
A secure browser that protects your privacy is a critical tool for staying safe online and keeping your data secure from third parties. We have been reviewing, testing, and ranking browsers for the past six years and this guide contains the latest recommendations for 2024.
Do you want a secure browser that truly keeps your data private? Well, you may be surprised by how much of your data is actually getting exposed.
WARNING: Many browsers today are actually data collection tools for advertising companies. This is the case for Google Chrome, the largest and most popular browser. By collecting data through your browser, these companies can make money through their advertising partners with targeted ads. We see this same privacy-abusing business model with search engines, email services, and even free mobile apps.
Unless properly configured, most browsers contain lots of private information that can be exploited – or simply collected – by various third parties:
- Browsing history: all the websites you visit
- Login credentials: usernames and passwords
- Cookies and trackers: these are placed on your browser by the sites you visit
- Autofill information: names, addresses, phone numbers, etc.
And as we will explain further below, using “private” or “incognito” browsing will not protect you. Your IP address will remain exposed and various third parties can still track all of your activities. And even legal action may not protect you. Here is a recent headline related to a lawsuit against Google for capturing data from users who are in Incognito mode. This case has been going on for years now and isn’t close to resolution yet.
And even with a locked-down and hardened browser, exploits may still be found that expose your data and possibly your identity. For example, in 2021 there was a spate of zero-day exploits in Google Chrome with various effects up to allowing hackers to remotely execute code on affected systems. We discuss some other privacy issues (and solutions) in our guides on browser fingerprinting and also WebRTC leaks.
But don’t panic. Effective solutions and tools exist to deal with these problems and we cover them in detail in this article. In this browser security and privacy guide, we’re going to explain the following topics:
- Best secure browsers that respect your privacy
- Problems with other browsers
- Browser privacy compartmentalization
- Secure browser add-ons
- “Private browsing” mode is NOT very private (and why you need a VPN in addition to a secure browser)
Incognito / Private browsing mode still leaves you EXPOSED
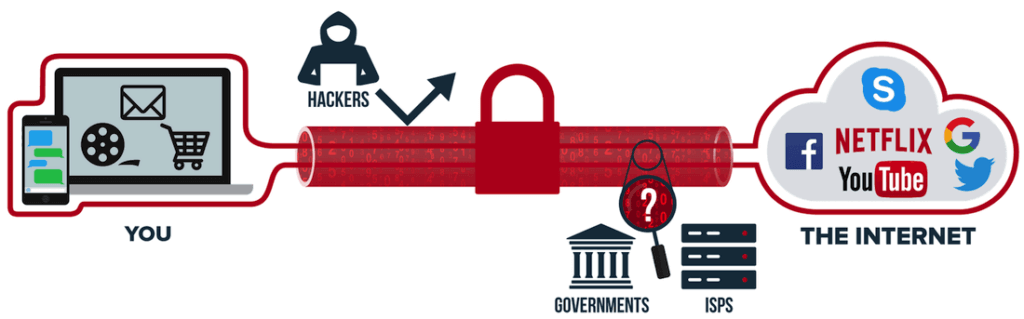
When using “private” or “incognito” browsing mode in your browser, your real IP address and location are still being revealed to every website, ad, and tracker that loads in your browser. Additionally, all your activities remain visible to your internet service provider (ISP). And at least here in the United States, ISPs log everything you do online and share the data with many other parties. This is why it’s critical to use a good VPN for basic digital privacy.
The best way to achieve true privacy while hiding your real IP address and online activities is to use a secure browser together with a good VPN. This protects you at both ends of the line, and in the middle too.
The secure browser will protect you as described in this article, while the VPN will protect your identity by hiding your real IP address and location. The VPN will also encrypt your traffic so your ISP (and any other snoops out there) cannot see your activities online. Here are our top three recommendations from the best VPN list that we have tested and reviewed:
- NordVPN: A fast, secure, audited VPN with advanced privacy features, built-in ad blocker, and a strict no-logs policy, based in Panama (see the 74% off coupon).
- Surfshark VPN: A no-logs VPN service with a large lineup of privacy and security features, based in The Netherlands.
- ExpressVPN – This is a secure and reliable VPN that boasts some great privacy features and also works well for streaming. It is based in the British Virgin Islands.
Now let’s examine the most secure browsers you can combine with a VPN for maximum privacy.
Secure browsers that protect your privacy
In this section we will examine the best browsers based on two main factors:
- Security: How well does the browser protect you from hackers, vulnerabilities, and online exploits?
- Privacy: How much data is the browser itself collecting about you and who is this data being shared with? How does the browser protect your privacy?
Conflicting opinions! Just like with Tor, opinions about browser privacy and security can be wildly divergent and contentious.
This guide is not meant to sell everyone on one browser that beats all others. Rather, it is a summary of information about different web browsers that do well with both privacy and security. Choose the best browser for you based on your own unique needs and threat model.
Here are the most secure and private browsers for 2024:
1. Brave: The most secure and private browser (for both desktop and mobile)
Brave is arguably the most secure browser with simple, out-of-the-box privacy. It is a Chromium-based browser that is fast, secure, and privacy-focused by default. It has a built-in ad blocker and browser fingerprinting protection, while also giving you access to numerous add-ons and extensions. The main developer behind Brave is Brandon Eich, who formerly worked for Mozilla.
To summarize this browser, Brave is based on open-source Chromium, but configured for more privacy. It does well with its default privacy settings and extra features. Here is a brief overview:
- Blocks ads and trackers by default
- Protects against browser fingerprinting and even offers fingerprint randomization
- Built-in script blocker
- Blocks all third-party storage
- Easy access to the Tor network
One of the reasons we like Brave is because it offers simple, out-of-the-box privacy by default. This makes it ideal for those who do not have the time, patience, or know-how for browser customizations and tinkering. Brave can also be used with Chrome extensions, making it an ideal alternative for Chrome. Just download it and you’re good to go.
Tor network – Brave also has a feature that allows you to access the Dark web by simply opening a new window with Tor. We discuss this feature in our guide on how to access the Dark web safely.
Ads – Brave has received some criticism for its ads program, which allows users to “view non-invasive ads without compromising your privacy.” While some people find it hypocritical that a privacy-focused browser has its own ad program, we also see it as a secure funding source. And with many browsers financially struggling, it appears that Brave’s business model is securing this browser’s future and ability to continue to innovate its products.
Here are some more results of Brave’s continuing innovation:
- Brave has developed a private search engine called Brave Search, which is now the default search engine when you do a new installation of the Brave browser. In March of 2023, they added the AI-powered Summarizer to Brave Search.
- A cookie consent blocker, which at least partly frees you from the endless hassle of accepting or rejecting cookies at new sites you visit.
- Brave News, an RSS news reader.
- Brave Wallet, a built-in cryptocurrency wallet.
You can read more about Brave’s privacy features here.
https://brave.com
2. Firefox (when modified and tweaked for privacy)

Firefox is a great all-around browser for privacy and security. It offers strong privacy protection features, many customization options, excellent security, and regular updates with an active development team. The newest versions of Firefox are fast and lightweight with many privacy customization options.
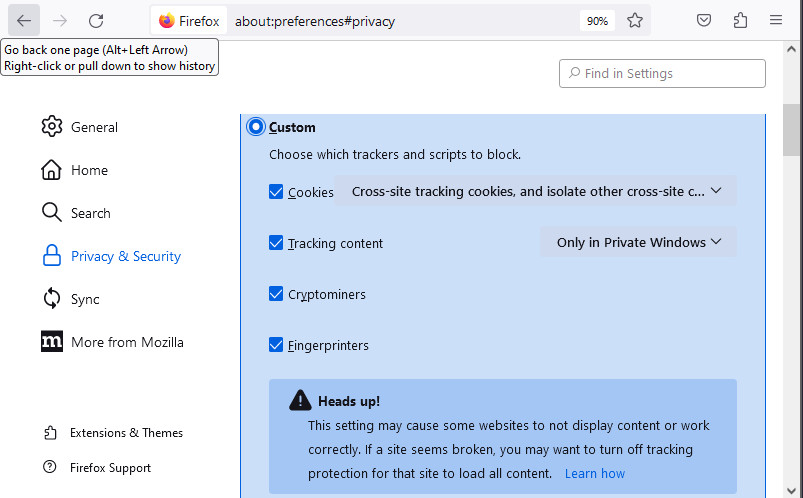
Out of the box, Firefox is not the best for privacy, but it can be customized and hardened, and we show you exactly how in our Firefox privacy modifications guide. Be sure to disable telemetry in Firefox, which is a feature that will collect “technical and interaction data” and also “install and run studies” within your browser.
Within the Privacy & Security settings area, there are many useful customization options for different levels of privacy: Standard, Strict, or Custom.
Another great benefit of Firefox is the ability to use numerous browser extensions that can enhance your privacy and security. We’ll go over some of these extensions later in this article.
Firefox highlights:
- Open source code that has been independently audited
- Active development with frequent updates
- Excellent privacy features and customization options
- Total Cookie Protection (TCP) to prevent cookies from tracking you as you move around the web
- Firefox View to easily return to recently used sites
- Built-in ad blocker
- Many browser extensions supported
- Telemetry and tracking need to be manually disabled
- Other modifications necessary for extra privacy and security
If you want to keep using older add-ons that are no longer supported by the latest Firefox release, you can go with the Firefox Extended Support Release (ESR). For those times when you want the maximum privacy viewing content on your Android phone, you could try Firefox Focus.
For additional customization and privacy settings, check out our Firefox privacy guide.
https://www.mozilla.org/firefox
3. Tor browser

Next up we have the Tor browser. The Tor browser is a hardened version of Firefox that is configured to run on the Tor network. By default, the Tor Browser is a secure browser that protects you against browser fingerprinting, but it also has some disadvantages.
Because it uses the Tor network, which routes traffic over three different hops, download speeds with the Tor browser can be quite slow. The default version may also break some sites due to script blocking. Finally, there are drawbacks to the Tor network itself. These include:
- Malicious/dangerous exit nodes
- High latency
- Many websites block IP addresses originating from the Tor network
- Dependence on US government financing, leading some to claim the Tor network to be fundamentally compromised
See the pros and cons of Tor here.
Another option is to use the Tor browser with the Tor network disabled. In this sense, the Tor browser will work like the other secure and private browsers we’ve covered above. Additionally, you can simply run a VPN in the background. Like the Tor network, a VPN will also encrypt your traffic and hide your IP, but it will be much faster.
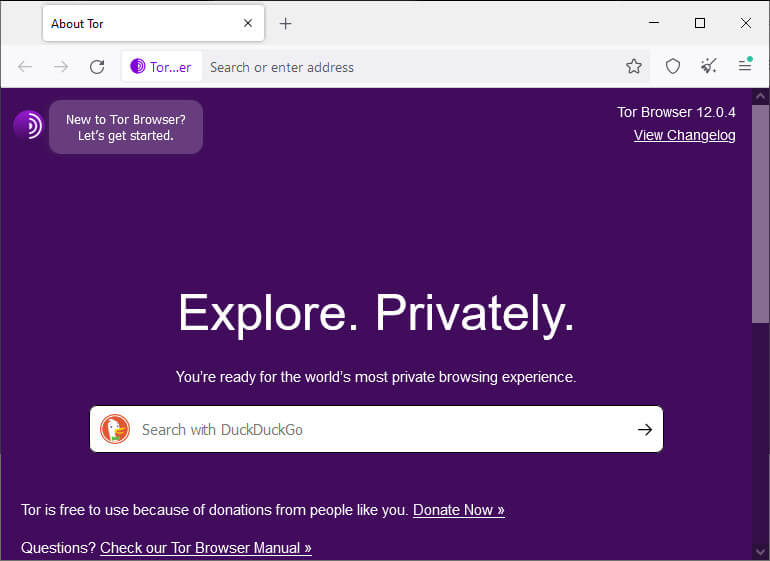
There’s a new browser out there that takes exactly this approach. It is a collaboration between Mullvad and the Tor project, and you can learn more about it in spot #6 on this list.
Be careful when adjusting the settings for the Tor browser, however, as this may compromise the browser’s built-in privacy and security features.
https://www.torproject.org/
4. Ungoogled Chromium browser

Ungoogled Chromium is an open source project to provide a Chromium browser, without the Google privacy issues:
ungoogled-chromium is Google Chromium, sans dependency on Google web services. It also features some tweaks to enhance privacy, control, and transparency (almost all of which require manual activation or enabling).
ungoogled-chromium retains the default Chromium experience as closely as possible. Unlike other Chromium forks that have their own visions of a web browser, ungoogled-chromium is essentially a drop-in replacement for Chromium.
UPDATE: Support for Ungoogled-Chromium has continued, but it has moved from its original github archive to the new archive linked below. It does require some technical skills to download this browser from the archives.
https://github.com/ungoogled-software/ungoogled-chromium
5. LibreWolf – A private and secure fork of Firefox

LibreWolf is a fork of Firefox that continues to grow in popularity. The project’s stated goals are to deliver a browser that is focused on privacy, security, and freedom. From the LibreWolf website:
LibreWolf is designed to increase protection against tracking and fingerprinting techniques, while also including a few security improvements. This is achieved through our privacy and security oriented settings and patches. LibreWolf also aims to remove all the telemetry, data collection and annoyances, as well as disabling anti-freedom features like DRM.
The website lists the main features of LibreWolf as:
- No Telemetry
- Private Search
- uBlock Origin pre-installed
- Enhanced Privacy
- Fast Updates
- Open Source code
LibreWolf is available for desktop operating systems, including Windows, Mac OS, Linux, and Open BSD. You can find installation instructions here.
One issue to keep in mind, however, is that there are no automatic updates. This means that you will need to manually update the browser, which is certainly a drawback to consider. Fortunately, LibreWolf frequently pushes these browser updates to the relevant archive managers, making it easier to update than it would otherwise be.
LibreWolf is always based on the latest version of Firefox. Updates usually come within three days from each upstream stable release, at times even the same day. Unless problems arise, we always try to release often and in a timely manner.
– LibreWolf FAQ section
This is definitely a browser to consider for those wanting more privacy and security on desktop operating systems.
https://librewolf.net/
6. Mullvad Browser – A privacy collaboration between Mullvad and Tor

When we talked about the Tor browser earlier in this article, we suggested using the Tor browser with the Tor network disabled and a quality VPN might be a better way to go than using the Tor network. We’re not the only people who feel this way. The Mullvad Browser is designed to do exactly this.
This privacy-focused web browser is a joint project between Mullvad VPN and the Tor Project. It incorporates the privacy benefits of the Tor browser such as tracker blocking and fingerprinting. But the Mullvad Browser isn’t designed to connect to the Tor network.
Instead of going through the Tor network, the Mullvad Browser is meant to be connected to the internet through a quality VPN. Obviously, the folks at Mullvad would love for you to use their browser with their VPN, but you don’t have to. In the image below I am using the Mullvad Browser to view this website through NordVPN.
This browser collaboration definitely has potential. To learn more about it, check out our recent article on this Mullvad – Tor project.
https://mullvad.net/en/browser
7. DuckDuckGo private browser (macOS, iOS, and Android)

The DuckDuckGo private browser is available for macOS as well as mobile devices running iOS or Android. It comes with lots of privacy-focused features by default. According to DuckDuckGo, their browser offers:
- Built-in tracking protection
- Encryption upgrades via Smarter Encryption technology
- Easy data management and clearing options
- Fast speeds
Issues with Microsoft trackers
One important thing to be aware of is that security researchers previously discovered that DuckDuckGo’s browser allowed Microsoft trackers. According to DuckDuckGo founder Gabriel Weinberg, this decision was based on a “confidential” agreement between DuckDuckGo and Microsoft.
Many people in the privacy community were outraged when the situation first came to light on Twitter here. There was clearly an element of hypocrisy going on here as we see DuckDuckGo castigate Google over the same practices. But last year, DuckDuckGo announced that they had reached an agreement to block Microsoft trackers.
Should you use DuckDuckGo’s privacy browser? I’d recommend that you consider some of the alternatives we recommend in this guide. That said, the changes DuckDuckGo has made to block the Microsoft trackers makes us much more comfortable with this browser. Ultimately, the choice is yours.
The DuckDuckGo private browser is available on both the Google Play and Apple stores.
8. Waterfox
Waterfox is a fork of Firefox that was maintained by just one person for many years. In February 2020, news broke that the developer of Waterfox sold out to a pay-per-click ad company called System1. However, in July 2023, news broke that Waterfox is once again independent:
I am happy to say that Waterfox is independent again. This change allows the community and myself to shape the browser’s future direction.
Waterfox Blog
Putting all that aside, Waterfox is a great option for those wanting Firefox with out-of-the-box privacy.
Waterfox website >>
Private browsers worth mentioning (but not necessarily recommended)
Here are a few private and secure browsers that didn’t make our recommended list but we think are still worth mentioning.
9. Bromite (Android)
Bromite is a Chromium-based browser for Android only (no desktop support). It comes with some great features by default, including ad blocking and various privacy enhancements.
Unfortunately, being a small project, Bromite suffers from infrequent updates. The last update was apparently in 2020!
Here are some highlights of this browser from the official Bromite website:
- The main goal is to provide a no-clutter browsing experience without privacy-invasive features and with the addition of a fast ad-blocking engine.
- Minimal UI changes are applied to help curbing the idea of “browser as an advertisement platform”.
- All patches are published under GNU/GPL v3 to enable other open source projects’ usage.
- Bromite is only available for Android Lollipop (v5.0, API level 21) and above.
Another cool feature I like with Bromite is that you can use custom ad block filters — learn more here. Bromite is under active development and remains a great browser for Android users.
https://www.bromite.org/
10. Pale Moon
Pale Moon is another open-source fork of Firefox, which aims for efficiency and customization. In testing out Pale Moon, it does offer different customization options, as well as support for older Firefox add-ons and its own lineup of add-ons. The design feels a bit dated, but it’s also not overly-cluttered and is lightweight and fast. Even more importantly, this secure browser is still being updated
Pale Moon is currently available on Windows and Linux, with other operating systems in development. Unlike other Firefox forks, Pale Moon runs on its own browser engine, Goanna, which is a fork of Gecko (used by Firefox). This is an older engine that was previously used by Firefox, but has long since been replaced. Many argue that this older codebase is a security vulnerability. And it’s also worth noting that the development team is very small compared to more popular browsers.
Pale Moon website >>
11. GNU IceCat
GNU IceCat is a fork of Firefox from the GNU free software project. IceCat is entirely “free software” as defined here and also includes various privacy add-ons and tweaks by default. Here are the privacy-protection features listed on the IceCat page:
- LibreJS
- HTTPS-Everywhere
- SpyBlock
- AboutIceCat
- Fingerprinting countermeasures
No updates – The big issue with GNU IceCat is that there do not appear to have been any updates since 2019. This can expose IceCat users to security vulnerabilities, which is why we are no longer recommending it.
GNU IceCat website >>
12. Iridium
Like Brave, Iridium is a secure browser that is based on Chromium and configured for more privacy by default. The following excerpt from Iridium’s website provides a good overview of this secure browser:
Iridium Browser is based on the Chromium code base. All modifications enhance the privacy of the user and make sure that the latest and best secure technologies are used. Automatic transmission of partial queries, keywords and metrics to central services is prevented and only occurs with the approval of the user. In addition, all our builds are reproducible and modifications are auditable, setting the project ahead of other secure browser providers.
Iridium is still being updated pretty frequently. However, it is not a widely-used browser, and there is no support for Android, iOS, or any other mobile devices.
Iridium browser website >>
Issues with other popular browsers
While some browsers claim to be secure against vulnerabilities, they might not be the best choice from a privacy perspective.
1. Google Chrome
Google Chrome is by far the most popular browser. Unfortunately, it’s a data collection tool as well and not a good choice for anyone looking for privacy.
You can safely assume that everything you do through Google Chrome is collected, saved to your data profile, and used for targeted advertising.
2. Microsoft Internet Explorer/Edge
Edge is a Microsoft product.
Just like with Windows, it’s a good idea to avoid Microsoft products, including the discontinued Internet Explorer and its replacement, called Edge. Both those browsers are closed-source, so there’s no telling what’s going on behind the scenes, and they’re also not the best for privacy reasons.
3. Opera browser
Opera started off as a decent browser, developed in Norway. However, in 2016 it was sold to a Chinese consortium for $600 million – and a lot has changed. The following information from Opera’s privacy policy explained how user data was collected and shared when you used Opera products. This was enough to turn us off to this browser:
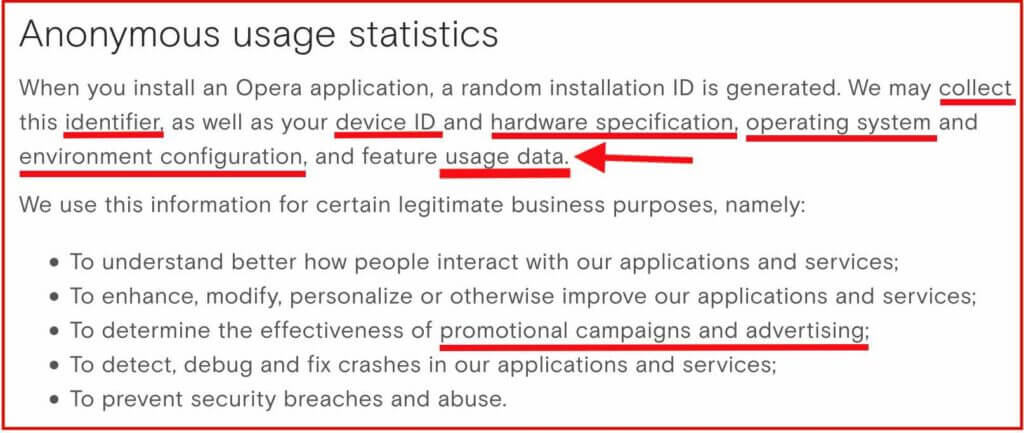
Opera also claims to offer a free VPN through the browser. However, as we covered in the Opera VPN review, it’s not really a VPN and does not offer full system-wide encryption. Additionally, your data is being collected when you use Opera browser and its “free VPN” feature.
4. Epic browser
Epic is a browser based on Chromium, created by “Hidden Reflex” which is based in India. Since 2014, Epic has been claiming they would open source the code, but it remains closed source today. What’s going on behind the scenes? How do they manage Chromium and remove invasive code? Who knows.
Just like with Opera VPN, Epic falsely claims to offer a “free VPN” through the browser, but this is not really true. The browser is merely routing traffic through a US proxy server. As we learned with Opera (and with many other “free proxy” services), proxies are often used for data collection (and they are often not secure). When reading the Epic privacy policy, we find that data from “video download and proxy services” is being collected.
One person who analyzed Epic found it to be connecting to Google on startup. This suggests that Epic is not, in fact, de-googled as it claims.
There are many better Chromium-based browsers to consider.
5. Safari browser
Safari is the default browser for macOS and iOS devices. Overall, Safari is not a horrible choice in terms of privacy and tracking protection – but it also cannot be recommended for a few reasons:
- Apple is a partner in the PRISM surveillance program
- Apple was caught “hoarding” Safari browsing history – even after it was deleted
- Apple was found to be collecting Safari history even when used in private mode
On a positive note, however, Apple does somewhat better with privacy than other large companies. The Safari browser blocks third-party cookies by default and also implements cross-site tracking protection.
6. Vivaldi browser
Vivaldi is a Chromium-based browser with source-code modifications that can be seen here. It is less popular than other browsers, with less active development than Firefox, for example.
Reading through their Privacy Policy, I did find some concerning information about data collection and the use of unique IDs:
When you install Vivaldi browser (“Vivaldi”), each installation profile is assigned a unique user ID that is stored on your computer. Vivaldi will send a message using HTTPS directly to our servers located in Iceland every 24 hours containing this ID, version, cpu architecture, screen resolution and time since last message. We anonymize the IP address of Vivaldi users by removing the last octet of the IP address from your Vivaldi client then we store the resolved approximate location after using a local geoip lookup. The purpose of this collection is to determine the total number of active users and their geographical distribution.
You can read more about Vivaldi here.
Secure and private browsers on mobile devices
Many of the recommended browsers above also offer versions for mobile users on iOS and Android.
With that being said, here are some good options for mobile users:
- Brave
- Bromite
- Firefox Focus
- DuckDuckGo
I also like using standard Firefox on mobile devices with customization and configurations for more privacy.
Browser privacy and compartmentalization
One problem that often comes with browser privacy and security is that people want to remain logged in to various accounts, while also browsing the web. But this is problematic. When you stay logged in to Gmail or Facebook, for example, their trackers can record your activity as you browse the web.
One potential solution to this problem is browser compartmentalization. This is when you use different web browsers for different online activities. For example:
- Browser #1 will only be used for accessing your online accounts that require a password. You can stay logged in with only this browser, and it won’t be used for general browsing.
- Browser #2 will only be used for web browsing, with various privacy configurations and no cookies or history being stored on the browser.
- Browser #3 could be completely locked down for maximum privacy and security.
You can also utilize different browsers, configured exactly the way you want, for various purposes, depending on your needs and threat model. The key is to keep the compartmentalization strict and not break the rules/uses for each browser.
Virtual machines – On the topic of compartmentalization, using virtual machines is also a good idea for both privacy and security. You can easily run Linux VMs through VirtualBox (FOSS) on your host computer.
Password managers – It should also be noted that storing your passwords in the browser may be risky depending on the browser you are using, especially since browsers may store passwords in cleartext. A better alternative would be to utilize a secure password manager. We have reviewed many popular options, including Bitwarden, Dashlane, LastPass, and more.
Browser add-ons for security and privacy
In addition to adjusting the settings within your browser, there are also a number of different add-ons or extensions you can install to improve your browser’s privacy and security.
Here are a few different options, but they may not all be supported by the browser you are using:
- uBlock Origin – This is one of the best browser-based ad blockers available that will also protect you against tracking.
- Cookie Autodelete – This will automatically delete cookies that are no longer needed from your browser.
- NoScript – NoScript allows you to customize exactly which scripts run on the websites you visit. Like uMatrix, this is for advanced users and requires lots of customization.
Warning: Be cautious about using third-party add-ons and browser extensions. There are many Chrome VPN extensions that are 100% free, but also very dangerous. Do your research first, since add-ons and extensions could function as spyware and data collection tools for third parties. This is especially true with free VPN services or browser proxy add-ons from questionable sources.
“Private” or “Incognito” browsing mode is NOT private (and why you need a VPN)
Many people falsely assume that using “private” or “incognito” mode in a browser actually provides some privacy. This is a false assumption.
Using “private” browsing mode only stops your browser from storing cookies, history, and passwords. But it doesn’t actually make you any more “private” to the outside world. Even when browsing in “private” or “incognito” mode, you are still exposed:
- Your internet provider can still see every site you visit. And note that internet providers are now forced to log web browsing activity of their customers and provide this data to authorities on request in many countries. In the United States, ISPs log everything and share the data with a huge network of third parties.
- Your real IP address and location remain exposed to all sites, ads, and trackers. This makes tracking and identification easy since your device has a unique IP address linked back to your identity through your internet service provider.
To easily solve these problems, we strongly recommend using a good VPN service. Using a VPN is simple. You just need to sign up for a VPN subscription, download the VPN app for your device, then connect to a VPN server and browse the web as normal. This offers many benefits:
- A VPN will securely encrypt your internet traffic, which prevents your ISP from seeing what you do online. (Your ISP will only see encrypted data, but not what you’re actually up to.)
- When you connect to a VPN server, the VPN server’s IP address and location will replace your real IP address and location. This allows you to appear to be anywhere in the world.
- A VPN will also allow you to access geo-restricted content, such as streaming Netflix with a VPN from anywhere in the world.
Below is a brief overview of our recommended VPNs. They have each come out on top in our testing for the respective VPN reviews.
- NordVPN: A fast, secure, audited VPN with advanced privacy features and a strict no-logs policy, based in Panama (with a 74% off coupon). See our NordVPN review here.
- Surfshark VPN: A no-logs VPN service with a large lineup of privacy and security features, based in The Netherlands. See the Surfshark VPN review.
- ExpressVPN – A fast, reliable, and secure VPN that also works well for streaming, but with above-average prices. See the ExpressVPN review for the pros and cons.
Short on money? There are also some good cheap VPNs that offer excellent features and performance, without breaking the bank. We also have detailed VPN comparisons. Our ExpressVPN vs NordVPN guide compares the top two providers.
Conclusion: Secure browsers and privacy in 2024
A well-configured secure browser is crucial for protecting your data if you want to browse the web with kind of privacy. But there are several good, secure browsers to choose from. So how do you do it?
Finding the best secure browser for you comes down to identifying the one that best fits your unique needs. Since this is a personal decision with subjective criteria, we can’t recommend a single option that is best for all use cases.
In truth, you need more than a secure browser that is configured to protect your privacy. To that browser you should add a quality VPN that will encrypt your traffic and hide your IP address.
You should also consider using a good ad blocker. Many ads include tracking code that companies can use to collect your browsing data and serve you targeted ads. If you aren’t blocking ads, your activities can be tracked by third-party advertising networks, which is not at all ideal.
Note: There are some VPNs that have built-in features to block ads and trackers. See our guide on VPN ad blocking for more info.
In terms of privacy, you may also want to protect yourself against browser or device fingerprinting and WebRTC browser leaks, which can expose your identity even when using a good VPN service.
This secure browser guide was last updated on May 15, 2024.

Only Brave browser has fingerprint randomization. Firefox, Librewolf etc. don’t come close to the fingerprint protection of Brave.
It’s the only browser on this page that’s actually private, and stops trackers from tracking you across different websites.
“https://brave.com/privacy-updates/3-fingerprint-randomization/”
If it wasn’t for Google funding, Firefox wouldn’t even exist anymore. Nobody is using that crappy browser.
I am.
I tried Brave but I couldn’t take all the crypto-scam-BS they’re peddling. Based on their past, it’s a shady product from a shady company. I don’t trust them. Went back to hardened Firefox in stead.
Brave browser has the BEST fingerprinting protection of any browser on here. Make no mistake, any browser on the list is better than the spybot/virus Google chrome & Edge.
But I think Brave is the best for privacy over Firefox,Waterfox… etc. It seems Brave’s development team is huge, so privacy & security is always up to date. Brave is only going to get better as time goes on.
Let’s Go Brave !!!
According to the latest news, they are removing some privacy features.
I sure am getting tired of hearing how supposedly great Brave browser is (it’s not). It’s simple, Brave is a chromium based browser, which is Google…more or less and Google sucks!
Any thoughts on Ghostery Private browser good or bad or anything similar to it.
https://www.ghostery.com/ghostery-private-browser
@Ned People talk good about Brave, because it IS good. Did you ever consider that? Brave has nothing to do with Google, so you better do some more research on that.
Brave proxies communication with Google servers (for safe browsing) so their users information is never sent to Google.
I trust Brave more that Ghostery not-private Browser, since they were caught selling info. to the trackers their users were trying to block.
“Brave has nothing to do with Google…”
Sorry, but that is not correct. Brave is built upon Chromium, and Chromium, open source or not, still belongs to Google. So Brave has nothing to do with Google as a corporation, but it has a lot to do with google as source code.
And anything made by google corporation is designed to collect users’ data.
Brave is touted as a privacy browser, but that is misleading. It protects you from fingerprinting, it protects you from tracking cookies, it protects you from social media trackers, it protects you from everything… except from google itself.
It’s right there on their website, in their privacy information. You are correct, it says that it proxies communication with google servers; but with that they are admitting that Brave does communicate with google servers.
Chromium is Google’s code. And a lot of that code is intended to connect to google. And if it connects to google, it’s spying on you. The fact that something called “Ungoogled Chromium” exists is proof of this. (And I wouldn’t trust “ungoogled” Chromium either. That is like saying “unleaded lead”. It’s still poisonous.)
This is just my opinion, but anyone using a Chromium based browser is fooling themself into thinking that their privacy is protected. It may be protected from many bad players, but not from the worse of them all.
Brave can send anything it wants to Google as long as Google can’t use it to ID me or my machine. I don’t see a problem with this position. Am I missing something? Do all Chrome variants claim to strip out telemetry and spying?
Me too, it reminds me of a cult. And you’re right: Brave is Chromium and Chromium is Google.
I just checked that spyware “Epic Browser”, and it is STILL closed-source !! Not to mention way out of date.
I hope nobody is using that junk browser.
@John Doe
I also found this on a internet forum: “https://forum.epicbrowser.com/viewtopic.php?id=407
Epic Spyware integrated into Firefox without user’s consent. Spying on Epic users was not enough, so they extended it to other browsers.”
That’s shady activity from a “privacy” browser. Epic Browser is talked about in this article, so i’m sure nobody is going to install a closed-source browser, and just assume it’s trustworthy.
@Ronnie If it’s closed-source it’s NOT for privacy. It’s probably a “honeypot” browser, where the developers are selling the users personal information for a profit.
Hidden Reflex also give NO explanation how they sustain the company, that’s a HUGE giveaway that something doesn’t add up.
Keep your hands off that browser.
@LA Dreamin’ Yeah, and Epic STILL connects to Google servers !!! Epic is a joke.
“https://medium.com/@xdotc/reasons-not-to-use-epic-privacy-browser-49a42c257791”
This website shows how bad it is. It’s funny how Hidden Reflex talk about how “honest” they are, while promoting their closed-source browser. They sell the data collected from their proxy just like Opera does. Both browsers are a total joke.
@LA Dreamin’ Honeypot is right. It’s the same garbage with free VPN’s, this Epic browser is epic spyware. There’s no excuse to use that browser, when there are open-source browsers that are transparent and actually protect their users privacy.
YouTube is accused of making computers with browsers equipped with adblockers work harder in hopes of pushing users to buy a subscription or to stop using them.
https://arstechnica.com/gadgets/2024/01/youtube-appears-to-be-reducing-video-and-site-performance-for-ad-block-users/
Cromite browser is a fork of Bromite browser. What do you think of Cromite?
https://www.cromite.org re-directs you to its github: https://github.com/uazo/cromite
@Giselle I tried using Cromite on my mobile phone a short time ago and testing the browser against sites, like Cover Your Tracks, shows the browser’s security and privacy functions are weak. I don’t think it is ready yet and suggest you use an alternative (like Brave).
@Mike Thanks for your input. I love Brave.
I’ve never heard of Cover Your Tracks. I just tried it out myself. The result was partial protection.
@Giselle You’re welcome. My hesitation to downloading or recommending browsers like Cromite is that it is seemingly another project done by well-meaning idealists who can later neglect their project.
A prime example is Bromite on which Cromite is based. Bromite was around for about 5 years and then one day its creator ended up abandoning it. This also happened with the Iridium browser too.
If you use Brave your web traffic is routed through Goggle’s servers; They know everything about you.
# ungoogled chromium
Hi RP Community,
Ungoogled Chromium recommends and extension that “If you want a comprehensive solution that handles installation and updates (of extensions for Ungoogled Chromium), see the chromium-web-store extension.” I am not sure how long this has been the case as I have just come across this.
https://ungoogled-software.github.io/ungoogled-chromium-wiki/faq#can-i-install-extensions-or-themes-from-the-chrome-webstore
The extension “NeverDecaf / chromium-web-store” About states, “Allows adding extensions from chrome web store on ungoogled-chromium. Also adds semi-automatic extension updating.”
https://github.com/NeverDecaf/chromium-web-store
I set this up yesterday – not too tricky and then downloaded the extensions I wanted directly from the Chrome Web Store and it worked seamlessly. (I only downloaded two as that’s all I wanted). When I click the Chromium Web Store extension it check for updates and advises me that “All extensions are up to date” I can’t report on the updates feature further as it is too soon.
The same developer (NeverDecaf ) has another extension that says, “Script for windows to keep ungoogled-chromium up to date.” I can’t find anywhere that Ungoogled Chromium recommends this extension (I can’t find that they refer to it at all) so I haven’t tried it. It appears to be a Python3 script with the Requests library. I don’t know how it is triggered but am guessing it uses Windows Task Scheduler.
What are the thoughts?
#LibreWolf
Hi RP Community,
Happy New Year to those who celebrate the day today!
LibreWolf appears to have auto updates for Windows. I found this when performing a Win 11 clean install.
When installing LibreWolf the setup exe gave me an option to include “LibreWolf WinUpdater”.
The LibreWolf docs say:
“If you want LibreWolf to be automatically updated (recommended), you can choose to install the LibreWolf WinUpdater, which is included in the installer.[BoBeX: “optionally”] You then can open the WinUpdater program and enable automatic updates by checking the box “Schedule a task for automatic update checks…”.
https://librewolf.net/installation/windows/
The updater app appears to be a PowerShell script, though the code is not shown when launched (It maybe Open Source but I haven’t searched this.
I have installed and run today, any problems I will add.
What are the thoughts?
@BoBeX I am a little confused. Are you saying LibreWolf now has automatic updates built-in or you have to place an extension or add-on to do it?
Hi @Mike,
I am saying LibreWolf has an automated process to update the browser for Windows.
No it is not built into the browser and is not an extension / add-on.
It appears to that LibreWolf has created a seperate application or .exe file that automates the update process; and this executable is added to the Windows Task Scheduler routines with a PowerShell script.
So it appears that LibreWolf has there own updater executable for their browser and that executable is triggered to run via Windows Task Scheduler (At log-in for example).
(It also appears that Mozilla schedules updates for Firefox with Task Scheduler too, but I don’t know if the activities are equivilent.)
What are the thoughts?
Automatic updates in Linux too. Just install it with the default package installer and the OS will keep it updated automatically.
Here’s another reason to avoid Chromium-based browsers. From NoScript’s website: https://noscript.net/usage/
(scroll down to the bottom)
Limitations on Chromium:
The API exposed by Chromium to browser extension is not as powerful and flexible as its Mozilla-developed counterpart. This is already true in Manifest V2, and gets much worse with Manifest V3, especially hurting privacy and security innovation. Therefore, even if NoScript is compatible with most browsers, some of its most advanced features are available only on Firefox and its derivatives, such as the Tor Browser.
In details, these are the current limitations imposed to NoScript by Chromium-based browsers such as Google Chrome, Edge or Vivaldi:
-The Injection Checker XSS filter is disabled because there’s no asynchronous blocking webRequest API.
-The Cross-tab Identity Leak Protection (TabGuard) is unavailable.
-The LAN protection works for numeric IPs but cannot resolve domain names (no DNS API).
Incognito should mean incognito.
https://arstechnica.com/tech-policy/2023/12/google-agrees-to-settle-in-chrome-incognito-mode-class-action-lawsuit/
Anyone can plainly see that Brave Browser is a tricksters browser, yes, it has decent privacy controls and it is quick (all chromium browsers are) but Brave Rewards…come on, really. Any browser that offers tokens/rewards is not on the up & up and dedicated to true privacy, its a sham! Sure, Firefox and like browsers are a little slower but I would trust them more than any of the chromium based browsers out there. Open your eyes people.
Firefox is funded by Google default search engine deal
@Brandon Brave is dependant on Google for their code, they ALSO had Google as their default search engine at one time. Brave also “phones home” to Google like all other chromium-based browsers do. It’s been said to be impossible to remove all Google code from chromium. (the source code is massive)
I don’t trust so-called “ungoogled chromium”, as far as i could throw it.
Brave Software Inc. is a for-profit company, that has a scam “ad program” that a REAL private browser would never dream of. Chromium-based browsers are the worst for privacy.
https://unixsheikh.com/articles/choose-your-browser-carefully.html
I agree with you about Brave and all Google derivate browsers.
@The Teflon Don Brave was deemed the most private browser in terms of phoning home in a study that was done on browser privacy 3 years ago (see link below). So what if Brave Tech is a for-profit company? Even Mozilla has had to cave in terms of benefiting from user data since they still have Firefox set to send diagnostic reports to them including a “suggestions from sponsors” feature that users have to switch off. Firefox’s Pocket addon also can be used to mine people’s data unless people do not use it or (better yet) remove it.
When it comes to Chromium source code, it is only when people use Chrome browser that their privacy is compromised, not when people use browsers based on Chorme source code (like Brave or Vivaldi). Brave’s cryptocurrency feature can be switched off and the browser has Brave Search set as its primary search engine when downloaded. So with all of this being said, which browser do you recommend people use?
https://www.zdnet.com/article/brave-deemed-most-private-browser-in-terms-of-phoning-home/
Staying private online is pretty simple: * Use a trustworthy VPN to hide your ip address/location. * Don’t use ANY web browser based on Chromium. There’s no such thing as a “private” chromium browser, since they ALL phone home to Google.
Brave has NO business being on this list, with their “AD” program garbage. Tor browser (a real private browser) doesn’t do that crap.
Firefox, Waterfox, Librewolf, Mullvad, and Tor browser. You want privacy, pick one of those browsers.
What about Pale Moon?
@vanp While the browser is not recommended by the people behind this website (please see above), this is a more detailed review. Pale Moon has a lot more negatives than positives. I personally do not recommend it but it is up to you which browser people, like yourself, choose. If you use Pale Moon, proceed with caution.
https://avoidthehack.com/pale-moon-browser-review
“Pale Moon has a lot more negatives than positives.”
That’s a matter of preference and opinion. The start.me stuff doesn’t bother me; I don’t use it. I’m not technical and generally don’t understand that stuff; it’s not a problem for me. The article states that Pale Moon is private and doesn’t do a lot of telemetry; sounds good to me.
“proceed with caution”
Not sure there’s a lot to be cautious about. I’ve been using Pale Moon since 2015; no major problems. There was a hack/security incident/something a few years ago. Can’t remember the details now, but it didn’t “make the earth move under my feet,” and the situation was corrected. I’m fine; thanks for your concern.
Also, concerning Pale Moon “is not recommended by the people behind this website ,” the only thing Sven says negative of possible substance is the age of the code base and related security concerns. Pale Moon is updated usually once a month, and security doesn’t seem to be any more a problem here than with any other browser. Again, I don’t see a problem–and haven’t had one.
I used Pale Moon for a few years. But unfortunately, the community turned toxic and the lead developer was extremely arrogant at the time. But it’s been a while, things may have changed.
Great article. Thank you for the information. Well done.
WHAT DO YOU THINK OF TEMPEST BROWSER? ITs NEW!
Seems Microsoft involved.
Privacy policy – https://tempest.com/privacy-policy
While slow load times for Firefox users who watch YouTube videos is nothing new, Google has every reason to do this in order to try to force people to accept watching ads.
https://9to5google.com/2023/11/21/youtube-firefox-slow-down-loading/
Here we go again! Google says they will roll out Manifest V3 that will restrict adblockers on their Chrome browser by June.
https://arstechnica.com/gadgets/2023/11/google-chrome-will-limit-ad-blockers-starting-june-2024/
Does anyone in this forum actually uses Chrome? And good job finding that article.
Which one you recommend?
I’ve been using Brave Search quite a bit lately.
If you take time to check out all the “secure private” browsers one thing stands out: the more secure browsers are mainly Firefox based, and the least secured are mainly chromium based. Am I the only one to notice this? Or maybe I’m missing something and maybe someone more tech savy can give me more insights on this.
As of now the ONLY browsers I use are Librewolf and Mullvad….I don’t even use Firefox anymore and Brave has issues that bothers me. As I said before there are not any 100% safe browsers, and actually I think the best you can get is around 85%.
@Ykcir Wrong. Only Brave has fingerprint randomization. Librewolf and Mullvad browsers have weak tracking protecton, since “hide in the crowd” doesn’t work. Brave is the best browser that’s private and secure against tracking, so i ONLY use Brave.
Brave browser is the ONLY browser I use and trust on this list. #1: Chromium’s code base is much more secure than Firefox’s. #2: Only Brave gives you fingerprint randomization. (the best solution)
Firefox, Librewolf, and Mullvad browsers all have “hide-in-the-crowd” fingerprint protection, but it is NOT effective. You will still stick out on websites that have little traffic, and can be tracked easily.
Brave browser is the best when it comes to security, and anonymity (when paired with a no-log vpn) and deserves the #1 spot on this list.
What’s the difference between fingerprint randomization and hide in the crowd fingerprint protection?
@Jessica I have tried looking for a comparison, but was unsuccessful. This article goes into fingerprint randomization which involves making one’s browser look different in order to confuse tracking and script programs between browsing sessions and websites. As I understand it, “hide in the crowd” involves a browser transmitting common browser characteristics.
https://www.zdnet.com/article/brave-to-generate-random-browser-fingerprints-to-preserve-user-privacy/
Thanks Mike. I think browsers that do fingerprint randomization also hide in the crowd. For example, Brave used to have its own Brave user agent but later changed to just Chrome.
No surprise! YouTube’s efforts at cracking down on adblockers is backfiring spectacularly.
https://www.androidauthority.com/youtube-ad-block-installs-3382289/
No Mike, both install and uninstall are increasing so YouTube’s effort didn’t misfire spectacularly. It’s actually people scrambling to test multiple ad blockers to see which one work on YouTube.
@Jessica I don’t think they’re scrambling since that shows they’ll end up using a different browser with a better adblockers. YouTube might impose stricter rules down the line that will probably result in their going after browsers next. A recent, interesting development indicates that YouTube may be in violation of EU privacy laws.
https://www.theverge.com/2023/11/7/23950513/youtube-ad-blocker-crackdown-privacy-advocates-eu
@Jessica “scrambling to test multiple ad blockers” Are you kidding me?? Just use BRAVE Browser. I have NEVER seen any Youtube ads (or any ad on any website) using Brave.
Everything is built into Brave, so i don’t have to “add” anything. The way it should be.
No kidding, it’s based on the article SerialThriller515. That’s why ad blockers are experiencing a surge of install and uninstall.
Brave is a good option for non technical users. Fanboy, who works on EasyList and Fanboy list also works for Brave. That being said, your ad blocking would act the same if you disable Brave Shield and install uBlock instead, should you want it.
This is not true, I have been trying out Brave Browser for over 6 month and it DOES NOT block all Youtube ads. Brave is a decent browser but it is nothing special or magical as the above is posting would have you believe. Your best shot is to try it out as I did and try to turn off as many of the settings as you can with in it.
If you still want to watch videos on YouTube, there are good ways to get around Google’s nonsense outlined in the comments section of this article.
https://arstechnica.com/google/2023/11/youtube-tries-to-kill-ad-blockers-in-push-for-ad-dollars-premium-subs/
What about Iceraven on Android? It seems a good Firefox-based browser.
At present updating regularly, and being ahead from Mull and Fennec f-droid, on FF version number.
Custom speed dial option is unlimited.
Has the option to clear add-on metadata.
More add-on support.
These are also not available in Mull and Fennec.
BUT-
Included one non FOSS library – Google mobile services.
If you feel okay with that con, then it’s a great alternative browser.
Be sure of hardening, following the guide provided by Sven here.
@A.B. Normal A post on the Reddit page for Iceraven doesn’t instill a lot of confidence the browser is trustworthy due to this disclaimer:
“No warranties or guarantees of security or updates or even stability!”
In other words, use this browser at your own risk. This tells me Iceraven is unstable and could be a threat to your privacy and security resulting from potentially infrequent or unstable updates. Consequently, I do not recommend using Iceraven.
Mullvad Browser is improved LibreWolf, if any need something similar for Android Mull Browser is the one.
Questionable activity by Brave:
https://alternativeto.net/news/2023/10/brave-browser-s-latest-update-installs-vpn-services-without-user-consent-on-windows/
@Quietme
Brave recognizes the issue and has said they will change it to install the browser’s VPN only with the user’s approval. However, existing installations can be manually removed.
https://www.androidcentral.com/apps-software/brave-browser-secretly-installing-vpn
Zoho has launched its Chromium browser, Ulaa on major platforms meanwhile Vivaldi has finally arrived on iOS.
@Jessica is Zoho’s browser open source? If not, I would suggest you not use it.
I use Vivaldi and i love it
If you use Firefox mobile, you may want to stop using it for the time being. I have come to find out that the browser’s engine, Geckoview, does not support site isolation or isolation process. Consequently, this makes Firefox mobile less secure than Chromium-based browsers. Firefox desktop, however, does have these features.
https://hacks.mozilla.org/2021/05/introducing-firefox-new-site-isolation-security-architecture/
https://bugzilla.mozilla.org/show_bug.cgi?id=1565196
I am looking to replace Ghostery Dawn browser (huge memory hog and a pain) and looking for some Firefox based browser alternatives. Are there any other good safe prviate browsers other than LibreWolf, that have the auto updating? Thanks.
I recommend Mullvad’s. It is based on Firefox’s source code.
https://mullvad.net/en/browser
A security flaw has been detected recently in most Chomium-based browsers (like Brave and Vivaldi) and a lot of applications. No indication as to which operating systems this applies to. Be on the look out for updates!
https://www.techradar.com/pro/security/huge-security-breach-affects-chrome-firefox-brave-edge-and-plenty-more-apps-besides-heres-what-you-need-to-know
Firefox as well.
@Bronco of course. However, other news sources I have read seem to make out that it is worse for Chromium browser users than Firefox.
Any info on Comdo’s Dragon and IceDragon Browsers? They’re Chromium based (most everything is now).
Hi Curios,
Dragon used to be called FireDragon and IceDragaon is still IceDragaon.
FireDragon was the Chromium offer and IceDragon is still the FF offer.
Why a security company is offering free browsers may rise eye-brows.
That they offer both Chromium and FF may point to there commercial interests, for compatibility with customer.
For me, I’d pick from the browsers above;
I use many of them.
LibreWolf is my favourite which I use for general browsing.
Good luck.
I stumbled upon your post and it piqued my interest. Comodo used to be recommended, particularly for their firewall. However, my personal favorites from the past were ZoneAlarm (before they adopted an adware model) and Private Firewall (compatible up to Windows 7).
When I visited Comodo’s website, I noticed they offered two options: Dragon and IceDragon, with the possibility to install them in a portable mode. You could choose between the Firefox version or the Chromium version.
However, it turned out to be misleading. Both installer files were, in fact, Chromium-based. There was no Firefox option. To opt for the portable mode, you had to make that selection at the beginning of the installation process and pay close attention to the portable checkbox.
I decided to test the installations in a virtual box, and the so-called portable version actually ended up writing itself into the Windows registry. I had to use Revo Uninstaller to completely remove it. Furthermore, there was no Firefox version as they claimed.
Based on my experience, I wouldn’t recommend using Comodo. Instead, I suggest considering a customized Firefox version or LibreWolf, which is also a solid choice.
Just for starters even if you modify and tweak Firefox DON’T forget to change about:config settings in DEVTOOLS! There is a s very long seemlngly unending list that Firefox can use to track and record everything you do while using rhis browaer. Yep check it!!!
I know I’m going to get a lot of hate, so I will be brief. “Friends” don’t let the friends who they care about use Brave browser. The heavily monetized promotion of crypton within the browser is telling.
what does it tell? –there is no obligation to use the crypto wallet
Waterfox is NOT tied to any corporations. Stop spreading lies.
Do you have a source for this claim? It was sold to System1. Did that change?
“Did that change?”
Uh, yeah.
https://www.waterfox.net/en-US/blog/a-new-chapter-for-waterfox/
Updated.
I tried using Cromite on my mobile phone recently and, while the layout is very similar to Bromite, testing the browser against sites, like Cover Your Tracks, shows the browser’s security and privacy functions are weak. Uazo has a way to go to get Cromite up to par. Until he does, I recommend using Brave.
It’s a pity that Firefox no longer upgrades itself after version 115x for Windows 7. Mozilla is following Microsoft. How shameful.
Are you still using Windows 7? If so, why?
Brave? No thanks. It advertises crypto and I find it’s intrusive. FF is not the best for sure for Android, but at least I find it trustworthy enough to sync my passwords et al across platforms.
@Tarzan much of the features in Brave a lot of people like yourself object to (like Crypto) can be shut off. You’re not required to use it, but would you please elaborate on what is it about Brave you find “intrusive”?
you should learn how to use an application firewall before you go around declaring what is “intrusive” and what is not
I am switching to Linux Ubuntu Win 11. I am woman getting close to 80 and it’s harder to keep up with all the major disasters without fighting my old Win 8.1 computer. Does anyone have any recommendations for security suites that can work with both Linux and IOS, that don’t cost a fortune, and bombard you with with scare threats that suggest you pay them more to another component to your service to save your behind. Thanks in advance
I’m the last person to be a computer expert, but I’m confused by some of your terminology. As far as I know, “Linux Ubuntu Win 11” is not an OS. Linux is. Win 11 is. They have nothing to do with each other. And what does iOS have to do with your issue?
Also, I don’t have experience with a lot of security products, but none I’ve used have cost a fortune or tried to scare or threaten me into anything. I think you’re pretty safe in that regard.
I think she might be confused because she heard that it is possible to install Linux on a virtual machine in Windows 11 and she also heard that Linux is more stable than Windows — but if you despise the instability of Windows system configurations (which is a fundamental design flaw that can never be fixed) then you want to replace Windows with Linux. She is putting the cart before the horse: Need to install Linux first, then she can go to the Ubuntu support forum for help with the rest, instead of posting off-topic comments in random places online.
Hi R,
Win 8.1 is not recommended, support was ended January 10, 2023 – you are in dangerous territory.
Your best first and immediate solution may be to upgrade to Win 10 which is currently supported until Oct 14, 2025.
https://support.microsoft.com/en-us/windows/upgrade-to-windows-10-faq-cce52341-7943-594e-72ce-e1cf00382445
In many cases it is best for Windows users to stick with Windows, Linux (Ubuntu) can be a steep learning curve.
If you do want to learn Linux, Ubuntu or an Ubuntu flavour should be considered;
Though you are probably best to just buy a new computer that comes with Win 11 pre-installed.
It doesn’t now work on “security suites” anymore – there isn’t one to be recommended.
You can pay for one if you want – but they won’t save you if you are running Win 8.1
Ensuring that your operating system and other software is updated to the latest version (or a supported version) is probably the most important thing, many softwares update automatically – but your operating system won’t automatically update to a knew version.
I don’t know who is “bombard” or bombarding you, but nobody should be “scaring” you:
– if it is Win 8.1, your operating system, and it is telling you to update – it is very correct;
– if it is other applications / programs / software on your computer – it is up to you whether you are satisfied whether they are installed on your system.
– if you are being contacted by phone or email it is likely a scam, you should independently find the contact details of the organisation and contact them directly.
When you say “major disasters”, and say this on this forum, I assume you mean data breaches.
Unfortunately, when the data is breached you can’t get it back.
You can only mitigate and I am not sure that is actually what you are saying.
Maybe this would be an informative start for you:
https://restoreprivacy.com/identity-theft-protection/
Kind regards,
What makes you believe the 80-year-old woman has a modern PC that qualifies for an upgrade to Windows 10? Furthermore, Windows 10 is no longer officially supported except for essential security updates. It will not have any new features or upgrades,
While this woman’s question is valid, her ignorance and gullibility is obvious.
The last OS they should use is Linux. It’s too complicated and has an aggressive learning curve for most people. Those who prefer Linux or use it, are in fact hard-wired differently than most.
My suggestion would be to buy a new or year old iPAD tablet. Not any Android. Ditch the old PC or buy a PC in a box like something from BeeJive for a few hundred USD on Amazon which will run Windows 10/11. They can use their existing monitor, assuming it’s HDMI.
Otherwise, the iPad is the best option and she can visit an Apple store and receive training how to use it.
Hi xEb0b, thank you for repeating what I just said in a less kind way.
Great suggestion about the tablet, I completely agree that this is a solution that should be considered.
After reading the leaked emails where Apple volunteered to spy on a presidential candidate and all of his contacts, I would say that Apple users should address their own ignorance & gullibility before they address it in others.
She mentioned Ubuntu, and that is not as complicated as fixing Windows registry issues that typically force a complete re-installation of the OS.
What’s wrong with Android? A Google-free Android distribution is more secure than anything else you suggested. She indicated that security is important, remember? And iOS has been hammered by two Israeli spyware firms that break its security every month. All it takes is one text message and you are owned. That is why Apple has to keep issuing these out-of-band security patches which it refuses to document. The truth would damage its reputation too much.
It might be an acceptable option, IF she wants a small screen, AND she can afford the device, AND she does not care about the privacy of herself or any of her contacts.
Sounds like someone who has never used it. And what is the learning curve for fixing registry problems that prevent apps from working??? –She will never learn that.
That will not address the system instability which she is complaining about, because M$ cannot fix this without breaking all of the apps… and then you might as well replace the OS anyway. Did you not read what she wrote?? Her primary objective is to eliminate Windows!
She is talking about the nag pop-ups in some cheesy Windows platform security app
I think you are a scammer.
@R.
See my reply to BoBeX.
@ xEb0X, we see scammers understand elderly people are moving to tablets, I bet you see this too.
Thanks for the intel.
my cookieblocked/tweaked firefox is allowing numerous cookies through – it is become unusable – It’s lying to users about blocking cookies – it’s not.
Metager is now unusable (without the recent too-quietly introduced paid-for key option) and ddg are no longer doing the job either.
I would pay for anonymity if a fully anon prepaid card option was offered.
I’m looking at the alternatives. But quietly introduced changes to the above have allowed many sites to harvest info about users who thought they were more secure. This combined with AI analytics has revealed much to the snoopyverse.
On Android it could be Cromite and Mull for me.
Absolutely supportable.
Mull is rapid to update consistently, for very long time. And the dev has other project of mobile OS, Mull is default browser on that.
From the background, history and business model situation, which is very, very important to maintain such project, Mull and Fennec F-droid (can be hardened like Mull following Sven’s guide here) seems, will continue.
Interestingly, Ice raven also updating frequently now, but have to prove consistency so far.
For cromite, as @Mike said logically before, considering Bromite’s history, it is difficult to depend on. That’s absolutely right-thinking.
On the other hand, because Bromite was open source, it was possible to continue the project as a fork by another. We may wish the same for Cromite in such disaster.
But forget about bookmark, account synchronization.
Here comes Brave, the most technologically advanced, stable fingerprint randomizer.
And it should be noted that in mobile, chromium based browser arguably more secure than FF or its forks, due to lack of fission implementation.
But I’ve seen, time to time, enabling Netguard’s network connection log, that Brave continuously connect with Facebook – on start, with every browsing, with every webpage.
I don’t know why RP mentors not mentioned or explained in support/against this.
As an ordinary user, I can’t handle this. So I have to run away.
I have made this point before, but wanted to do so again as I think this information needs to be highlighted from time-to-time. Has anyone noticed that there are fewer Gecko-based browsers but more Chrome-based ones? There is a good reason for this is and it is not what you may think.
After discussing browsers with a good friend of mine who has a background primarily in software development, during our talk he pointed out that Firefox’s source code is very complicated. According to my friend, Firefox’s source code is made up of half a dozen or more different languages and attempted to build a Firefox fork only to later sack the idea when he had to use compilers for every language in Firefox’s source code.
Browsers in and of itself are very difficult to construct and, in fairness, my friend has not reviewed Chromium source code yet. However, Chromium, on the other hand, may not have the complexity problem Gecko has as evidenced by the amount of Chromium browsers. Because browsers are difficult to construct it is small wonder there are only 3 types of browsers (Chromium, Blink, and WebKit). No doubt what my friend experienced is probably why Brendan Eich based Brave on Chromium rather than Gecko.
FWIW, after learning about this, I switched to Brave on my mobile devices and have dumped using Firefox altogether. It is not that Chrome or Google has a monopoly on browsers, as some people allege. Rather, it is very likely that because it is so complicated, Firefox’s source code makes development of browsers based on it very hard.
Consequently, more browsers are base don Chromium and, while Firefox is a great browser, it makes no sense that Mozilla seemingly would not want to address this problem with Firefox’s source code and make it easier to use.
Thank you.