The world is changing fast and your private data is at risk whenever you go online. Numerous entities, both public and private, are working hard to track, monitor, and record your digital activities. There are many reasons for this:
- Advertisers (including Google and Facebook) want to know everything about you, including your web browsing history, location data, contacts, and more. This makes it easier (and more profitable) to serve you targeted ads and influence your purchases.
- In an age of pandemics and lockdowns, many governments around the world are working hard to track movement and biometric data of their citizens.
- ISPs (internet service providers) are spying on their customers and feeding this data to various third parties, including advertisers and government agencies. In many countries, this is not only legal, but required. See for example in the United Kingdom (with the Investigatory Powers Act), United States (Senate Joint Resolution 34), and now also in Australia (mandatory data retention).
- The internet is also becoming less free due to censorship efforts and content blocking. Whether it is China, Germany, the UK, or the United States, various groups are working hard to censor content online.
But don’t get discouraged. Alternative technologies are experiencing a renaissance as awareness about these issues grows and people seek out solutions. Indeed, for all of the problems listed above, we find excellent solutions to give you more privacy, security, and freedom in your digital life. And that is the purpose of this guide: to give you solutions. Here’s what we’ll cover in this guide:
- Secure and privacy-focused browser
- Virtual Private Network
- Ad blocker
- Password manager
- Secure and encrypted messaging
- Private search engine
- Private email
- Operating system
- Antivirus software
- Conclusion
But before we begin, one key consideration is your threat model. How much privacy and security do you need given your unique situation and the adversaries you may face?
Most people today are seeking protection against online tracking by advertising networks as well as a higher level of privacy and security. Others, such as investigative journalists working with sensitive information, would likely need an even higher level of protection. So keep this in mind as you proceed. Everyone is unique in their approach to privacy and security; there is no one-size-fits-all solution.
So here’s what you need:
1. Secure and privacy-friendly browser
Everyone needs to be using a secure and privacy-friendly browser for three important reasons:
- Browsers have a large attack surface and can be compromised in many ways.
- By default, most browsers contain lots of private information, including your browsing history, usernames, passwords, and autofill information, such as your name, address, etc.
- Browsers can reveal lots of identifying information about your location, system settings, hardware, and much more to third parties.
Secure Browsers: Based on my own tests and experience, here are the most secure browsers that also respect your privacy:
- Brave – Brave is a chromium-based browser that is very privacy-focused right out of the box. By default, it will block ads and trackers, and it’s also customizable, fast, and has built-in protection against browser fingerprinting.
- Firefox (modified) – Firefox is a great browser for both privacy and security after doing some modifications. It is highly customizable to give you the level of security and privacy you desire, while also being compatible with many browser extensions. See our guide on how to modify Firefox for more privacy.
- Tor browser – The Tor browser is hardened version of Firefox that also utilizes the Tor network by default (but this can be disabled).
- Ungoogled Chromium – As the name suggests, Ungoogled Chromium is a stripped-down Chromium browser that has been “Ungoogled” for more privacy. Source code is here.
Of course, there are many browsers on the market and choosing the best one all comes down to your own needs and tastes. Chrome, Opera, Safari, and Vivaldi also get some attention, but they’re not the best choices from a privacy standpoint.
Worth mentioning: Don’t use a browser-based password manager, which will store your usernames and passwords in plaintext, thereby leaving them vulnerable to exploitation. Passwords saved in browsers are popular targets for hackers.
2. Virtual Private Network (VPN)
Using a good VPN (virtual private network) is one of the simplest and most effective ways to protect your privacy, secure your devices, and also access blocked content online. A VPN is a critical tool to be using, especially with internet service providers spying on their users.

Here are some of the problems that VPNs solve:
- ISP Spying – A VPN will encrypt and anonymize your internet connection. This makes your traffic completely unreadable to your ISP and other third parties.
- Blocked content – A VPN will let you easily get around blocked content and censorship. Simply connect to a VPN server in the region you need and access the website or stream as normal.
- IP and location tracking – Many websites and advertisers track users through their IP address. With a VPN, your IP address and location will be replaced by the VPN server’s IP address and location.
- Copyright issues – Torrenting and streaming media from third-party sources can come with some risk in the form of copyright issues. A VPN will anonymize your IP address and help keep you safe.
We’ve tested all of the popular VPN services and the results can really vary. Below are our current recommendations that are private, secure, fast, and reliable on many platforms.
- NordVPN – Best all-around VPN with secure apps for all major devices and very fast speeds (over 700 Mbps). It’s great for streaming and also offers security features (with a 69% off coupon).
- Surfshark – Best VPN for many devices (unlimited)
- ExpressVPN – Secure and reliable VPN service, but expensive
- Proton VPN – Simple, private VPN in Switzerland
We have other recommendations and providers in our guide on the best VPN services.
And if you are new to VPNs, we have a general VPN overview here, which covers all the important details.
3. Advertisement, tracker, and malware blocker
A good ad blocker is essential for privacy and security reasons. From a privacy perspective, it’s important to block ads because they also function as tracking by recording your online activity to create an intimate user profile. This data is then used for targeted ads and/or sold to other parties.
Ads are also risky from a security perspective because they can contain malicious code that can infect your device when a web page loads – no clicks required.
Effectively blocking all ads is the only way to go. Here are a few different options from our guide on the best ad blockers:
- Browser ad blocker extensions – Browser-based ad blocker extensions, such as uBlock Origin are quite popular, but they also come with some tradeoffs. Online ads may still be using up resources and tracking you, even if the ads are not being displayed. Choose your ad blocker carefully – some ad blockers, such as Ghostery and Adblock Plus will collect user data for profit and/or show you “approved” ads.
- Ad blocker apps – A dedicated app will most likely do a very good job blocking ads on your device. One popular and well-regarded option is AdGuard.
- VPN ad blocker – Another option is to use a VPN that offers an ad blocking feature (VPN ad blocker). I tested various options for the VPN ad blocker guide and found most to work well.
- Ad blocking on a router – Ad blocking on a router can be accomplished various ways – from using ad blocking DNS to loading custom filter lists onto your router.
- Pi-hole – Pi-hole is a network-wide ad blocker that functions as a DNS server and can be deployed in various ways. It is most often used on a Raspberry Pi, connected to your home router (but there are many other different setup options).
The best ad blocking setup will depend on your situation and needs. If you have numerous devices you use at home, setting up a network-wide ad blocker would be a good solution for blanket protection. uBlock Origin remains a popular option for browser-based ad blockers. However, I like NordVPN with the Threat Protection feature as a simple, all-in-one solution for VPN and ad-blocking.
4. Password manager
The topic of passwords is actually quite large, encompassing password strength, password management, and password storage. In this section we’ll focus on password management and storage. Many people store passwords directly in the web browser — but this can be risky.
A more secure method is to use a dedicated password manager app. And note that a dedicated password manager can also offer browser extensions that are convenient and secure. Here’s a screenshot of Bitwarden, which is one of our favorites:
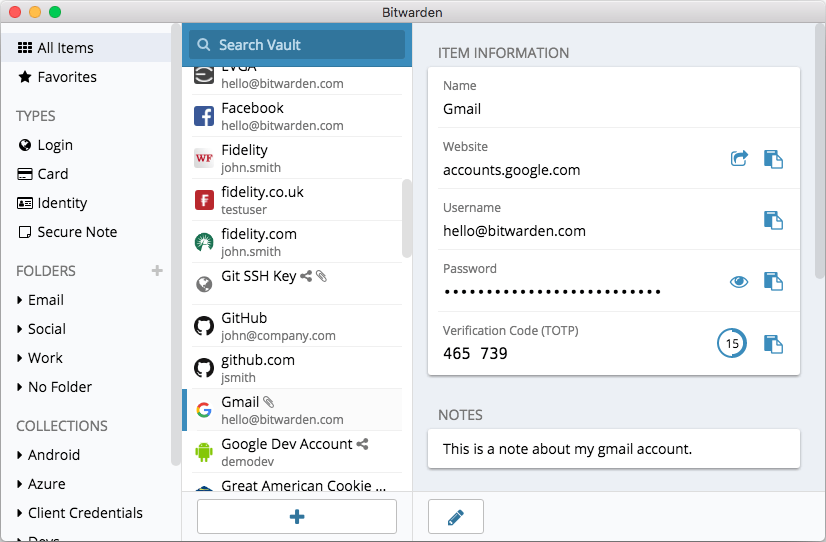
Here are the best password managers we have tested:
- NordPass – From the makers of NordVPN and NordLocker, NordPass is a secure, user-friendly password manager that has also passed a third-party audit. (See the NordPass review here.)
- Bitwarden – A free and open source password manager that is user-friendly and secure. (See our Bitwarden review.)
- 1Password – Another great option is 1Password, with many features and strong security standards for all types of devices (our 1Password review has more info).
- KeePassXC – As a locally-hosted password solution, KeePassXC differs from the others on our list. See the pros and cons of this password manager in our KeePass review.
Start using a good password manager today. See also our guide on how to create strong passwords.
5. Secure and encrypted messaging apps

Many people are turning to secure and encrypted messaging apps over concerns with privacy and security of other popular messengers. For example, WhatsApp collects and shares data from your phone with Facebook, the parent company of WhatsApp. If you find this concerning (and you should), then consider some of the secure alternatives below.
Additionally, with the inherent limitations of email, we recommend a secure messaging app for those wanting the most secure messaging platform possible. The secure messaging apps below utilize strong encryption standards and work well for teams or individual use on various operating systems and devices.
- Signal – This is probably the most popular secure messenger with a rapidly-growing user base. It is free, open source, and very secure. We really liked how it performed in our Signal review — but also noted some drawbacks, such as the need to use your phone number for verification.
- Wire – Based in Switzerland, Wire is another great option that is secure, user-friendly, and fully featured. While there is a free version for personal use, it is hard to find, as described in our Wire messenger review.
- Threema – This is one of the few paid encrypted messengers, but it’s only $3.09 for a lifetime license. Threema is also based in Switzerland and is open source. See our Threema review here.
- Telegram – Telegram is a very popular encrypted messaging app out of Russia, but it also is not encrypted by default. See the pros and cons in our Telegram review.
With all of the people abandoning WhatsApp and going over to Signal, there’s a better chance to connect with people you know on a secure platform. This trend kicked off early last year and we hope to see it continue!

Note: Also keep in mind that standard SMS text messages are not secure or private. They can be read by your phone service provider and are susceptible to man-in-the-middle attacks and also eavesdropping by Stingray devices. When privacy matters, use a good secure messaging app.
6. Private search engine
The big search engines (Google, Yahoo, Bing) record and track your searches, which helps them to build a user profile for their advertising partners.
Consider these privacy-friendly search engines instead:
- MetaGer – An open source metasearch engine with good features, based in Germany.
- Searx – A privacy-friendly and versatile metasearch engine that’s also open source.
- SwissCows – A zero-tracking private search engine based in Switzerland, hosted on secure Swiss infrastructure.
- Qwant – A private search engine based in France.
- DuckDuckGo – A private search engine based in the US.
- Mojeek – The only true search engine (rather than metasearch engine) that has its own crawler and index (based in the UK).
- YaCy – A decentralized, open source, peer-to-peer search engine.
There are also a few “private search engines” that are now owned by advertising companies. For example, Startpage was bought out by System1, a pay-per-click ad company. For more information, see our guide on private search engines.
7. Private email
Many of the popular email providers, such as Gmail, Yahoo, and iCloud are not good choices when it comes to privacy. Would you want random people having full access to your emails, collecting data for targeted ads, or passing the information on to third parties? This actually happens.
- Gmail gives third parties full access to emails and also tracks all of your purchases by reading the receipts in your inbox.
- Advertisers are allowed to scan Yahoo and AOL accounts to “identify and segment potential customers by picking up on contextual buying signals, and past purchases.”
- Yahoo was found to be scanning emails in real-time for US surveillance agencies.
And while Gmail remains the most popular service in the world, you pay with your privacy. Consequently, as awareness about these issues grows, many people are seeking alternatives to Gmail.
If you care about privacy and the security of your data, consider these secure email services. And if you want to learn more, check out these reviews:
- ProtonMail Review
- Tutanota Review
- Mailfence Review
- Mailbox.org Review
- Hushmail Review
- Posteo Review
- Fastmail Review
- Runbox Review
Note: We also have a guide on encrypting email.
8. Operating system
Consider using the free and open source Linux operating system. There are many different versions of the Linux operating system designed for different types of users:
- If you want the look and feel of Mac OS or Windows, check out Elementary OS.
- Ubuntu, Mint, and Debian are other popular options.
Tails is another privacy-focused operating system that can be run live on a USB drive, CD, or SD card.
Problems with Windows and Mac OS
Windows – The latest version of Windows (Windows 10) is a platform built for total surveillance – giving corporations and governments complete access to everything you do on your machine. Aside from data collection concerns, most malware targets Windows users – another serious drawback and security risk.
Mac OS – While Apple may be slightly better in terms of privacy, it too has problems. Just like Microsoft, Apple has configured its operating systems to collect vast amounts of your private data, whether it is browsing history through Safari, connection data, location services, and more.
9. Antivirus software
While not necessarily a “privacy” tool, using good antivirus software may be wise depending on your situation. The problem, however, is that many antivirus solutions abuse your privacy and may come with some invasive and “unwanted” additions.
Just like with sketchy free VPN services, free antivirus software can also be problematic. In testing eight popular free antivirus suites, Emsisoft discovered that seven of them were bundled with PUPs (potentially unwanted programs), which can be harmful and very annoying. Tip: avoid free antivirus software!
Another major issue is privacy. Many popular antivirus suites utilize invasive data collection, to include browsing history, “suspicious” files, metadata, and more. Carefully read through the privacy policy of your antivirus before installing.
Although Restore Privacy does not devote much attention to antivirus software, one solution that offers the highest levels of security while also respecting user privacy is Emsisoft. Another potentially good option, which is entirely FOSS, is Clam AV.
See also the antivirus privacy guide.
10. Data removal tools
As regular readers of this site know, personal data is valuable. In fact, there massive companies working behind the scenes to collect, compile, and sell your private data to third parties.
While there are good solutions for how to delete your digital footprint, there are also tools that take an active approach in targeting these data brokers. These types of tools and services are becoming increasingly popular, especially as the data collection problem becomes increasingly worse.
Here at RestorePrivacy, we will be testing and removing various data removal tools in the months ahead. So far, we have tested out Incogni, which is a service offered by Surfshark. Check out our full Incogni review here, or click the button below to learn more Incogni’s features and solutions to the never-ending data collection problem.
Conclusion: Restore your privacy and take control of your data in 2023
That’s all for now, although this guide will continue to be updated with more privacy tools and information.
If you have any feedback, tips, or suggestions based on privacy and security tools you are using, feel free to drop a comment below!
This article was last updated on January 18, 2024.

Information source,
[https://windowsxlite.com/]
[https://www.minitool.com/news/windows-x-lite-optimum-11-24h2.html]
Windows X-Lite Optimum 11 24H2 is a custom lite system based on Windows 11 version 24H2.
This release allows you to bypass TPM, Secure Boot, RAM, CPU, and storage checks, and bypass Microsoft’s forced account creation during setup/installation. So, it will give you a smoother experience on lower-spec machines.
How about some reality in your privacy insights to all the reviews you do. Update the privacy/security categories for any companies that are allowed to assign, transfer, and subcontract its rights and/or obligations under their Terms without any users notification. Making a special cautionary note in the review at least for your readers.
Another view, would be how much a business (vpn,email,browser,device) prospers from the actual purpose its in business of and offers users.
User base versus revenues minus overhead. How profitable is it? Is it selling users data to pad its profits? How is a users data used to make the business money buy the Terms you have to agree to by using it. Please include this research as well RP.
Thanks for your full reviews.
Oeprating system:
It shoud included BSD variant – OpenBsd, FreeBSD…
Apple may have to open its app store to alternatives resulting from the recent anti-trust court decision, but it is doing so placing numerous restrictions and fees in order for them to operate.
https://money.usnews.com/investing/news/articles/2024-01-24/apple-plans-new-fees-restrictions-for-downloads-outside-app-store-wsj
For people wanting to buy a smartwatch but are concerned about Google’s and Apple’s data mining (yes, Apple does it too), there are privacy-oriented alternatives. One other brand not listed whose products tend to rate very well with Mozilla’s “Privacy Not Included” list is Garmin.
https://howchoo.com/technology/best-smartwatch-for-privacy-and-security/
There are a number of Black Friday discounts on a variety of privacy-oriented products. Some even extend through Cyber Monday.
https://youtu.be/psl0SqT3INc?feature=shared
Apple is working on unlocking their mobile devices in order to accommodate sideloading which could mean new apps and repositories similar to Android.
https://9to5mac.com/2023/11/18/apple-head-of-security-iphone-app-sideloading/
Privacy protections are almost non-existent when it comes to automobiles.
https://arstechnica.com/cars/2023/09/connected-cars-are-a-privacy-nightmare-mozilla-foundation-says/
Mozilla compiled a list of the privacy practices of the major car brands.
https://foundation.mozilla.org/en/blog/privacy-nightmare-on-wheels-every-car-brand-reviewed-by-mozilla-including-ford-volkswagen-and-toyota-flunks-privacy-test/
This group has some ideas on what you can do.
https://privacy4cars.com/
Hi Sven,
I just bartely got a brand-new Macbook Pro 16-inch laptop for school, which comes with the M2 chip. I also just got a brand new iPhone 14. I installed MacOS Ventura, but I’m wondering if I should switch to Linux to better protect my privacy? Or does that just defeat the purpose of having a Macbook Pro in the first place?
Hey Spencer!
Brand new Apple gear… wow! IMO, stick with the Mac OS and do whatever you can to lock it down for security and privacy. Sven has many helpful articles in different categories on how to do that. A decent VPN for starters is a must
The iPhone, on the other hand, (and any other mainstream cells) are built for data collection = not privacy friendly.
BTW, there are very few current Linux OSes (distros) that are designed for an M2 chip. I have Linux, i.e. Mint, MX and Sparky — see https://distrowatch.com/ — running on 3 older iMacs because I could not install newer Mac OSes on them. Work great but you gotta pick and choose = pretty steep learning curve all round.
Good luck with your schooling! Cheers, George
Hi Sven,
Tools like LittleSnitch (for Mac) or Glasswire (for Windows) are not mentioned. With the great amount of control they give over incoming and outgoing connections, they can be a useful tool to improve privacy&security. Is there a reason they are not mentioned here?
Good points John, I think they were on here at one point, and should be added back.
With Little Snitch Mini there is now a version available that is less cumbersome to set up than the full version, and with LuLu from Objective-See there is a free & open source tool with similar features.
Got another suggestion for Restore Privacy – Sven.
Add to your ‘Restore Privacy Checklist’ the inclusion of an antivirus on the device.
To the ‘Privacy and Security Essentials’ links could have information about nowadays phishing URL’s or malware download link’s especially with technology advancing faster than follow-up security patches roll out. The more mainstream the technology has become, the more attractive it has become to threat actors. The same accessibility that makes the QR code a useful tool also makes it an effective vector for phishing and malware delivery. Quick Response (QR) codes are two-dimensional barcodes used to enable users to access data or web-based resources (URLs).
QR codes -‘ Quick Response codes’ are nothing new, having first been devised in 1994 as a way of tracking car parts during manufacturing. However, smartphones and mobile connectivity have caught up to the QR codes’ potential, and the digital tiles now provide handy shortcuts for consumers to complete actions or get more information. They are commonplace on travel and event tickets in many countries, with restaurant menus and advertisements being other popular uses. And of surges, anyone who has done a COVID test will have noticed a QR code as an alternative to typing out the long string of ID numbers.
There are several factors that make QR codes an appealing attack tool. Codes can be used in emails as a substitute for URL links or attached files. In normal use, this will automatically redirect the recipient to a specified web page or interact with a specialized device or application. Attackers can exploit this trait to disguise a phishing URL or malware download link that might otherwise be picked up by email gateways or other anti-phishing cybersecurity solutions.
But the QR code itself is not malicious and there is nothing to give one set of pixelated squares away as a potential threat. This, combined with our growing familiarity with the technology, means many users will simply wave through a QR code where they might have been suspicious of a normal link.
Added to this, the codes are usually intended to be scanned by a smartphone, which means a user that opened an email on their desktop endpoint will be jumping devices. This will often mean switching to a less secure personal device, particularly in the age of remote working.
https://www.emsisoft.com/en/blog/32351/how-to-prevent-phishing-attacks/
https://portswigger.net/daily-swig/qr-code-security-best-approaches-to-using-the-technology-safely-and-securely
https://www.techradar.com/features/do-not-overlook-the-security-risk-posed-by-qr-codes
Will AI (artificial imitation) someday allow people to lay on a beach somewhere while it runs their business and brings in record profits?
I have recently learned how the reCAPTCHA test works:
https://www.cloudflare.com/en-gb/learning/bots/how-captchas-work/
If it is true that “The reCAPTCHA also may assess the cookies stored by the browser on a user device and the device’s history in order to tell if the user is likely to be a bot” and that “The latest versions of reCAPTCHA are able to take a holistic look at a user’s behavior and history of interacting with content on the Internet”, then it seems that there are some privacy issues here… How to protect from that?
Thank you!
What about smartphones?
Hi
As I know, on RP, there are (at least) two articles, part of which address your question.
One is “Browser Fingerprinting Protection: How to Stay Private”.
https://restoreprivacy.com/browser-fingerprinting/
The other is “Controlling Communication Channels is Crucial for Privacy”.
https://restoreprivacy.com/controlling-communication-channels/
You might look into these two.
Hi Sven Sir,
Online Privacy is a struggle and a fight which we are loosing every day. With each passing day it is becoming more and more difficult to restore privacy. One has to become a digital hermit and a digital vagabond to get some sort of online privacy and misses out on so much. Amazon, Google Products, Microsoft Products etc are not private but one has to use them in certain situations and there is no other option, like for example Microsoft Office. Or Google Maps. And now there is Chat GPT. Data is monitized in this age of information and data is power. People aren’t rich enough to pay for all services and so this is what we are left with. Big Tech is a necessary evil as Open Source communities are not resourceful and Governments can’t produce this kind of technology so rapidly, we will be years behind. Online security from fraud and hack is still a goal which is feasible and can be persued. But online privacy is very very difficult.
Digital world emerges out of real life world and is influenced by its problems. In an ideal society free from exploitation we can have a great digital life. But otherwise the area of work is real world. VPN, Adblocker etc are not the fundamental solution. Just a kind of plaster on an already fractured arm.
Hi Sven,
Reading this article on RP motivates me to look into Linux. And, I find that Ubuntu did sell users’ information to Amazon. So, I guess, although Ubuntu is more private than windows and Mac OS, some other Linux distros can do better.
For more details, might consult the following article by Richard Stallman, a founder and leader of the free software movement.
https://www.gnu.org/philosophy/ubuntu-spyware.en.html
Best,
CP
As a BSD user I recommended you one of them: FreeBSD, OpenBSD…
Sven Sir Please review Malloc VPN: Privacy & Security available for Android and iPhone. It is much more than a VPN and comes with very powerful and unique features to protect user privacy and security.
[https://www.mallocprivacy.com/]
The developers behind this service are very passionate about security and privacy.
Sven
Could you move https://restoreprivacy.com/browser-fingerprinting/
To you Page Header TOOLS Tab across the top in the dropdown listings? It’s hard to locate now really as it located presently.
Thanks
Yep, I just added it Kathy, thanks.
Thank you Sir. Your proving the site more valuable as you make things easier to find, understanding them for resolve or of a red flag to the privacy issues out there in the web.
Oh, maybe you can work on this demise I’m finding about/with your site and the wonderful comments your fans have left here over time. Yes, if you take the long route through your sites map it’s possible still? https://restoreprivacy.com/sitemap/
The issue of demise is – if you can remember the commenting authors name of something that was relevant to you. YOU Can’t Presently SEARCH for that NAME given for the comment(s) your site had posted from this commenting author. Why?
End result is once that page (with relevant comment) is push away to add room in present day comments. It’s dead for easy recall here – why?
I elect for you to have an easy search for a comments author by name, first – in your tabs search functions, second – in the sites archives. Please sir : )
If I have NordVPN this mean I have the AdBlock feature so, knowing this: Can I delete all browser extensions and be safe?
Thanks to all.
Sven Sir,
There are things which should be added to this article under ‘Other security and privacy practices’ which should include email compartmentalization and using different email for different services and different category of services and keeping banking email separate private, using encrypted cloud storage or one from a privacy respecting provider, secure and privacy friendly note taking apps, network and bandwidth monitors like Glasswire, being careful and showing good judgement when downloading apps and software on Smartphone and PC and preferring web apps, using email aliases and temporary throwaway emails, Keeping system and apps up to date, Securing Home Router and home Network, Being careful with phone number sharing as it serves as a unique identifier, avoiding personal assistants and chat bots, Using private alternative to Microsoft Office, Private Navigation Apps like Osmand and Sygic, Taking care of Smartphone Bluetooth and Wifi Connection when in Public, and finally ensure physical security of devices we use.
Thank you
Sven Sir,
1. I don’t use Data removal tools as it adds to extra cost and my data is not with data brokers as I have been careful from the beginning.
2. I use WhatsApp as the very few people whom I communicate are on WhatsApp and no use going for Signal or Session Messengers.
3. I use Ads free Microsoft Outlook Premium which comes with additional security features. Considering the nature of email protocols where the above options make you stand out without adding much to privacy and lesser security than Gmail and Outlook, I believe it is better to use Outlook Premium and also compartmentalize emails for various types of accounts.
4. I use Windows OS on HP Laptop and Android from Samsung. I need these for features which are not present on Linux and privacy is tricky on a smartphone. Still I do get ample privacy by using high quality and trustworthy apps and services and reduce data collection on these platforms via settings.
5. I use Neeva Premium as Private Search Engine and it works for me. Ads free and high quality results.
So OS, Email, Messenger are what I am using based on my convenience.
Corrections:
1. Wickr Me, the free encrypted messaging app owned by Amazon Web Services, is shutting down on December 31st, 2023
2. Session Messenger should be included in the list secure messenger options
3. Number 10 After Antivirus is not conclusion but Data removal tools.
PASS THIS ALONG-
We recently became aware of an incident in which a code-signing certificate, fraudulently claiming to be from Emsisoft, was employed in a targeted attack against one of our customers.
The attack failed – our product detected and blocked it – but we are issuing this alert so that both our customers and users of other products are aware of the tactics that were used in this case. We strongly recommend that users of Emsisoft products set an administrator password.