
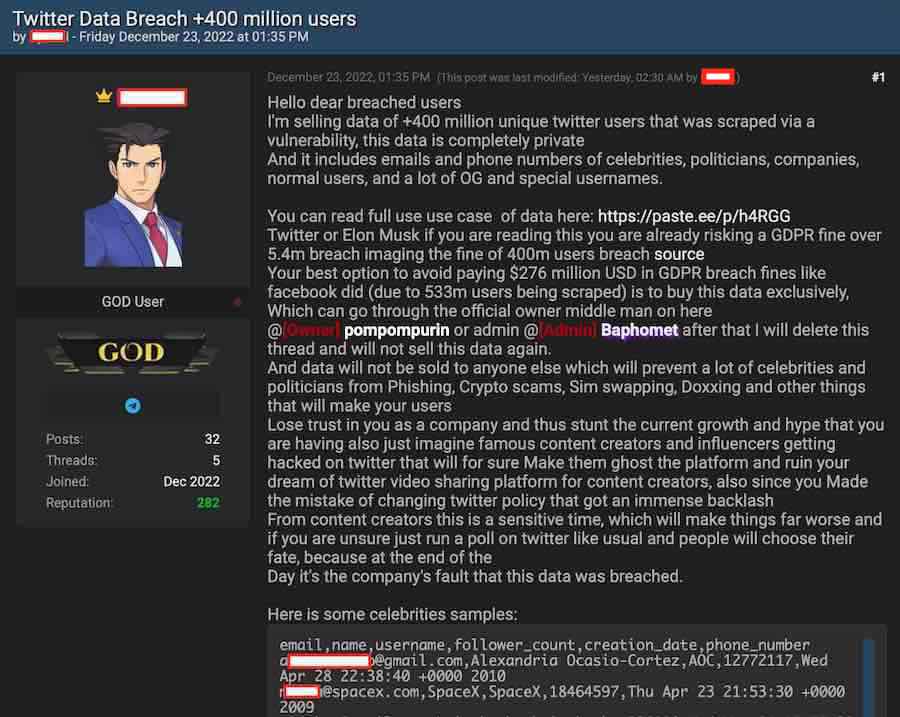
In what appears to be yet another privacy blow to Twitter, a hacker is now selling data allegedly from 400+ million Twitter users.
In a post published on the ‘Breached’ forum yesterday, the hacker explained that the data was acquired in 2021 and early 2022. This timeframe lines up with the previous Twitter data leak of 5.4 million users that we reported in July.
The hacker has confirmed the data was obtained via the same vulnerability.
Source: RestorePrivacy.com
As to the legitimacy of the data, everything appears to check out.
A few of the leaked “celebrities” and notable users in the sample include:
- Alexandria Ocasio-Cortez
- Kevin O’Leary
- Donald Trump Junior
- Piers Morgan
- Brian Krebs (security researcher)
Analysis and verification of data sample
The seller has listed two samples for verification on the hacker forum. One is directly in the post and contains noteworthy individuals (above). The second sample contains 1,000 users from verified Twitter accounts saved in a .CSV file.
We examined the data sample of 1,000 users that was released via a third-party file-sharing website. When cross-checking Twitter users in the sample with publicly available information, the data appears to be authentic. Some of the accounts did not have a linked phone number.

Source: RestorePrivacy.com
Furthermore, the hacker is also requesting to go through a middleman service via the forum’s owner Pompompurin, which further bolster’s the hacker’s claims.
How did the breach allegedly happen?
Based on statements made by the hacker, it appears this data was from the same API vulnerability as the previous breach. This vulnerability allowed the hacker to enter known email addresses and match them up to Twitter accounts. A similar type of exploit also resulted in the Facebook leak of 533 million users in 2021.
The seller is claiming that the vulnerability was exploited in 2021 and early 2022, before Twitter eventually patched it.
Looking at the Hacker One report from the previous data breach, the Twitter vulnerability was patched on January 13, 2022.
Brian Krebs, a security researcher who is also listed in the data sample for this latest breach, obtained more information from the hacker about how the leak transpired:
The seller told me they scraped the data using the same set of weaknesses in Birdsite APIs that allowed the scraping (and publishing) early this year of profile data on 5.4M Twitter users.
– Brian Krebs on Mastadon
They said they scraped the data via an exploit that was patched earlier this year, in the login api, and specifically the part of it that checks for duplicate accounts.
That, according to the seller, leaked the Twitter user ID, which was then converted via another Twitter API into a username. They also said that same iterative process worked for user telephone numbers.
Possible implications
Should the data prove to be accurate, this would be the largest Twitter breach on record, massively dwarfing the previous breach of 5.4 million users. Twitter is already being investigated by the EU for the previous breach.
Like Meta/Facebook, who was fined $276 million for their previous data leak, this breach could result in large fines under Europe’s GDPR privacy laws.
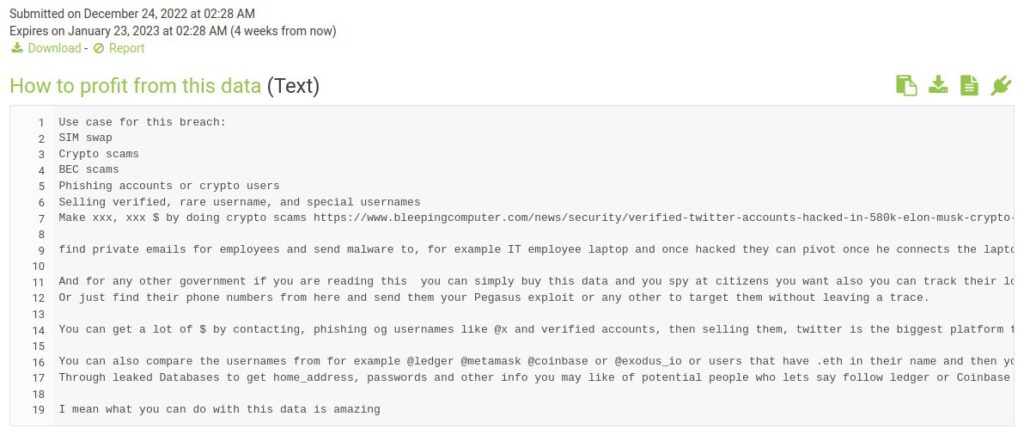
This breach could also put millions of Twitter users at risk for fraud, phishing attacks, and more, as the seller explained in a separate post on paste.ee that has since been removed:
Source: RestorePrivacy.com
Restore Privacy has reached out to Twitter for comment, but we have not heard back at the time of publication.
We will update this article with any new developments.

 Phishing Attacks that Bypass 2FA Protection Are on the Rise
Phishing Attacks that Bypass 2FA Protection Are on the Rise
https://www.bleepingcomputer.com/news/security/twitter-claims-leaked-data-of-200m-users-not-stolen-from-its-systems/
“Twitter finally addressed reports that a dataset of email addresses linked to hundreds of millions of Twitter users was leaked and put up for sale online, saying that it found no evidence the data was obtained by exploiting a vulnerability in its systems.”
Sven Sir please also cover Lastpass data breach.
I second this. And include the criticism by 1Password. It’s not the first time LastPass has been proven less than reliable and honest.
Should we afraid about rising “DeepFlakes”? Thank you!
This would explain the recent tighter login and security protocols.
It is important to note that data leak, data theft, and data breaches can result in further loss of user’s data and funds from bank account as the data about him or her that goes in wrong hands givers the malicious actors opportunity to carry out a well designed. sophisticated and calculated attack on the user based on the information available giving him or her further troubles. The motive of target is based on the vested interests if the attacker which can be political, religious, financial or may be just intention to cause harm.
Sven Sir should one also have a side VPN other than the main VPN? How many VPN accounts should one ideally have?
Hi Bubble Bird, that’s definitely not a bad idea as it distributes trust further across different VPNs, so all of your eggs aren’t in one basket. I like to run one VPN on a router connected to a nearby server, and then another VPN on my computer, but for many users this may be overkill. It all depends on your threat model.