
Ukrainian police announced they have arrested six people suspected of being members of the “Cl0p” ransomware gang. The Cl0p group has wreaked cybersecurity havoc on businesses and governments alike, with an estimated $500 million in damages from their ransomware.
The operation was conducted by Ukranianan authorities, in collaboration with law enforcement from South Korea, United States, and Interpol.
The Ukrainian National Police stated on Wednesday that they were able to arrest 6 members from the ransomware gang and conducted 21 searches in the homes of the defendants and in their cars. Electronic devices, cars and about 5m Hryvnias ($184,000) in cash were confiscated.

Ukrainian police published a video of the operation, which shows law enforcements entering homes, conducting searches, and seizing the suspects’ belongings.
Ukrainian authorities claim that Cl0p operators have caused more than $500 million in financial damages over the years. The Cl0p ransomware has been around since 2019, but has gained notoriety over the past year. This is caused by their increasing volume of their attacks and hitting dozens of victims by encrypting the files and demanding ransom.
Energy giant Shell, the Reserve Bank of New Zealand and multiple universities and organizations have fallen victim to Cl0p operators. For the past few months, Cl0p operators were able to hack these companies because of the vulnerabilities in Accellion’s File Transfer Appliance, essentially a dedicated computer used to move large and sensitive files within a network.
What is Cl0p?
Cl0p is thought to be an Eastern European cybercriminal gang responsible for large ransomware attacks and has been active since 2019. It appears the group may be associated with TA505 and FIN11, with similar malware.
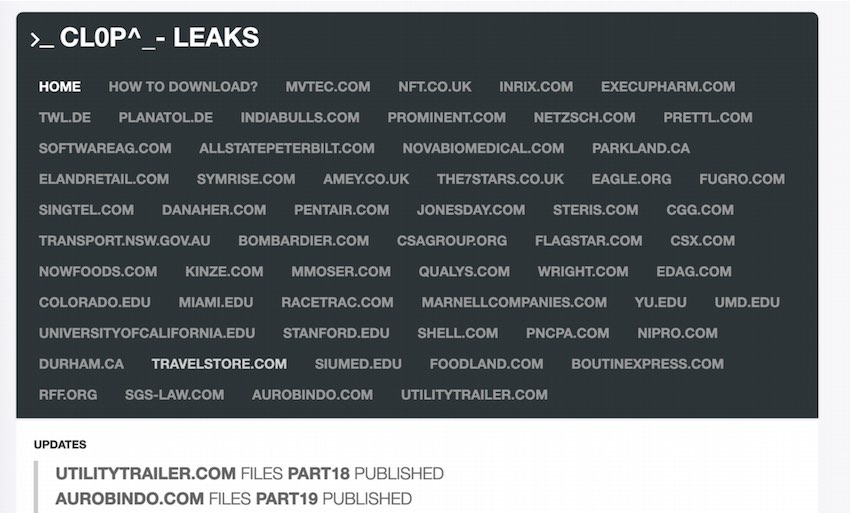
Cl0p is one of several ransom gangs that use double extortion. With double extortion, threat actors go beyond just encrypting the file, they actually threaten to publicize the encrypted data and/or leak all the data online. This allows the gangs to demand two ransoms: one for the key to decrypt the file and a second one to avoid having the data published. Most of these ransomware gangs have their own dedicated data leak website where they will publish the leaked data if the ransom is not paid.
Cl0p published the name of the companies, and the sample of its stolen data, on its website, CL0p^- LEAKS. The data will be removed as soon as the ransom is paid.
Now let’s see how Clop ransomware is tied in with Accellion.
Accellion data breaches and Clop
For the last couple of months, Cl0p has been exploiting the vulnerability in Accellion’s File Transfer Appliance, resulting in dozens of attacks on major companies. Clop stole data from companies that relied on Accellion’s legacy file transfer Appliance and exploited the vulnerability.
So how does this process work with a threat actor?
Cl0p contacts the breached companies through email, offering to negotiate a payment before leaking any data. If the company pays quickly, they will not leak any data, sometimes they even show proof that they have deleted the sensitive data.
“Based on multiple cases the Cl0p operators seem to be professional, respectful and that they even sometimes offer discounts.” according to Kimberly Goody, the manager of the financial crime analysis team at FireEye.
Is Cl0p still going to be active after the latest arrests?
Unfortunately, despite the arrests, the CL0P ransomware gang is still in operation, according to cybersecurity firm Intel 471. Intel 471 suspects that the police raid primarily affected CL0P’s money-laundering business. “We do not believe any of the main actors behind CL0P were caught, as they are probably living in Russia. The overall impact on CL0P is expected to be modest.”
However, the arrests also represent the second time in weeks that authorities have targeted a cybercrime gang by following the money. In early June, the US Department of Justice announced that it had seized most of the ransom paid to Colonial Pipeline hackers. This is a step in the right direction in the fight against ransomware gangs and cybercrime.
RestorePrivacy recommendations:
- Regularly update your systems, software, and applications
- Monitor any warning of suspicious behavior with all accounts
- Only use trusted antivirus and malware software
Related:

 COMB Data Leak: Everything You Need to Know
COMB Data Leak: Everything You Need to Know
Leave a Reply