
A hacker calling themselves “the McFlurry Bandit” has leaked what is claimed to be source code from a breached McDonald’s Git repository.
The leak was first spotted and published on social media platform X by user’ vx-underground,’ who noted that the leak contained a suspiciously large quantity of code. The screenshots posted on X include one for McDonald’s Single Sing-On (SSO) service, used for secure authentication.
On Wednesday, a user named ‘euphoria’ reposted the leaked data on a popular hacker forum, making it widely available.
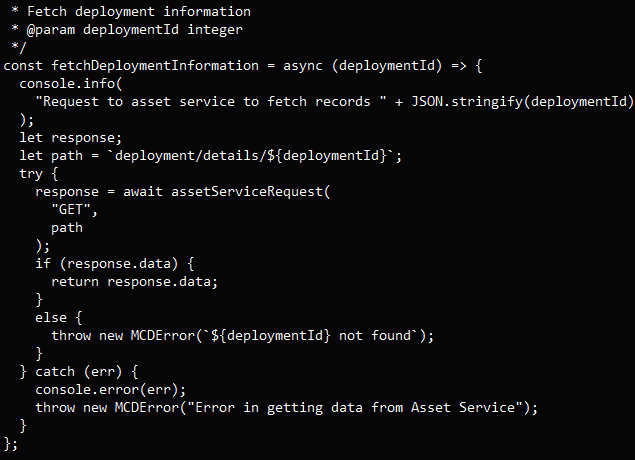
RestorePrivacy reviewed the contents of the leaked files and found several references to Docker, a platform used for developing, shipping, and running applications inside lightweight containers, components relating to Internet of Things (IoT), continuous integration/continuous deployment (CI/CD) pipelines, and possibly a Node Package Manager (npm) module. There are also references to AWS services like Lambda functions.
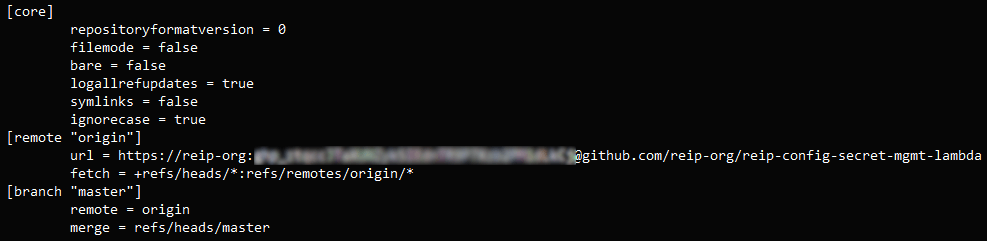
Upon further examination of the configuration files, documentation comments, asset folders, and script files, the likelihood of this data leak being real increased. We found personal access tokens in the URL of configuration files, indicating that this data was exfiltrated from a private repository.
RestorePrivacy
Moreover, a random sample JavaScript file we looked into, which includes functions for interacting with AWS services and Git, includes a custom error class named ‘MCDError,’ which suggests that it could be part of a McDonald’s software project (“MCD” is a common abbreviation for McDonald’s).
Of course, these indicators aren’t conclusive on their own about the origin of the data, as the possibility of the data being intentionally falsified exists. However, such a scenario becomes less plausible with the presence of multiple, consistent indicators in large volumes of source code.
RestorePrivacy has contacted McDonald’s since the initial leak of the data to ask about the authenticity of the files, but we are still waiting for a comment. As such, the origin and content of the leaked data remain unconfirmed.
If the leaked code is legitimate, the potential damage to McDonald’s could be significant and multifaceted, including security risks from the exposure of private access keys and intellectual property loss from the exposure of proprietary technology and business processes. If malicious actors leverage this knowledge to compromise critical systems, the ramifications could extend to impacting services.

 Independent Deloitte Audit Verifies NordVPN’s No-Logs Claim
Independent Deloitte Audit Verifies NordVPN’s No-Logs Claim
Leave a Reply