
Popular parental control apps for the Android platform were found to be vulnerable to multiple security flaws, risking the data and safety of the users they aim to protect.
Parental control apps are installed by parents on their children’s smartphones and tablets, setting usage limits, blocking certain types of content, tracking the device location, and giving the parent access to data like SMS content, IM exchanges, and browsing activity.
These apps are designed to help parents keep their children safe online and offline. However, if the apps are vulnerable to unauthorized access and data leaks, they may introduce unwanted surveillance risks and even put the user at physical risk.
Unfortunately, a study from the independent cybersecurity group SEC Consult found that many apps suffer from flaws that could allow unauthorized remote actors to access web dashboards, stealthily track children, and perform attacks.
Additionally, the children themselves can exploit the flaws to remove or bypass the usage or content access restrictions set by their parents.
App Analysis
SEC Consult picked a group of popular parental control apps for analysis, using static and dynamic analysis methods, including scrutinizing the security of their network traffic, whether or not they encrypt sensitive user data, what API access restrictions are in place, and more.
The analyzed apps are the following, ranked by the number of downloads of Google Play, Android’s official app store:
- Find My Kids – 10 million downloads
- Kids Place – 5 million downloads
- Family Time – 1 million downloads
- Quostodio – 1 million downloads
- Wondershare FamiSafe – 1 million downloads
- Parental Control Kroha – 1 million downloads
- Parental Control App – 1 million downloads
- Boomerang – 100,000 downloads
All eight apps feature a web dashboard, are accompanied by privacy policies, and their vendors are located in the U.S., Canada, Japan, Spain, Hong Kong, Ukraine, and Kazakhstan.
The vulnerabilities SEC Consult’s analysts looked into concerned the five categories of remote device control, privilege escalation, restriction bypass, “safe mode” bypass, and web-based attacks.
Worrying Security Findings
None of the tested apps allowed remote control of devices they are installed on, but this is where the positive findings of the study end.
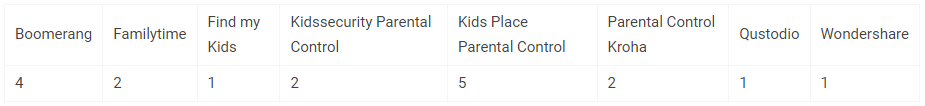
All eight tested apps had at least one vulnerability, with Kids Place topping the negative standing with five flaws and Boomerang coming second with four.
“Two of the tested apps allowed an attack against their own parent device using a cross-site scripting (XSS) JavaScript payload. If a parent used the web dashboard of the app, the children’s device could perform arbitrary actions on behalf of the parents and potentially bypass current restrictions or gain access to the parents’ user credentials.” – SEC Consult
Restrictions could be bypassed on all tested apps by revoking their permissions via Android settings, which disables them. The parents granted these permissions during installation, but since the user is still privileged enough to access Android settings, the system is weak.
In the cases where the apps overlay a screen to prevent changing settings without providing a PIN, the users may reboot the device on safe mode and uninstall the parental apps entirely.
SEC Consult didn’t disclose exactly which vulnerabilities impact each tested app to prevent specific targeting and exploitation. However, the firm has informed all vendors accordingly since November 2022, and some are already working on a fix.
SEC Consult
Privacy Concerns
Parental apps are by nature intrusive to their users’ privacy, but keeping the sensitive data they handle safe is crucial; otherwise, extremely exposing data leaks may occur.
SEC Consults found that the data the apps send from the devices to their servers is not encrypted, so if the company’s employees wanted to access it, they would see everything.
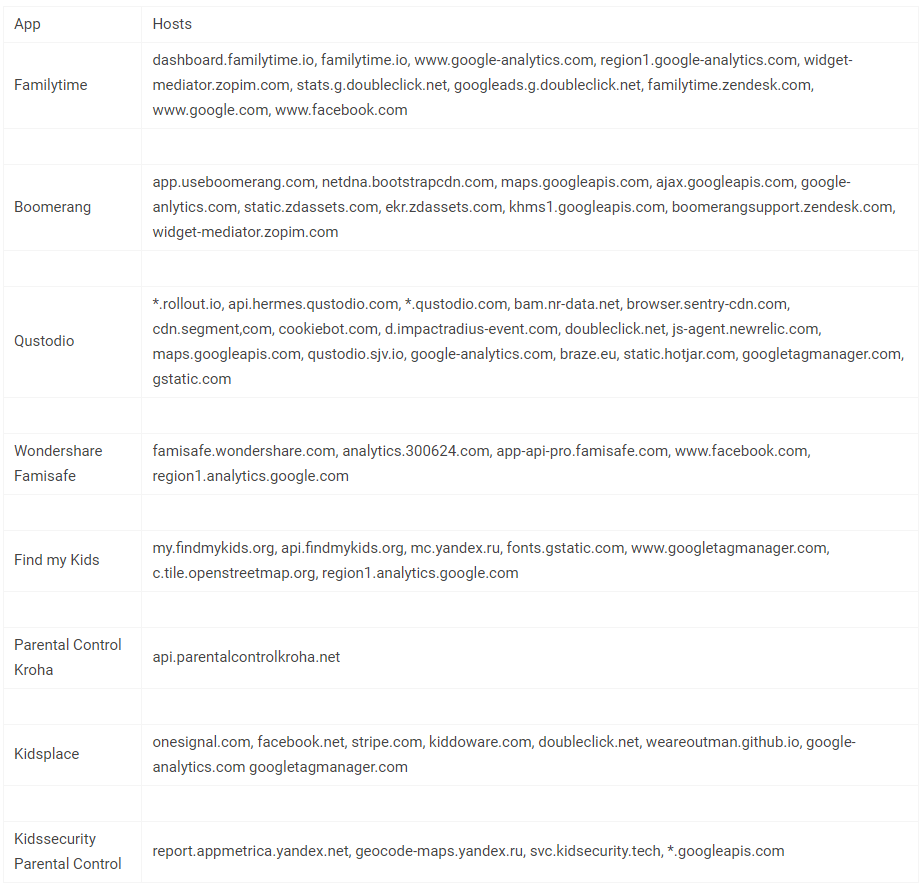
Finally, there’s a galore of third-party tracking platforms loading their code snippets on the web-based dashboards of these apps, including Google, Yandex, and Facebook. This means that some data parents access on these dashboards is also shared with networks of dizzying size.
SEC Consult

 Fujitsu Smart City 5G Source Code Leaked Online
Fujitsu Smart City 5G Source Code Leaked Online
Though I am not a parent, I have been using ESET Parental Control App whose subscription comes included with ESET Internet Security on my android smartphone to filter out bad websites and further secure my smartphone. For example, spyware like Pegasus trick users on Android to enable accessibility access for it but ESET Parental control will block any such attempt as it locks down such areas of phone.
ESET Parental control is a very powerful, reliable and trustworthy piece of software from ESET. It is a high quality product which I believe respects user privacy as ESET is a highly reputed and established brand.
Similarly Parental control apps from Norton and Kaspersky are also considered good.
I think you are preaching to the wrong crowd . People who would even think about installing apps such as this have no regard for what data gets exposed . Dont treat your phone like a private device , because it isnt . That fight is a lost cause atm .
That’s why most people and reputable companies in the know prefer the iPhone ecosystem. Then again, Canada’s national police agency prefers Android. There are always exceptions.
I was half expecting Life360 to make this list.