
Update: In a statement provided to RestorePrivacy, Airbus has confirmed the cybersecurity incident and has launched an investigation (full statement below).
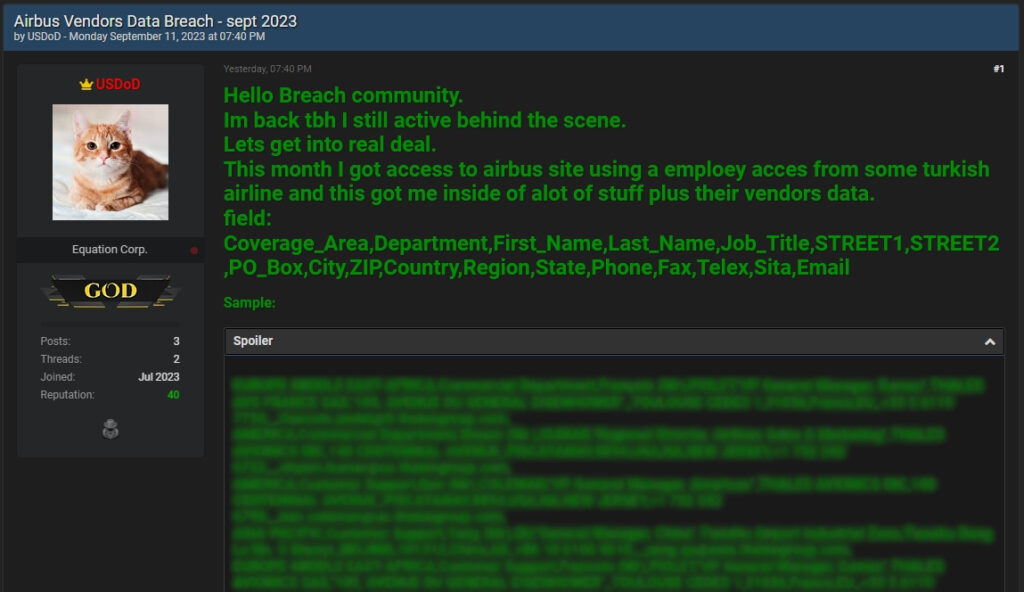
A hacker using the moniker “USDoD” has leaked sensitive data of 3,200 Airbus vendors, including their names, contact details, email addresses, physical addresses, and more.
A hefty sample of the data was made freely available on BreachForums, while registered members paying a small sum can view the rest.
The vendors exposed in the provided data sample are Avic Cabin Systems, Aerolux, and the Thales Group. However, none have made any announcements about an indirect exposure or data breach.
USDoD is the same hacker who, in December 2022, offered a database stolen from the FBI’s “InfraGard” network system for sale on hacking forums. Having evaded prosecution since then, the hacker returned to the cybercrime spotlight this week, announcing his participation in the “Ransomed” ransomware-as-a-service (RaaS) operation and leaking the Airbus data.
It is unclear if access to Airbus’ systems is to be monetized through a ransomware extortion process or if the attacker is merely flexing his initial access skills on the hacker forums.
The attacker claims that the breach on Airbus was made possible by first compromising the account of a Turkish Airlines employee. Turkish Airlines is an Airbus customer, and hence, some privileged employees are likely to have access to the airplane maker’s systems.
Cyber-intelligence company Hudson Rock has confirmed the validity of this claim, saying that a Turkish Airline computer was infected by Redline, a widely distributed information-stealing malware family, in August 2023.
Hudson Rock states the Turkish Airlines employee likely attempted to download a pirated version of the Microsoft .NET framework but downloaded a malware dropper instead. This is a typical distribution pathway for info-stealers, which are generally promoted via malvertizing on Google Search, torrent sites, and Black SEO tactics.
It is highly possible that the attackers used credentials gathered and exfiltrated by the Redline stealer to hijack the Turkish Airlines account and access Airbus’ systems directly.
RestorePrivacy has contacted Airbus to learn more about the claimed breach, scope of impact, and measures the firm has taken to remediate the situation.
Airbus’s statement to RestorePrivacy
Airbus provided RestorePrivacy with a statement on September 13th confirming the cybersecurity incident and the company is now investigating the situation.
Airbus has launched an investigation into a cyber event during which an IT account associated with an Airbus customer has been attacked. This account was used to download business documents dedicated to this customer from an Airbus web portal.
Immediate remedial and follow-up measures were taken by our security teams to prevent our systems from being compromised.
As a major high tech and industrial player, Airbus is also a target for malicious actors. Airbus takes cybersecurity seriously and continuously monitors activities on its IT systems, has solid protection tools, skilled cyber experts and associated processes to protect the company by taking immediate & appropriate measures as and when needed.
– Airbus spokesperson
Meanwhile, USDoD has also threatened Lockheed Martin and Raytheon, two major U.S. defense contractors, that they are next, which is a direct “Ransomed.vc” ransomware infection threat.

 ‘See Tickets’ Says Hackers Stole Over 323,000 Payment Card Details
‘See Tickets’ Says Hackers Stole Over 323,000 Payment Card Details
Great article Heinrich!