Kape Technologies (formerly Crossrider) has now acquired four different VPN services and a collection of VPN “review” websites that rank Kape’s VPN holdings at the top of their recommendations. This report examines the history of Kape Technologies and its rapid expansion into the VPN industry.
Update: We have added new information and corrections to this report, while also publishing another article that closely examines the business of Kape and Crossrider.
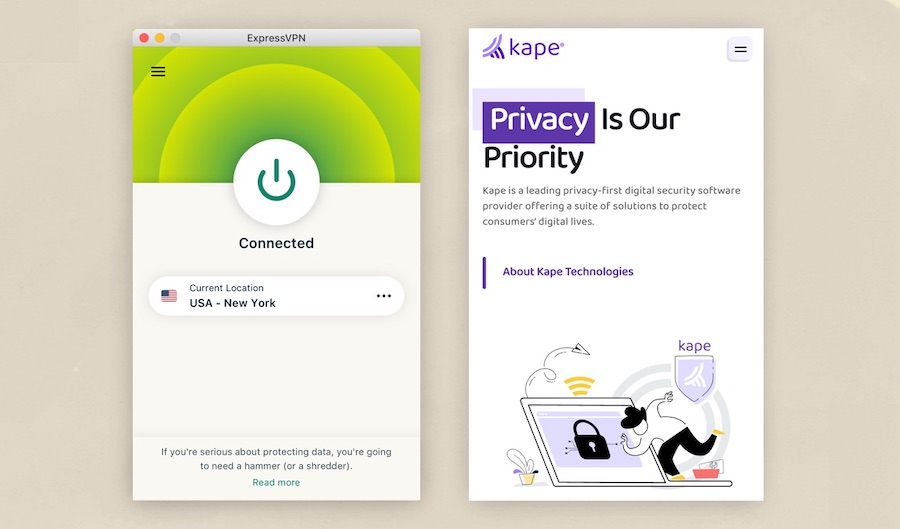
As is normal in the tech industry, the VPN world is undergoing some major changes and consolidation. The most recent example of this is with ExpressVPN, which announced plans this week to be acquired by Kape Technologies. While this may come as a surprise to some, it is nothing new in the industry. In fact, Kape has been on a VPN buying spree since 2017.
Unfortunately, many VPN users remain oblivious about the real owners of the VPN they are using as well as the history behind some of these entities. This is not because the owners are concealing anything, but rather, most “VPN review” websites fail to mention these important facts. This in-depth report intends to reveal the details for all to see. Here’s what we’ll cover:
- Kape (formerly Crossrider) was previously attributed to malware and adware, but it was not in fact responsible for creating the malware (this is addressed in detail here)
- The people behind Kape and Crossrider
- Crossrider begins purchasing VPN services, then changes name to Kape Technologies
- Kape purchases a collection of VPN “review” websites, then changes the rankings
- The future of Kape’s VPN ventures
To get a better understanding of the situation, we must first examine the history of Kape.
Kape (formerly Crossrider) created a cross-browser development platform
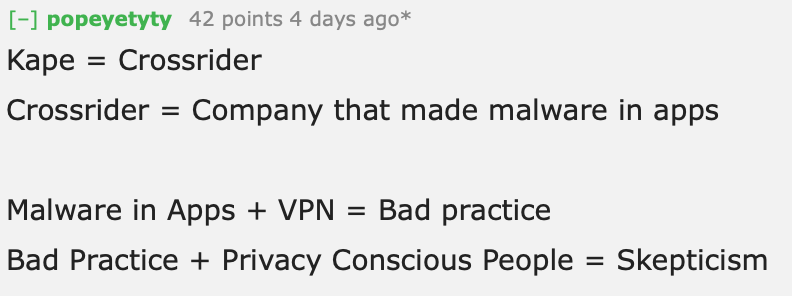
Before 2018, Kape Technologies was called Crossrider and it was often discussed in the malware and adware industry. You can still find numerous outlets that discussed Crossrider malware and adware infecting various devices, such as with Malwarebytes, Symatec, and Security Beulevard in 2019.
Below is an excerpt from a Malwarebytes article that discussed how Crossrider malware infected devices through software bundles:
Crossrider offers a highly configurable method for its clients to monetize their software. The common method to infect end-users is software bundlers. The installers usually resort to browser hijacking. Targeted browsers are Internet Explorer, Firefox, Chrome, and sometimes Opera. Crossrider not only targets Windows machines but Macs as well.
PUP.Optional.Crossrider installs are typically triggered by bundlers that offer software you might be interested in and combine them with adware or other monetizing methods.
While many outlets attributed this “Crossrider malware” to the people/business behind Crossrider itself, the truth is that Crossrider never created malware. Instead, the Crossrider platform was abused by third parties to spread malware and adware.
Crossrider offered monetization options that were used by ad injectors
We closely examined Crossrider’s history here and learned that it was a big player in the ad injection industry. In fact, there was even a research paper published by UC Berkeley, Google, and other co-authors who called out Crossrider’s business practices.
Crossrider is a mobile, desktop, and extension development platform that enables drop-in monetization via major ad injectors. Crossrider provides its affiliate ID to ad injectors while separately tracking kick-backs to developers. The other top affiliates listed in Table III are all cross-browser extensions and plugins that impact Chrome, Firefox, and Internet Explorer.
We summarized our investigation into Crossrider’s business history as follows:
- Crossrider created a development platform, which was used for many different purposes (both good and bad).
- Crossrider offered monetization options with its platform and was used by major ad injectors.
- Third parties also used Crossrider’s platform for malware distribution, but Crossrider was not the owner or creator of that malware.
- Crossrider completely shut down the program in 2016, changed out the company’s leadership, and pivoted to the privacy and security niche.
- In 2018, Crossrider changed its name to Kape Technologies.
Now that we’ve examined the business operations of Kape/Crossrider, let’s look at the leadership.
The people behind Kape and Crossrider
The main investor behind Kape is Teddy Sagi, an Israeli billionaire who previously spent time in jail for insider trading — but this happened all the way back in 1996, early in Sagi’s career. Sagi acquired Kape Technologies in 2012 and is an investor in many other industries.
Interestingly, Sagi is also named in the Panama Papers that detail a “rogue offshore financial industry.”
Another key figure behind Crossrider/Kape is Koby Menachemi. Forbes wrote a interesting article on Menachemi, detailing his ties to Israeli intelligence and cyber espionage.

Forbes noted the ties that Crossrider had to Israeli state surveillance entities:
A vast number of companies are affiliated with ad injectors, either packaging their tools or funnelling ads down to them. One of the biggest is Crossrider, the majority stake of which is held by billionaire Teddy Sagi, a serial entrepreneur and ex-con who was jailed for insider trading in the 1990s. His biggest money maker to date is gambling software developer Playtech. Co-founder and CEO Koby Menachemi was part of Unit 8200, where he was a developer for three years.
What went unnoticed, until now, is that most of the searchable organisations involved in this potentially dangerous business are based in Israel. They also happen to have links to the nation’s military and its top signals intelligence agency, the Israeli equivalent of the NSA or GCHQ: Unit 8200, which works out of the Israel Defense Forces (IDF).
It’s important to note, however, that Menachemi is no longer with Kape. And as we noted here, nearly the entire leadership of Crossrider left the company when Crossrider closed down its development platform. Furthermore, today, Kape is led by CEO Ido Ehrlichman, who was never part of Crossrider.
Interestingly, we also just learned that ExpressVPN’s CIO, Daniel Gericke, also has ties to state surveillance activities. According to Reuters, Gericke and two others are accused of “violating U.S. hacking laws and prohibitions on selling sensitive military technology” to the United Arab Emirates. According to reports, this “sensitive military technology” helped the UAE spy on dissidents and human rights activists.
“Hackers-for-hire and those who otherwise support such activities in violation of U.S. law should fully expect to be prosecuted for their criminal conduct,” Acting Assistant Attorney General Mark J. Lesko for the Justice Department’s National Security Division said in a statement.
Note: We have an article on this case as well:
High-Level ExpressVPN Executive Ensnared in Criminal Surveillance Operation
Make of this situation what you will. However, keep in mind that when you use a VPN, you are trusting the service to handle all of your internet traffic and not do anything questionable in the background.
Crossrider begins purchasing VPN services, then changes name to Kape Technologies
Now that you understand the background and leadership behind Kape Technologies, let’s examine its involvement in the VPN industry.
2017: Crossrider purchases CyberGhost VPN for $10 million
Crossrider’s first big VPN acquisition was in March 2017 when it purchased CyberGhost VPN for about $10 million. Originally founded in 2004, CyberGhost was a big player in the industry that experienced rapid growth before it was acquired.
2018: Crossrider changes name to “Kape”
Sometime in 2018, Crossrider decided to change its name to “Kape Technologies” as part of a rebranding effort. Ido Erlichman, the CEO of Kape, stated that the name change was an attempt to distance Kape from “past activities”:
The decision to rename the company, explains Erlichman was due to the strong association to the past activities of the company as well as the need to enhance the consumer facing brand for the business.
CyberGhost founder Robert Knapp also stated in a blog post that Crossrider was an “ad tech” company that did the “opposite” of what CyberGhost does (privacy and security):
While CyberGhost focused on privacy and security from day one, Crossrider started out as a company that distributed browser extensions and developed ad tech products. Quite the opposite of what we did.
2018: Kape purchases Zenmate VPN for $5 million
Not being content with just one VPN service, Kape then moved on to purchase Zenmate VPN, based in Germany, for around $5 million.
2019: Kape purchases Private Internet Access for $127 million
The next acquisition came in 2019 when Kape purchased Private Internet Access (PIA) for $127 million in cash and shares. At the time, PIA was a major player in the VPN industry with a substantial user base.
We wrote an article about it back in 2019 and described how many PIA users were upset about the acquisition and did not trust Kape. This screenshot from a PIA user on the PIA subreddit summarizes the sentiment of some users.
But the acquisitions were not over…
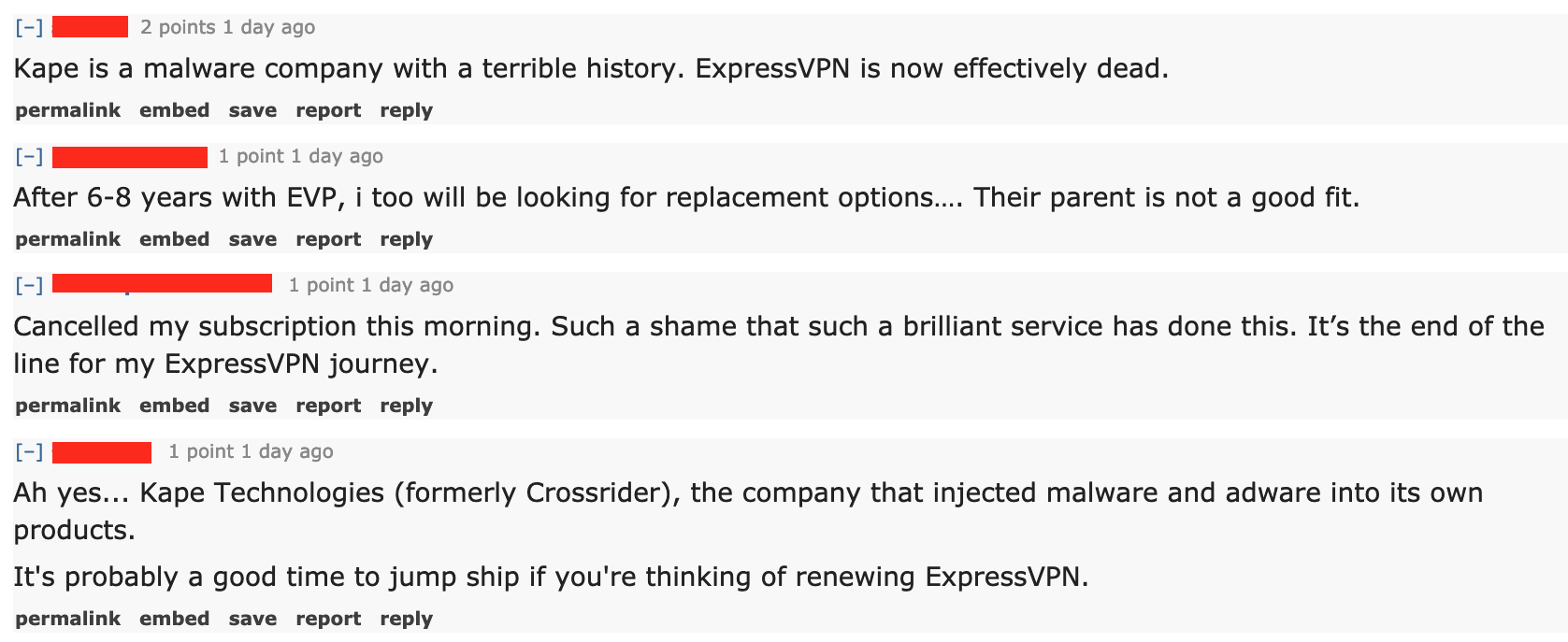
2021: Kape purchases ExpressVPN for $936 million
The latest major VPN acquisition we have for Kape Technologies is ExpressVPN, which it agreed to purchase for nearly $1 billion. This is by far the largest VPN acquisition to date and a major addition to Kape’s portfolio.
Watching this same story play out over and over again over the past four years is kind of like Groundhog Day. We generally find two reactions, with the user base being upset and the acquired VPN trying hard to calm everyone down.
- ExpressVPN users largely seem upset by the news.
- ExpressVPN issues canned statements and press releases along the lines of “Don’t be alarmed, everything is good!”
Let’s see how many more times this same story plays out with future VPN acquisitions.
Kape purchases a collection of VPN “review” websites for $149 million, then changes the rankings
In another twist to the plot, Kape Technologies also purchased a collection of VPN review websites in 2021. Yes, you got that right. The parent company that owns these VPNs now also owns a few high-profile websites that “review” and recommend VPNs to users around the world.
This is clearly a conflict of interest, but that goes without saying.
In May 2021, news broke that Kape had purchased a company called Webselenese. According to various press releases, we learned that Webselenese operates out of Israel and runs the websites vpnMentor.com and Wizcase.com. Collectively, these two websites have monthly search traffic of around 6.1 million visitors according to Ahrefs traffic analysis tool (September 2021).
Note that there may be other VPN review websites in Kape’s portfolio that we’re not aware of.
We also have a dedicated article on this topic:
These VPN “Review” Websites are Actually Owned by VPNs
Visiting vpnMentor’s homepage today, we find that the parent company’s three large VPN services all hold the top 3 spots in the rankings of the best VPNs for 2021.
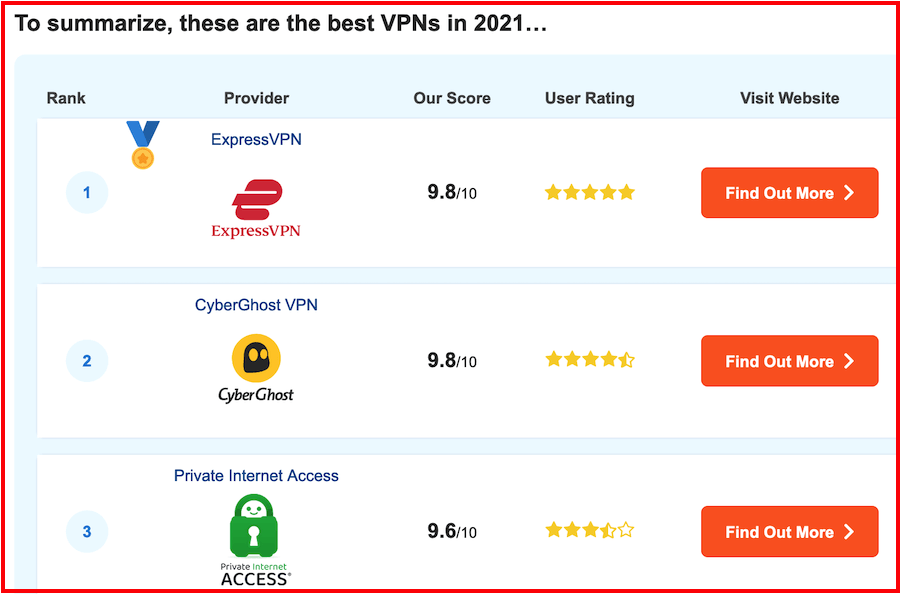
Wizcase.com: Similarly, we find the exact same top 3 rankings on Kape’s other website Wizcase.com.
Note: As we showed here, both vpnMentor and Wizcase had NordVPN and Surfshark in their top rankings just a few months ago. However, since Kape purchased these websites, we see big rankings changes, with all of the top 3 recommendations given to Kape’s own VPN companies. However, ExpressVPN has held the top #1 spot, even before the recent acquisition was announced. You can see the exact changes (before and after the Webselenese acquisition) documented in this article.
The future of Kape’s VPN ventures
If the past is an indication of the future, Kape will continue to expand its holdings in the cybsersecurity and VPN industry, which only continues to grow. Perhaps in the not-so-distant future, this conglomerate of VPNs and VPN review websites will be spun off and potentially sold as its own company.
In the meantime, there are now millions of VPN subscribers who fall under Kape’s ownership and control. Unfortunately, none of Kape’s VPNs that I have tested have been stand-out performers. The one exception would be ExpressVPN, but it too has fallen behind in the past year and dropped a few spots in our rankings, which are regularly updated to reflect industry news and our own test results.
Hopefully, this trend in consolidation will slow down as it gives the end-user fewer choices with independently-owned VPN services.

 ProtonMail Gives Up Logs on User, Then Scrubs Website of No IP Logging Claims
ProtonMail Gives Up Logs on User, Then Scrubs Website of No IP Logging Claims
Alex, I now notice that my first comment spelled the company name without the “m”, and should have been shown as “Unikmind”.
Kape is said to have been taken over by a company called Unikind, but it sounds to me as if that is being done in order to stealthily continue their operations under the cover of yet another name.
Kape Technologies Layoffs: How It Affects Your VPN in 2024 – Feb 12, 2024
https://www.cloudwards.net/kape-technologies-layoffs/
Kape also is said to have recently purchased PIA VPN.
“Kape is said to have been taken over by a company called Unikind”
Do you have a source for this comment?
Alex, this info is further down at the link I left, and the pertinent portion is quoted below:
“Kape Technologies Going Private
Another side to this story is the recent ownership changes that have taken place with Kape Technologies itself. Back in April, the majority shareholder (54.8%) in Kape Technologies, a holding company called Unikmind, offered to take the company private for the price of approximately $1.6 billion.
This offer got the sufficient support of at least 90% of shareholders, allowing Unikmind to squeeze out any remaining holdouts (if there were any) and acquire all the shares of the company.
This move allowed Unikmind to delist Kape Technologies from the London AIM stock exchange, making it a private company wholly owned and controlled by Unikmind. This can have benign reasons such as wanting greater flexibility and control over the direction of the business. However, it also means the company becomes less transparent as it no longer needs to meet the same reporting requirements.”
Kape Technologies Layoffs: How It Affects Your VPN in 2024 – Feb 12, 2024
https://www.cloudwards.net/kape-technologies-layoffs/
Thanks Flanders
Evil people exploiting people’s trust on something we put our confidence on it.
Thats why i never used Whatsapp and never will as i remember was infested with infected evil from evil people. Now im using surfshark and reading this im already concerned with this surfshark as most of the servers are located in vassal or 5 brothers states. Are SurfShark related with ExpressVPN at all?
No, Surfshark is not in the ExpressVPN/CyberGhost/PIA/Kape family.
Is there a trustworhty VPN review site in 2023? Any trustworthy VPNs out there?
Mullvad
yes, create own TOR exit….
And Proton VPN as well. Fast and secure.
Windscribe is a good choice too.
IVPN and AirVPN as well.
Free VPN “ZenMate-Best VPN for Chrome” collects the following:
Personally identifiable information:
For example: name, address, email address, age, or identification number
Authentication information:
For example: passwords, credentials, security question, or personal identification number (PIN)
Location:
For example: region, IP address, GPS coordinates, or information about things near the user’s device
Source: Chrome Web Store
[https://www.safetydetectives.com/] ,which Reviews Antivirus and VPN products is owned by Kape technologies as stated by their website.
You have heard of the central bank system? They have unlimited money to do whatever they want.
I wonder is it safe now to use these VPNs? Currently I have ExpressVPN and PandaVPN (from this company [http://pandavpnpro.com/]) at the same time in case sometimes anyone is not working… If it’s not as safe as before, I won’t continue the subscription.
On a positive note, ExpressVPN will continue to operate independently, last I heard, and it is performing very well right now. But go with services you trust.