
Google has announced that all Pixel 7 and Pixel 7 Pro users will now get to use “VPN by Google One” for free.
Google’s VPN is normally available only to Premium subscriptions on Google One, giving users a privacy cloak for when they’re surfing the web using public WiFi or untrustworthy connections.
Pixel users can now activate their VPN connection through the Google One mobile app even without a Google One membership.
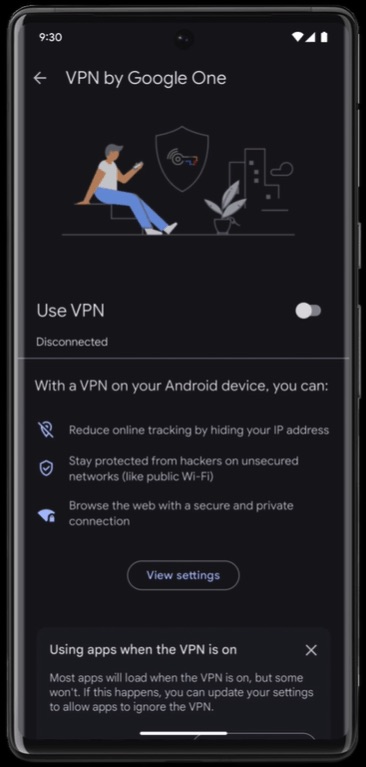
This VPN access is handy for smartphone users who browse the internet while on the go and often find themselves forced to trust unknown networks in airports, cafes and shared working spaces.
Google says its VPN solution is completely safe from outsiders, even Google itself, so nobody can see the users’ network traffic or identify them.
To dissociate users with VPN connections, “blind signing” is used. Google says the system is essentially a strict separating layer between browsing data and traffic rerouting servers, so even users who are logged in to their Google account all the time cannot be identified.
Moreover, the users’ real IP addresses are not logged in Google’s servers but instead processed on the fly, so the origin of the network requests is completely hidden.
“There’s some minimum logging to ensure quality of service, but this never includes your IP address or network traffic,” claims Google.
Finally, Google promises its VPN has such good performance that users are unlikely to notice any speed drops or connectivity hiccups.
For alternative VPN apps suitable for the Android platforms, check out our Android VPN list containing solid options like NordVPN, ExpressVPN, Surfshark, and others.
More Pixel Perks
Another feature announced by Google exclusively for the Pixel family is a Privacy and Security overview, giving users a summary of their stance.
The new system will scan stored accounts, security settings, and system update status and inform users of actions they can take to improve their security.
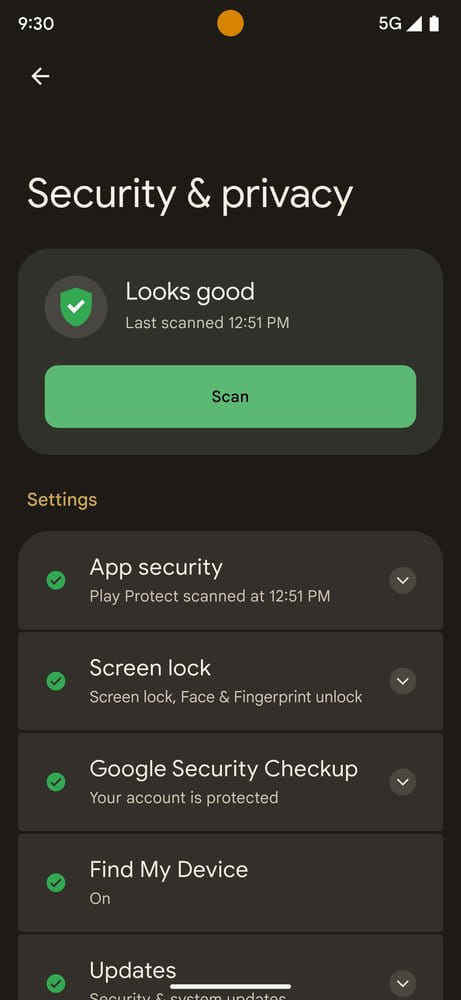
This system incorporates account password protection, checking if the user’s credentials have leaked on the internet by comparing encrypted pairs, never getting to learn usernames and passwords in the process.
The privacy and security system will run periodical scans to determine the status of the device, but the user also gets the option to perform a scan on command at any time.

 ExpressVPN Clone Sites Infect Visitors with Redline Malware
ExpressVPN Clone Sites Infect Visitors with Redline Malware
Works in Canada. No option to select server location so I doubt it has any benefit to access geoblocked sites.
This is like Dracula being given the task of guarding and securing the blood bank.
LoL so true 😉
does not work OUTSIDE the USA, wothless
Would Google still be able track inside your gmail, drive, photos, etc if you’re always running Google’s VPN or any VPN for that matter?
I confused about your willingness to present a Google product without significant cautionary language.
Wow! These are the people that invented surveillance capitalism. They shadow ban people with social and political views they disagree with. They block search results they don’t agree with. They own all of your Gmail content. These are the people that sell all of your data and/or use it against you.
I’m accustomed to articles from you that critically review and critique online products and services. This is basically a promo piece that is seemingly written by Google?
What’s up with that?
Hi Mike, we have a small team of writers covering privacy and security news and individual views may vary. This is simply a news article we wrote covering a very large company (Google) that will be offering their VPN for free on Pixel phones. It’s just news (filed under our news articles) and is not promotional in nature.
As for me, any services that has google in it will try to avoid. Its main business is to know everything about you and makes money out it.
Fox Incorporated Henhouse Security
Trust Us, we KNOW Henhouses….!
Thank you for the post Sven. I have a question, wthat do you thing about google pay and google wallet for pay? is secure ?
Yes, these are secure payment options, no doubt, but it also gives Google insight into your purchase habits.
why is your article saying it’s free for Pixel 7 Pro owners when you need to have a Google One subscription of at least 2TB, which costs $9.99/mo.?
Sven Sir can I choose country of my choice when using Google VPN? Does it unblocks streaming sites?
Would you recommend this VPN?
While this is good news and we’ll commend Google on it, I still (personally) recommend avoiding Google services due to privacy issues and using alternatives. I have never tested Google’s VPN.