
ESET researchers have discovered a new campaign attributed to the Bahamut APT (advanced persistent threat), which uses a VPN app as a lure to infect targets with Android spyware.
Bahamut is a cyberespionage threat group that has been operational since 2017, targeting primarily the Middle East and South Asia.
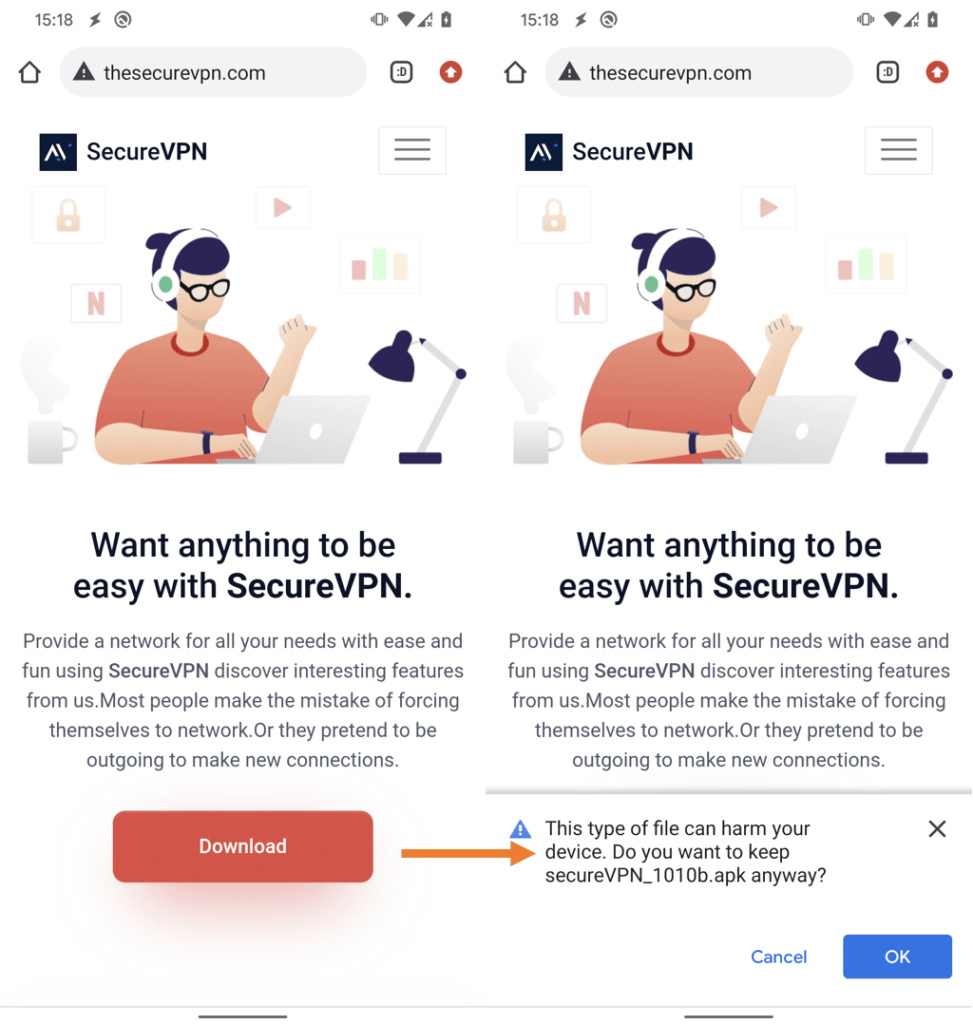
The VPN apps used by the Bahamut hackers are trojanized versions of SoftVPN and OpenVPN, distributed through a fake SecureVPN site where victims end up after clicking on links embedded in phishing emails.
ESET
The downloaded APK files install the usable VPN application, but they also infect the devices with spyware capable of exfiltrating SMS, tracking location, and recording phone calls.
Additionally, the spyware can intercept all communications on otherwise secure instant messaging apps like Signal, Viber, WhatsApp, Telegram, and Messenger.
VPN Spyware Details
ESET’s analysts were able to sample eight different versions of the spyware, following a progressive version numbering that indicates gradual development.
Earlier versions were based on SoftVPN, while later versions are based on the legitimate open-source application OpenVPN, which has over 10 million downloads on Google Play.
Likely, the threat actor was forced to pick up the latter when SoftVPN stopped working and made server connectivity unreliable, threatening to compromise the operation.
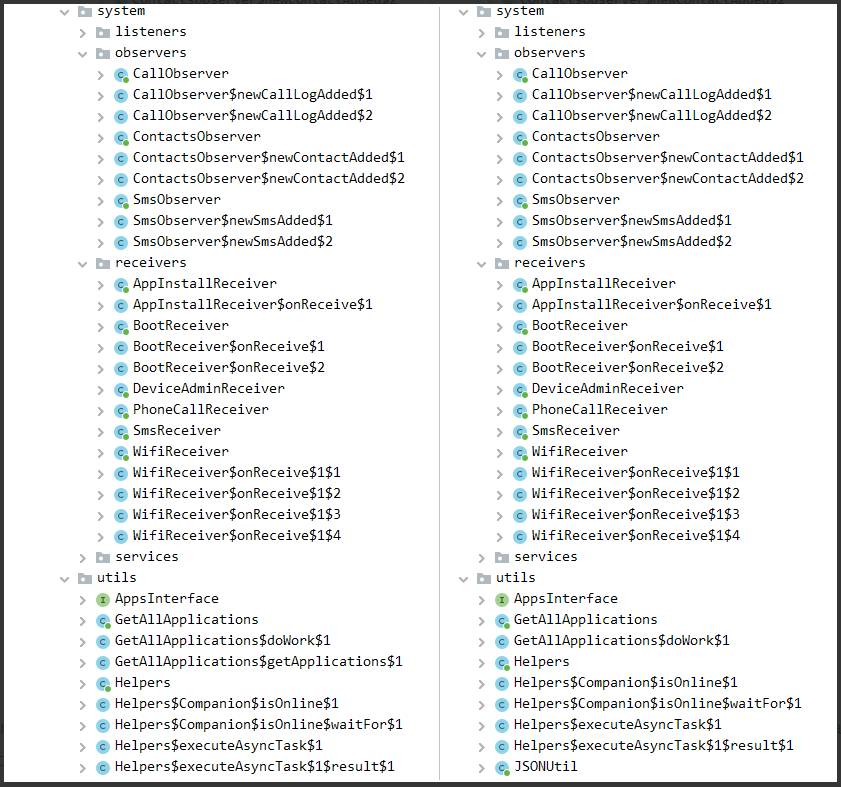
Both contain the same malicious code, with only minor refactoring and optimizations that don’t impact the spyware’s core functionality.
The spyware will only activate if a valid key is provided from the server side, meaning that the threat actors have validated the target and enabled the app remotely.
When activated, the app can steal the following data:
- contacts
- SMS messages
- call logs
- a list of installed apps
- device location
- device accounts
- device info (type of internet connection, IMEI, IP, SIM serial number)
- recorded phone calls
- a list of files on external storage
The fake VPN app also requests access to Accessibility services upon installation, which it abuses to perform screen actions and view the content of secure screens, normally hidden from remote connections.
This enables the spyware to steal notes from SafeNotes, Messenger, Viber, Signal, WhatsApp, Telegram, WeChat, and Conion.
Stolen data is stored locally on a database created by the malicious app and sent to the command and control server when the threat actors choose.
ESET attributes the bogus SecureVPN campaign to Bahamut after comparing the code class structure and SQL query with Bahamut malware seen in past campaigns and noticing extensive similarities.
ESET
While this threat group has been predominately targeting users in South Asia, it doesn’t mean that it’s unlikely to focus on other parts of the world if its espionage goals change.
Free VPN apps are notoriously risky. A landmark study examining 270 free Android VPN apps found that 38% contained malware and roughly 82% of the apps attempted to access the user’s sensitive data. While there are reputable free VPNs that operate on the freemium business model, such as with Proton VPN and Atlas VPN, it is still wise to proceed with caution, especially given the amount of trust that one places in a VPN service.
Users are advised to be cautious of messages asking them to download a VPN app, and always check the reputation of VPN vendors before installing anything that can snoop on their network traffic.

 Europe Reacts to Meta’s Chaotic User Data Management
Europe Reacts to Meta’s Chaotic User Data Management
More and more people are feeling the need to use a VPN for a variety of reasons but not everyone can afford a VPN subscription and so millions resort to using a free VPN. This makes free VPN market for advertisers and data collectors as well as malicious actors very alluring. In fact there have been instances where a data breach at a free VPN service exposed sensitive information of millions of users.
It is high time Google and Apple take stringent measures for quality control of free VPN applications on their app stores.
There are so many free VPN applications that collect and harvest user data like Thunder VPN and Hola VPN. Many such VPNs are Chinese honeypots and we only know the tip of the iceberg. Data collection is a massive industry. Some credible sources and users based in China confirm heavy Chinese surveillance machinary within their home country and use of Chinese apps like their free VPN apps and apps like Tik tok for extensive data collection and surveillance of users outside China. This is state sponsored surveillance of innocent population which has nothing to do with the state and such data collection has geopolitical implications specially in these turbulent times.
Free VPN’s I recommend are:
Tunnelbear
Adguard VPN
Proton VPN
Atlas VPN
Some other not so good options,
Windscribe
Hide.me
Hotspot shield and other siblings VPNs
VPNs I do not recommend:
All the rest of free VPNs specially those which are not reputed and trusted names as about 75 percent of free VPNs are Chinese honeypots.
VPN is a necessary tool for preventing third party and even second party from knowing the geolocation and ip address of the user and prevents tracking by ip address which is very significant. It also confuses trackers by sharing IP address with other users and hides monitoring of your online activity by ISP and thus from not so reliable Government. VPN is a great addition and supplement to existing HTTPS security.
Unblocking is a plus.
VPN helps mitigate privacy invasion, tracking and surveillance and that is why dictatorial regimes and partially democratic republics like India hate VPNs.
I agree.
Societies should have a basic set of freedoms, including free access to the internet.
I personally think Calyx VPN/Riseup VPN could be added to the list of good free VPNS.