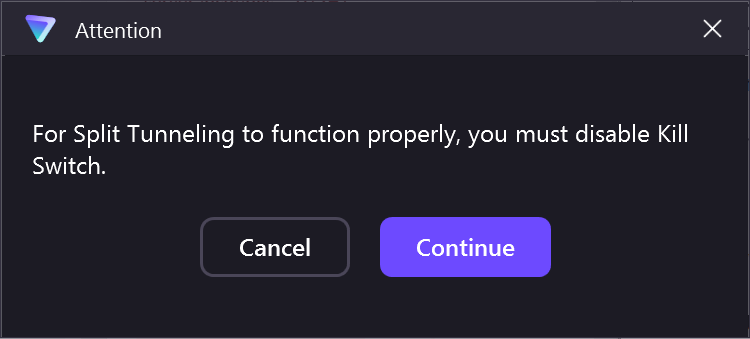
As the Attention message above shows, you need to disable the Kill Switch to use the Split Tunneling feature. This is really inconvenient. As we already mentioned, split tunneling is very useful in certain situations.
But if you disable the kill switch you are risking your privacy. You really want to be able to have both active at the same time. That you can’t is a fairly big mark against Proton VPN.
Custom and predefined profiles
The Quick Connect button lets you get up and running with Proton VPN protection with a single click. The Proton VPN app then selects the best country, protocol, and type of server for you.
You can also manually select the specific options you want, then connect. But if you always end up manually choosing one or a few sets of options, you’ll like what the Proton engineers cooked up for you.
Their VPN connection profiles let you store the exact settings you need as a named profile, saving you the hassles of repeatedly entering them manually. They also have a few predefined profiles that you might find interesting.
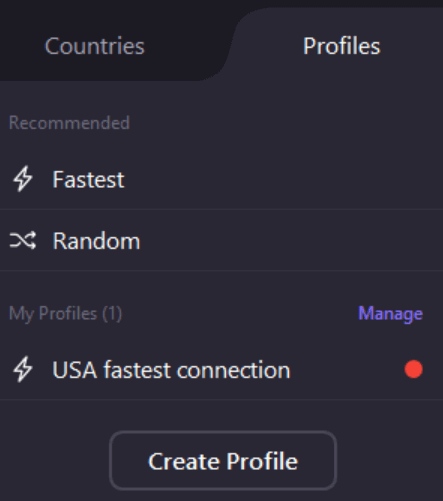
During our testing of the Proton VPN’s Free plan, we could see the full range of profile options. But many of them were disabled in that version and only active when we were working with the Proton VPN Plus plan.
NetShield to block ads and malware
When you turn on NetShield, it automatically blocks advertisements and malicious software from reaching your computer or mobile device. This is basically a VPN ad-blocking feature that uses DNS filtering to prevent data downloads from websites known to host ads and malware.
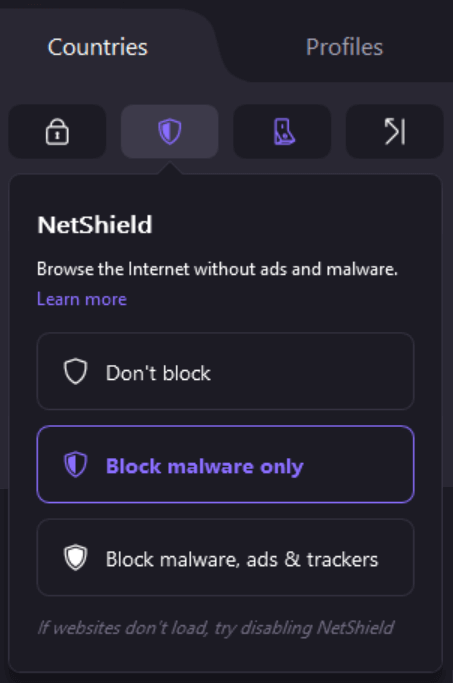
NetShield works very much like the ad-blocking features we tested out in both Surfshark and NordVPN.
Port forwarding
Proton VPN includes a firewall that blocks all ports except those used by the VPN. Port forwarding routes the traffic you specify through the firewall, supporting uses like P2P file transfers (Bit Torrent) and online gaming.
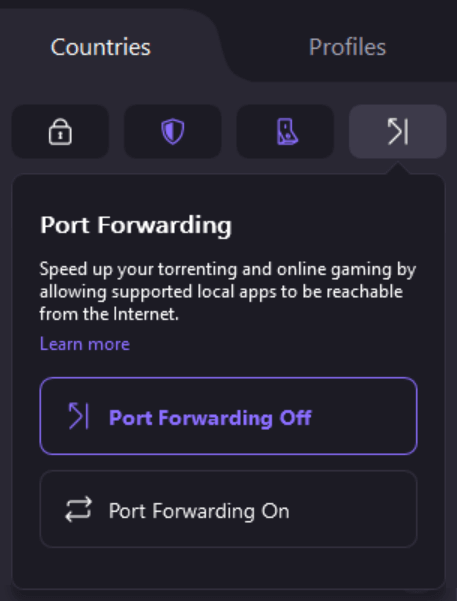
It is easy to enable Port Forwarding from the Countries tab of the main Proton VPN window. You may want to refer to the Proton VPN support center to find specific instructions for forwarding popular apps.
Tor over VPN
The Tor network (Onion network) anonymizes your message traffic by passing it through a chain of three Tor servers. Normally you need to use the Tor browser to access the Tor network, but Proton VPN lets you do so directly. This is not only more convenient; it also gives you the security and privacy of Proton VPN along with Tor anonymity.
Not every country where the Proton VPN has servers also has Tor over VPN servers. The countries that do have Tor over VPN server locations are indicated by an icon that looks like an onion after their name. The Proton VPN servers in that country that do support Tor over VPN are indicated by the word TOR after their name.
There are a couple of other interesting features that you will see repeatedly when working with server lists. Proton VPN tells you how many of each type of server you have access to, and provides an information icon to the right of the type that tells you more about those particular servers.
To the left of each server’s name is an icon that shows how heavily loaded that server is. Try to avoid servers that have red in their ring. Finally, if you hover the cursor over a server name, the Connect button for that server will appear.
Worldwide streaming
Many streaming media sites use geo-blocking software to control who has access to their content. Proton VPN’s Worldwide Streaming can sometimes unblock these locations so you can view their content regardless of your geographic location.
To use Worldwide streaming, you need to find a country that has servers that can unblock the content you want to see. Country names have the icon of a globe next to them if they have Worldwide Streaming servers. Click the information icon for that country to learn about the special servers (including the streaming servers) in this country.
In the image below you can see that South Korea has dedicated servers that can unblock BBC iPlayer and Netflix. At least from this perspective, Proton VPN has potential as a VPN for Netflix.
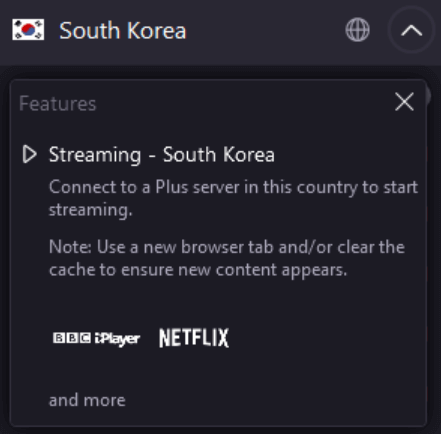
There is a good bit more to understand if you want to use Proton VPN for streaming content from around the world. Get the info you need on this streaming information page.
P2P/BitTorrent
If you download content from P2P services like BitTorrent, you really do need to use the best VPN for torrenting. You really don’t want to get into a copyright problem with a multi-billion dollar company!
Proton VPN supports P2P downloads and torrenting, as long as you use one of their P2P-capable servers to do so. To make the connection, find the name of a country that is physically close to your current location and also has the P2P icon next to it (circled in red in the screen capture below).
Look for an individual server in that country that has that same icon next to its name. Hover the cursor over the icon to see that it is indeed a P2P server. Then click the Connect button which appears.
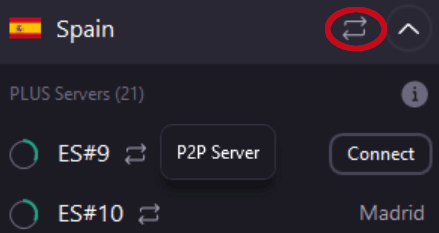
Note: Be aware that you do not have access to P2P servers when you are using the Proton VPN Free plan.
Access to the Secure Core servers
Secure Core is one of the main privacy features you get access to with a Proton VPN Plus subscription. Seeing as it is a feature of the server network, we’ll talk about it when we get to the server section of the review.
Proton VPN encryption and protocols
The Proton VPN Windows client that I tested out for this review supports OpenVPN and WireGuard. The macOS and iOS apps support the IKEv2 and WireGuard protocols. The Proton VPN Android app and the Linux app both support OpenVPN and WireGuard.
Leak test results: all clear
I ran the Windows and Mac OS apps through some basic VPN tests to identify potential leaks or flaws. Everything checked out — no leaks were detected:
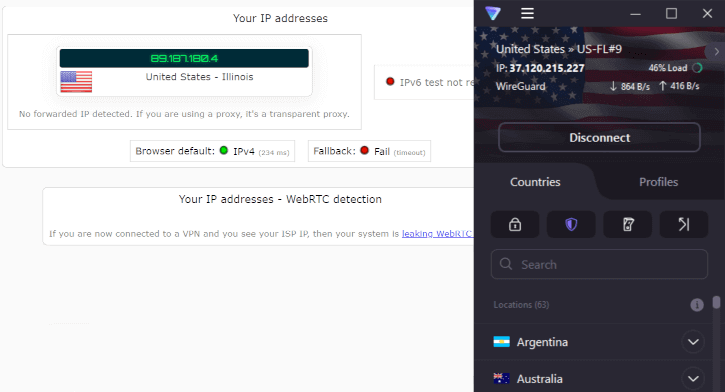
The Proton VPN applications did not have any leaks in our tests for this review.
The screenshot above is with the Proton VPN Windows client. The macOS client also did not have any leaks that I could find.
Proton VPN Settings
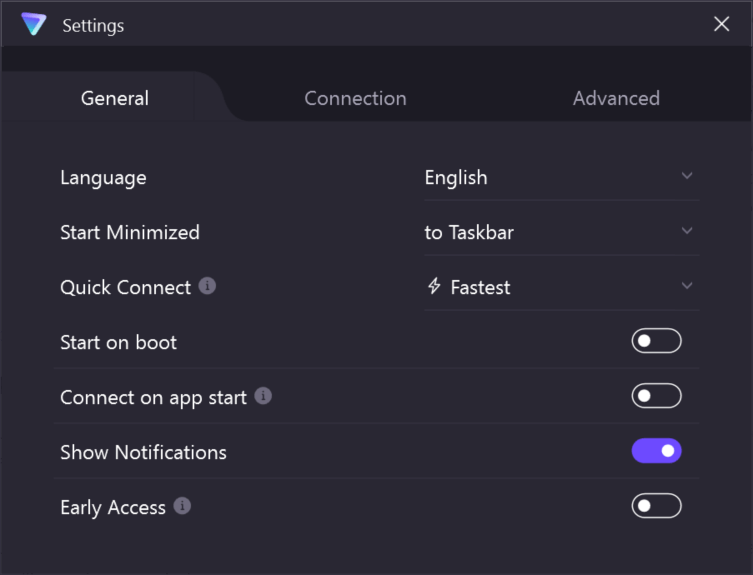
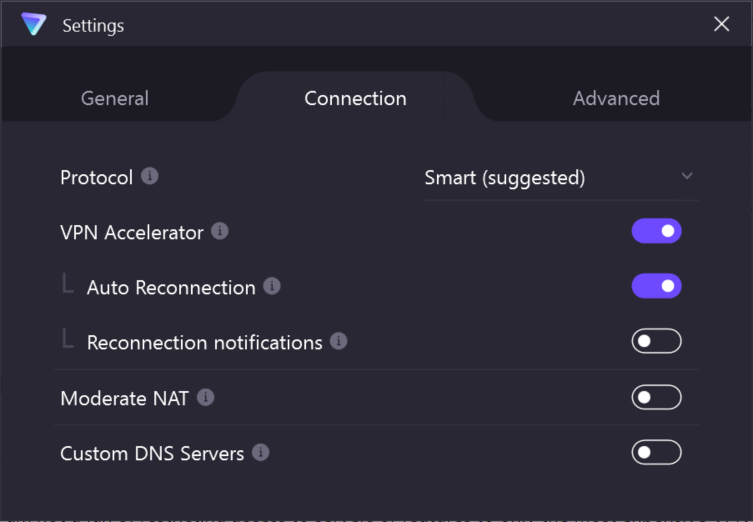
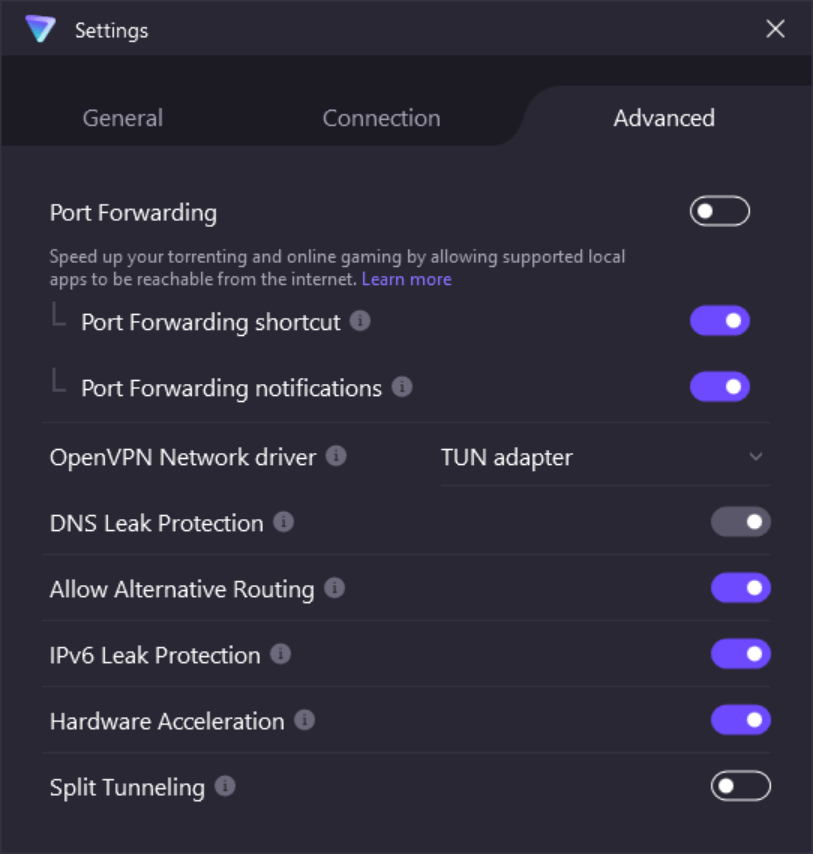
The controls for the features we just discussed (and several others) are managed through the Settings window. This is a very short overview of what controls are to be found on one of the three tabbed pages.
The General Settings tab has some useful but less common options like selecting the language that the app will use, and Quick Connect, a control that lets you choose the profile you want the VPN to use when you hit the Quick Connect button.
The Connection Settings tab lets you control things like the protocol that will be used, triggers for the VPN to start running or not, as well as whether or not the VPN Accelerator will be used.
The Advanced Settings tab lets you control things like split tunneling, port forwarding, leak protection, and some more esoteric settings as well.
Everything we tested across the various tabs worked well.
WireGuard VPN protocol support
The addition of WireGuard VPN protocol support to Proton VPN was a big positive step. WireGuard is best known for its performance. In our experience, all the fastest VPNs now rely on WireGuard. But speed is not the only advantage of this protocol.
Aside from raw speed, WireGuard offers several other benefits including:
- A small, open-source codebase that is easy to validate
- It is extremely secure
- The algorithms it uses run well on modern CPUs
- It connects and reconnects fast, allowing you to roam without losing the internet connection
As of right now, it seems clear that the future of VPNs will be built around WireGuard.
Secure server network (Secure Core)
Proton VPN runs its entire network on dedicated bare-metal servers. This is similar to Perfect Privacy and OVPN in Sweden.
Currently, Proton VPN has over 3,800 servers in 85 different countries. While ProtonVPN has fewer servers than NordVPN, the geographic diversity is very similar, as you can see in the NordVPN review.
One unique aspect of Proton VPN is its implementation of Secure Core.
What is Secure Core?
The Secure Core (SC) feature is basically just a double-VPN server configuration routed through Proton VPN servers in Switzerland, Sweden, or Iceland. In other words, your traffic will first get routed through one of the SC servers before going to the second VPN server and exiting the encrypted tunnel.
You activate SC on the main VPN window’s Countries tab. Click the lock icon (circled in red below) to open the
The main advantage of this approach is that it provides an additional layer of protection. This protects against a compromised server in a third-party data center, for example. Proton VPN has gone to great lengths to ensure the security of these “core” servers:
We have also gone to extraordinary lengths to defend our Secure Core servers. First, servers are located in countries selected specifically for their strong privacy laws (Iceland, Switzerland, and Sweden). We also placed our Secure Core servers in high-security data centers to ensure strong physical security. ProtonVPN infrastructure in Switzerland and Sweden is housed in underground data centers, while our Iceland servers are on a former military base. Furthermore, Secure Core servers are wholly owned and provisioned by us(shipped on-site directly from our offices). Finally, Secure Core servers are connected to the Internet using our own dedicated network with IP addresses that are owned and operated by our own Local Internet Registry (LIR).
In addition to Proton VPN, there are also other VPN providers that offer multi-hop VPN configurations.
Restricted access to SC servers
Unfortunately, Proton VPN restricts access to these double-VPN server connections. This is done by blocking access and forcing you to upgrade your account to the “Plus” ($4.99 per month) plan.
I am not a fan of restricting access to servers or features to only the paid VPN plans. Unfortunately, this is a recurring problem with Proton VPN that also affects other VPN features, as we’ll examine more below.
Another concern I have with these secure servers is that they were sometimes overloaded during our testing. At one point, the SC servers in Switzerland, Iceland, and Sweden were all loaded at close to 100%. In our most recent tests, these servers have been loaded at around 30%, as shown below.
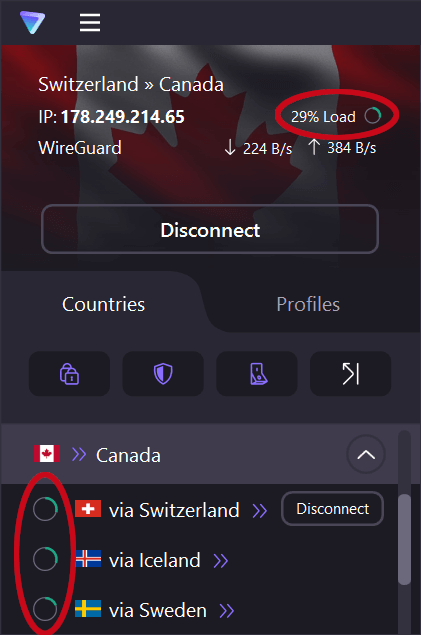
Assuming Proton VPN can keep the loading on these servers around these more recent levels, it should have no impact on their performance. But if they do get overloaded again, it will likely affect the speed of your connection through them.
Are Secure Core (SC) servers slow?
The SC servers I tested for this review were not very fast. However, this is not surprising since traffic is getting routed and encrypted over two locations. This adds more latency and will be slower than a single-hop connection.
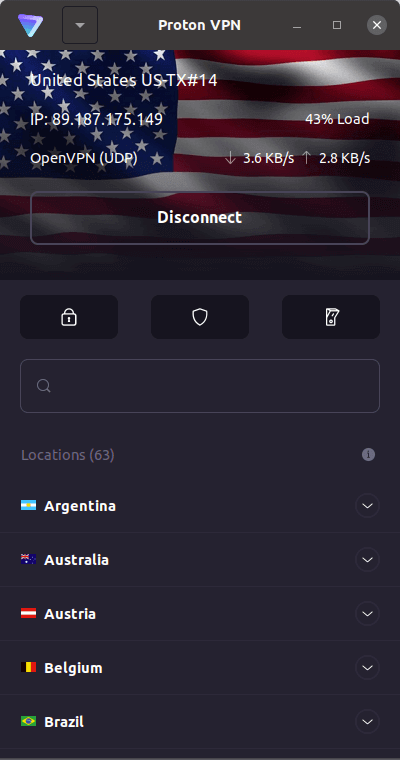
Here is one Secure Core server connection from Switzerland to the US using the WireGuard protocol:
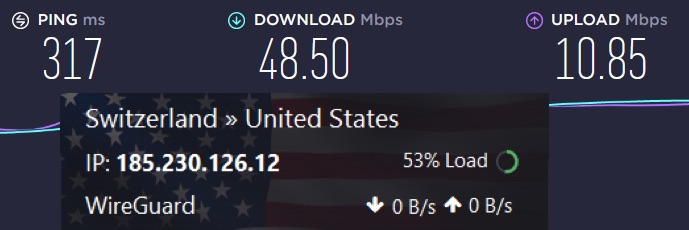
Proton VPN’s secure core is slower than other servers. You can see the ping (latency) is somewhat high. This would not be the best VPN for gaming, where low ping is important. Gamers should instead use single-hop servers close to their location.
If you want the fastest VPN speeds with double-VPN servers, then I would recommend NordVPN. Below you can see I’m getting about 214 Mbps with a double-VPN server from NordVPN: USA > Canada.
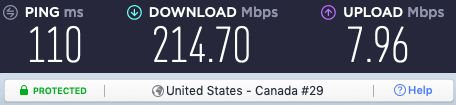
You can find double-VPN servers with a few other VPNs, as we discuss in the Proton VPN vs Surfshark comparison.
Good privacy jurisdiction and data protection policies
Proton VPN is based in Switzerland under the company Proton VPN AG. Switzerland is a good privacy jurisdiction and is not part of the five eyes, nine eyes, or 14 eyes surveillance alliances. As noted on the Proton VPN website:
We are headquartered in Switzerland which has some of the world’s strongest privacy laws. Switzerland is also outside of EU and US jurisdiction and is not a member of the fourteen eyes surveillance network.
From a business standpoint, Proton VPN is a separate entity from Proton Mail. However, it still falls under the same parent organization, Proton Technologies AG, based in Geneva, Switzerland. As we’ve covered before, Switzerland is a great jurisdiction for both VPN services and secure email providers.
There are many USA VPN providers that claim jurisdiction does not matter. However, we’ve seen cases where VPNs have logged user data for various state agencies, such as the case with IPVanish.
There have also been US VPN providers caught embedding trackers in their apps, or sharing data with advertisers, such as the case with Hotspot Shield VPN. We also see this with many free VPN apps of Chinese origin.
Proton VPN logs policy
Proton VPN describes itself as a no-logs VPN provider. The one thing they store is timestamps, as explained on their support page:
Proton VPN respects its users’ privacy and enforces a no-logs policy. This means your VPN connections remain private and we do not store information about your connections or the websites you visit.
For the purpose of securing your account and making sure it’s you who is signing in, we store a single timestamp of your accounts most recent login. Again, we do not store any information about where you signed in from or how long you were logged in.
The Proton VPN privacy policy offers further clarification on the timestamp issue:
Each time a user connects to the Service, we only monitor the timestamp of the last successful login attempt. This gets overwritten each time you successfully log in. This timestamp does not contain any identifying information, such as your IP address or your location; it only contains the time and date of the login.
We retain this limited information to protect user accounts from password brute force attacks. This is necessary to identify password guessing attempts targeting specific user accounts and to take action to protect those accounts.
This is definitely not concerning given that it’s a single timestamp. Proton VPN also explains in this blog post how they are fully compliant with GDPR privacy protections and do not share data with third parties.
Further increasing our confidence in Proton VPN’s no-logs policy is the fact that they have had the no-logs status of their apps and their infrastructure independently audited by Securitum. According to the auditors, Proton VPN does not keep metadata logs, log your VPN activity, and does not engage in any practices that might compromise your privacy.
If you are still not comfortable with the situation, you should check out these verified no-logs VPN providers.
Transparent company with a good track record
It’s no secret that Proton AG, including Proton VPN and Proton Mail, has a good reputation in the privacy community. It is also a company that is transparent and led by reputable, public-facing people.
Proton Mail was started in 2014 by a group of academics/scientists who were working at CERN in Switzerland and also MIT. On the topic of transparency, Proton Mail published an interesting blog post about the organization and leadership.
As noted above, Proton VPN and Proton Mail both fall under the parent company Proton AG, based in Geneva, Switzerland. The Proton VPN arm of this business is officially registered as Proton VPN AG, which shares the same core leadership as Proton Mail.
The Proton Mail IP logging case
Above we noted now Proton VPN and Proton Mail fall under the same parent company, which operates in Switzerland. This is important to consider since Proton Mail was in the spotlight last year with an IP logging controversy. You can get all the details in our article on the Proton Mail logging case, but here’s a brief synopsis:
- The French government requested that Proton Mail engage in targeted IP address logging of a specific user in France. The request was made in a Switzerland court.
- Proton Mail complied with the court order, logged the user, and provided the IP logs to French police.
- French police then arrested the Proton Mail user.
- Proton Mail then edited “we do not keep any IP logs” from its website… after the IP logging incident.
- Based on 2020 Proton Mail transparency reports, there were thousands of data requests that year alone that Proton Mail complied with. When updating this review, we noticed that Proton AG no longer appears to publish transparency reports, and the old ones are no longer online.
Proton Mail, and any other service, must comply with the laws of the jurisdiction in which it operates. Additionally, we can see that the number of requests for user data continues to drastically increase every year.
Interestingly, we found that Proton VPN does not keep any transparency reports, and also has a different “no logs” policy than Proton Mail. This is important to keep in mind as the two services are very different in regard to data stored by Proton Technologies.
So, can you trust Proton VPN with securing your internet traffic? Only you can decide on that answer.
Cons of Proton VPN
Now we’ll take a look at some of the cons of Proton VPN:
Inconsistent speeds
While Proton VPN has generally improved with speeds since the last review, it’s also not the fastest VPN we have tested. To measure speeds, I tested out various Proton VPN servers around the US and Europe on a 500 Mbps internet connection from my location in the US. We used the WireGuard VPN protocol with the “VPN Accelerator” feature activated.
For the first round of Proton VPN speed tests in the United States, I went with west coast servers.
Here are the results for a Proton VPN server in Los Angeles: 90 Mbps

This is not a great start to the testing. We should definitely be above 100 Mbps at least when using WireGuard with nearby servers.
Next, I tested a Proton VPN server in Seattle. The speeds were a bit faster at around 122 Mbps.
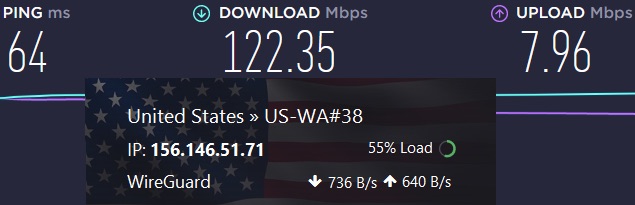
You can see we are still way below the baseline speed, but still better than with the first Proton VPN speed test.
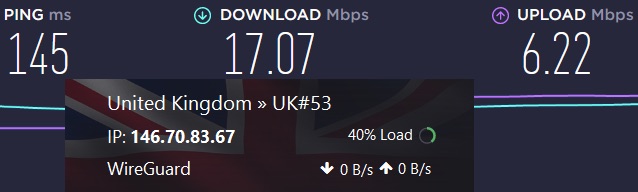
Next up was a server in New York. This one gave us speeds of around 158 Mbps. This was the best speed test I found for this review.
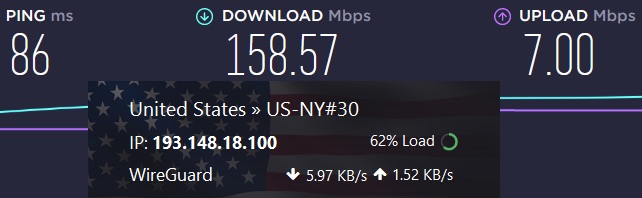
Lastly, I tested a Proton VPN server in the UK. This was the slowest Proton VPN server I found at 17 Mbps. Notice also the server is only at 40% load, so it should theoretically be much faster.
Overall, I would rate Proton VPN’s speed as inconsistent. Some servers were OK, but other servers were average to poor with performance. There are definitely some faster VPNs on the market if you have a need for speed.
Take for example NordVPN, which also supports the WireGuard protocol. With NordVPN, I was able to hit 445 Mbps when testing out the NordVPN server in Seattle:
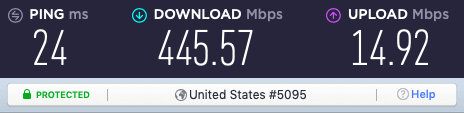
Recall with Proton VPN, the Seattle server with WireGuard was only 122 Mbps.
Learn more about NordVPN here >>
Note: The slow speeds are one reason that Proton VPN did not come out on top in the ProtonVPN vs NordVPN comparison.
Restrictions on servers and features
Proton VPN has simplified its pricing structure since we last reviewed the service. For new users, there are only three pricing plans available: Proton VPN Free, Proton VPN Plus, and Proton Unlimited.
We’ll get into the details of the pricing for Proton VPN plans later. Right now I want to point out that there are major differences between the Free and Plus plan when it comes to servers and features.
You can use the Free plan as long as you like. But it imposes severe limits on what you can do and the resources you have access to. For example, here are some of the things Proton VPN paid plans give you:
- Full-speed access to 3,800+ servers in 85 countries
- 10 simultaneous VPN connections
- Streaming, torrenting, Tor over VPN servers
- Access to Secure Core servers
- NetShield malware and ad blocker
But with the Proton VPN free plan, you get:
- Reduced-speed access to 100+ servers in 3 countries
- 1 VPN connection
- No streaming, torrenting, or Tor over VPN servers
- No access to Secure Core servers
- No NetShield malware and ad blocker
It may be that the Free plan is all you need. But keep in mind the functional differences between the two plans when we get around to talking about prices.
Additional research findings
Below are additional findings from my research of Proton VPN for this review.
Customer Support
Proton VPN’s website has various FAQ articles and guides, which can help you resolve most standard questions without contacting the Customer Support team.
This is good because the only way to contact that team is by email. I used the contact form on their website to submit various inquiries to test out support’s response time.
Overall I was happy with the prompt replies. My inquiries were usually answered on the same day they were submitted. With previous reviews of Proton VPN, I was critical of their support due to delayed response times (several days). Support with Proton VPN has definitely improved over the past few years.
However, most of the large VPN service providers offer live chat support. If this is important to you, consider looking elsewhere. See our ExpressVPN vs Proton VPN comparison, which discusses the support topic in more detail.
Pricing, payment options, and refunds
If you intend to upgrade from the free plan, you will find that Proton VPN is not a cheap VPN. But it isn’t the most expensive VPN on the market, and the prices are much more reasonable than in the past.
Proton VPN Plus gives you full VPN functionality, along with the free features of Proton Mail, Calendar, and Drive.
A monthly subscription to this plan runs $9.99/mo.
A 12-month subscription to this plan runs $5.99/mo.
A 24-month subscription to this plan runs $4.99/mo.
There is also a higher-priced plan called Proton Unlimited. It gives you the full VPN functionality, along with the full functionality of Proton Mail, Proton Calendar, and Proton Drive.
Unfortunately, pricing is generally not a strength with Proton products, but it has gotten better over the years.
To get started with Proton VPN, you can create a free or paid account. If you opt for a paid account, you’ll have the option to pay with PayPal or a credit card. However, if you are upgrading your account, you’ll have the option to pay with:
- Credit cards
- PayPal
- Bitcoin
- Cash
Bitcoin and cash can offer more privacy, but you can also pay with a virtual credit card (such as from privacy.com) using an anonymous name and address.
Does Proton VPN ever offer any discounts, deals, or VPN coupons? The answer is yes. We have seen them offer specials around Black Friday and Cyber Monday every year. To get the details, see these Black Friday / Cyber Monday VPN Deals.
Proton VPN refund policy
Proton VPN offers a pretty good refund policy. As they explain on their Terms and Conditions page,
To request a refund, please contact us using our support form. For the sake of clarity, the cancellation and the request for refund must both be addressed within the 30-day period. Payments made by cash or bank transfers are not refundable. Refunds can only be requested once per user.
This is still generous in comparison to other free VPNs, such as Windscribe and TunnelBear, which both have more restrictive refund policies.
Proton VPN FAQ
Here are the most frequently asked questions related to Proton VPN.
Does Proton VPN work for torrenting?
Many people are looking for the best VPN for torrenting due to the risks associated with copyright infringement.
Generally speaking, Proton VPN is a good VPN for torrenting, but with one catch. Torrenting is blocked on all free plans. This is understandable since they don’t want bandwidth being eaten up by torrents.
With paid plans, torrenting is allowed without restrictions.
Is Proton VPN good for Netflix?
Proton VPN currently works with Netflix. Right now, according to Proton VPN’s website, it works with ten Netflix regional libraries — but there’s another catch! These streaming servers are blocked unless you have a “Plus or Unlimited” subscription.
If you want even more access, you could consider another VPN service that specializes in streaming. For example, both NordVPN and ExpressVPN offer access to 15+ Netflix regions.
I tested US Netflix with a Proton VPN server in New York and did not have any problems getting through. The speeds were adequate for the short tests that I ran.
To see other VPN services that unblock Netflix regions around the world, check out the best VPN for Netflix guide.
What about other streaming services?
Proton VPN does offer support for a few other streaming services, in addition to Netflix, but it’s still pretty limited compared to our other top contenders. However, we do see that Proton VPN is a decent VPN for Firestick, with a dedicated app in the Amazon store.
Does Proton VPN work in China?
Unfortunately, it does not look like Proton VPN is working in China, according to the latest support update:
“As of Sept. 18, 2019, the Chinese government is blocking access to Proton VPN as part of a larger crackdown on Internet freedom.”
The Chinese government works hard to control its citizens’ access to the Internet. The Great Firewall employs a vast system of technical tools, including DNS filtering, URL filtering, and deep packet inspection, that the Chinese government uses to prevent people in China from accessing foreign websites. The government also uses these tools to detect and block VPN servers.”
You can see these best VPNs for China here.
Does Proton VPN work well for gaming?
Gamers have unique needs for a VPN. Important factors include a large server network, fast speeds, and servers that do not get blocked. In these areas, we find Proton VPN does not do well. For example:
* It has a smaller server network than other leading competitors
* Speeds with Proton VPN are mediocre even with their VPN Accelerator technology
* It still gets blocked by most streaming services
Overall, Proton VPN is not the best VPN for gaming. Consider some alternatives.
Proton VPN review conclusion
Proton VPN is not the best VPN we have tested, but it is certainly one of the better services. They have made nice improvements in the last couple of years and this VPN is worth considering.
On the other hand, Proton VPN has some significant drawbacks. For one, server speeds can be hit or miss, depending on your geographic area, servers selected, and other factors. In addition, Proton VPN remains relatively expensive, even after the significant price cuts the company has made.
Nonetheless, Proton VPN remains a solid choice, with excellent security from a very reputable company. So if you think it’s up your alley, it doesn’t hurt to give it a test drive. And if you are still on the fence, then check out the alternatives to Proton VPN below.
Alternatives to Proton VPN
Click the VPN name below to read our full review – or grab the discount for the best savings. All of these VPNs have a 30-day money-back guarantee.
You can also check out our best VPNs list here for other recommendations.
If you have used Proton VPN, please share your honest review (good or bad) below.
This Proton VPN review was last updated on March 18, 2024.

I’ve been using Proton VPN for over a year now, and I have *zero* complaints. I’m not a major bandwidth user, so Proton VPN is a very good fit for me. If you’re a real time gamer, it might not be *your* best choice. But I absolutely love it!
From 4rth March 2024, free plan got more restrictions.
1) no split tunneling.
2) no choice between free country (though number of free country increased).
3) no custom profile setting.
4) no access for VPN accelerator.
I’ve been griping to Proton since 2021 about not being able to use the permanent kill switch and split tunneling at the same time. No movement whatsoever on their side. Others (NordVPN, Mullvad, etc.) do this. So it’s entirely possible using the WFP (Windows Filtering Platform).
@Sven – maybe they’ll take notice of you highlighting this huge gap. They certainly didn’t listen to me. Here’s hoping…
The recent update to the my basic paid Proton service provided new architecture interface with new restrictions that greatly limit my ability to change the few countries and servers previously allowed, with a bold reminder each time I try, “your inability to choose the country you prefer, will now require a new $ upgrade. what a slap and snub. I’m shopping around for a more friendly VPN
For anyone following these things: ProtonAG is partnered with the WEF, and has recently won an award from them.
https://www.startupticker.ch/en/news/embion-and-proton-awarded-as-technology-pioneer-by-world-economic-forum
https://www.weforum.org/organizations/proton
Of course Proton is an easy favorite for a group of unelected financial elites in their quest to establish “trust”. I don’t trust these folks at all.
The last few weeks I am constantly getting DNS errors when trying to load webpages. It’s not limited to any particular browser and the problem is not there when I disconnect from my VPN. The only way to resolve it is to click on a new server and thus refresh the connection. It’s a pain in the butt and I’m going to have to change my VPN provider.
Just downloaded and tried to use this VPN. It took absolutely ages and nothing happened. Forget it. I’ll stick with Express or find another. Failed at the first hurdle.
Thanks for the review. There is a bit of inaccuracy in the article though, when it comes to the 3-state kill switch.
The article said : “Whereas the typical kill switch has two states (on or off), they added a third state: Permanent Kill Switch.”
Be careful. There is NO PERMANENT KILL SWITCH on the Mac.
So this means that when your waking the computer from sleep or reconnecting to a different server or connecting to proton upon startup, there is LEAKAGE of your IP.
I’d sent this serious issue to proton and they said : they know about it but have no plans to fix it.
Thanks again.
Been using ProtonVPN for 2 years and sick of it. Constantly disconnects. Slow sometimes. Software on Debian is buggy. Not happy with it and wish I went with someone else.
Today I had to get another cell phone (3rd phone in three weeks) and when I was setting up this phone and installed the proton VPN app and went to sign in with the exact same email account and password as I’ve used for about a year and a half now, I get a message of “account or email is unverified”or something similar. Even going to the main website and trying to sign in there I get similar messages. So I try to do a new account using the same email account and get a message “email account unverified” again. So what the hell is going on here?? Tried getting help from their support but get messages that support is for signed up members only. WTF?!! Well they are going to have a lot less members if you can’t even get information about why you can’t even sign in much less sign up for an account Free or paid. And I’ve been trying to get answers thru proton VPN service and on reddit and on countless other sites now going on over 5 hrs. And yet have any solution to this matter. If I could afford to pay for the service I would love to but seeing how chemo takes every extra cent and also the saved up cents I’ve got it’s not really an option for some people. But being able to spoof someone somewhere using a VPN service may not be something to most people but for those that don’t have many days left it’s a fun feeling anyways. Or at least was a fun feeling now that I can’t even get an account with my email accounts. Also you guys here at this here website keep up doing what y’all been doing. Y’all taught some of us more about this privacy stuff then over half the dang internet websites All combined together. So just remember that next time someone wants to piss in your water, and make some negative remarks on the work you guys are doing here.
10👍⬆️…
I am honestly shocked to read so many reviews about Protonvpn on a couple of websites about forced auto-renew,credit card info stolen,charge cancellation refusal,refund refusal and so many other horrible complaints.
Can you imagine how many people have been victims of Proton?
Only by reading these reviews will you understand the anguish,bitterness and despair of these people.
Proton’s policy is hidden and underground and lacks transparency.
The Proton website does not mention automatic renewal anywhere.
If you write to the support of the website “How can I cancel the automatic renewal?” or “How do I cancel my recurring subscription?”, the response is “We’re sorry,but nothing matches your search terms.Please try again with some different keywords”.
If you write “Automatic renewal”, the answer is “How to pay for Proton services in Russia”, this is a disgusting association.
As for the alleged safeguarding and protection of personal data by Protonvpn and Protonmail,it is just a touted theory,nothing more.
Considering Proton as an evil and perforated vpn,thirteen months before the end of my subscription I got rid of it. (Invoice #117…0)
Proton does not survive on user subscriptions but on grants from the Swiss government and donations,offers and grants from Organisations,Foundations,Services and Individuals.
That reminds me of something.
It has free internet service and is a good VPN
works with OpenVPN too.
better that
nordVPN
and
ExpressVPN
I spoke to Proton, their no-log policy aren’t the same for ProtonVPN and ProtonMail. Don’t worry, ProtonVPN is good. If you want, use ProtonMail onion service, should Swiss court orders ProtonMail to log IP address.
We have been using ProtonVPN for about a year, and it has worked pretty well for us. However, as of October, 2022, servers are beginning to be overloaded more frequently, and speeds are declining.
I do not understand the objection that certain features are not free. The famous saying runs: “If you aren’t paying for the product, YOU are the product.” I would rather pay for a VPN than have the VPN company receive funding from sources other than its customers.
I am not sure if we will stay with ProtonVPN. I found the review spot-on in most regards; however, I do think the criticism of its costing money is misguided.
https://protonvpn.com/blog/stealth-vpn-protocol/
I cant even access proton’s website in Africa.
Excellent post about ProtonVPN Steve. I would only add an issue I recently had with this VPN as I had to reinstalled my Linux distribution several times due to their DNS error. Even with a wifi or cable connection, ProtonVPN affected my internet. It made it impossible to browse or load any website. I would never recommend it for Linux or at least Zorin OS.
I had similar experience but mine was caused due to VPN being on while powering off pc causing the ipleak protection to stay active when logging back which block all traffic including proton client.
Firstly, I know at least 1 person that can testify that proton-mail encryption is extremely weak… from an encryption strength point of view…… better to over-encrypt on it (like Hushmail in the past);
Now the VPN is very slow compared to other VPN (even with WireGuard).
Moreover, I know that Proton sends IP access to Protonmail when I European judge asks for it (see https://thehackernews.com/2021/09/protonmail-shares-activists-ip-address.html)
Leon Pardi
As it turned out it’s because there’s only privacy but not anonymity.
Were they using the Free porton mail or paid?? You get what you pay for. They even say you are not fully encrypted on the free tier.
I have mixed feelings about Proton, knowing ProtonMail logged, but it offers .onion service. Being from Swiss, is still a good place for privacy.
Who really cares if Proton Corp’s Andy Yen was recently interviewed by Wired Magazine? Nobody really.
Anyone interested can read carefully and word by word Sven Taylor’s review of Protonvpn and Protonmail and clearly see the truth and reality.
I’m not going to go into detail about my experiences with Proton right now,but ultimately Proton is an obnoxious vpn in every way.
The article mentions privacy.com as a mechanism to pay for Proton’s services anonymously (through a virtual credit card). Doesn’t this merely shift the trust to a different online provider? How is this any different from paypal? Is the only advantage to decouple the payment identity from the email account identity?
I’ve enjoyed ProtonMail and ProtonVPN (free versions) for a while now. I recently upgraded my ProtonVPN to the Plus plan and am excited with the the servers and features like Secure Core.
ProtonVPN serves my threat model perfectly. Proton is a real-world company; there’s no “security through obscurity” when it comes to Proton: Proton is transparent, and I trust Proton.
I use a Windows laptop and an iPhone. My home connection is only 100Mbs, so ProtonVPN is handling all my home online web activity perfectly. As for outside the home, there’s plenty of fast 5G in my area, so no trouble with ProtonVPN speeds on the iPhone 13 ProMax. (I don’t game or stream movies, but I do make extensive use of video calling services.)
I don’t expect the best for free. If one wants cheap, or “free,” he should stick with Facebook and Google.
Proton Corp’s Andy Yen was recently interviewed by Wired Magazine to discuss his company’s future.
https://www.wired.com/story/proton-mail-calendar-drive-vpn/
They claim to offer a “free” version but make it so hard just to OPEN an account that is not worth even trying.
Use disposable email, and open via browser when making new account
proton stole money from my credit card the account was closed for over a year, took max payment out! they are being investigated for fraud/theft by the credit card agency.
Never say never. Proton is an insidious and marginal provider.
I have ordered and purchased dozens of products online and my providers have always sent me an email confirming my order and purchase. Proton has never done that,it may be the only exception in the world.
Proton support is slow to respond citing the large number of tickets and the situation(?)and when it does respond,it is just parroting.
Proton servers overload relatively quickly,making it difficult to operate the computer.
Proton is based in Europe,where I also live.
However,after two years of promises,my language has not yet been implemented in the Proton application.
You see,other unknown and third world languages precede it,aiming at clientele and wealth.
Poor minds! Poor Protonvpn!
I have used Proton’s products for nearly four years and never had a problem. Their customer service has been very prompt in responding too. My only complaint is that I think Proton focuses to much on fluff rather than things that matter.
What happened to you was unfortunate, but I am curious as to which email service do you use or recommend?
As for stability, your mileage may vary, too often I spend 30 minutes a day trying to get a working connection, logging out, logging in, reconnecting, trying different servers and so on. The software is primitive, for linux there is no split tunneling.
So,
I’ve been using Proton for a bit over 3 months now.
I’ve noticed, ping times are still ~70 whereas they were ~30ms with my last vpn, but I mean who can really tell the difference there when just goofing off. Speeds, for me, are 10Mbps which is my max connection speed so that’s great.
Occasional issues trying to connect, but otherwise rock solid and never once have I had a disconnect. Haven’t had any need to use support.
Overall still a great experience. Cheers All
Proton VPN is outstanding service and I can recommend it to everyone. One VPN service that is also worth to mention and review is IVPN based on Gibraltar. Beside standard VPN features and basic anti tracker this VPN offer Hardcore mode which block all Facebook and Google trackers in websites, apps and other. Also you don’t need email to create account you simply generate your account and login with one code which is also good for privacy.
Good news! As of mid-October, ProtonVPN is now fitted with WireGuard and it is turned on by default for their customers.
https://protonvpn.com/blog/wireguard/
I just noticed your Kill Switch comment,
I was curious if you noticed there are 2 settings for the KS.
Kill Switch
vs
Permanent Kill Switch.
The latter disables my connection no matter if I have Proton running or not.
Cheers