
ProtonMail is widely touted as the most secure and private email service in the world. Having tested and reviewed the service ourselves, we have been recommending ProtonMail for years. However, the company behind ProtonMail is now in hot water — and at least one of its users has been arrested.
What happened exactly?
Last weekend, news blew up about ProtonMail logging one of its users and providing IP address logs to French authorities. The ProtonMail user was subsequently arrested in France.
Note: ProtonMail has provided us with more clarification, stating that the location and identity of the suspect were already known to the police. The logs that ProtonMail provided helped the police to further build a case against the person, ultimately leading to his arrest.
The news gained traction first on Twitter, with various media outlets also picking up the story. The key evidence of what transpired behind closed doors was a court document detailing how ProtonMail provided IP address logs of its user to French authorities.
The backlash has been swift. But should we jump to condemn ProtonMail or is this type of situation inevitable with privacy services? Let’s examine how ProtonMail responded to the situation and put it into context by comparing it to other cases where email and VPN services provided logs to authorities — as well as cases when they did not.
ProtonMail touts Swiss jurisdiction and privacy protection
We place a lot of trust in privacy services to do what they actually say. In the case of ProtonMail, they have boldly touted their privacy and security credentials for years. Not only have they claimed to not keep any IP logs by default, but they also regularly tout their Swiss jurisdiction, which allegedly confers legal independence.
Here is how ProtonMail advertises itself and its Switzerland jurisdiction.

So now let’s compare the reality of this situation with ProtonMail’s claims. We have learned that:
- Switzerland jurisdiction does not mean very much. Governments can simply go through a Swiss court and then ProtonMail will start logging any user that is requested by the court.
- The “extremely limited user information” is enough to find and arrest a ProtonMail user, with IP address and device info data.
It is also interesting how ProtonMail responded to this situation and the subsequent website revisions.
ProtonMail scrubs “we do not keep any IP logs” from its website… after IP logging incident
When a privacy service’s claims do not line up with reality, trust is eroded and potentially lost forever. While trust is very subjective, ProtonMail’s logging activities and subsequent website revisions have certainly raised some eyebrows.
Using the Wayback Machine, we can see that ProtonMail did some editing to its website in the wake of this logging incident.
Before the logging scandal:
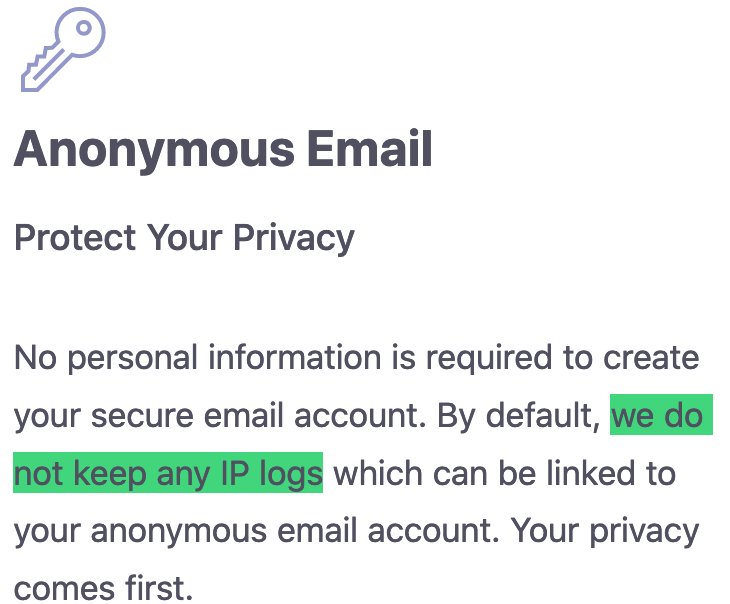
In the image above, you can see that the “we do not keep any IP logs” claim is prefaced with the “By default” at the beginning. Now, after the logging fiasco, the reference to not keeping IP logs is gone.
After the logging scandal:
Gone is the claim, “we do not keep any IP logs which can be linked to your anonymous email account.”
In ProtonMail’s defense, it does not seem like anything changed. Technically, they probably did not keep any IP logs by default — but that is the key distinction. With just one quick request through a Swiss court, however, an outside government or agency could quickly get all the logs they needed to find and arrest the ProtonMail user they’re looking for. Case closed.
You can read ProtonMail’s response to the situation here.
Not the first time ProtonMail has logged users
We should also point out that ProtonMail has logged users in the past when ordered to be a Switzerland court. This is detailed on the Transparency Report here.

ProtonMail’s Transparency Report shows numerous cases where they have complied with various court requests for user data.
And similar to the current logging case, ProtonMail did some major site revisions by changing the wording of the Transparency Report after some other cases came to light. This was first noted by Martin Steiger in Switzerland here.
Other email provider’s that have bowed down to logging demands
Before you rush to condemn ProtonMail, you should understand the situation a bit more with some background information. For one, this is nothing new. We have been keeping a close eye on the privacy space for years now, and this is not the first time something like this has happened.
Riseup logs user data for US authorities
Riseup, which is an email and VPN provider based in the United States, was forced to comply with data requests a few years ago:
After exhausting our legal options, Riseup recently chose to comply with two sealed warrants from the FBI, rather than facing contempt of court (which would have resulted in jail time for Riseup birds and/or termination of the Riseup organization).
There was a “gag order” that prevented us from disclosing even the existence of these warrants until now. This was also the reason why we could not update our “Canary” [warrant canary that warns users about these events].
This appears to be similar to the ProtonMail situation, except that with ProtonMail, the goal was to identify the user with IP address logs.
Tutanota saves unencrypted emails for German authorities
A similar situation unfolded in 2020 with the German email provider Tutanota. In this case, Tutanota was required by a German court to log incoming and outgoing emails for a specific user identified in a German court order. This only affected unencrypted emails for a specific user, as Tutanota explained here.
However, all unencrypted emails that were sent and received by this user would have ended up with the German government, while encrypted emails would have been safely encrypted (and unreadable). The original article explains the case is in German here.
Similar to the ProtonMail case, this was a specific court order targeting one individual who was using Tutanota’s service for (alleged) illegal activities. In other words, the courts did not force a blanket policy that affects all of the service’s users.
When logging requests are denied (with VPNs)
When putting the current logging situation into context, it’s also important to examine when logging requests are denied. We have written about different examples of this in our no logs VPN guide. This includes cases where ExpressVPN, Private Internet Access (PIA), and OVPN have all successfully denied government requests for user data.
As one example, we’ll take a look at a recent case with OVPN, a Swedish-based VPN service that has successfully fought back against logging demands. The VPN was ordered by a court to log users who were accused of violating copyright laws by downloading movies. They were being sued by a group called the “Rights Alliance” on behalf of the movie industry.
Rather than comply with the request, OVPN lawyered up and went to court to fight for its users. And they won the case, proving that they are a truly no logs VPN service that takes their users’ privacy seriously.
To summarize the verdict, the Rights Alliance and their security experts have not been able prove any weaknesses in OVPN’s systems that could mean that logs are stored. OVPN therefore wins the information injunction as our statements and evidence regarding our no log VPN policy have not been disproven. The movie companies also need to pay OVPN’s legal fees which amounts to 108,000 SEK (roughly $12,300 at current exchange rate).
While the nature of an email service and VPN service are very different, this case does show that there are examples when privacy companies successfully fight back against demands for user data.
However, there are other VPNs that bow down and comply with these demands, as we have seen with PureVPN logging users for the FBI, as well as with IPVanish, which is based in the US.
Should people still use ProtonMail?
While this latest logging fiasco (and ProtonMail’s website revisions) will probably shake many peoples’ trust in the service, ProtonMail itself remains secure and private compared to most other options. With most free email services, such as Gmail and Yahoo, your inbox is wide open for data collection and advertising exploitation.
Conversely, ProtonMail keeps your inbox encrypted and secure at rest, without giving others access. Sure, they may be forced to log user IP addresses, but there is a simple solution for that (see below). Additionally, you can be certain that advertisers are not collecting the content of your inbox to hit you with targeted ads.
Nonetheless, if you now want to seek out alternatives to ProtonMail, see our guide on private and secure email services. We’ll still be recommending ProtonMail because nothing has really changed. The same goes for Tutanota.
Be smart and always use a VPN (and other privacy tools)
We’ve said this before and we’ll say it again. Everyone reading this should be using a VPN when going online. A VPN is simply basic protection that will hide your IP address and geographic location when you go online. This is something everyone needs in today’s world of mass surveillance and tracking.
Had the ProtonMail user in question been using a good VPN, and also implementing basic OPSEC, he probably would never have been arrested. ProtonMail would have logged the user’s IP address, but that would have only led investigators to a VPN server in some random data center, rather than the user in question.
In addition to using a secure browser and a VPN, we also recommend using a good ad blocker that can effectively block ads and trackers on all browsers. There is also the option to combine both VPN and ad blocker, which is especially effective in many circumstances, while also being easy to use. See our VPN ad blocker guide for additional information.
Consider using an encrypted messenger for really private communications
Lastly, this is a good opportunity to repeat another piece of advice that we have been saying for years:
If you really need privacy, don’t bother using email. Instead, use a good encrypted messaging service.
Email is simply an outdated method of communication that is leaky and contains lots of private data. By contrast, there are some great privacy-focused encrypted messaging systems, from Signal to Telegram and Wickr. We have also been impressed with Session, which takes privacy to another level and keeps no metadata whatsoever.
Check out our guide on the best encrypted messaging services to learn more.

 Hacker Selling Private Data Allegedly from 70 Million AT&T Customers
Hacker Selling Private Data Allegedly from 70 Million AT&T Customers
Leave a Reply