
A hacker is claiming to have breached Fujitsu’s code repositories and is now selling the source code for Fujitsu’s Smart City 5G project online. RestorePrivacy examined the data sample and obtained an explanation from the hacker on how the code was accessed.
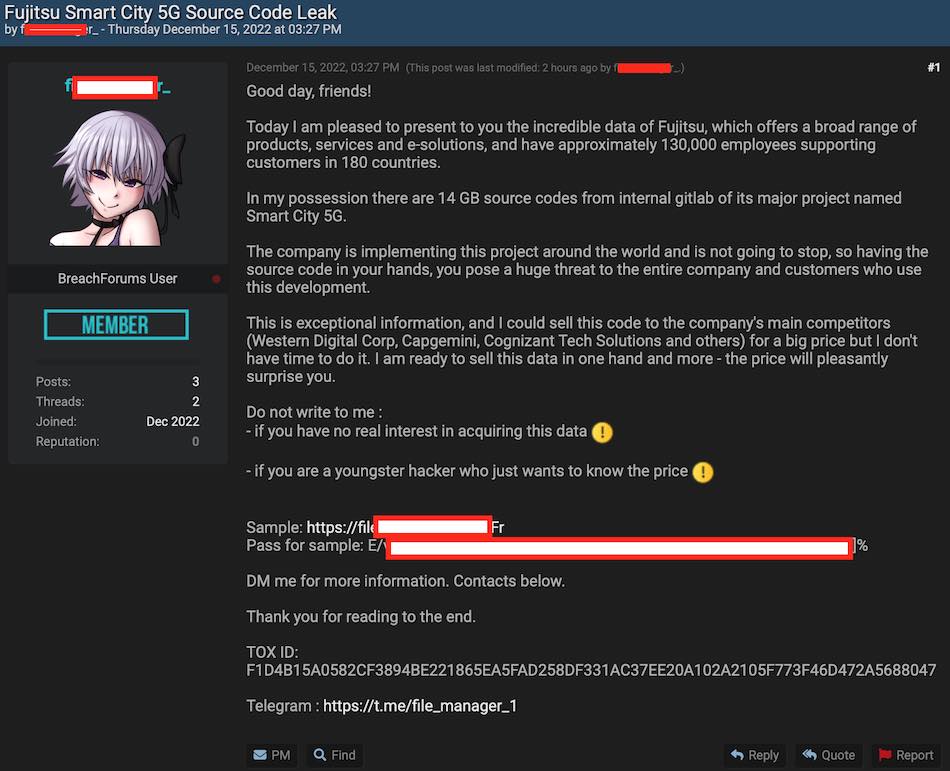
Samples of data allegedly belonging to Fujitsu’s Smart City 5G project were leaked on a popular hacking forum over the weekend. The threat actor is selling the full data set for an undisclosed price.
The data appeared on the hacking forum ‘Breached’ over the weekend, with links to a third-party file-sharing platform where anyone could download and view samples from Fujitsu’s Smart City 5G code.
The seller is claiming to have 14 GB of source code from the Fujitsu Smart City 5G project.
Source: RestorePrivacy.com
The threat actor is claiming to have breached Fujitsu via an internal GitLab server.
Hacker releases data sample
In our investigation for this report, RestorePrivacy examined the data sample posted by the threat actor. When unpacked, the sample size is about 50 MB.
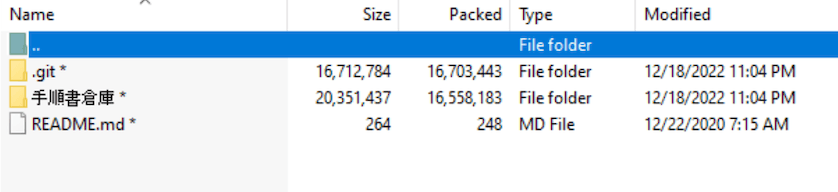
Source: RestorePrivacy.com
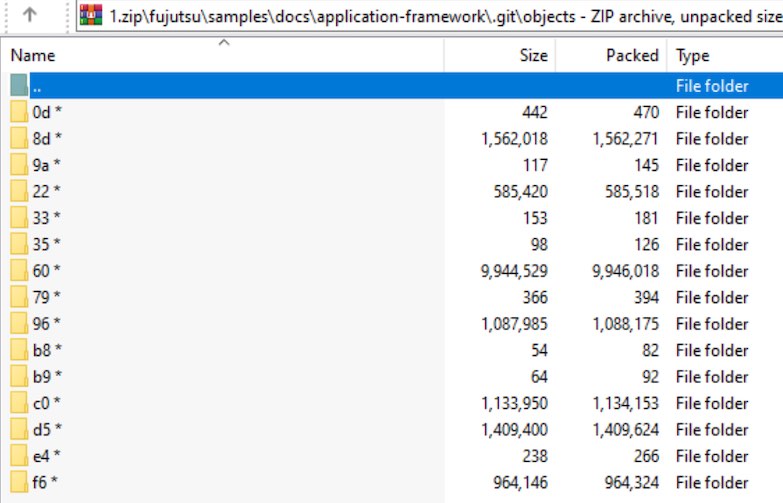
Source: RestorePrivacy.com
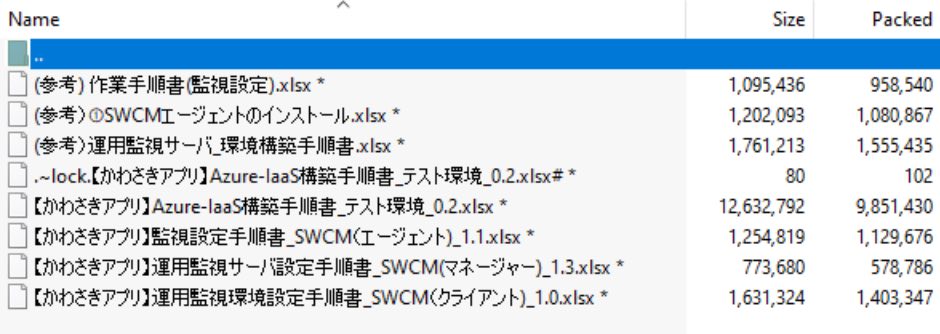
Source: RestorePrivacy.com
The hacker told RestorePrivacy that the breach took place within the past few months and access was obtained through an GitLab vulnerability. The hacker also demonstrated the vulnerability live in action with another company.
Source: RestorePrivacy.com
The hacker told RestorePrivacy that this same method has been used to obtain “many source codes of comapnies” (sic).
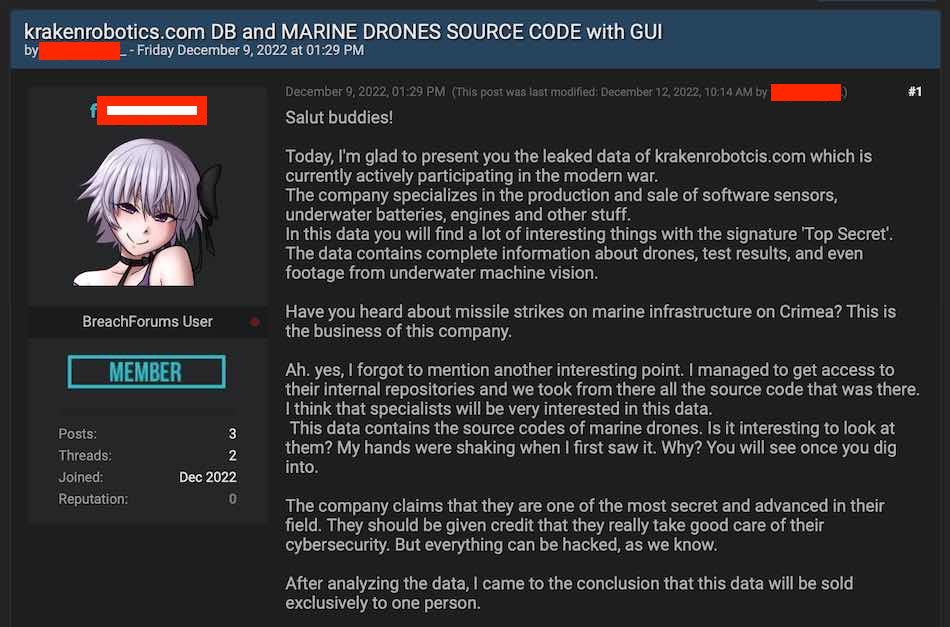
Earlier this week, the hacker also posted the source code from Kraken Robotics for sale on the same forum.
Implications of this breach
Should the hacker’s claims prove accurate, the source code leak could be devastating to Fujitsu and a boon to its competitors in the smart city 5G IOT space, which is being rolled out globally.
RestorePrivacy reached out to Fujitsu for comment before publication.
Fujitsu has confirmed they are investigating the situation, but do not have any additional commentary to provide at this time.

 NIST Retires SHA-1 Cryptographic Algorithm After 27 Years
NIST Retires SHA-1 Cryptographic Algorithm After 27 Years
Leave a Reply