
In today’s digital world, privacy and security have become paramount. With cyber threats on the rise and geo-restrictions limiting your online experience, a reliable VPN is more crucial than ever. NordVPN offers comprehensive features and robust security measures to help you navigate the digital landscape safely and effortlessly.
But is NordVPN the right choice for you? And do the marketing claims live up to real-world test results? In this NordVPN review, we’ll delve deep into NordVPN’s features, performance, and user experiences to answer these pressing questions.
Let’s first cover the basics in the table below, and then dive into the nitty-gritty details.
| Website | NordVPN.com |
| Based in | Panama |
| Logs | No logs (audited) |
| Price | $3.09/mo. |
| Support | 24/7 live chat |
| Refund | 30 days |
| Coupon | 69% Off + 3 months FREE |
As with all of our VPN reviews here on RestorePrivacy, we really get into the details with test results and analysis. Here’s what we looked at for this NordVPN review:
- Numerous speed tests conducted with NordVPN servers around the world
- Leak tests conducted on the desktop applications (checking for IPv4, IPv6, and DNS leaks)
- Testing the kill switch and all features
- Streaming compatibility checks with Netflix and other services
- Testing the specialty servers, including the Double-VPN and P2P servers
- Analyzing all features and pricing options
With cyberattacks and corporate surveillance on the rise, a good VPN is a crucial tool for everyone going online. And with the massive growth in online streaming platforms, a VPN is your ticket to watching pretty much anything from anywhere in the world. So, let’s begin this NordVPN review by examining the basic findings.
+ Pros
- User-friendly and reliable apps
- Double-VPN and Tor-over-VPN servers
- Passed numerous 3rd-party audits
- Strong encryption standards with full support for WireGuard
- Works with Netflix and many streaming sites
- Threat Protection feature to block ads, trackers, and malware
- Professional 24/7 live chat support
- Consistently fast speeds
- Dedicated RAM-servers with 10 Gbps bandwidth channels
– Cons
- Big discounts only available with 2-year plans
NordVPN Overview: Key Features and Benefits
NordVPN is a top-tier VPN provider that has consistently performed well in our tests over the years. It has also earned lots of praise in the industry for its range of features and robust security measures. Here are some key features of NordVPN:
Over 5,700 servers in 60 countries
Excellent speed test results (over 750 Mbps)
- Advanced tunneling protocols (NordLynx)
- Extra security features (Threat Protection and data breach monitoring)
- Specialty servers
Unrestricted streaming and torrenting capabilities
- User-friendly apps
Now let’s examine the speed test results and find out if NordVPN is a fast VPN.
NordVPN speed test results: Is NordVPN fast?
For this NordVPN review, I ran dozens of speed tests using different VPN protocols and various servers around the world. Within the NordVPN desktop apps (Windows and macOS), you can select the VPN protocol you’d like to use. For all speed tests, I left it on “Automatic” to let the VPN select the best protocol. My baseline speed was around 900 Mbps.
This table summarizes our speed test results.
| NordVPN Server Location | Speed (Mbps) |
| Seattle | 755 |
| Los Angeles | 636 |
| New York | 613 |
| London, UK | 592 |
| USA-Canada (Double VPN) | 614 |
The closest VPN server I tested was in Seattle, where I hit download speeds of 755 Mbps.
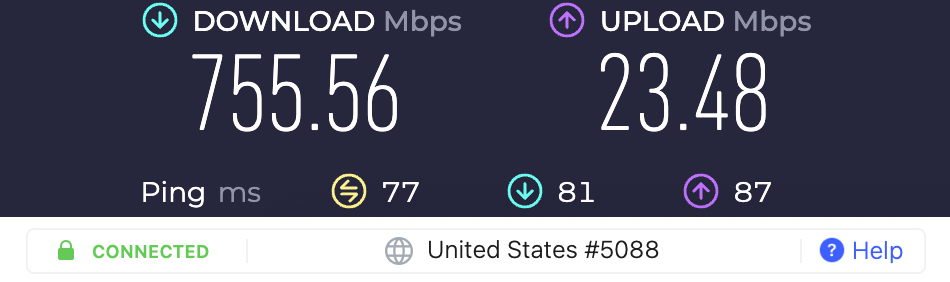
This is the fastest VPN download speed test result we’ve gotten on RestorePrivacy.
Next, I tested a NordVPN server in Los Angeles. Once again, the test results were excellent, with download speeds around 636 Mbps:
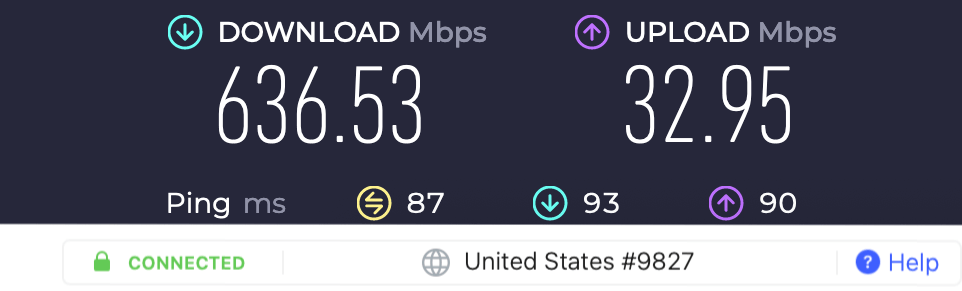
At over 600 Mbps, it is clear that NordVPN belongs in the “fastest VPNs” category. It even came out on top in the NordVPN vs ExpressVPN comparison.
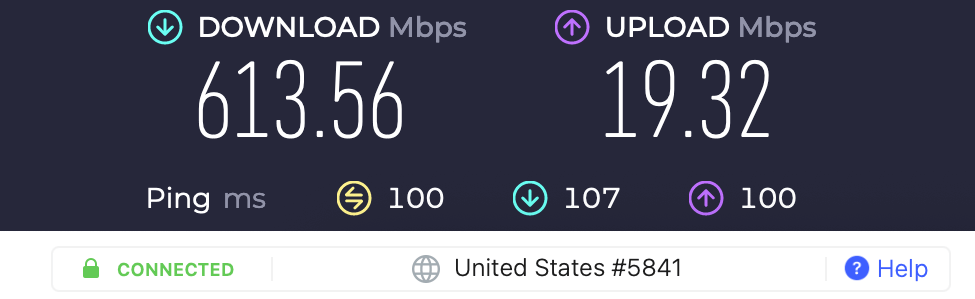
Next, I tested a server in New York, and it was again very fast at 613 Mbps.
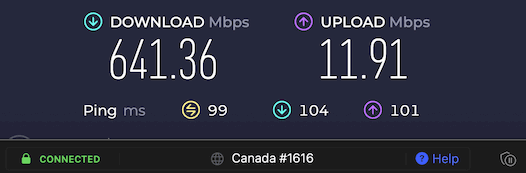
In speed tests for our guide on the best VPNs for Canada, we were able to consistently hit speeds around 640 Mbps with NordVPN servers in Canada.
Lastly, I tested a server in the United Kingdom. Here is the NordVPN UK server with speeds of around 592 Mbps:
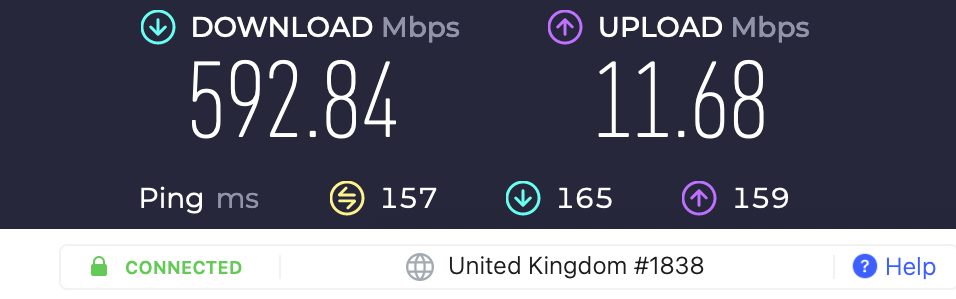
We have been consistently running NordVPN speed tests for years, and these are the fastest speeds we have observed. It’s clear that NordLynx with its built-in WireGuard VPN protocol and the server network upgrades has really improved performance. We also used NordVPN for our WireGuard vs OpenVPN comparison, where we found WireGuard to be significantly faster than OpenVPN.
Note: Not all WireGuard VPNs perform on this level. For example, you can see in the CyberGhost vs NordVPN report that NordVPN had a huge performance advantage, despite both VPNs using WireGuard.
NordVPN Double-VPN speed test results
Finally, I also ran some double-VPN speed tests. These are the “Double-VPN” servers that you can select within the NordVPN app.
Usually, due to the longer distance, double encryption, and increased latency, you’d expect these double-VPN servers to be slower. Nonetheless, the double-VPN servers I tested with NordVPN were also surprisingly fast.
Here is the USA > Canada server combination I tested with speeds of 614 Mbps!
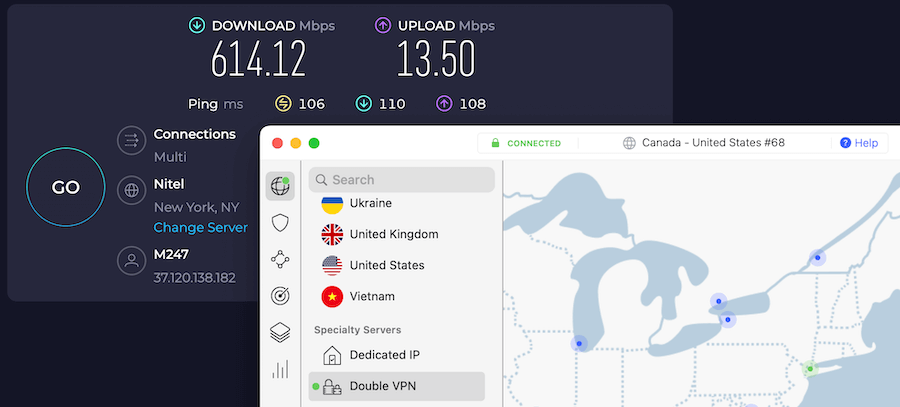
For a double-VPN connection, these speeds are excellent.
NordVPN significantly outperforms other VPNs that offer double-VPN configurations. You can see this in the NordVPN vs ProtonVPN article.
Reliability and connections
On the topic of performance, it’s also important to discuss reliability and connections:
- Reliability – I found NordVPN to be very reliable. The servers were consistently fast and I did not experience any dropped connections.
- Connections – When using the WireGuard VPN protocol, I found that NordVPN was extremely fast at establishing a connection — nearly instantly. While OpenVPN can take a few seconds, it also was not sluggish at all. This makes switching VPN servers all the more quick and easy.
Conclusion on performance – With the latest round of speed tests for this review, I can conclude that NordVPN offers fast, consistent, and reliable speeds. It also consistently comes out on top in comparison with other VPNs, such as in the NordVPN vs IPVanish comparison.
NordVPN’s privacy and security features
NordVPN offers some solid features to enhance both the privacy and the security of users – above and beyond most other VPNs.
Encryption and VPN protocols
NordVPN’s OpenVPN clients use an AES-256-GCM cipher and HMAC SHA256 hash authentication. The AES-256-GCM cipher is used to encrypt traffic with the IPSec/IKEv2 protocol.
In addition to OpenVPN and IPSec/IKEv2, NordVPN also supports the WireGuard VPN protocol directly in all VPN apps. NordVPN’s privacy-focused implementation of WireGuard is called NordLynx. You can easily switch between protocols under Settings/Preferences.
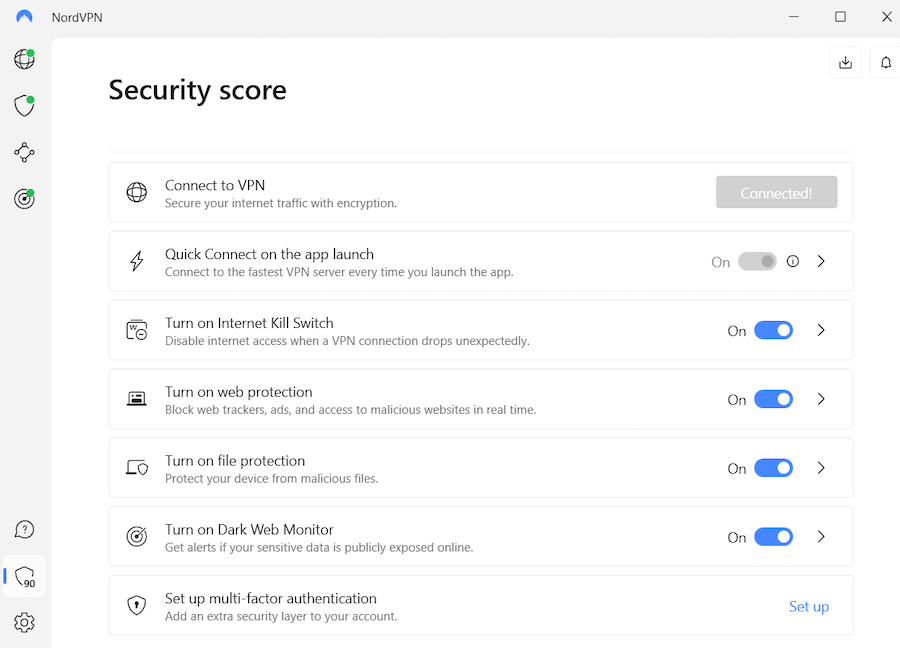
Threat Protection to block ads, trackers, and malware
The Threat Protection feature goes beyond the normal boundaries of what a VPN does. There are two versions of Threat Protection.
Threat Protection Lite for mobile devices and Linux
Despite the “Lite” in the name, Threat Protection Lite is a powerful tool. It blocks ads, trackers, unsafe connections, and malicious websites for any connections passing through a VPN server. In our tests of Threat Protection Lite for this review, it was very effective at blocking ads and trackers.
Threat Protection Lite is the version of Threat Protection available for the Android, iOS, and Linux operating systems. It is also the version of Threat Protection available in the NordVPN Chrome, and Edge browser extensions. This makes NordVPN one of the best VPNs for Chrome available.
Threat Protection (full version for Windows and macOS)
Threat Protection does everything that Threat Protection Lite does, but also offers the ability to, “Scan files downloaded files and delete the harmful ones before they do damage.”
You can see the current set of Threat Protection features we tested out in the following image.
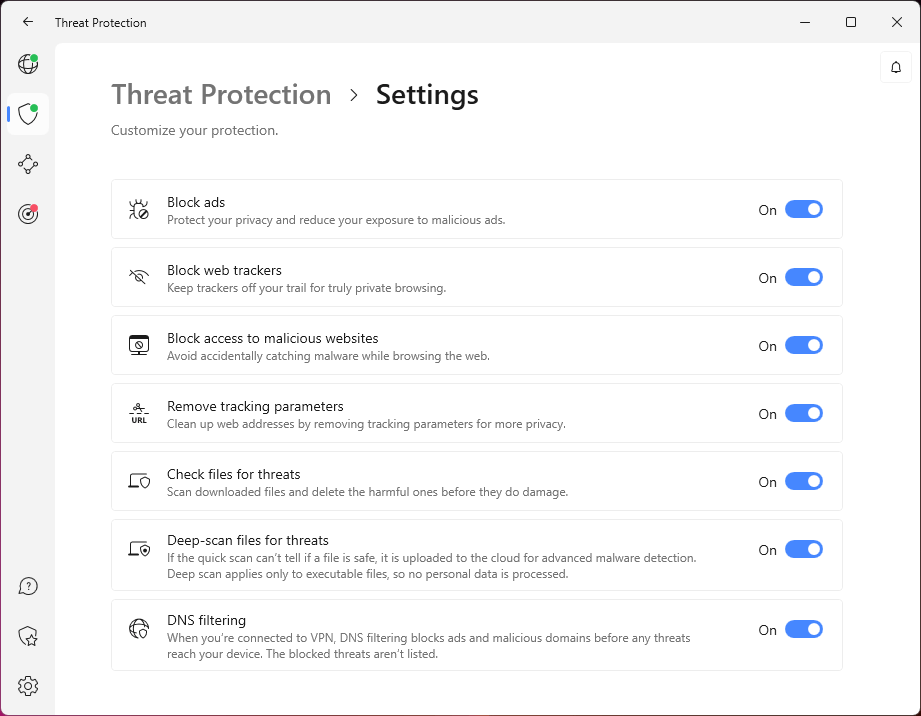
Another impressive aspect of the full Threat Protection features is that it works even when you are not connected to a VPN server. Turn on Threat Protection and it protects everything you do online, whether or not your data is going through the VPN server.
Threat Protection gives you more privacy by blocking ads. These days, almost every ad you see online is a sophisticated tracking tool that lets ad agencies and social media record your online activities and use the data to profile you and bombard you with targeted advertising. It works so well that NordVPN with Threat Protection belongs on our list of the best VPN ad blockers.
Besides the ads you see, many websites try to install third-party trackers that allow companies like Google and Facebook to track your activities everywhere you go online. Letting Threat Protection block ads and trackers gives you a major privacy boost and cuts down on the distractions you see.
Threat Protection gives you more security by blocking malicious websites and nuking corrupted downloads. In addition to trying to track you online, some ads try to sneak malware onto your devices where it can wreak havoc. Some of these malicious advertisements (known as malvertising) can even install malware on your system simply by appearing.
Then there are the files you download. Open the wrong downloaded file and it can infect your system before you have any idea something is wrong. Threat Protection can scan those documents before you open them, and delete them from your system before they can do any harm.
At the time of this review, the full-powered Threat Protection is only available in the NordVPN Windows and Mac OS apps. Nonetheless, the Lite version is still a powerful alternative.
Double-VPN servers (multi-hop)
NordVPN is one of a handful of VPN providers that offer multi-hop functionality – or in this case, double-VPN servers. With NordVPN’s double-VPN servers, your traffic is encrypted across two VPN servers before exiting onto the regular internet. This also offers some advantages.
- Double-VPN gives you an extra layer of encryption between your device and the regular internet.
- This could also protect you against a compromised data center. In a double-VPN setup, no single server can see both your machine’s IP address and the sites you visit.
- Distributes trust across two different servers.
Using a multi-hop VPN is certainly not a bad idea. We also see this feature with Surfshark and ProtonVPN.
NordVPN currently offers 31 double-hop VPN configurations. These can easily be selected from within the NordVPN client, as you can see below.
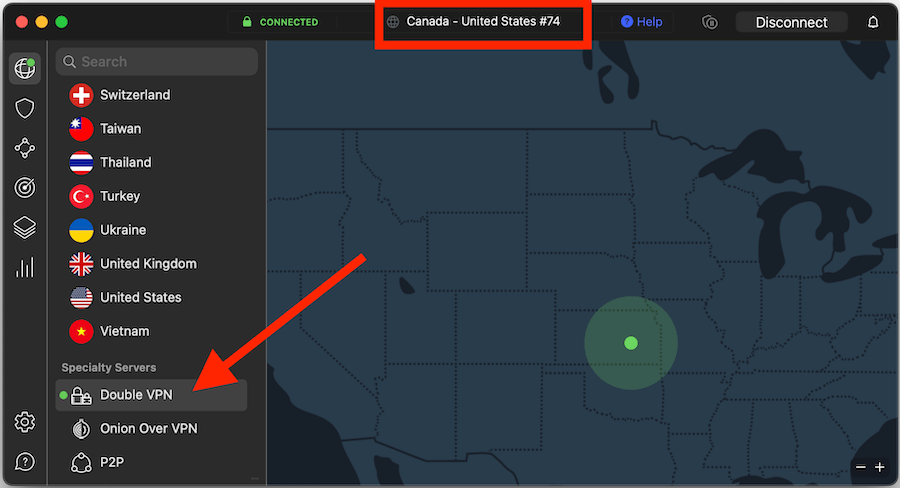
Note in the screenshot above that we also have “Dark Mode” enabled within the macOS VPN app we were testing.
For those wanting a higher level of privacy protection and security, double-VPN servers are a great option to consider.
See all NordVPN features here >>
Onion-over-VPN servers
If you are looking for additional encryption and anonymity beyond a single-hop VPN server, another option is to use an Onion-over-VPN server. These servers encrypt traffic with the Tor Network, in addition to the regular VPN server. NordVPN currently offers two locations for this: the Netherlands and Switzerland.
Obfuscated Servers
These servers are available directly in the VPN client when you are using the OpenVPN protocol. These servers hide (obfuscate) VPN traffic to appear as regular HTTPS traffic and are useful in the following situations:
- When you need to get around VPN blocks at work, school, or restricted networks.
- To evade state censorship efforts and VPN blocks in certain countries, such as in China, UAE, and others.
The selection of obfuscated servers makes NordVPN a great option if you need a VPN for the UAE, the best VPN for China, or internet access in any other restricted country. It offers built-in obfuscation features that will conceal VPN traffic and get around difficult obstacles like the Great Firewall of China.
To use NordVPN in one of these restricted areas, simply connect to one of the Obfuscated servers in the VPN client. When you use one of these servers, the NordVPN client will automatically obfuscate your VPN traffic to make it appear as regular HTTPS encryption. Since virtually all internet traffic today uses HTTPS encryption, your VPN traffic becomes effectively invisible to the censors.
Note: Some VPN providers utilize obfuscation through VPN protocol changes rather than specific servers, as we described in the Surfshark vs NordVPN comparison.
NordVPN kill switch
NordVPN is one of the few VPNs that offers two different kinds of kill switches. A VPN kill switch is important because it blocks traffic if the VPN connection drops, which protects you from de-anonymization and your regular traffic being exposed.
In the screenshot below you can see the two different kill switches on the NordVPN Windows client:
- Internet Kill Switch – This kill switch gives you two options. The first option is to block all traffic if the VPN connection drops unexpectedly. This option would activate if something unusual happens, but not if you disconnect from the VPN manually. The second option is to block all traffic if the connection drops for any reason. This second option would also block traffic if you disconnect from the VPN manually.
- App Kill Switch – This kill switch will close specific apps if the VPN connection drops, but will not block traffic. Click the Add apps button shown below to specify which apps should be shut down.
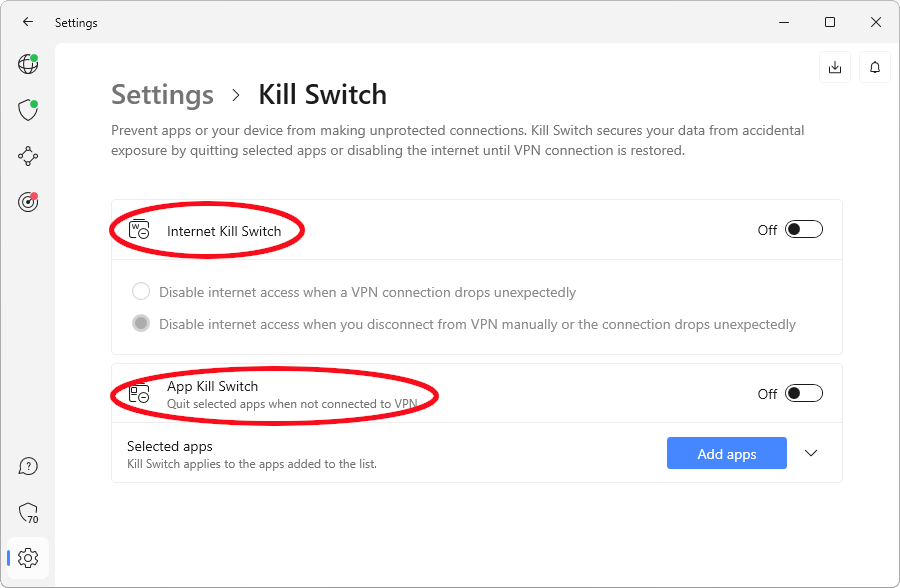
If you are concerned about address leaks, it would be best to use the “Internet Kill Switch” as this will block non-VPN traffic via the firewall. And if you are using the kill switch, then you probably don’t need to use the App kill switch.
Meshnet
NordVPN’s Meshnet feature allows secure device-to-device connections for file sharing and routing traffic. This innovative feature enables users to create a secure network of devices, facilitating the sharing of files and data without exposing their activities to potential threats. Earlier this year, NordVPN released Meshnet for free.
Meshnet is a valuable addition to NordVPN’s security toolkit, providing users with yet another layer of protection for their online activities.
Data breach monitoring
In an age where data breaches are becoming increasingly common, NordVPN offers data breach monitoring to alert users if their personal information is compromised. This proactive feature continuously scans the internet for any new data breaches and notifies users if their credentials appear in a breach.
Specifically, NordVPN can check to see if the email you used to register is leaked in any data breaches (this is just like the Have I Been Pwned service).
NordVPN leak test results (no leaks found)
I ran the NordVPN Windows and Mac OS clients through some basic VPN tests and checks to identify any leaks or problems. Additionally, I also tested out NordVPN’s kill switch to see if it was effectively working in both clients.
With the NordVPN Windows client, I did not find any address leaks or DNS leaks. In the screenshot below, you can see:
- the IPv4 address matches up with the VPN client (no IPv4 leaks)
- IPv6 is effectively being blocked (no IPv6 leaks)
- No WebRTC leaks (but this is blocked in your browser)
- DNS requests are being handled by the NordVPN servers (no leaks)
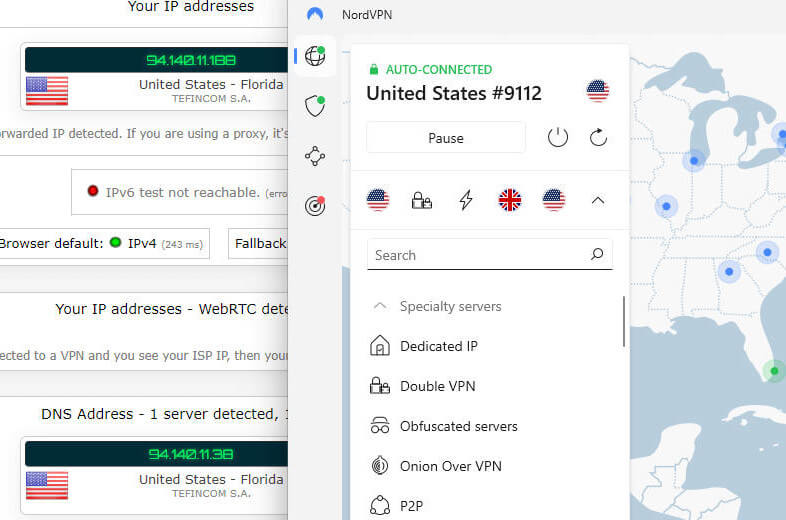
I also found the Internet Kill Switch and App Kill Switch to work well – no issues or problems to report.
MacOS leak tests – I ran the MacOS VPN clients through the same tests as above with the Windows client. The results were the same in that I did not find any leaks or problems. Additionally, the Mac OS kill switches worked correctly without any issues.
Android leak tests – Another team member tested the NordVPN Android client when working on the Best VPN for Android roundup. He found it to perform very well without any leaks or issues. If you want more options, both Surfshark and ExpressVPN also offer good Android clients.
NordVPN offers secure and user-friendly apps
NordVPN also offers a nice lineup of secure apps (clients) for all major operating systems and devices:
- Windows
- Mac OS
- Linux
- Android and iOS (mobile)
- Android TV
Here were my main takeaways from testing and reviewing the NordVPN clients on Windows and Mac OS:
- Fully-featured – The NordVPN apps are loaded with features, including specialty servers, leak protection, and startup/connection settings.
- Easy to use – Whether you are new to VPNs or a seasoned pro, you should find NordVPN clients user-friendly and intuitive. Adjusting settings and selecting features is simple.
- Secure – Aside from the strong encryption we discussed above, NordVPN also secures data with a kill switch. This blocks traffic (or closes specific apps) if the VPN connection drops for any reason. We’ll examine this more below.
NordVPN Windows
The NordVPN Windows app (client) utilizes the OpenVPN and WireGuard VPN protocols and supports the full NordVPN feature set we discussed above, as well as:
Two split tunneling options
Two kill switch types
LAN invisibility
Auto-connect
Pause capabilities
To connect to a server in the NordVPN Windows client, you can use the list on the left or click a location on the map. You can also configure it to find and connect to a server automatically. In the screenshot below, I’m testing the Windows VPN client.
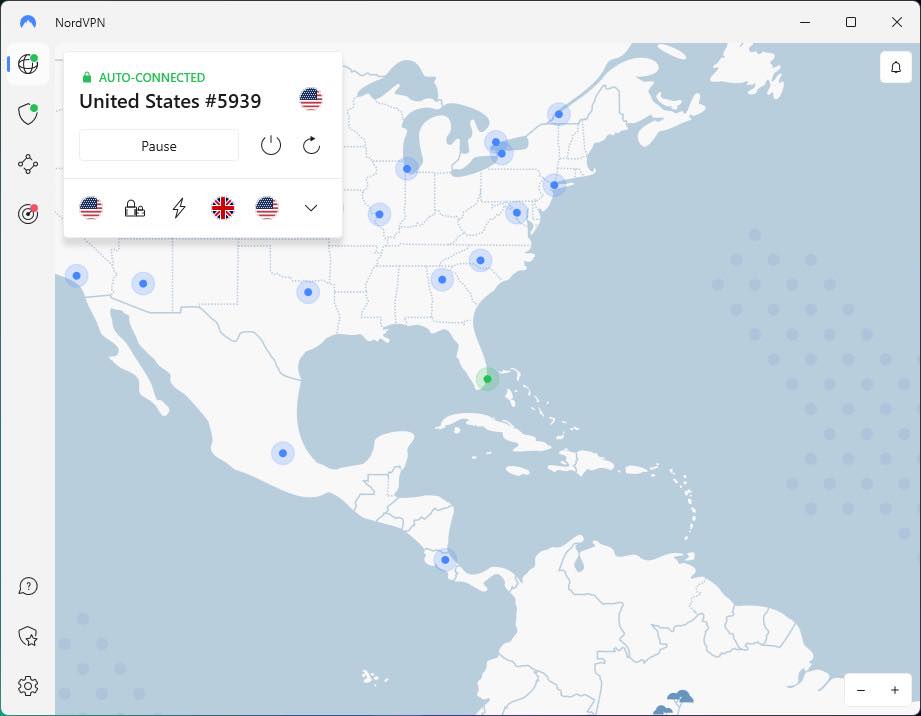
Users can choose between NordLynx and OpenVPN (UDP/TCP) tunneling protocols from the client, ensuring optimal performance and security based on their needs.
NordVPN macOS
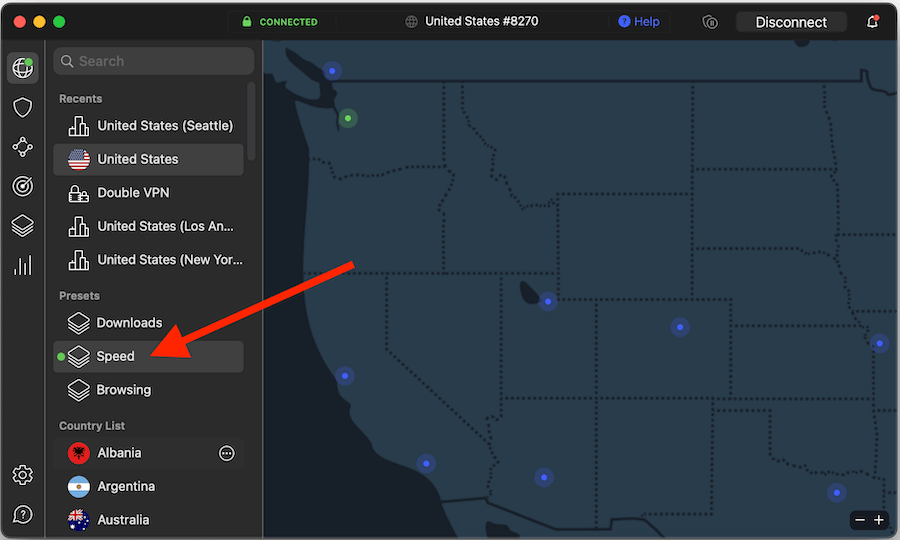
The NordVPN Mac OS app offers all of the same features and a built-in kill switch that automatically blocks traffic if the connection drops. With the Mac OS client, you can select between the following VPN protocols: IKEv2, OpenVPN UDP, OpenVPN TCP, and NordLynx (WireGuard). You can also check out our top-rated VPNs for Mac for additional options.
With its strong security features and intuitive design, NordVPN’s macOS app is an excellent choice for Mac users looking for a reliable VPN solution.
NordVPN Linux
The NordVPN Linux client is a very different critter. Like most VPNs that do have a Linux VPN app, this one has a command line interface, instead of a nice desktop app. What does such a critter look like? Like this:
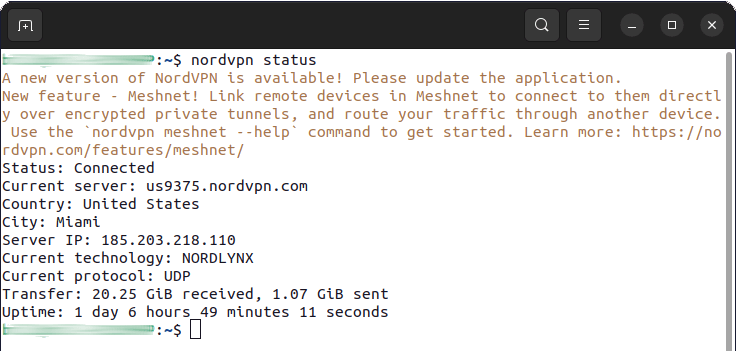
NordVPN’s Linux app includes DNS leak protection, preventing DNS leaks, and supports the NordLynx protocol by default, providing a secure and fast connection for Linux users. With detailed setup guides available on the NordVPN website, Linux users can quickly and easily configure their VPN connection to meet their specific needs.
NordVPN Android and iOS apps
NordVPN’s Android and iOS apps provide a consistent and user-friendly experience across mobile devices. The apps offer a clean interface and easy access to essential features, ensuring a smooth VPN experience on the go. While there are some differences between the iOS and Android apps, such as the presence of a Favorites tab on iOS, both apps maintain a high level of functionality and ease of use.
Below is the Android VPN app we tested out for this review:
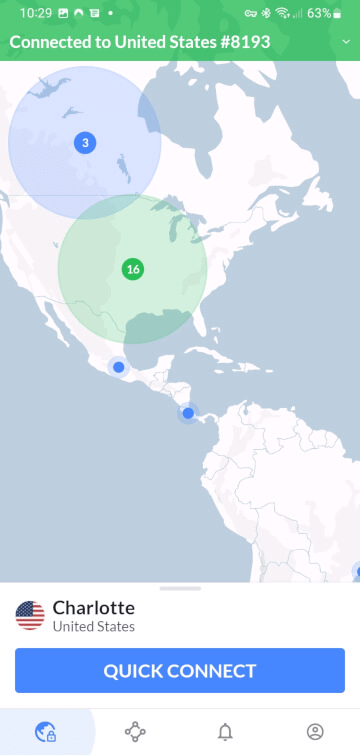
In terms of security, the Android and iOS apps support IKEv2, OpenVPN (TCP/UDP), and NordLynx protocols, providing flexibility and strong protection for mobile users. With their accessible design and robust security features, NordVPN’s mobile apps are an excellent choice for users seeking a secure and easy-to-use VPN solution on their smartphones and tablets.
NordVPN’s server network
NordVPN boasts a huge server network, which currently includes over 5,700 servers in 60 countries. With such a large number of servers in its network, it is easy for NordVPN to unblock websites and other digital content. It also makes finding a fast and reliable server close to your location easy. This helps to minimize latency (ping), which is important if you need the best VPN for gaming.
Additionally, the NordVPN client will automatically select the fastest server for a given location you want. You can also just click “Speed” under the Presets section, as you can see below.
Aside from the large network we noted above, there are many other features of NordVPN’s server network that make it stand out from the rest of the VPN crowd:
- Colocated servers – While most VPNs rent servers from various third parties, NordVPN has decided to raise the bar by deploying their own hardware (colocated servers). Most of NordVPN’s network already includes colocated servers, with the only exceptions being remote locations.
- All servers run on RAM (no hard drives) – Similar to other leading VPNs, NordVPN runs all of its servers on RAM memory without hard drives. This means it is physically impossible for any user data to be stored on any server in NordVPN’s network.
- 10 Gbps bandwidth channels – Many of NordVPN’s popular server locations are running on 10 Gbps bandwidth channels, providing huge throughput for NordVPN users. This is most likely a major factor in our good speed test results.
See all NordVPN server stats here >
NordVPN’s server network is a bit like the engine under the hood of a Ferrari. It’s the powerful driver behind the VPN.
NordVPN Customer support
NordVPN offers 24/7 live chat support and the representatives are quite helpful.
Chat support is always available through the NordVPN website in the bottom-right corner. You don’t have to log in, simply click on the chat icon and you’ll be connected with a representative. You may need to go through a chatbot to get to a real person, but I did find the chatbot was good at pointing me to helpful support articles.
It’s appears that NordVPN does not outsource support to third parties. Everything is handled by NordVPN staff and not by an external agency.
Third-party audits
Over the years, NordVPN has undergone numerous privacy and security audits
No-logs privacy audits
NordVPN is one of the few VPN services that has had its no-logs claims audited and verified on three separate occasions. The first two no-logs audits were conducted by PricewaterhouseCoopers in 2019 and 2021. Finally, the most recent no-logs audit was completed by Deloitte in 2023.
Here is a further explanation of the NordVPN logging policy from their privacy policy:
NordVPN strictly keeps no logs of your activity online. That means we do not track the time or duration of any online session, and neither do we keep logs of IP addresses or servers used, websites visited or files downloaded. In other words, none of your private and secure data is logged and gathered at any time. As a result, we are not able to provide any details about your behavior online, even if you request it yourself. NordVPN is based away from the EU and US jurisdiction and is not required to collect your personal data and information– it means nothing is recorded, monitored, stored, logged or passed to third parties.
Overall, NordVPN is a solid choice if you are looking for a no-logs VPN provider that has been verified and proven to be true.
Security audits
Finally, NordVPN underwent a full infrastructure security audit more recently this year.
Most recently, Cure53 completed an audit (penetration testing and source code auditing) of NordVPN’s security posture. The audit was wide-ranging, including browser extensions, VPN servers, NordLynx server-side code, the NordVPN account you log in with, and much more. All the detected vulnerabilities have been fixed and verified by Cure53. Learn more about this audit here.
NordVPN is based in Panama (a good privacy jurisdiction)
Another advantage of NordVPN is that it is based in Panama. Panama is not a member of any international surveillant alliances (see the Five Eyes) and has no mandatory data retention laws. In other words, it remains an excellent jurisdiction for privacy.
As NordVPN explains this issue further on its website:
We are based and operate under the jurisdiction of Panama. There is no mandatory data retention law in Panama so we do not need to store logs which is perfect for a VPN provider.
Being based in Panama is indeed a good jurisdiction that gives NordVPN advantages over other VPN service providers, as I also explained in my NordVPN vs PIA comparison.
Streaming Capabilities: Can NordVPN Unblock Your Favorite Content?
Accessing geo-restricted content on streaming platforms is a primary reason many users utilize a VPN. NordVPN excels in this area, unblocking popular streaming services like Netflix, Hulu, and Amazon Prime, providing users with a seamless and enjoyable streaming experience.
NordVPN’s SmartPlay technology ensures users can access streaming platforms without any restrictions, making it a top choice for users who want to enjoy their favorite content from anywhere in the world.
I tested NordVPN servers in the US to access American Netflix. Everything worked perfectly without any issues, as you can see below:
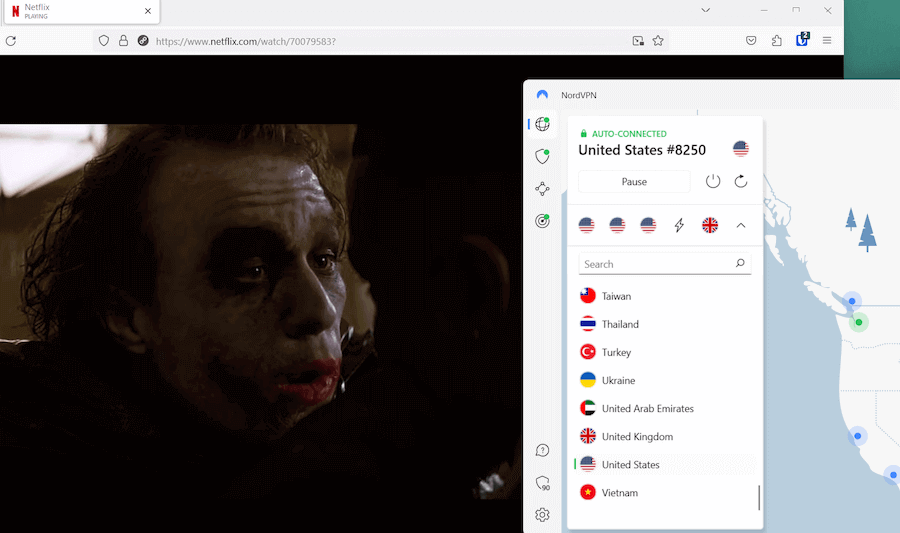
With NordVPN, you can get full access to the following Netflix regions: US, UK, Canada, France, Germany, Netherlands, Spain, Japan, Australia, India, and Italy. (Other regions may also work, but were not tested for this review.) With full regional support, NordVPN is definitely one of the best VPNs for Netflix.
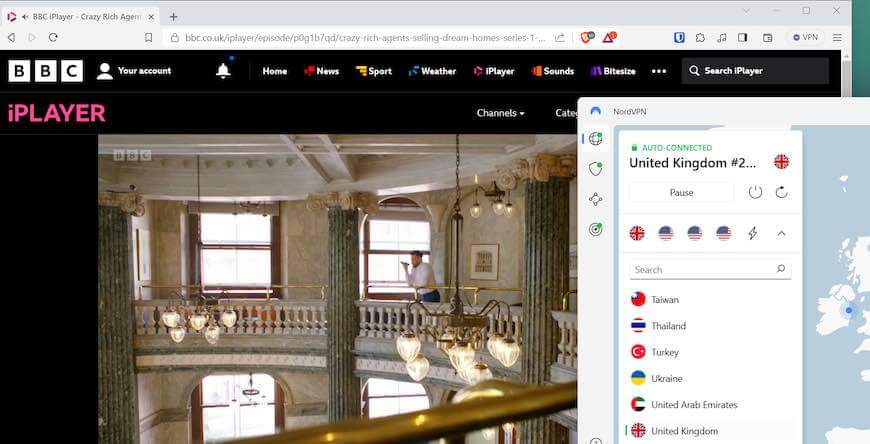
Hulu, Amazon Prime, and other streaming services
NordVPN works with other streaming services, such as Hulu, Amazon Prime, and others. It is also a great VPN for Disney Plus, which offers lots of content in 10 different regional libraries. With the latest test results, NordVPN is one of only three other VPNs that work with BBC iPlayer, as you can see below.
Note: If you have any trouble getting Netflix to work with NordVPN, simply ask Support. The live chat representatives will tell you exactly what servers to use.
Torrenting with NordVPN
Torrenting can be a risky endeavor, with potential security threats and legal consequences if done without proper protection. NordVPN is an excellent choice for users who engage in P2P file sharing, as it offers dedicated P2P servers and robust security features to ensure a safe and anonymous torrenting experience.
With its SOCKS5 proxy, specialized P2P servers, fast speeds, and secure apps, NordVPN provides a great environment for torrenting. It will ensure your downloads are protected from prying eyes, and your identity remains protected. It’s currently ranked the best VPN for torrenting due to all these factors.
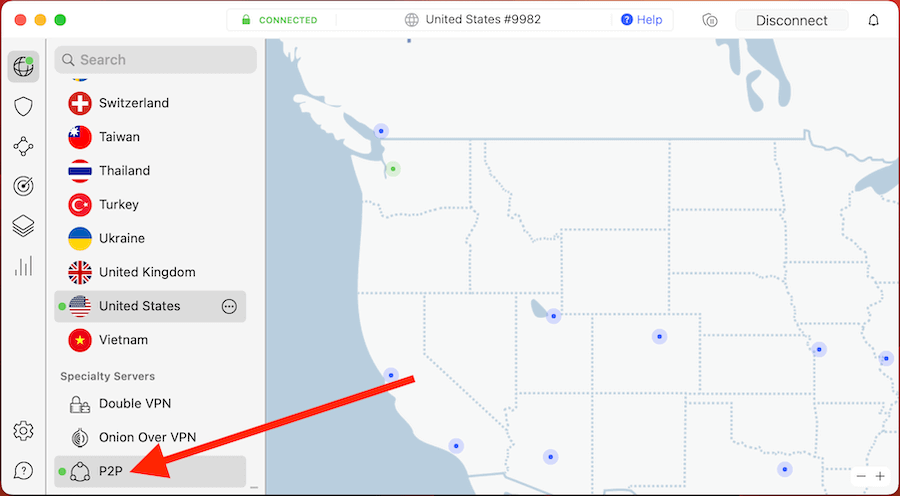
The NordVPN app will automatically connect to the fastest P2P server for a given country you select. Additionally, you can also manually connect to certain torrenting servers through the NordVPN app.
Dedicated IP addresses
NordVPN users can add one or more dedicated IP address (also referred to as a dedicated IP) to a subscription. A dedicated IP from NordVPN is a static IP address that is dedicated solely to you. At the same time, that address is protected by the VPN and has access to VPN features. VPN users can connect up to two devices to each dedicated IP; one configured to use the OpenVPN (TCP) protocol, and the other configured to see the OpenVPN (UDP) protocol.
NordVPN offered dedicated IPs for the following locations:
- United States (Buffalo, Los Angeles, Dallas, New York)
- Germany (Frankfurt)
- The United Kingdom (London)
- The Netherlands (Amsterdam)
- France (Paris)
- Canada (Toronto)
- Japan (Tokyo)
- Italy (Milan)
- Sweden (Stockholm)
- Australia (Sydney)
There is an additional cost for a dedicated static IP from NordVPN. The last time I checked, the price was $70 per year for each dedicated IP, regardless of the location you choose. NordVPN is probably the best VPN for a static IP. You can purchase a dedicated IP by contacting NordVPN support to arrange the IP location you want.
NordVPN prices
NordVPN offers competitive pricing and subscription plans, catering to a wide range of users and budgets. The three main plans available are:
Standard: Provides access to NordVPN’s core features.
Plus: Includes additional services such as NordPass password manager.
Complete: Includes additional services such as NordPass password manager and NordLocker encrypted cloud storage.
Each plan has different features and benefits.
The 2-year subscription of the Complete plan, which includes all Nord products, is on sale with a 69% off coupon here. NordVPN accepts a variety of payment methods, including:
Credit card
Google Pay
AmazonPay
ACH Transfer
UnionPay
Cryptocurrencies like Bitcoin, Ripple, and Monero
DEAL: NordVPN is now offering a discounted two-year subscription price. The savings here are indeed significant, dropping the price down to only $3.09 per month with an additional three months free.
Below are the NordVPN prices, including the discount you will get if you use our coupon:
We consider any VPN service that is under $4 per month a cheap VPN. A two-year Standard plan with all the features and capabilities of NordVPN at under $4.00 per month could well be the best cheap VPN on the market today.
All NordVPN plans allow up to six devices connected at a time. Meshnet allows up to 10 simultaneous connections.
If you are hesitant about the one or two-year subscription plans, NordVPN also offers shorter-duration subscriptions, but they are more expensive. (I’m also maintaining a NordVPN coupon page to track the latest offers and deals.)
NordVPN refund policy (30 days)
To ensure user satisfaction, NordVPN provides a comprehensive 30-day money-back guarantee with each purchase. In our experience, the refund process was efficient and straightforward, with helpful customer service representatives. We experienced no difficulty in obtaining a full refund within a few days.
NordLocker and NordPass add-ons
Beyond its core VPN features, NordVPN provides supplementary services that bolster users’ online security. NordLocker is an encrypted cloud storage service that allows users to securely store and share files with others. It performed well in our NordLocker review.
NordPass is a password manager that enables users to store and manage their passwords securely, ensuring easy access to their online accounts without compromising security. It also performed well in the NordPass review and has really benefited from new features over the past year.
These add-on services can be purchased separately or bundled with NordVPN’s Complete plan, providing users with a comprehensive suite of security tools to protect their digital lives. With NordLocker and NordPass, users can enjoy an all-inclusive security solution, safeguarding their files, passwords, and online activities.
NordVPN with routers
Some VPN services, such as ExpressVPN and VyprVPN, offer a dedicated router app for certain router models. This makes it easier to get a VPN up and running on your router. It also makes it easier if you need to use a VPN for Apple TV and other devices that don’t connect easily to VPNs.
Currently, NordVPN does not offer any VPN router app. Nonetheless, you can still use NordVPN with a router. Here are three ways to do that:
- Get a pre-configured router from an outlet such as Sabai Technology or FlashRouters. These will be somewhat expensive, but they will be ready to use with NordVPN right out of the box and pre-configured with the router firmware you need.
- Get a VPN-enabled router that can be used with a VPN without any flashing required. The best selection of VPN routers comes from Asus. Asus offers numerous routers that can be easily loaded with OpenVPN configuration files (from any VPN provider) and work in just minutes.
- Flash your existing router. This can be tricky and somewhat risky (bricking your router), so you will want to proceed with caution if you go down this route. The degree of difficulty will depend on the router you are using.
Tip: When using NordVPN on a router, connect to the nearest suitable server with the lightest load.
Overall, not having a router app is not a dealbreaker since there are still many ways to use NordVPN on a router. If you go with the Vilfo router, all NordVPN config files are built into the router by default. And as always, NordVPN support can help you get everything set up correctly.
NordVPN for gaming
Online gaming has become increasingly popular, and with it comes the need for a secure and fast VPN connection. NordVPN provides a reliable and fast connection for gaming, ensuring:
Low latency
Secure gaming experience
Robust encryption protocols
Kill switch for data protection
Protection from potential cyber threats and DDoS attacks
NordVPN’s features for gamers include:
Impressive speeds and minimal latency
Optimal choice for ensuring a smooth and enjoyable gaming experience
No sacrifice in security
Compatibility with consoles, computers, and mobile devices
Whether you’re playing on a console, computer, or mobile device, NordVPN has you covered. It is one of the best VPNs for gaming available, especially considering the performance.
Ease of Use: Is NordVPN User-Friendly?
With its easy-to-use interface and straightforward installation process, NordVPN is accessible to users of all skill levels, from beginners to advanced. With native apps available for various platforms, including Windows, macOS, Android, iOS, and Linux, users can enjoy a consistent and user-friendly VPN experience on all their devices.
In addition to its intuitive design, NordVPN provides a range of customization options, including:
Selecting the most suitable tunneling protocol
Enabling advanced security features
Choosing specific servers for optimal performance
Configuring automatic kill switch and DNS leak protection
- Light and Dark modes
These options allow users to tailor their VPN experience to their specific needs and put them in control of their online privacy and security.
Installation Process
NordVPN’s installation process is straightforward, with native apps available for various platforms, such as:
Windows
macOS
Android
iOS
AndroidTV
Secure browser extensions are also available for Chrome, Firefox, and Edge, making installation a breeze.
You simply need to download the appropriate app for your device, follow the installation instructions, and log in with your NordVPN account to get started.
App Navigation
Navigating the NordVPN apps is simple, with a clean interface and easy access to essential features. You can quickly connect to a VPN server by selecting a specific location on the map or choosing from the list of available countries in the sidebar. The NordVPN app ensures a seamless experience for its users.
The app also provides a range of settings and options, allowing users to customize their VPN experience to their preferences.
Customization Options
NordVPN allows users to customize their VPN experience with various settings and options. Users can:
Manually configure their VPN connection on Windows
Use pre-configured settings for secure access to specific apps or websites
Add a dedicated IP
Enable auto-connect
Alter their online location
Specify a custom DNS server
Customize settings in the NordVPN Chrome Extension.
With these customization options, users can tailor their VPN experience to suit their specific requirements and preferences, optimizing their VPN usage.
Comparing NordVPN to Other Top VPN Providers
NordVPN distinguishes itself from other leading VPN providers with its superior speed, security, and privacy. With consistently fast speeds, NordVPN ensures a smooth browsing experience, allowing users to access content without any noticeable lag. In terms of security and privacy, NordVPN offers cutting-edge features and ongoing development, providing superior protection compared to other VPN providers.
With its high-speed performance, robust security features, and user-friendly interface, NordVPN offers several advantages in the VPN market.
- High-speed performance (700+ Mbps download speeds)
- Robust security features
- User-friendly interface
- Commitment to user privacy
- Innovative features
- Consistent access to streaming sites
These qualities make NordVPN a top choice for users seeking a reliable and secure VPN solution. Its closest competitor is Surfshark, with ExpressVPN not too far behind.
Speed Comparison
NordVPN consistently delivers fast speeds compared to other VPN providers, ensuring a smooth browsing experience for users. In our tests, NordVPN outperformed its competitors in terms of speed, allowing us to access content quickly and without any noticeable slowdown.
This impressive speed performance sets NordVPN apart from other VPN providers, making it an ideal choice for users who prioritize speed and reliability. These are both crucial factors if you need a VPN for streaming or torrenting, as well as everyday browsing.
Security and Privacy Comparison
NordVPN’s security and privacy features are on par with, if not better than, other top VPN services in the market. With its strict no-log policy, robust encryption, and reliable tunneling protocols, NordVPN provides a high level of security and privacy for its users.
Additionally, NordVPN’s commitment to transparency and independent audits further demonstrates the company’s dedication to user privacy and security, making it a strong competitor in the VPN industry.
User Opinions: What Do Real Users Think of NordVPN?
User opinions on NordVPN are generally positive, with many users praising its speed, security, and streaming capabilities. NordVPN’s commitment to user privacy and innovative features have earned it a loyal user base and a strong reputation within the VPN community.
While opinions on different internet forums can really vary, overall it seems most people are satisfied with NordVPN.
The wide range of subscription options, including the Complete plan with its bundled Nord products, ensures that users can find a plan that suits their needs and budget. With its impressive performance and user-friendly interface, NordVPN is a top choice for users seeking a reliable and secure VPN solution.
NordVPN review conclusion: It still outperforms the competition
I’ve been testing NordVPN for about seven years now, as both a personal user and also for VPN reviews. Once again, our test results show that NordVPN continues to improve their service. With this level of performance, NordVPN is a premium VPN at a very reasonable price.
NordVPN has made major improvements over the past year in many areas and continues to get better. Here’s what stands out to me with the latest review:
- Faster speeds and better reliability throughout the server network
- Replaced CyberSec with Threat Protection for even greater security and privacy
- Big security upgrades, with all servers, converted to run in RAM-disk mode and colocated (self-owned) server rollout continuing
- Integrated WireGuard VPN protocol into their own NordLynx protocol with support in all VPN apps
- More support for Netflix and other streaming services
While there are a few minor drawbacks, NordVPN remains a great choice for virtually any user. It remains our top-recommended VPN based on these test results.
Are you ready to test-drive this killer VPN? Give it a shot with the coupon below for the best deal.
NordVPN’s Cyber Deal is live:
Get 69% Off NordVPN two-year subscriptions plus 3 months extra:
(Coupon is applied automatically; 30 day money-back guarantee.)
Alternatives to NordVPN
Click the VPN name below to read our full review – or grab the discount for the best savings. Both of these VPNs have a 30-day money-back guarantee.
You can also check out our best VPN services list for other recommendations.
Does NordVPN work for torrenting?
Yes, NordVPN is an excellent choice if you need a good VPN for torrenting. Here are three reasons why.
1. Fast and consistent speeds – This will be useful when torrenting large files.
2. Leak protection – The NordVPN apps come with built-in leak protection settings. This allows you to torrent for hours without worrying about your IP address being exposed.
3. Safe jurisdiction – NordVPN is based in Panama. Unlike the US and Europe, Panama does not have draconian copyright laws. NordVPN can simply ignore DMCA/copyright requests from other countries.
Does NordVPN work in China?
Thanks to its obfuscated servers, NordVPN is a great choice if you need internet access that can get around the Great Firewall of China. These servers make your VPN traffic look like standard internet traffic, so the Great Firewall and other anti-VPN technologies can’t detect it.
Is NordVPN worth the money?
The answer to this question is yes. In test after test, NordVPN ranks as one of the top VPNs for any VPN use case. Yet at the same time, it is one of the least expensive VPNs on the market. NordVPN is a great value and definitely worth the money they charge you.
Does NordVPN use virtual servers?
NordVPN is now adding some select virtual server locations to its lineup of servers. The reason for this is to give NordVPN users more options with server locations and to better access content from remote locales.
Does NordVPN offer static IP addresses?
NordVPN offers dedicated IPs, which are static IPs that are dedicated to a single user. You can get a dedicated IP address by contacting NordVPN support. They cost $70 per year above and beyond your subscription cost. It is one of the best VPNs with a dedicated IP.
Is NordVPN good for streaming?
NordVPN is an exceptional VPN for streaming. It is extremely fast, so content streams smoothly without buffering or other delays. And NordVPN does a great job of unblocking geo-blocked content from streaming sites. That means you can use it to view content from all around the world while remaining comfortably ensconced on your sofa at home.
If you have used NordVPN, feel free to share your honest review (good or bad) below.
This NordVPN review was last updated on March 18, 2024.

What’s the reason behind NordVPN’s decision not to incorporate virtual servers into Canada?
Reflecting on the situation about five years ago, I distinctly recall NordVPN having a considerable number of data centers spread across Canada, tallying around a hundred.
However, in the present scenario, their presence seems to have dwindled to just a handful. This marked reduction in Canadian servers contrasts sharply with their expansive network in the United States, where they proudly tout well over 200 servers.
I recently looked at NordVPN’s presence in Canada, and also tested the NordVPN servers in Vancouver, Montreal, and Toronto. With every location, I easily hit speeds over 600 Mbps with all tests. Our testing location is in the US, closest to the Vancouver server. Nonetheless, NordVPN performed flawlessly in Canada, as you can see here:
https://restoreprivacy.com/vpn/best/canada/nordvpn/
And to your question, VPNs (all of the big ones) utilize virtual servers for remote locations where good data centers for servers are typically hard to come by, or there are other challenges. Examples of this from the NordVPN app that I’m testing right now include Uzbekistan, Venezuela, Sri Lanka, Pakistan, Lebanon, and many more. This is obviously not the case for countries like Canada, US, UK, Germany, where real dedicated servers can be deployed.
Sven,
Your mention of NordVPN’s impressive speeds in Canada is duly noted, though it is tangential to the central issue at hand.
The fundamental concern lies in NordVPN’s notable and concerning eduction in Canadian data centers, transitioning from over a hundred to just a handful.
In this context, the introduction of virtual servers emerges as a practical solution to rectify this shortfall. By reinstating virtual servers, NordVPN could effectively bolster its server capacity in Canada, thus improving service reliability and coverage. Moreover, such an implementation could mitigate the risk of websites detecting VPN traffic, thereby enhancing user experience.
Looks like nordvpn is adding virtual servers to their lineup:
https://nordvpn.com/blog/new-nordvpn-virtual-servers/
Yes, good catch. I see the reasoning for doing this as it gives users more server options and access to media and content in those respective locations.
Greetings Sven Taylor,
In your Nord VPN review you state that “+ 3 months are FREE.” However, the Nord VPN site shows the 3 months as “extra”, with a 24 (27) month total of 80.73. 3.09 x 24 + 3 “free” should add up to 71.76. NVPN has obviously tacked on the 3 “extra” months for a total of 80.73.
I don’t mean to quibble about a few extra cents, but should not this discrepancy be corrected one way or the other? Thanks and I love your website. It is most informative and up-to-date.
Tony
Hey Tony, good point, I’ll adjust this.
I’m on a Nord VPN trial now and Amazon Prime blocks NordVPN despite changing the protocols. Facebook also knows my actual location too with NordVPN.
I suppose a smaller VPN company might not be blocked, or does FB and Amazon base the block on IP address range instead?
Try using the Nord browser extension and split tunnel the browser outside the VPN. That usually works better for streaming
I always say to myself “everything is figureoutable”, but being a total newbie to the VPN world and after reading some of these comments….are VPN’s really that easy to use and install? I don’t even know how to clear cookies😳!!! I will google it and find out if need be, but all this other tech stuff is really over my head. I started looking into this this as I am now travelling to Mexico 6 months of the year and want to stream Netflix from another country where Netflix is cheaper and connect to US Netflix streaming. From what I read this sounds easy to do but now I am wondering…🤔
Team Sven or anyone, please share your opinions, as I’m really stumped here. I have a NordVPN subscription and I also have a free VPN too (why not) for for testing.
I am writing to seek your help with an issue I am experiencing with NordVPN and VoIP calls over Costco Wi-Fi.
I am using an iPhone 13 and I have NordVPN installed.
I am from the UK and I was recently in the US at a Costco warehouse. I was using their free Wi-Fi, which had speeds of around 20-30 Mbps. I wanted to make a FaceTime call, but I could not. I then tried to make a call with WhatsApp and Google Voice, but I was also unable to do so. I had no issue making VoIP calls when connected to cellular or to the Wi-Fi at my Airbnb. I couldn’t make a call using Wi-Fi calling which I normally can do as well. And I’m even able to make Wi-Fi calling calls with speeds as low as 1-2 Mbps.
I tried connecting to NordVPN using the standard automatic protocol, but my connection stopped immediately. I then tried connecting using OpenVPN UDP Obfuscate and OpenVPN TCP Obfuscate protocols, but neither of those worked either. I also tried changing the default DNS, but that did not help either. I tried every possible connection option within the app without success.
I tried connecting to my other free VPN, but I had the same issue. I also tried using Stealth mode, but that did not help either.
I am concerned that Costco may be blocking VoIP calls, given that many financial institutions block VPN access and Meta/Facebook is blocking users from accessing Canadian news sites within Canada with a VPN and that Google may be considering doing something similar with news links. I can’t help wonder if this might be a new issue for us who use VPNs for unblocking restrictions.
I contacted NordVPN support, but they told me after a long, long, frustrating, drawn out process that the issue is with my iPhone’s hardware and not with their VPN. There was an outrageous amount of gaslighting, and they had me try everything, except to stand in front of a mirror in the dark and proclaim Hail Mary a hundred times.
I do not believe at all that I have any hardware issues as I have connected to other public access points like Starbucks, malls, McDonald’s and more.
I am wondering if anyone has a workaround for this issue. I am also concerned about the future of VPNs in regard to bypassing geolocation restrictions and blocking ports such as VoIP. Perhaps this will become the new normal?
I believe Nord VPN should not be recommended, definitely not anymore. Though I am myself a Nord VPN user because I renewed the subscription two weeks back under the impression that Nord VPN is a good VPN due to it being recommended by certain privacy oriented communities. Those privacy oriented communities which do not recommend Nord VPN and find it suspicious turns out to be correct. Even I failed to judge Nord VPN because of lack of proper or mixed information and limited research. Nord VPN is monitoring traffic of their users and is suspending accounts on the pretext of web scraping although almost all of those users don’t even know what that means and are normal users who use internet for privacy and security and connect using the service for ordinary day to day activities. Even my account was suspended soon after I renewed. They also won’t refund, citing violation of contract. Besides I was not very happy with Nord VPN as I had problems with their service though not too many because I am always patient and my needs are very small, just using internet for learning and never streaming or torrenting.
Also I initially didn’t want to write this on restore privacy, worried it would be a waste of time and effort as I hold the view and believe that there is a lot of censorship or at the least selectivity on this website and comments are not published which is also something worse than privacy violation.
Further, I don’t like VPNs being ranked as things are dynamic and multidimensional and everyone has different needs and those needs are often small. For normal privacy, and prevention of online data collection even an average US/Canada based VPN for a good vendor like for example Torguard or Tunnelbear is enough unless one is going against the state which is altogether a different dimension and needs strengthening of public institutions at ground level, not sitting behind screens and using Adblocker and VPN. Digital lives including digital activism and digital surveillance are very limited aspects of life and not the most essential things to be focused on.
Not the least, I believe despite privacy issues online, one need not be overly paranoid like some of the online privacy communities are and one can understand some of the technical, social, political and cultural aspects of technology, life, administration and civilization as a part of basic literacy, general digital literary, good cyber security hygiene and privacy-security incorporated in use of technology and beyond without being hyper sensitive and fanatical about digital privacy and beibg a privacy absolutist. Once one uses products from trustworthy developers and pays handsomely for them so that data monetization is not needed, there is privacy. Or when one uses software develoed by communities that are opensource, it is again privacy oriented. There are bigger things to worry about than gadgetry and data monetization, both in society and specially at an individual level where one needs to find the truth and light of life for himself and herself. Technology and internet is just a tool, not vitality and essence. Not being secure, that is not being private means the tool is defective or less useful. It is altogether never essential and the most important thing.
Update: After few back and forth emails Nord VPN did restore services to my account. It took a few days, less than a week. Though it is not necessary whether Nord will do it for everyone, they investigate and then decide whether to restore account or not. Also if this again happens, even when a false positive, based on other reviews, Nord will permanently terminate the service to my account. Also it is noteworthy that they only terminate service to the account and not the account itself. There is a option to renew subscription for that account whose services has been terminated (but never the account itself), which is certainly suspicious and more of a money grab. They would have rather terminated it permanently. No warning is sent if Nord detects malicious behaviour from your internet traffic which they are constantly monitoring. Account services are immediately terminated and support it slow to reply after an initial copy paste reply and investigate which takes a few days up to a week and it seems they might be storing logs, how would it otherwise possible to investigate. CTO of Adguard once told that it is possible for companies to undergone third party audit and still store logs. As, they might just not store logs during the time of Audit and delete previous logs and start storing it again after the audit. Nord says it has been audited three times independently and uses discless RAM only servers which cannot store logs.
I though agree that Nord client applications are good and free from most bugs which many other VPNs, even prominent ones cannot claim, thought they are catching up and VPNs while becoming more famous and common day by day are also getting better and improving on several notes and smaller players are fast catching up to big players and difference between them is reducing. And constant CAPTCHAS are less of a problem or not a problem at all with smaller VPN providers than the big players.
As for Nord VPN, I did share my experience on trustpilot which Nord did not like and flagged the review as defamatory and malicious.
If one subscribes to Nord VPN one might have to constantly live under the fear of a ban and cannot use internet worry free, even if one is a benign and responsible internet user like me who himself blocks all malicious websites using ESET Internet Security Web filtering and never does torrenting, streaming or file sharing and uses internet for knowledge and research, and writing and learning, and attending lectures and some work.
Nord VPN is not developer friendly and it will terminate your service if you take backups of your WordPress blogs, considering it to be malicious behaviour and abuse of their service and terms of contract, ‘web scraping’. No refund provided.
I bought Nord mainly for travelling (don’t trust that public WiFi) and accessing Netflix from Asia and Europe. I travel a lot. So far, Nord has been flawless in these use cases. It consistently works for US Netflix, with great speeds and reliability. I also like the Threat Protection features. I’ve used other VPNs (Proton and Mullvad) and speeds were sub par.
I bought a three years of subscription but unfortunately I can’t use Nord VPN anymore because it is no longer works on Mac OS High Sierra. I don’t understand what is change, I can understand the newest application with new features (if there’s any) would be not supported by old computers but why my old app stop working.
We , users of legacy products abandoned by Nord VPN.
I would never pay for any of their products anymore.
My 2c on Nord. It’s fast – no doubt about that. And most of the time streaming works well. Split tunneling does too. My biggest gripe is the kill switch. You can enable a “permanent kill switch” i.e. always-on, even after reboot. The problem is that an app update doesn’t become active until after a reboot and the reboot that happens along with the update causes the permanent kill switch to not work that first time. Once you connect after the update/restart, then the permanent kill switch works again across reboots until the next update comes along. But that actual reboot tied to the update leaves the computer unprotected until the first connect completes successfully. Not a showstopper but definitely something to watch for if you’re trying to ensure your ISP isn’t selling your data. Nord used to allow the update to run manually/interactively but then they changed it to only apply the update at a reboot and now it creates this unprotected scenario described above.
I also agree with the previous commenter(s) about Nord’s support being useless. They truly are. They just scan your message for some keywords and then throw canned suggestions at you – as if this is the first time you’ve ever messed with a VPN or even anything to do with computer networking. And if you do manage to get past this initial nightmare back and forth, then when it’s clear that there’s a gap in the product, they tell you they’ll forward your suggestions to the development team but you know instantly that they’re going straight to /dev/null.
If you can live with the above gap relating to the kill switch and app update and you don’t need any support, then it’s a good option. I wish I could recommend something else instead as an all encompassing solution. IMO the most robust VPN apps are Mullvad’s and IVPN’s. But neither of them support streaming/regular IP rotating to avoid blacklisting. So you end up getting sites that don’t stream or don’t work or present you with a lot of Captchas. One day, someone will come up with the perfect service. Until then, you just have to decide what the best compromise is for you.
UPDATE: they’ve now changed it where the app update isn’t tied to a reboot. So, if desired for privacy, you can either close the browser(s) before updating or enable airplane mode temporarily while updating, Then go back to normal once the update finishes – no reboot involved. The permanent kill switch then seems to work at every reboot – including the first/next one after the app update.
Only issue now is that you can’t see that an app update is needed unless you open the app itself and then a red dot appears next to the “Settings” icon. Would be nice if they indicated something in the System Tray about there being a new update. But at least this is progress in terms of the permanent kill switch now working at every reboot/system start.
As an amateur I wonder how it is today with NORD VPN, they are still safe from bad ownership? I remember cyberghost was bought up one year, and 1-2 year ago express vpn was bought up also by bad company. u know what I mean cause i read it here 1-2 years ago. 2 i think it was. Som Israel company that in their beginning was making maleware and so on. Nordvpn has not been bought up like that? I see no info in the review. And is express vpn still dangerous cause this?
No, NordVPN remains independent and was never purchased. The parent company is Nord Security (same brand). ExpressVPN was purchased by Kape Technologies, but operates independently.
Nord support says they don’t support IPv6 protocol. They also don’t support natively IKEV2.
I’m now led to believe that Nord is not a good VPN client because it leaks your IP address via IPv6 protocol. This can yield devastating results if you’re torrenting.
Please correct me if I’m wrong here.
Yes this is wrong. Whenever a VPN says they “don support IPv6” — that means they do not give you an IPv6 address, but instead block it. There are no IPv6 leaks and we have tested this ourselves.
It seems you’re both right and you’re both wrong.
Nord only supports IPv6 blocking using Open VPN. This is from their website. If you’re using NordLynx then you’re exposed (that’s my inference). I haven’t confirmed this but there’s ongoing chatter by some who use Nord or other VPNs which don’t support IPv6 have received copyright infringement letters.
Nord also claims IPv6 isn’t common but in my experience it is. They instruct users when they contact support to disable IPv6 in your adapter settings.
Yes I agree it is smart to completely disable IPv6 on your device. But I have tested IP leaks with NordLynx and there were no IPv6 leaks on a fresh Windows device (without IPv6 disabled). In my assessment and tests, this is a non-issue. Most VPNs do not support IPv6, but some do, such as these IPv6 VPN services here.
Hi Sven,
I use NordVPN on my Mac OS and as far as I can tell it is not possible to have (Full) Thread Protection and a Systemwide Killswitch.
The NordVPN version I downloaded from their website offers full thread protection, but this version does not seem to offer a system-wide killswitch. At least I couldn’t find one! Irritated, I downloaded the version from the App Store and I have the Systemwide Killswitch but only Thread Protection Lite. The review doesn’t say anything about that.
Am I missing something or is it really the case on Mac OS that you can’t have both?
Hi John, this would be a question for Nord.
I asked Nord twice and got vague answers to my direct questions. But their reply and the info on their website leave only one conclusion. If you choose the App-Store-Version of their NordVPN-App you get Thread Protection Lite and a system-wide Kill Switch. If you choose the Website-Version of their app you get the full Thread Protection feature but no system-wide Kill Switch. You can however choose apps to be shut down, if the connection to the VPN is lost.
Just as info for those who, like me, are irritated by the two different versions!
And thanks to the hole Restorprivacy-Team for the excellent work here!
Unfortunately, NordVPN doesn’t always play nice when you have another VPN client installed (yet inactive) on your system. There seems to be a conflict that support can’t resolve which results in their VPN Client being non-functional (can’t connect to the internet with or with NordVPN).
Anyone else have this issue on a Windows 11/10 system?
This is usually the case whenever you have two or more VPNs installed on Windows.
Hi Sven Sir,
Nord VPN passed another 3rd party audit.
NordVPN passes third no-logs audit with flying colors
https://www.techradar.com/news/nordvpn-passes-third-no-logs-audit-with-flying-colors
I want to use nordvpn, but the only way to make the connection stable is by using a 3rd party app since i live in a restrictive country. I use “tunnelblick” for mac and “openvpn connect app” for iphone. My question is am I still under nordvpn privacy and security? or things changes since I use 3rd-party apps?
I really hope you can answer my question.
Thank you
Yes you are Mark. The drawback is you don’t get all of the features that come with the full NordVPN app, but you will get basic VPN functionality still with those third-party apps.
Would be nice to also add the ping time and upload speed to this particular info the next time.
“Unlike the US and Europe, Panama does not have draconian copyright laws.”
This was not always the case. Back in September 2012, the United States forced Panama to approve an extremely draconian copyright law, even more draconian than the United States’ laws that have been highly corrupted by the International Intellectual Property Alliance (a group of 7 content cartels that just lobby for extremely draconian copyright law in foreign countries), The law was called Bill 510 and it was widely infamous.
This is not the first time I heard this. The US government has been forced to export draconian copyright legislation to other countries by IIPA after the first Special 301 Report (which identifies “trade barriers” to the United States) was published in 1989. I further digged deeper and I found out that the Omnibus Foreign Trade and Competitiveness Act of 1988 spawned the Special 301 Reports (even though IIPA was founded in 1984).
Fortunately, I found no news articles about Panamian copyright law since 2014, so I think that it has been possibly repealed without notice from the public.
Hi Sven, thank you so much for your RestorePrivacy website! What a service! I’m always looking here first before looking anywhere else 🙂
I just signed up with NordVPN, connected to Iceland, and ran a test to whoer.net (a VPN provider in Cyprus) which detected that I’m not in the same time zone as the Iceland server I connected to.
Looks like NordVPN still has some work to do!
A temporary work-around is to change my computer’s time zone to Iceland, but it is cumbersome. Hopefully NordVPN will solve this soon!
Max, that is most likely your browser giving that information away, not NordVPN. A VPN does not and will not mask your browser settings and preferences. You need to lock down your browser.
Hi, Max
A VPN can’t hide your timezone. You have to change it in your router first if you want to mitiate that information. As for mitigations, it might be more important to check if your VPN status is hidden or not (obviously, it’s better if it’s not detected that you’re using a VPN) , for that information you can use this website: https://www.deviceinfo.me/
If it says that you are using some of the common VPN services, you shoud try with obfuscated servers…
Thank you a lot Sven for the valuable post
please, could you make a review on Hide[dot]me VPN?
Thanks again.
Yes, we should get to this one sometime soon.
I have been using Nord VPN for awhile now. Recently I went into my FireFox settings and found the following message: “Your browser is being managed by your organization.” There is a certificate called “ImportEnterpriseRoots.” My computer is my own and not associated with an employer or other organization, and I only realized this is there very recently. I read that sometimes ad blockers or antivirus programs will have this as a security feature. Is this something that would have been put there by Nord as part of Nord’s security features to block ads? Is it something I should be concerned about? There does not appear to be a way to remove it. [I have contacted Nord but their response did not answer the question. This is typical with them; I have only ever received canned, irrelevant responses that do not answer the question asked.]
This could be caused by a browser add-on or extension you installed with Firefox. I don’t think it would be the VPN. Did you install the NordVPN browser add-on in Firefox?
I don’t think so. I am a little tech-confused, though…. I have Nord set to NordLynx and I toggled some setting inside Nord to “on” that said it would help block malicious sites. I may have also added the UBlock extension in Firefox (I am trying implement the various things you recommend on this site). So maybe it is from that…?
> “added the UBlock extension in Firefox”
That may be it.
“managed by your organization”
You will see this if you’re running a Linux OS, because the updates are managed (with your control) through the system’s “apt” update manager, rather than by Firefox itself.
Nord works well on my google TV, but is terrible on my android phone. No matter what servers I switch to, I keep getting disconected to the point I have to uninstall Nord to do what I need. I have seen these same complaints from other users posted on other sites. Any thoughts?
We did not have any issues when testing Nord on Android earlier in the year. I’d recommend switching VPN protocols and see if that helps. It may be an issue with your network or settings on your Android.
Hi Sven, is it possible to know how many connections/devices can be used at the same time with a single account with NordVPN? Thank you very much.
Yep, here you go:
“A total of six devices can be connected with one NordVPN account at the same time.”
Ok great! Thanks Sven!
NordVPN doesn’t work through Windows in China at all. They are still working out how to fix it. However, the connectivity through Android App – StrongSwan is much faster than ExpressVPN. The only concerns would be typing the server address one by one manually and would have to try different server once its dropped out.
Thanks for this site, Sven. It’s very informative.
For those interested, I have had Nord for a couple of years, and couldn’t recommend it to anyone. If I’m logged into my account with my huge crazy password, I should have full control over changing settings like my email. I do not, unless of course I know the exact date I started service, the exact amount I paid and the source of my payment.
I use 5 credit cards and Paypal, so I have no idea what I used. I have no idea about the date either, and of course I have no idea what I paid considering it might have been on sale or not.
I won’t renew just because of that, but the other factors are it puts me in Germany if I’m on several US sites. It also won’t load certain sites depending on the location.
There is zero customer service, so I’m out, but think Surfshark might end up being the same if they have the same insane rules.
Router question.
If I buy a pre installed router, it can only be used with nordvpn forever, right?
Perhaps another stupid question, but how to protect both all the phones and pc’s that go out of the house and at the same time protect tv etc? And can I share with visitors in our hone without compromising own privacy?
“If I buy a pre installed router, it can only be used with nordvpn forever, right?”
No, you should be able to configure your router with other VPN services, no problem.
“Perhaps another stupid question, but how to protect both all the phones and pc’s that go out of the house and at the same time protect tv etc?”
A VPN router would be the best option for this, and then connect every device that you want protected to your VPN router. Additionally, you can run your regular ISP router at the same time, and connect devices that do not need protection to that network.
And can I share with visitors in our hone without compromising own privacy?
Yes you can.
Check out our VPN router guide. It should answer most of your questions.
Thank you 🙂
“Additionally, you can run your regular ISP router at the same time, and connect devices that do not need protection to that network.”
Could you maybe make a post on strategies about this, and just how to make a secure home network in general. Maybe define what would be ok on a isp router, what should be on you VPN router etc… would be a good read for many of us rookies out here.
CHEERS
We have some tips here:
https://restoreprivacy.com/secure-home-network/
Plus check out our VPN router guide:
https://restoreprivacy.com/vpn-router/
I was using expressvpn, which was working fine, but wanted to try one for a month that had gotten higher marks. NordVPN is completely unreliable on Ubuntu 20 LTS. At first is would just stop sending packets, and I was able to find some hackery online to reset its world for a while (on the order of hours). A new version came out, which seemed a bit better, but soon showed that it would disconnect after a while and nothing short of rebooting would make it functional again. Worst service of any kind I’ve tried in many years.
Hi Sven,
I discovered your blog yesterday and have been down the rabbit hole since then. I read that Nord recently merged with SurfShark. Although both companies say they will operate independently, how does that impact jurisdictional protections? I also read that SurfShark has been acquiring other VPN businesses. Do you think this will compromise privacy and other awesome functions that Nord has come to be known for? I just wondered because I have been heavily considering Nord as a VPN option. Thank you for all you do.
All rights reserved without prejudice
I see no impact to jurisdictions with this. Surfshark will continue to operate in The Netherlands while NordVPN operates under the Panama jurisdiction. If anything, it will give both VPNs a greater foundation to stand on when it comes to investing in their products and R&D. I have not seen news about Surfshark acquiring other VPN businesses, other than Atlas VPN joining the group earlier this year.
You may be thinking of Kape Technologies buying up ExpressVPN and others.
Sven,
Thank you for getting back to me so quickly. About the acquisitions, I’m sure you’re correct. I’m just learning about VPNs and the privacy realm since yesterday. I’ve been reading tons of articles on different websites but mainly yours. So I probably got it mixed up. Anyhow. I’ve already shared the website with a friend who is also very concerned about privacy. It’s amazing to me how many people think it’s a conspiracy theory to be so concerned and take such measures when it’s clear to see our rights, privacy and freedoms being threatened so openly every day. The government is literally telling us every day they do not care about our rights, privacy and freedoms. But I digress.
~All rights reserved without prejudice
Thank you 🙂 how do I find your answers 🙈 i have asked more questions. Sorry..
One of four ways to access Nord on Linux: 1. Terminal CLI (but see difficult changes they’ve made); 2. Browser website (I use Brave–Chrome derivative– app); 3. Router, though not as great, comes with problems; 4. Network Manager, difficult to get country-specific server location ISP defitinitions;
They’ve made several changes since January 1, 2022, and they’ve been strangely NOT transparent about them. CS is also almost non-existent–wait several days for a generic response…
I’m looking elsewhere…sorry
Based on your recommendations I purchased a two year subscription to NordVPN. It works great; I like it. BUT, when I purchased the VPN I also, without my knowledge, purchased NordPass for US$40. I did not intend to purchase it as I have and use an excellent, really excellent, password manager. I tried to get a refund for NordPass, but the representative said I would have to cancel my entire subscription and buy NordVPN again. No…I’ll just leave it as is. The VPN is excellent, but the marketing of NordPass is total deceptive nonsense that’s left me with a useless $40 expense bit of a bad taste for Nord.
I feel you; I almost fell for it too but happened to notice that nordpass was added onto there. Hate when companies do this. Sorry they got you!
Nord cautions that the Google version of their app (downloaded from Google Play Store) does not allow ad blocking of Google ads.
This is concerning. Obviously the Google version contains a unique identifier. My question is could that identifier potentially disclose the Google account of the downloader to any third party?