A supermassive data leak comprising 26 billion records, dubbed the “mother of all breaches” (MOAB), has been discovered, and many media outlets are touting it as a historic finding that should be a wake-up call for regulators, especially in the U.S.
However, the truth is that the news is overblown.
The MOAB data is most likely an aggregation of already leaked, mostly old and unusable information; the likelihood of large volumes of duplicate records in the dataset is very high. Still, and though the actual impact on people’s security is limited at best (or worst), that is not to say that the finding is insignificant.
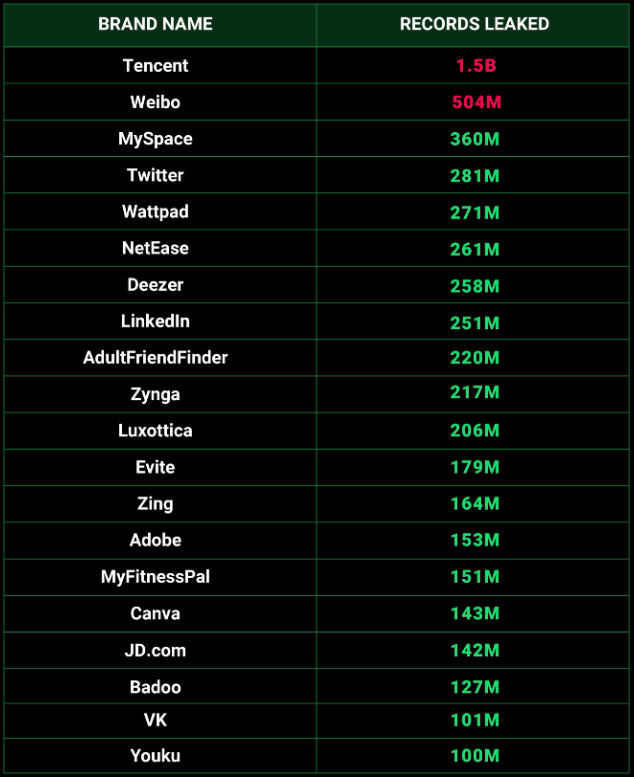
The discovery of MOAB was the work of researcher Bob Diachenko and the Cybernews team, who found an unprotected database instance that contained 26 billion records in 3,800 folders. The original report mentioned that the dataset appeared to be a compilation of previous breaches, with the largest number of records, 1.5 billion, coming from the Tencent QQ messaging platform.
Other data found in the set includes Weibo (503M), MySpace (360M), Twitter (281M), Deezer (258M), Linkedin (250M), AdultFriendFinder (220M), Adobe (152M), Canva (142M), VK (100M), Daily Motion (85M), Dropbox (68M), and Telegram (40M). The data also included highly sensitive data from government organizations in the U.S., Brazil, Germany, and the Philippines, among other countries.
Cybernews
The report mentions that the leaked dataset, which is of unknown origin, “almost certainly holds new data, that was not published before.” However, this statement is based on the assumption that the reporting party’s own data leak checker contains a total of 15 billion records derived from 2,500 data breaches, and hence the rest must be new. However, this fails to account for duplicates in the dataset and is far from concrete evidence of new data existing in the set.
Troy Hunt, the creator of the “Have I Been Pwned” breach alerting service, declared that there’s no point in adding the data to the platform, as it appears to be data that is already there. This means that Hunt does not see new data in the set.
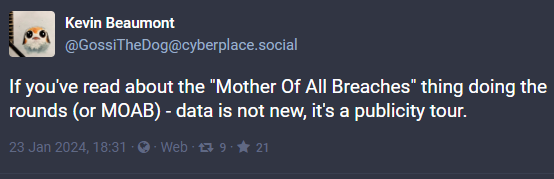
Security analyst Kevin Beaumont also took to Mastodon to call the “mother of all breaches” a publicity stunt, noting that the data is old.
MOAB still noteworthy
Despite the above, and even if MOAB contains no new data at all, the risk of such an extensive collection circulated among cybercriminals shouldn’t be underestimated. Attackers possess sophisticated tools to conduct data correlation among massive sets and to perform automated phishing and credential-stuffing attacks against long lists of websites and online services.
Aggregated data from multiple breaches can be combined to create detailed profiles of individuals. These profiles are valuable for targeted phishing campaigns or more sophisticated fraud. Large datasets can also be used to train AI and machine learning models for various purposes, including creating more effective phishing emails or cracking passwords.
Even if exposed users have previously changed their passwords to protect online accounts, certain types of personal information, like Social Security numbers, birth dates, or full names, do not change over time. Cybercriminals can use this static information for identity theft, fraud, or spear phishing attacks at any point in the future.
Understanding the potential value of old, leaked data highlights the importance of:
- continuous vigilance
- regular updates of security credentials
- enabling MFA protection
- monitoring accounts for unusual activities.
So, if anything, MOAB should act as a good reminder for all to exercise the above.
“If, time after time, we’re told as consumers that nothing important was stolen in the last headline breach then why would the bad guys bolt it all together to build this mega list of individuals?” stated Richard Bird, CSO of API security firm Traceable AI.
“The existence of this ‘extremely dangerous’ file proves that all data is valuable, and it is time we stop kidding ourselves that it isn’t.”
“Maybe it finally takes something like a MOAB to get the U.S. Government and the companies operating within its borders to wake up. We live in a nation with no national data privacy laws, no incentives for companies to protect the data they are trusted with, and no disincentives that seem to work.”
As years pass and new breaches inevitably happen, threat actors will create, sell, and leak new supermassive datasets that surpass MOAB in size, creating new, previously untapped possibilities for hackers using advanced data analysis and exploitation tools.

 Zero-Click Bluetooth Attack Impacts Unpatched Android Phones
Zero-Click Bluetooth Attack Impacts Unpatched Android Phones
Thank you for the article Sir. Very informative and helpful.
From the moment I saw this blowing up in the press (daily mail), I figured it was over hyped and sensationalized “news” if you want to even call it that. Then reading deeper, there’s nothing even new, just someone’s stash of old stuff, not even newsworthy in my humble opinion. Even the name they concocted makes me lol — “mother of all breaches” 🧐 hmmm ok….